Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
An Azure Virtual Machine (VM) has one or more network interfaces (NIC) attached to it. Any NIC can have one or more static or dynamic public and private IP addresses assigned to it.
Assigning multiple IP addresses to a VM enables the following capabilities:
Hosting multiple websites or services with different IP addresses and TLS/SSL certificates on a single server.
Serve as a network virtual appliance, such as a firewall or load balancer.
The ability to add any of the private IP addresses for any of the NICs to an Azure Load Balancer back-end pool. In the past, only the primary IP address for the primary NIC could be added to a back-end pool. For more information about load balancing multiple IP configurations, see Load balancing multiple IP configurations.
Every NIC attached to a VM has one or more IP configurations associated to it. Each configuration is assigned one static or dynamic private IP address. Each configuration may also have one public IP address resource associated to it. To learn more about IP addresses in Azure, see IP addresses in Azure.
Note
All IP configurations on a single NIC must be associated to the same subnet. If multiple IPs on different subnets are desired, multiple NICs on a VM can be used. To learn more about multiple NICs on a VM in Azure, see Create VM with Multiple NICs.
There's a limit to how many private IP addresses can be assigned to a NIC. There's also a limit to how many public IP addresses that can be used in an Azure subscription. See Azure limits for details.
This article explains how to add multiple IP addresses to a virtual machine using the Azure CLI.
Prerequisites
An Azure account with an active subscription. Create an account for trial.
If you prefer to run CLI reference commands locally, install the Azure CLI. If you're running on Windows or macOS, consider running Azure CLI in a Docker container. For more information, see How to run the Azure CLI in a Docker container.
If you're using a local installation, sign in to the Azure CLI by using the az login command. To finish the authentication process, follow the steps displayed in your terminal. For other sign-in options, see Sign in with the Azure CLI.
When you're prompted, install the Azure CLI extension on first use. For more information about extensions, see Use extensions with the Azure CLI.
Run az version to find the version and dependent libraries that are installed. To upgrade to the latest version, run az upgrade.
This tutorial requires version 2.0.28 or later of the Azure CLI.
Note
Though the steps in this article assigns all IP configurations to a single NIC, you can also assign multiple IP configurations to any NIC in a multi-NIC VM. To learn how to create a VM with multiple NICs, see Create a VM with multiple NICs.
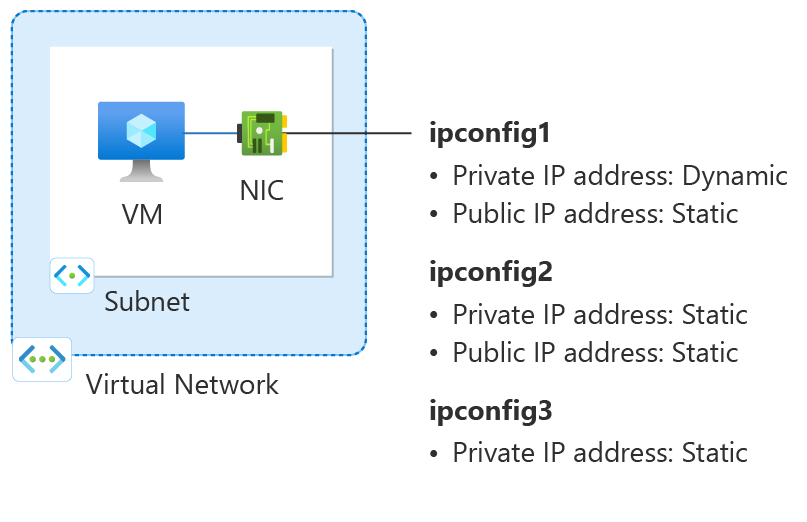
Figure: Diagram of network configuration resources created in this How-to article.
Create a resource group
An Azure resource group is a logical container into which Azure resources are deployed and managed.
