Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Important
Attention: All Microsoft Sentinel features will be officially retired in Azure in China regions on August 18, 2026 per the announcement posted by 21Vianet.
Important
The new version of the Fusion analytics rule is currently in PREVIEW. See the Supplemental Terms of Use for Azure Previews for additional legal terms that apply to Azure features that are in beta, preview, or otherwise not yet released into general availability.
Microsoft Sentinel uses Fusion, a correlation engine based on scalable machine learning algorithms, to automatically detect multistage attacks by identifying combinations of anomalous behaviors and suspicious activities that are observed at various stages of the attack chain. Based on these discoveries, Microsoft Sentinel generates incidents that would otherwise be difficult to catch. These incidents comprise two or more alerts or activities. By design, these incidents are low-volume, high-fidelity, and high-severity.
Customized for your environment, this detection technology not only reduces false positive rates but can also detect attacks with limited or missing information.
Configure Fusion rules
This detection is enabled by default in Microsoft Sentinel. To check or change its status, use the following instructions:
Sign in to the Azure portal and enter Microsoft Sentinel.
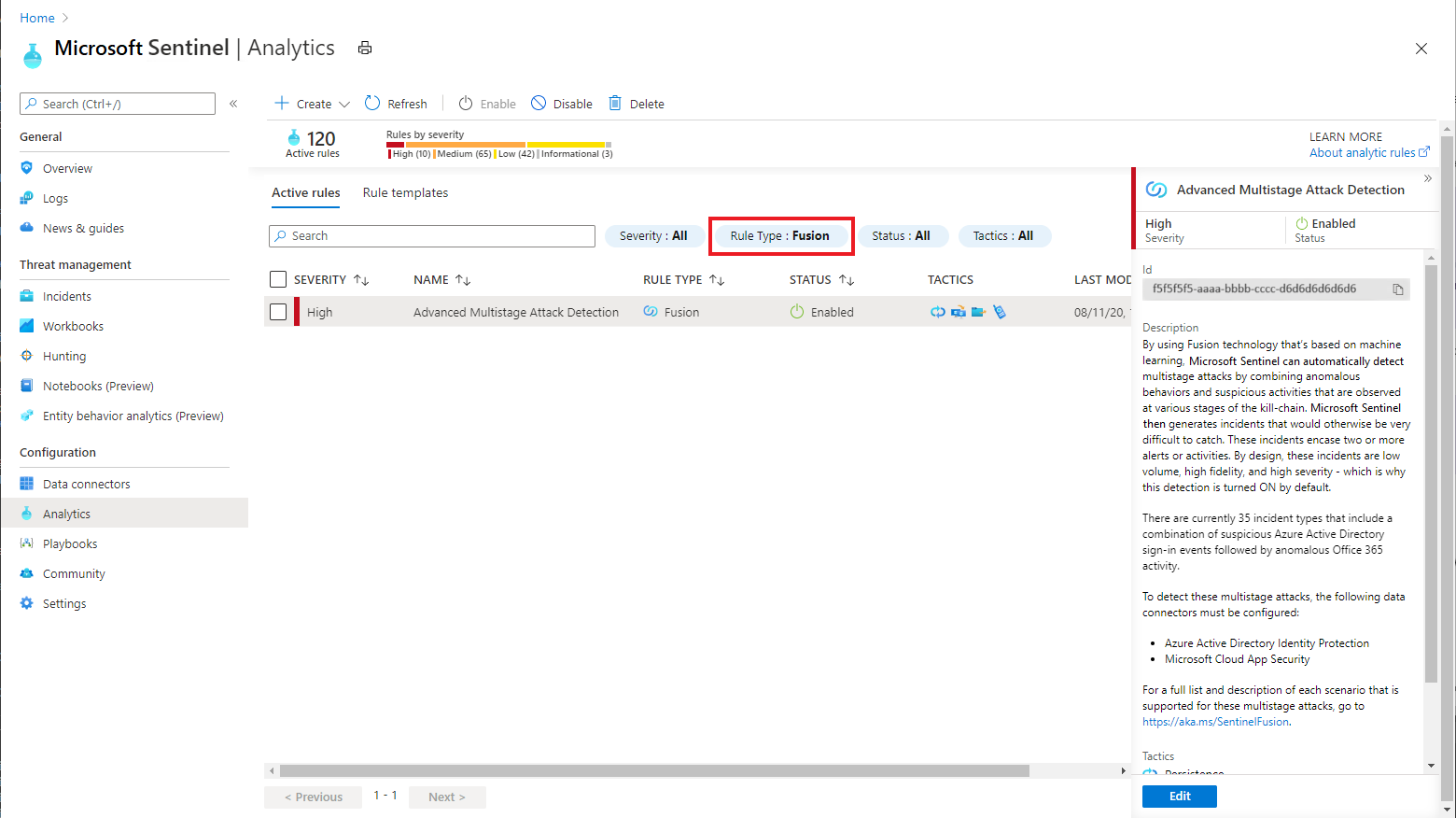
From the Microsoft Sentinel navigation menu, select Analytics.
Select the Active rules tab, and then locate Advanced Multistage Attack Detection in the NAME column by filtering the list for the Fusion rule type. Check the STATUS column to confirm whether this detection is enabled or disabled.
To change the status, select this entry. On the Advanced Multistage Attack Detection preview pane, select Edit.
In the General tab of the Analytics rule wizard, note the status (Enabled/Disabled), or change it if you want.
If you change the status but have no further changes to make, select the Review and update tab and select Save.
To further configure the Fusion detection rule, select Next: Configure Fusion.
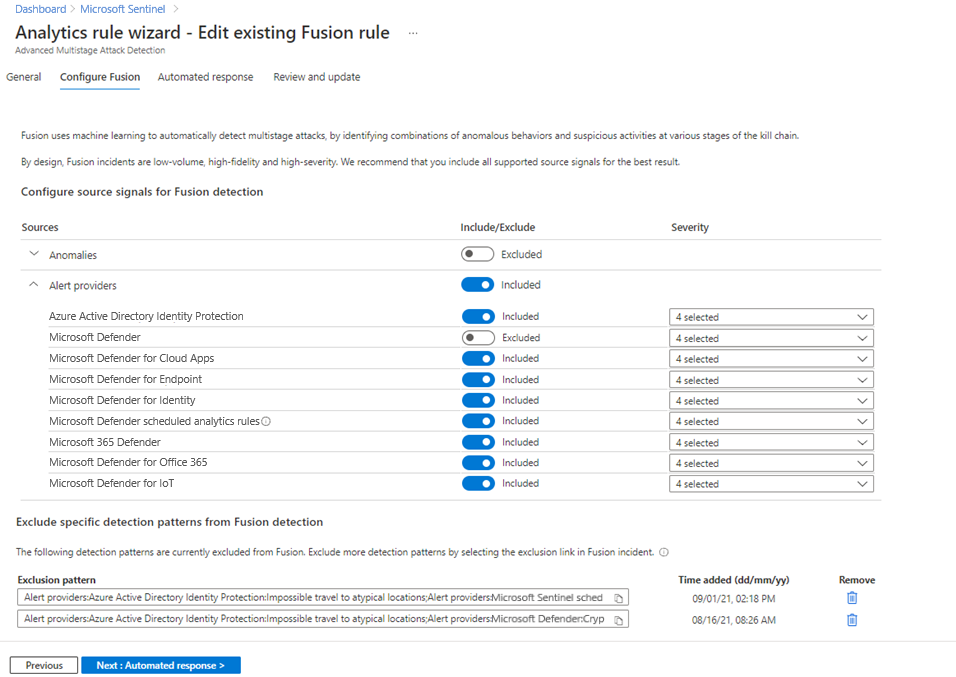
Configure source signals for Fusion detection: we recommend you include all the listed source signals, with all severity levels, for the best result. By default, they're already all included, but you have the option to make changes in the following ways:
Note
If you exclude a particular source signal or an alert severity level, any Fusion detections that rely on signals from that source, or on alerts matching that severity level, won't be triggered.
Exclude signals from Fusion detections, including anomalies, and alerts from various providers.
Use case: If you're testing a specific signal source known to produce noisy alerts, you can temporarily turn off the signals from that particular signal source for Fusion detections.
Configure alert severity for each provider: By design, the Fusion ML model correlates low fidelity signals into a single high severity incident based on anomalous signals across the kill-chain from multiple data sources. Alerts included in Fusion are lower severity (medium, low, informational), but occasionally relevant high severity alerts are included.
Use case: If you have a separate process for triaging and investigating high severity alerts and prefer not to have these alerts included in Fusion, you can configure the source signals to exclude high severity alerts from Fusion detections.
Exclude specific detection patterns from Fusion detection. Certain Fusion detections might not be applicable to your environment, or might be prone to generating false positives. If you want to exclude a specific Fusion detection pattern, follow the instructions below:
Locate and open a Fusion incident of the kind you want to exclude.
In the Description section, select Show more.
Under Exclude this specific detection pattern, select exclusion link, which redirects you to the Configure Fusion tab in the analytics rule wizard.
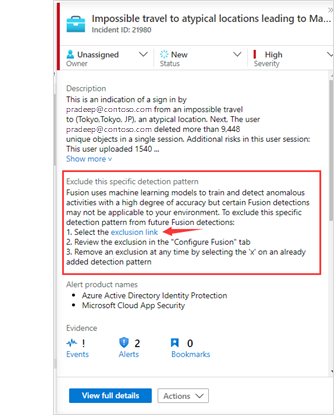
On the Configure Fusion tab, you see that the detection pattern—a combination of alerts and anomalies in a Fusion incident—has been added to the exclusion list, along with the time when the detection pattern was added.
You can remove an excluded detection pattern at any time by selecting the trashcan icon on that detection pattern.

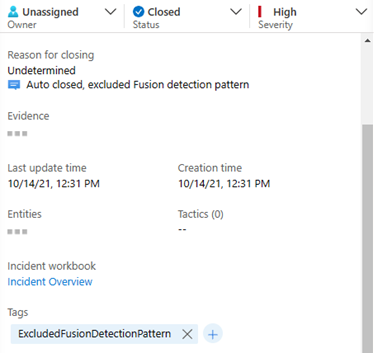
Incidents that match excluded detection patterns still trigger, but they don't show up in your active incidents queue. They're autopopulated with the following values:
Status: "Closed"
Closing classification: "Undetermined"
Comment: "Auto closed, excluded Fusion detection pattern"
Tag: "ExcludedFusionDetectionPattern" - you can query on this tag to view all incidents matching this detection pattern.
Note
Microsoft Sentinel currently uses 30 days of historical data to train the machine learning systems. This data is always encrypted with Microsoft's keys as it passes through the machine learning pipeline. However, the training data isn't encrypted with Customer-Managed Keys (CMK) if you enable CMK in your Microsoft Sentinel workspace. To opt out of Fusion, go to Microsoft Sentinel > Configuration > Analytics > Active rules, right-click on the Advanced Multistage Attack Detection rule, and select Disable.
Configure scheduled analytics rules for Fusion detections
Important
Fusion-based detection using analytics rule alerts is currently in PREVIEW. See the Supplemental Terms of Use for Azure Previews for additional legal terms that apply to Azure features that are in beta, preview, or otherwise not yet released into general availability.
Fusion detects scenario-based multistage attacks and emerging threats by using alerts generated by scheduled analytics rules. To get the most out of Microsoft Sentinel's Fusion capabilities, take the following steps to configure and enable these rules.
Fusion for emerging threats uses alerts generated by any scheduled analytics rules that contain kill-chain (tactics) and entity mapping information. To ensure that Fusion can use an analytics rule's output to detect emerging threats:
Review entity mapping for these scheduled rules. Use the entity mapping configuration section to map parameters from your query results to Microsoft Sentinel-recognized entities. Because Fusion correlates alerts based on entities (such as user account or IP address), its ML algorithms can't perform alert matching without the entity information.
Review the tactics and techniques in your analytics rule details. The Fusion ML algorithm uses MITRE ATT&CK information for detecting multistage attacks, and the tactics and techniques you label the analytics rules with show up in the resulting incidents. Fusion calculations might be affected if incoming alerts are missing tactic information.
Fusion can also detect scenario-based threats by using rules based on the following scheduled analytics rule templates.
To enable the queries available as templates in the Analytics page, go to the Rule templates tab, select the rule name in the templates gallery, and select Create rule in the details pane.
- Cisco - firewall block but success logon to Microsoft Entra ID
- Fortinet - Beacon pattern detected
- IP with multiple failed Microsoft Entra logins successfully logs in to Palo Alto VPN
- Multiple Password Reset by user
- Rare application consent
- SharePointFileOperation via previously unseen IPs
- Suspicious Resource deployment
- Palo Alto Threat signatures from Unusual IP addresses
To add queries that aren't currently available as a rule template, see Create a custom analytics rule from scratch.
For more information, see Fusion Advanced Multistage Attack Detection Scenarios with Scheduled Analytics Rules.
Note
For the set of scheduled analytics rules used by Fusion, the ML algorithm does fuzzy matching for the KQL queries provided in the templates. Renaming the templates doesn't impact Fusion detections.
Next steps
Learn more about Fusion detections in Microsoft Sentinel.
If you're ready to investigate the incidents that are created for you, see the following tutorial: Investigate incidents with Microsoft Sentinel.