Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Azure Firewall Premium includes a TLS inspection feature, which requires a certificate authentication chain. For production deployments, use an Enterprise PKI to generate the certificates that you use with Azure Firewall Premium. Use this article to create and manage an Intermediate CA certificate for Azure Firewall Premium.
For more information about certificates used by Azure Firewall Premium, see Azure Firewall Premium certificates.
Prerequisites
If you don't have an Azure subscription, create a trial subscription before you begin.
To use an Enterprise CA to generate a certificate to use with Azure Firewall Premium, you need the following resources:
- an Active Directory Forest
- an Active Directory Certification Services Root CA with Web Enrollment enabled
- an Azure Firewall Premium with Premium tier Firewall Policy
- an Azure Key Vault
- a Managed Identity with Read permissions to Certificates and Secrets defined in the Key Vault Access Policy
Request and export a certificate
Access the web enrollment site on the Root CA, usually
https://<servername>/certsrv, and select Request a Certificate.Select Advanced Certificate Request.
Select Create and Submit a Request to this CA.
Fill out the form using the Subordinate Certification Authority template created in the previous section.
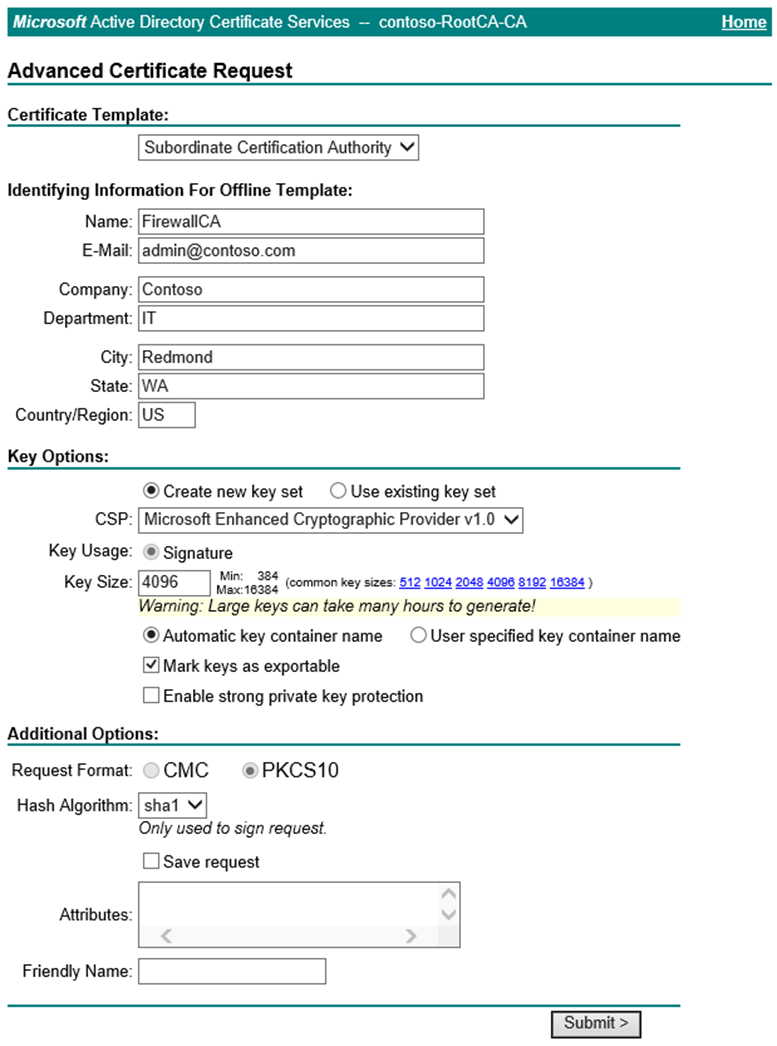
Submit the request and install the certificate.
Assuming you make this request from a Windows Server using Internet Explorer, open Internet Options.
Navigate to the Content tab and select Certificates.
Select the certificate that the CA issued and then select Export.
Select Next to begin the wizard. Select Yes, export the private key, and then select Next.
The wizard selects the .pfx file format by default. Uncheck Include all certificates in the certification path if possible. If you export the entire certificate chain, the import process to Azure Firewall fails.
Assign and confirm a password to protect the key, and then select Next.
Choose a file name and export location and then select Next.
Select Finish and move the exported certificate to a secure location.
Add the certificate to a Firewall Policy
In the Azure portal, go to the Certificates page of your Key Vault, and select Generate/Import.
Select Import as the creation method. Enter a name for the certificate, select the exported .pfx file, enter the password, and then select Create.
Go to the TLS Inspection page of your Firewall policy and select your Managed identity, Key Vault, and certificate.
Select Save.
Validate TLS inspection
Create an Application Rule that uses TLS inspection for the destination URL or FQDN of your choice. For example:
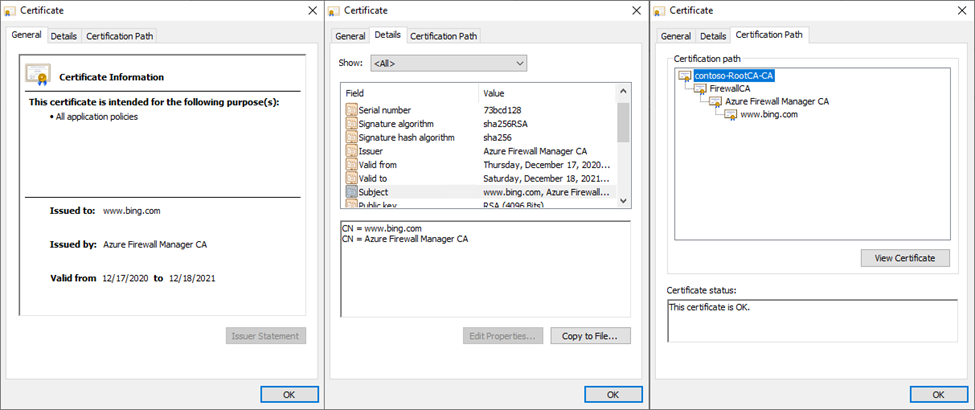
*bing.com.From a domain-joined machine within the source range of the rule, go to your destination and select the lock symbol next to the address bar in your browser. The certificate should show that your Enterprise CA issued it rather than a public CA.
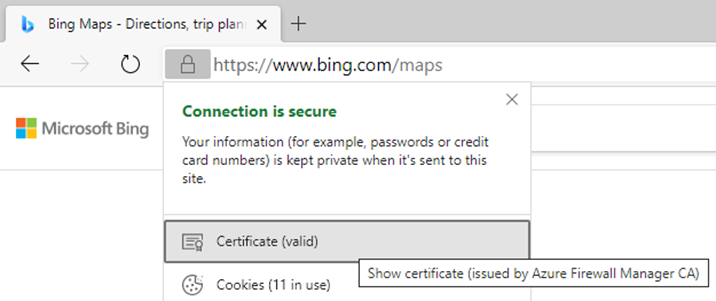
Show the certificate to display more details, including the certificate path.
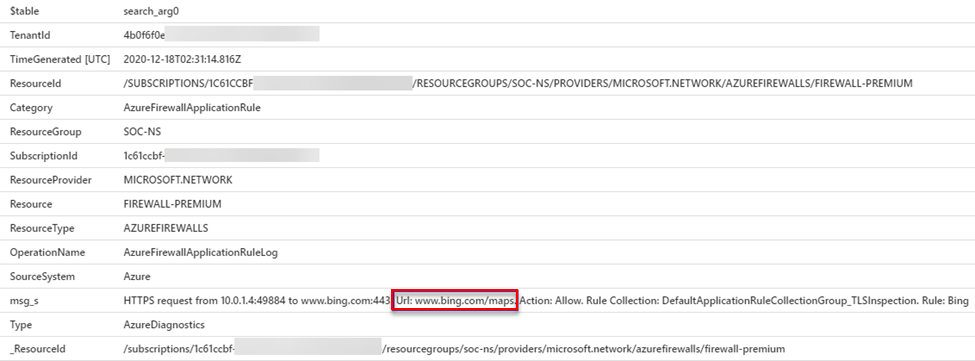
In Log Analytics, run the following KQL query to return all requests that are subject to TLS Inspection:
AzureDiagnostics | where ResourceType == "AZUREFIREWALLS" | where Category == "AzureFirewallApplicationRule" | where msg_s contains "Url:" | sort by TimeGenerated descThe result shows the full URL of inspected traffic: