Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Applies to: ✔️ Front Door Standard ✔️ Front Door Premium
This quickstart shows you how to create an Azure Front Door profile by using the Azure portal. You can create an Azure Front Door profile by using either Quick create or Custom create. The Quick create option helps you configure the basic settings of your profile, while the Custom create option enables you to customize your profile with more advanced settings.
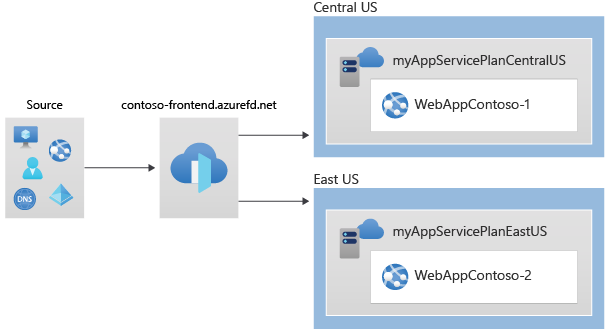
In this quickstart, use the Custom create option to create an Azure Front Door profile. First, deploy two App Services as your origin servers. Then, configure the Azure Front Door profile to route traffic to your App Services based on certain rules. Finally, test the connectivity to your App Services by accessing the Azure Front Door frontend hostname.
Note
For web workloads, we highly recommend utilizing Azure DDoS protection and a web application firewall to safeguard against emerging DDoS attacks. Another option is to employ Azure Front Door along with a web application firewall. Azure Front Door offers platform-level protection against network-level DDoS attacks. For more information, see security baseline for Azure services.
Prerequisites
An Azure account with an active subscription. Create an account.
Create an Azure Front Door profile
Custom create
Create an Azure Front Door profile by using Custom create and deploy two App services that your Azure Front Door profile uses as your origins.
Create two Web App instances
If you already have services to use as an origin, skip to create a Front Door for your application.
This example demonstrates how to create two Web App instances deployed in different Azure regions. Both web application instances operate in an active/active mode, meaning they can both handle incoming traffic. This configuration differs from an active/standby configuration, where one instance serves as a backup for the other.
To create the two Web Apps for this example, follow these steps:
Sign in to the Azure portal.
To start creating the first Web App, select the + Create a resource button on the top left corner of the portal. Then, type Web App in the search box and select Create to proceed with the configuration.
On the Create Web App page, fill in the required information on the Basics tab.
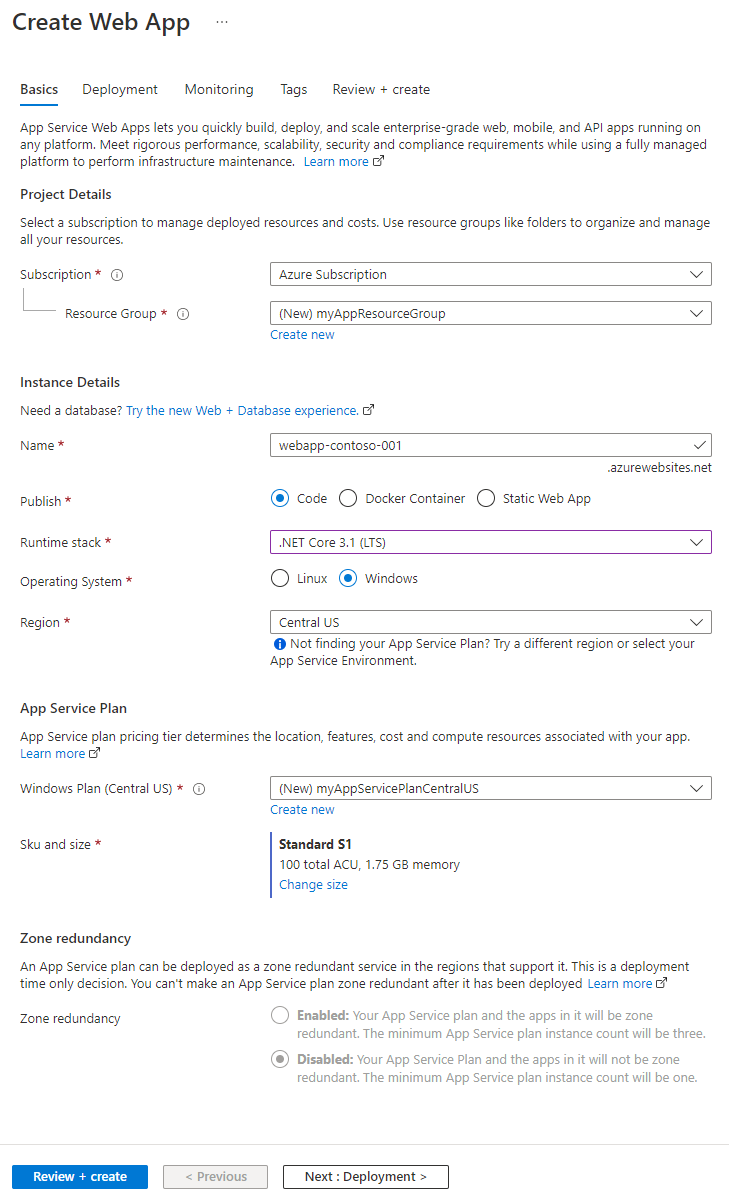
Setting Description Subscription Select your subscription. Resource group Select Create new and enter myAppResourceGroup in the text box. Name Enter a unique Name for your web app. This example uses webapp-contoso-001. Publish Select Code. Runtime stack Select .NET Core 3.1 (LTS). Operating System Select Windows. Region Select China North 3. Windows Plan Select Create new and enter myAppServicePlanChinaNorth3 in the text box. Sku and size Select Standard S1 100 total ACU, 1.75-GB memory. To complete the creation of the Web App, select Review + create button and verify the summary of the settings. Then, select the Create button to start the deployment process, which can take up to a minute.
To create a second Web App, follow the same steps as for the first Web App, but make the following changes in the settings:
Setting Description Resource group Select Create new and enter myAppResourceGroup2. Name Enter a unique name for your Web App, in this example, webapp-contoso-002. Region A different region, in this example, China North 2 App Service plan > Windows Plan Select New and enter myAppServicePlanChinaNorth3, and then select OK.
Create a Front Door for your application
In this step, you configure Azure Front Door to route user traffic to the nearest Web App origin based on latency. Additionally, you apply a Web Application Firewall (WAF) policy to protect your Azure Front Door from malicious attacks.
Sign in to the Azure portal.
From the home page or the Azure menu, select + Create a resource, search for Front Door and CDN profiles, and select Create.
In the Endpoint tab, select Add an endpoint, enter a globally unique name (for example, contoso-frontend), and select Add. You can create more endpoints after the initial deployment.
To configure routing to your Web App origin, select + Add a route.
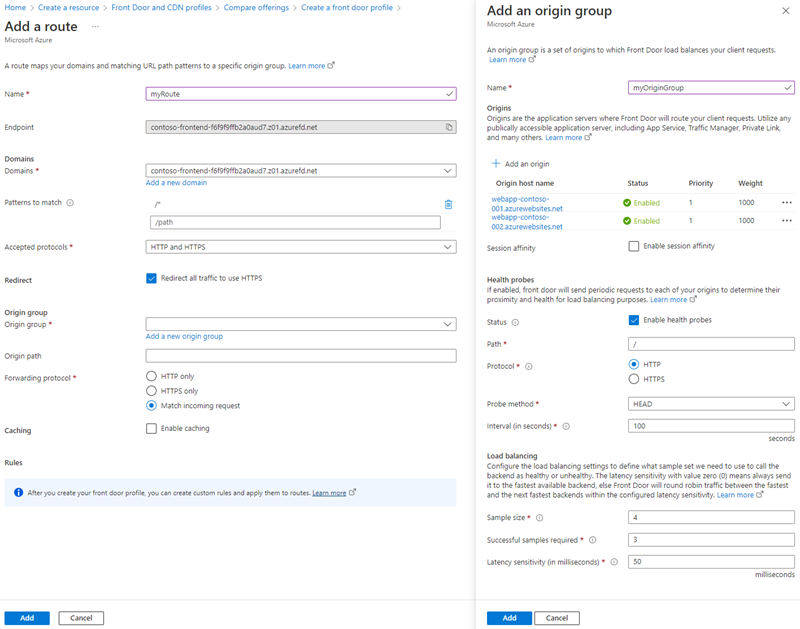
On the Add a route page, enter or select the following information and then select Add to add the route to the endpoint configuration.
