Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
The Azure CNI plugin enables per container/pod networking for stand-alone docker hosts and Kubernetes clusters. In this article, you learn how to install and configure the CNI plugin for a standalone Linux Docker host.
Prerequisites
- An Azure account with an active subscription. Create an account for trial.
Create a resource group
In the portal, search for and select Resource groups.
Select + Create.
In the Basics tab of Create a resource group, enter, or select the following information:
Setting Value Subscription Select your subscription. Resource group Enter test-rg. Region Select China North 3. Select Review + create.
Select Create.
Create a virtual network
The following procedure creates a virtual network with a resource subnet.
In the portal, search for and select Virtual networks.
On the Virtual networks page, select + Create.
On the Basics tab of Create virtual network, enter, or select the following information:
Setting Value Project details Subscription Select your subscription. Resource group Select test-rg. Instance details Name Enter vnet-1. Region Select China North 3. Select Next to proceed to the Security tab.
Select Next to proceed to the IP Addresses tab.
In the address space box in Subnets, select the default subnet.
In Edit subnet, enter or select the following information:
Setting Value Subnet details Subnet template Leave the default Default. Name Enter subnet-1. Starting address Leave the default of 10.0.0.0. Subnet size Leave the default of /24 (256 addresses). Select Save.
Select Review + create at the bottom of the screen, and when validation passes, select Create.
Deploy Azure Bastion
Azure Bastion uses your browser to connect to VMs in your virtual network over Secure Shell (SSH) or Remote Desktop Protocol (RDP) by using their private IP addresses. The VMs don't need public IP addresses, client software, or special configuration. For more information about Azure Bastion, see Azure Bastion.
Note
Hourly pricing starts from the moment that Bastion is deployed, regardless of outbound data usage. For more information, see Pricing and SKUs. If you're deploying Bastion as part of a tutorial or test, we recommend that you delete this resource after you finish using it.
In the search box at the top of the portal, enter Bastion. Select Bastions in the search results.
Select + Create.
In the Basics tab of Create a Bastion, enter, or select the following information:
Setting Value Project details Subscription Select your subscription. Resource group Select test-rg. Instance details Name Enter bastion. Region Select China North 3. Tier Select Developer. Configure virtual networks Virtual network Select vnet-1. Select Review + create.
Select Create.
It can take a few minutes for the Bastion host to deploy. You can continue with the steps while the Bastion host is deploying.
Create a virtual machine
In the search box at the top of the portal, enter Virtual machine. Select Virtual machines in the search results.
Select + Create then Azure virtual machine.
In Create a virtual machine enter, or select the following information in the Basics tab:
Setting Value Project details Subscription Select your subscription. Resource group Select test-rg. Instance details Virtual machine name Enter vm-1. Region Select (Asia) China North 3. Availability options Select No infrastructure redundancy required. Security type Select Standard. Image Select Ubuntu Server 24.04 LTS - x64 Gen2. VM architecture Leave the default of x64. Size Select a size. Administrator account Authentication type Select SSH public key. Username Enter a username. SSH public key source Select Generate new key pair. Key pair name Enter vm-1-key. Inbound port rules Public inbound ports Select None. Select Next: Disks then Next: Networking.
In the Networking tab, enter, or select the following information:
Setting Value Network interface Virtual network Select vnet-1. Subnet Select subnet-1 (10.0.0.0/24). Public IP Select None. Network interface (NIC) network security group Select Advanced. Configure network security group Select Create new.
In Name enter nsg-1.
Select OK.Leave the rest of the options at the defaults and select Review + create.
Select Create.
A Generate new key pair pop-up appears. Select Download private key and create resource.
The private key file downloads to your computer. Save the private key file to a known location on your computer. This key is used to connect to the virtual machine with Azure Bastion in a later step.
Add IP configuration
The Azure CNI plugin allocates IP addresses to containers based on a pool of IP addresses you create on the virtual network interface of the virtual machine. For every container on the host, an IP configuration must exist on the virtual network interface. If the number of containers on the server outnumber the IP configurations on the virtual network interface, the container starts but doesn't have an IP address.
In this section, you add an IP configuration to the virtual network interface of the virtual machine you created previously.
In the search box at the top of the portal, enter Virtual machine. Select Virtual machines in the search results.
Select vm-1.
In Settings, select Networking.
Select the name of the network interface next to Network Interface:. The network interface is named vm-1 with a random number.
In Settings of the network interface, select IP configurations.
in IP configurations, select ipconfig1 in Name.
In the ipconfig1 settings, change the assignment of the private IP address from Dynamic to Static.
Select Save.
Return to IP configurations.
Select + Add.
Enter or select the following information for Add IP configuration:
Setting Value Name Enter ipconfig-2. Private IP address settings Allocation Select Static. IP address Enter 10.0.0.5. Select OK.
Verify ipconfig-2 has been added as a secondary IP configuration.
Repeat the previous steps to add as many configurations as containers you wish to deploy on the container host.
Install Docker
The Docker container engine must be installed and configured on the virtual machine you created previously.
Sign-in to the virtual machine you created previously with the Azure Bastion host you deployed with the virtual network.