Create a resource group with az group create named myResourceGroup in the chinanorth3 location.
az group create \
--name myResourceGroup \
--location chinanorth3
Create a virtual network
In this section, you create a virtual network for the virtual machine.
Use az network vnet create to create a virtual network.
az network vnet create \
--resource-group myResourceGroup \
--location chinanorth3 \
--name myVNet \
--address-prefixes 10.1.0.0/16 \
--subnet-name myBackendSubnet \
--subnet-prefixes 10.1.0.0/24
Create public IP addresses
Use az network public-ip create to create two public IP addresses.
az network public-ip create \
--resource-group myResourceGroup \
--name myPublicIP-1 \
--sku Standard \
--version IPv4 \
--zone 1 2 3
az network public-ip create \
--resource-group myResourceGroup \
--name myPublicIP-2 \
--sku Standard \
--version IPv4 \
--zone 1 2 3
Create a network security group
In this section, you create a network security group for the virtual machine and virtual network.
Use az network nsg create to create the network security group.
az network nsg create \
--resource-group myResourceGroup \
--name myNSG
Note
The default rules of the network security group block all inbound access from the internet, including SSH. To connect to the virtual machine, use Azure Bastion. For more information, see Quickstart: Deploy Azure Bastion with default settings.
Create a network interface
You use az network nic create to create the network interface for the virtual machine. The public IP addresses and the NSG created previously are associated with the NIC. The network interface is attached to the virtual network you created previously.
az network nic create \
--resource-group myResourceGroup \
--name myNIC1 \
--private-ip-address-version IPv4 \
--vnet-name myVNet \
--subnet myBackEndSubnet \
--network-security-group myNSG \
--public-ip-address myPublicIP-1
Create secondary private and public IP configuration
Use az network nic ip-config create to create the secondary private and public IP configuration for the NIC. Replace 10.1.0.5 with your secondary private IP address.
az network nic ip-config create \
--resource-group myResourceGroup \
--name ipconfig2 \
--nic-name myNIC1 \
--private-ip-address 10.1.0.5 \
--private-ip-address-version IPv4 \
--vnet-name myVNet \
--subnet myBackendSubnet \
--public-ip-address myPublicIP-2
Create tertiary private IP configuration
Use az network nic ip-config create to create the tertiary private IP configuration for the NIC. Replace 10.1.0.6 with your secondary private IP address.
az network nic ip-config create \
--resource-group myResourceGroup \
--name ipconfig3 \
--nic-name myNIC1 \
--private-ip-address 10.1.0.6 \
--private-ip-address-version IPv4 \
--vnet-name myVNet \
--subnet myBackendSubnet
Note
When adding a static IP address, you must specify an unused, valid address on the subnet the NIC is connected to.
Create a virtual machine
Use az vm create to create the virtual machine.
az vm create \
--resource-group myResourceGroup \
--name myVM \
--nics myNIC1 \
--image Ubuntu2204 \
--admin-username azureuser \
--authentication-type ssh \
--generate-ssh-keys
Add IP addresses to a VM operating system
Connect and sign in to a VM you created with multiple private IP addresses. You must manually add all the private IP addresses, including the primary, that you added to the VM. Complete the following steps for your VM operating system.
Windows Server
Expand
Open a command prompt or PowerShell.
Enter
ipconfig /allat the command line. You see the Primary private IP address that was assigned through DHCP.Enter
ncpa.cplat the command line to open the Network Connections configuration.Open the Properties for the network adapter assigned the new IP addresses.
Double-click Internet Protocol Version 4 (TCP/IPv4).
Select Use the following IP address:. Enter the following values.
Setting Value IP address: Enter the Primary private IP address. Subnet mask: Enter a subnet mask based on your IP address.
For example, if the subnet is a /24 subnet then the subnet mask is 255.255.255.0.Default gateway: The first IP address in the subnet.
If your subnet is 10.0.0.0/24, then the gateway IP address is 10.0.0.1.Select Use the following DNS server addresses:. Enter the following values.
Setting Value Preferred DNS server: Enter your primary DNS server.
Enter the IP address of 168.63.129.16 to use the default Azure provided DNS.Select the Advanced button.
Select Add.
Enter the private IP address you added to the Azure network interface. Enter the corresponding Subnet mask. Select Add.
Repeat the previous steps to add any more private IP addresses that you added to the Azure network interface.
Important
You should never manually assign the public IP address assigned to an Azure virtual machine within the virtual machine's operating system. When you manually set the IP address within the operating system, ensure that it's the same address as the private IP address assigned to the Azure network interface. Failure to assign the address correctly can cause loss of connectivity to the virtual machine. For more information, see Change IP address settings.
For more information about private IP addresses, see Private IP address.
Select OK to close the secondary IP address settings.
Select OK to close the adapter settings. Your RDP connection re-establishes.
Open a command prompt or PowerShell.
Enter
ipconfig /allat the command line.Verify the primary and secondary private IP addresses are present in the configuration.
PS C:\Users\azureuser> ipconfig /all Windows IP Configuration Host Name . . . . . . . . . . . . : myVM Primary Dns Suffix . . . . . . . : Node Type . . . . . . . . . . . . : Hybrid IP Routing Enabled. . . . . . . . : No WINS Proxy Enabled. . . . . . . . : No Ethernet adapter Ethernet: Connection-specific DNS Suffix . : Description . . . . . . . . . . . : Microsoft Hyper-V Network Adapter Physical Address. . . . . . . . . : 00-0D-3A-E6-CE-A3 DHCP Enabled. . . . . . . . . . . : No Autoconfiguration Enabled . . . . : Yes Link-local IPv6 Address . . . . . : fe80::a8d1:11d5:3ab2:6a51%5(Preferred) IPv4 Address. . . . . . . . . . . : 10.1.0.4(Preferred) Subnet Mask . . . . . . . . . . . : 255.255.255.0 IPv4 Address. . . . . . . . . . . : 10.1.0.5(Preferred) Subnet Mask . . . . . . . . . . . : 255.255.255.0 IPv4 Address. . . . . . . . . . . : 10.1.0.6(Preferred) Subnet Mask . . . . . . . . . . . : 255.255.255.0 Default Gateway . . . . . . . . . : 10.1.0.1 DHCPv6 IAID . . . . . . . . . . . : 100666682 DHCPv6 Client DUID. . . . . . . . : 00-01-00-01-2A-A8-26-B1-00-0D-3A-E6-CE-A3 DNS Servers . . . . . . . . . . . : 168.63.129.16 NetBIOS over Tcpip. . . . . . . . : EnabledEnsure the primary private IP address used in windows is the same as the primary IP address of the Azure VM network interface. For more information, see No Internet access from Azure Windows VM that has multiple IP addresses.
Validation (Windows Server)
To validate connectivity to the internet from the secondary IP configuration via the public IP, use the following command. Replace 10.1.0.5 with the secondary private IP address you added to the Azure VM network interface.
ping -S 10.1.0.5 outlook.com
Note
For secondary IP configurations, you can ping to the Internet if the configuration has a public IP address associated with it. For primary IP configurations, a public IP address isn't required to ping to the Internet.
SUSE Linux Enterprise and openSUSE
Expand
SUSE-based distributions use thecloud-netconfig plugin from the cloud-netconfig-azure package to manage the IP configuration. No manual steps are required on the part of the administrator. The first IP address of an interface set on the platform is assigned via DHCP. The cloud-netconfig plugin then probes the Azure Instance Metadata Service API continuously (once per minute) for more IP addresses assigned to the interface and adds/removes them as secondary IP addresses automatically.
This plugin should be installed and enabled on new images by default. Configuration steps for old workloads can be found here: https://www.suse.com/c/multi-nic-cloud-netconfig-ec2-azure/.
Ubuntu 14/16
Expand
We recommend looking at the latest documentation for your Linux distribution.
Open a terminal window.
Ensure you're the root user. If you aren't, enter the following command:
sudo -iUpdate the configuration file of the network interface (assuming ‘eth0’).
Keep the existing line item for dhcp. The primary IP address remains configured as it was previously.
Add a configuration for another static IP address with the following commands:
cd /etc/network/interfaces.d/ lsYou should see a .cfg file.
Open the file. You should see the following lines at the end of the file:
auto eth0 iface eth0 inet dhcpAdd the following lines after the lines that exist in the file. Replace
10.1.0.5with your private IP address and subnet mask.iface eth0 inet static address 10.1.0.5 netmask 255.255.255.0To add other private IP addresses, edit the file and add the new private IP addresses on subsequent lines:
iface eth0 inet static address 10.1.0.5 netmask 255.255.255.0 iface eth0 inet static address 10.1.0.6 netmask 255.255.255.0Save the file by using the following command:
:wqReset the network interface with the following command:
ifdown eth0 && ifup eth0Important
Execute both ifdown and ifup in the same line if using a remote connection.
Verify the IP address is added to the network interface with the following command:
ip addr list eth0You should see the IP address you added as part of the list. Example:
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc mq state UP group default qlen 1000 link/ether 00:0d:3a:04:45:16 brd ff:ff:ff:ff:ff:ff inet 10.1.0.5/24 brd 10.1.0.255 scope global eth0 valid_lft forever preferred_lft forever inet 10.1.0.6/24 brd 10.1.0.255 scope global secondary eth0 valid_lft forever preferred_lft forever inet 10.1.0.4/24 brd 10.1.0.255 scope global secondary eth0 valid_lft forever preferred_lft forever inet6 fe80::20d:3aff:fe04:4516/64 scope link valid_lft forever preferred_lft forever
Validation (Ubuntu 14/16)
To ensure you're able to connect to the internet from your secondary IP configuration via the public IP associated with it, use the following command:
ping -I 10.1.0.5 outlook.com
Note
For secondary IP configurations, you can only ping to the Internet if the configuration has a public IP address associated with it. For primary IP configurations, a public IP address isn't required to ping to the Internet.
For Linux VMs, when attempting to validate outbound connectivity from a secondary NIC, you may need to add appropriate routes. See appropriate documentation for your Linux distribution. The following method to accomplish this goal:
echo 150 custom >> /etc/iproute2/rt_tables
ip rule add from 10.1.0.5 lookup custom
ip route add default via 10.1.0.1 dev eth2 table custom
Ensure to replace:
10.1.0.5 with the private IP address that has a public IP address associated to it
10.1.0.1 to your default gateway
eth2 to the name of your secondary NIC
Ubuntu 18.04+
Expand
Starting on 18.04, netplan is used in Ubuntu for network management. We recommend looking at the latest documentation for your Linux distribution.
Open a terminal window.
Ensure you're the root user. If you are not, enter the following command:
sudo -iCreate a file for the second interface and open it in a text editor:
vi /etc/netplan/60-static.yamlAdd the following lines to the file, replacing
10.1.0.5/24with your IP and subnet mask:network: version: 2 ethernets: eth0: addresses: - 10.1.0.5/24To add private IP addresses, edit the file and add the new private IP addresses on subsequent lines:
network: version: 2 ethernets: eth0: addresses: - 10.1.0.5/24 - 10.1.0.6/24Save the file by using the following command:
:wqTest the changes with netplan try to confirm syntax:
netplan tryNote
netplan trywill apply the changes temporarily and roll back the changes after 120 seconds. If there's a loss of connectivity, wait 2 minutes, and then reconnect. At that time, the changes will have been rolled back.Assuming no issues with
netplan try, apply the configuration changes:netplan applyVerify the IP address is added to the network interface with the following command:
ip addr list eth0You should see the IP address you added as part of the list. Example:
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc mq state UP group default qlen 1000 link/ether 00:0d:3a:04:45:16 brd ff:ff:ff:ff:ff:ff inet 10.1.0.5/24 brd 10.1.0.255 scope global eth0 valid_lft forever preferred_lft forever inet 10.1.0.6/24 brd 10.1.0.255 scope global secondary eth0 valid_lft forever preferred_lft forever inet 10.1.0.4/24 brd 10.1.0.255 scope global secondary eth0 valid_lft forever preferred_lft forever inet6 fe80::20d:3aff:fe04:4516/64 scope link valid_lft forever preferred_lft forever
Validation (Ubuntu 18.04+)
To ensure you're able to connect to the internet from your secondary IP configuration via the public IP associated with it, use the following command:
ping -I 10.1.0.5 outlook.com
Note
For secondary IP configurations, you can only ping to the Internet if the configuration has a public IP address associated with it. For primary IP configurations, a public IP address isn't required to ping to the Internet.
For Linux VMs, when trying to validate outbound connectivity from a secondary NIC, you may need to add appropriate routes. Follow the appropriate documentation for your Linux distribution. The following method is one way to accomplish this goal:
echo 150 custom >> /etc/iproute2/rt_tables
ip rule add from 10.1.0.5 lookup custom
ip route add default via 10.1.0.1 dev eth2 table custom
Ensure you replace:
10.1.0.5 with the private IP address that has a public IP address associated to it
10.1.0.1 to your default gateway
eth2 to the name of your secondary NIC
Red Hat Enterprise Linux and others
Expand
Note
To configure the extra IP addresses in RHEL10.x, it's enough to restart NetworkManger with: systemctl restart NetworkManger.service or reboot the system. No other steps are required.
Open a terminal window.
Ensure you're the root user. If you aren't, enter the following command:
sudo -iEnter your password and follow instructions as prompted. Once you're the root user, go to the network scripts folder with the following command:
cd /etc/sysconfig/network-scriptsList the related ifcfg files using the following command:
ls ifcfg-*You should see ifcfg-eth0 as one of the files.
Create a new configuration file for each IP added to the system.
touch ifcfg-eth0:0Open the ifcfg-eth0:0 file with the following command:
vi ifcfg-eth0:0Add content to the file, eth0:0 in this case, with the following command. Replace
10.1.0.5with your new private IP address and subnet mask.DEVICE=eth0:0 BOOTPROTO=static ONBOOT=yes IPADDR=10.1.0.5 NETMASK=255.255.255.0Save the file with the following command:
:wqCreate a config file per IP address to add with their corresponding values:
touch ifcfg-eth0:1vi ifcfg-eth0:1DEVICE=eth0:1 BOOTPROTO=static ONBOOT=yes IPADDR=10.1.0.6 NETMASK=255.255.255.0:wqRestart the network services and make sure the changes are successful by running the following commands:
systemctl restart NetworkManager.service ifconfigYou should see the IP address or addresses you added in the list returned.
eth0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500 inet 10.1.0.4 netmask 255.255.255.0 broadcast 10.1.0.255 inet6 fe80::6245:bdff:fe7d:704a prefixlen 64 scopeid 0x20<link> ether 60:45:bd:7d:70:4a txqueuelen 1000 (Ethernet) RX packets 858 bytes 244215 (238.4 KiB) RX errors 0 dropped 0 overruns 0 frame 0 TX packets 1021 bytes 262077 (255.9 KiB) TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0 eth0:0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500 inet 10.1.0.5 netmask 255.255.255.0 broadcast 10.1.0.255 ether 60:45:bd:7d:70:4a txqueuelen 1000 (Ethernet) eth0:1: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500 inet 10.1.0.6 netmask 255.255.255.0 broadcast 10.1.0.255 ether 60:45:bd:7d:70:4a txqueuelen 1000 (Ethernet)
Validation (Red Hat and others)
To ensure you're able to connect to the internet from your secondary IP configuration via the public IP associated with it, use the following command:
ping -I 10.0.0.5 outlook.com
Note
For secondary IP configurations, you can only ping to the Internet if the configuration has a public IP address associated with it. For primary IP configurations, a public IP address isn't required to ping to the Internet.
For Linux VMs, when attempting to validate outbound connectivity from a secondary NIC, you may need to add appropriate routes. See the appropriate documentation for your Linux distribution. The following method to accomplish this goal:
echo 150 custom >> /etc/iproute2/rt_tables
ip rule add from 10.1.0.5 lookup custom
ip route add default via 10.1.0.1 dev eth2 table custom
Ensure to replace:
10.0.0.5 with the private IP address that has a public IP address associated to it
10.0.0.1 to your default gateway
eth2 to the name of your secondary NIC
Debian GNU/Linux
Expand
We recommend looking at the latest documentation for your Linux distribution.
Open a terminal window.
Ensure you're the root user. If you aren't, enter the following command:
sudo -iUpdate the configuration file of the network interface (assuming ‘eth0’).
Keep the existing line item for dhcp. The primary IP address remains configured as it was previously.
Add a configuration for each static IP address using the following commands:
cd /etc/network/interfaces.d/ lsYou should see a .cfg file.
Open the file. You should see the following lines at the end of the file:
auto eth0 iface eth0 inet dhcpAdd the following lines after the lines that exist in the file. Replace
10.1.0.5with your private IP address and subnet mask.iface eth0 inet static address 10.1.0.5 netmask 255.255.255.0Add the new IP addresses information in the configuration file:
iface eth0 inet static address 10.1.0.5 netmask 255.255.255.0 iface eth0 inet static address 10.1.0.6 netmask 255.255.255.0Save the file by using the following command:
:wqRestart networking services for the changes to take effect. For Debian 8 and above, use:
systemctl restart networkingFor prior versions of Debian, you can use below commands:
service networking restartVerify the IP address is added to the network interface with the following command:
ip addr list eth0You should see the IP address you added as part of the list. Example:
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc mq state UP group default qlen 1000 link/ether 00:0d:3a:04:45:16 brd ff:ff:ff:ff:ff:ff inet 10.1.0.5/24 brd 10.1.0.255 scope global eth0 valid_lft forever preferred_lft forever inet 10.1.0.6/24 brd 10.1.0.255 scope global secondary eth0 valid_lft forever preferred_lft forever inet 10.1.0.4/24 brd 10.1.0.255 scope global secondary eth0 valid_lft forever preferred_lft forever inet6 fe80::20d:3aff:fe04:4516/64 scope link valid_lft forever preferred_lft forever
Validation (Debian GNU/Linux)
To ensure you're able to connect to the internet from your secondary IP configuration via the public IP associated with it, use the following command:
ping -I 10.1.0.5 outlook.com
Note
For secondary IP configurations, you can only ping to the Internet if the configuration has a public IP address associated with it. For primary IP configurations, a public IP address isn't required to ping to the Internet.
For Linux VMs, when attempting to validate outbound connectivity from a secondary NIC, you may need to add appropriate routes. See appropriate documentation for your Linux distribution. The following method to accomplish this goal:
echo 150 custom >> /etc/iproute2/rt_tables
ip rule add from 10.1.0.5 lookup custom
ip route add default via 10.1.0.1 dev eth2 table custom
Ensure to replace:
10.1.0.5 with the private IP address that has a public IP address associated to it
10.1.0.1 to your default gateway
eth2 to the name of your secondary NIC
Next steps
- Learn more about public IP addresses in Azure.
- Learn more about private IP addresses in Azure.
- Learn how to Configure IP addresses for an Azure network interface.