Setting Description Name Provide a name that identifies the mapping between domains and origin group. Domains The system generates a domain name for you to use. To add a custom domain, select Add a new domain. This example uses the default domain name. Patterns to match Specify the URLs that this route accepts. This example uses the default setting, which accepts all URL paths. Accepted protocols Choose the protocol that the route accepts. This example accepts both HTTP and HTTPS requests. Redirect Turn on this setting to redirect all HTTP requests to the HTTPS endpoint. Origin group To create a new origin group, select Add a new origin group and enter myOriginGroup as the origin group name. Then select + Add an origin and enter WebApp1 for the Name and App services for the Origin Type. In the Host name, select webapp-contoso-001.chinacloudsites.cn and select Add to add the origin to the origin group. Repeat the steps to add the second Web App as an origin with WebApp2 as the Name and webapp-contoso-002.chinacloudsites.cn as the Host name. Choose a priority for each origin, with the lowest number having the highest priority. If you need Azure Front Door to serve both origins, use a priority of 1. Choose a weight for each origin, with the weight determining how traffic is routed to the origins. Use equal weights of 1000 if the traffic needs to be routed to both origins equally. Once both Web App origins are added, select Add to save the origin group configuration. Origin path Leave this field empty. Forwarding protocol Choose the protocol that the origin group receives. This example uses the same protocol as the incoming requests. Caching Select the check box if you want to use Azure Front Door’s edge POPs and the Microsoft network to cache contents closer to your users globally. Rules After deploying the Azure Front Door profile, you can use Rules to customize your route. Important
Domain is mandatory. In the route, you can't select the AFD endpoint domain, only the custom domain can be selected. Moreover, the domain needs to obtain an ICP filing from 21Vianet. You can contact 21Vianet representative for more information.
Select + Add a policy to apply a Web Application Firewall (WAF) policy to one or more domains in the Azure Front Door profile.
To create a security policy, provide a name that uniquely identifies it. Next, choose the domains that you want to apply the policy to. You can also select an existing WAF policy or create a new one. To finish, select Save to add the security policy to the endpoint configuration.
To deploy the Azure Front Door profile, select Review + Create and then Create. The configuration propagates to all edge locations within a few minutes.
Verify Azure Front Door
The global deployment of the Azure Front Door profile takes a few minutes to complete. After that, you can access the frontend host by entering its endpoint hostname in a browser. For example, contoso-frontend.z01.azurefd.net. The request is automatically routed to the closest server among the specified servers in the origin group.
To test the instant global failover feature, follow these steps if you created the apps in this quickstart. You see an information page with the app details.
Enter the endpoint hostname in a browser, for example,
contoso-frontend.z01.azurefd.net.In the Azure portal, search for and select App services. Locate one of your Web Apps, such as WebApp-Contoso-001.
Select the Web App from the list and then select Stop. Confirm your action by selecting Yes.
Reload the browser to see the information page again.
Tip
Traffic may take some time to switch to the second Web App. You might need to reload the browser again.
To stop the second Web App, select it from the list and then choose Stop. Confirm your action by selecting Yes.
Reload the web page. You should encounter an error message after the refresh.

Clean up resources
If you no longer need the environment, delete all the resources you created. Deleting a resource group also removes all its contents. To avoid incurring unnecessary charges, delete these resources if you don't plan to use this Azure Front Door.
In the Azure portal, search for and select Resource groups, or go to Resource groups from the Azure portal menu.
Use the filter option or scroll down the list to locate the resource groups, such as myAFDResourceGroup, myAppResourceGroup, or myAppResourceGroup2.
Select the resource group you want to delete, and then choose the Delete option.
Warning
Deleting a resource group is irreversible. You can't recover the resources within the resource group once deleted.
Enter the name of the resource group to confirm, and then select the Delete button.
Repeat these steps for the remaining resource groups.
Next steps
Proceed to the next article to learn how to configure a custom domain for your Azure Front Door.