In the search box at the top of the portal, enter Virtual machine. Select Virtual machines in the search results.
Select vm-1.
In the Overview of vm-1, select Connect then Connect via Bastion.
In the Bastion connection page, enter or select the following information:
Setting Value Authentication Type Select SSH Private Key from Local File. Username Enter the username you created. Local File Select the vm-1-key private key file you downloaded. Select Connect.
For install instructions for Docker on an Ubuntu container host, see Install Docker Engine on Ubuntu.
After Docker is installed on the virtual machine, follow the instructions for the Linux post install. For instructions on the Linux post install, see Docker Engine post-installation steps.
After Docker is installed on your virtual machine, continue with the steps in this article.
Install CNI plugin and create a test container
The Azure CNI plugin is maintained as a GitHub project and is available for download from the project's GitHub page. For this article, you use git within the virtual machine to clone the repository for the plugin and then install and configure the plugin.
For more information about the Azure CNI plugin, see Azure Container Networking.
In the search box at the top of the portal, enter Virtual machine. Select Virtual machines in the search results.
Select vm-1.
In the Overview of vm-1, select Connect then Connect via Bastion.
In the Bastion connection page, enter or select the following information:
Setting Value Authentication Type Select SSH Private Key from Local File. Username Enter the username you created. Local File Select the vm-1-key private key file you downloaded. Select Connect.
The application jq is required for the install script for the CNI plugin, use the following example to install the application:
sudo apt-get update sudo apt-get install jqNext, you clone the repository for the CNI plugin. Use the following example to clone the repository:
git clone https://github.com/Azure/azure-container-networking.gitConfigure permissions and install the CNI plugin. The install script command requires a version number for the CNI plugin. At the time of the writing of this article, the newest version is
v1.4.39. To obtain the latest version number of the plugin or previous versions, see Releases.cd ./azure-container-networking/scripts chmod u+x install-cni-plugin.sh sudo ./install-cni-plugin.sh v1.4.39 chmod u+x docker-run.shTo start a container with the CNI plugin, you must use a special script that comes with the plugin to create and start the container. The following example creates an Alpine container with the CNI plugin script:
sudo ./docker-run.sh vnetdocker1 default alpineTo verify that the container received the IP address you previously configured, connect to the container and view the IP:
sudo docker exec -it vnetdocker1 /bin/shUse the
ifconfigcommand in the following example to verify the IP address was assigned to the container:ifconfig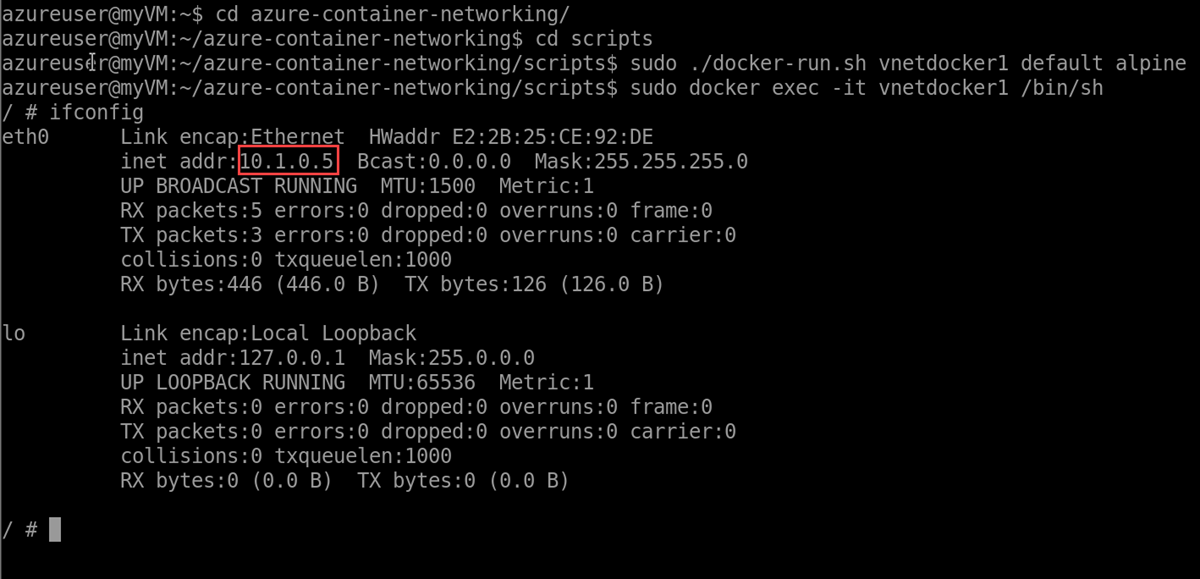
Clean up resources
When you finish using the resources that you created, you can delete the resource group and all its resources:
In the Azure portal, search for and select Resource groups.
On the Resource groups page, select the test-rg resource group.
On the test-rg page, select Delete resource group.
Enter test-rg in Enter resource group name to confirm deletion, and then select Delete.
Next steps
In this article, you learned how to install the Azure CNI plugin and create a test container.
For more information about Azure container networking and Azure Kubernetes service, see: