Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
When a credential is presented to Microsoft Entra ID in a token request, there can be multiple dependencies that must be available for validation. The first authentication factor relies on Microsoft Entra authentication and, in some cases, on external (non-Entra ID) dependency, such as on-premises infrastructure. For more information on hybrid authentication architectures, see Build resilience in your hybrid infrastructure.
If you implement a second factor, the dependencies for the second factor are added to the dependencies for the first. For example, if your first factor is via Pass Through Authentication (PTA) and your second factor is SMS, your dependencies are as follows.
- Microsoft Entra authentication services
- Microsoft Entra multifactor authentication service
- On-premises infrastructure
- Phone carrier
- The user's device (not pictured)
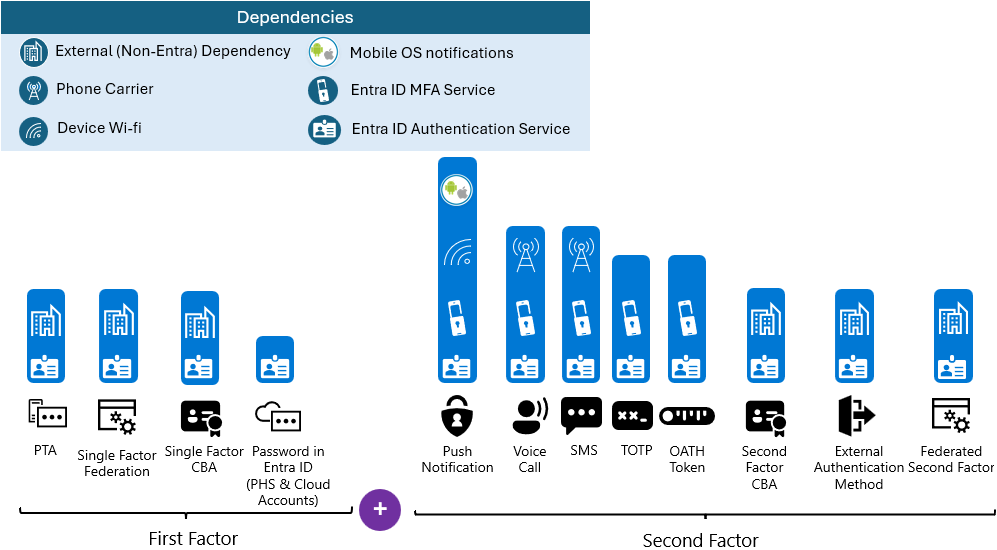
Your credential strategy should consider the dependencies of each authentication type and provision methods that avoid a single point of failure.
Because authentication methods have different dependencies, it's a good idea to enable users to register for as many second factor options as possible. Be sure to include second factors with different dependencies, if possible. For example, Voice call and SMS as second factors share the same dependencies, so having them as the only options doesn't mitigate risk.
For second factors, the Microsoft Authenticator app or other authenticator apps using time-based one time passcode (TOTP) or OAuth hardware tokens have the fewest dependencies and are, therefore, more resilient.
Additional Detail on External (Non-Entra) Dependencies
| Authentication Method | External (Non-Entra) Dependency | More Information |
|---|---|---|
| Federation | Federation server(s) must be online and available to process the authentication attempt | High availability cross-geographic AD FS deployment in Azure with Azure Traffic Manager |
| External Multifactor Authentication (External MFA) | External MFA provides a path for customers to use external MFA providers. | Manage external MFA in Microsoft Entra ID |
How do multiple credentials help resilience?
Provisioning multiple credential types gives users options that accommodate their preferences and environmental constraints. As a result, interactive authentication where users are prompted for multifactor authentication will be more resilient to specific dependencies being unavailable at the time of the request.
In addition to individual user resiliency described above, enterprises should plan contingencies for large-scale disruptions such as operational errors that introduce a misconfiguration, a natural disaster, or an enterprise-wide resource outage to an on-premises federation service (especially when used for multifactor authentication).
How do I implement resilient credentials?
Deploy the Microsoft Authenticator App as a second factor.
Turn on password hash synchronization for hybrid accounts that are synchronized from Windows Server Active Directory. This option can be enabled alongside federation services such as Active Directory Federation Services (AD FS) and provides a fallback in case the federation service fails.
Next steps
Resilience resources for administrators and architects
- Build resilience with device states
- Build resilience by using Continuous Access Evaluation (CAE)
- Build resilience in your hybrid authentication
- Build resilience in application access with Application Proxy