常见的警报架构会在 Azure 中标准化警报通知的使用体验。 过去,活动日志、指标和日志搜索警报都有自己的电子邮件模板和 Webhook 架构。 通用警报架构为所有警报通知提供一个标准化架构。
标准化架构有助于最大限度地减少集成数,从而简化管理和维护集成的过程。
通用架构在以下部分中包含有关受影响资源和警报原因的信息:
概要:标准化字段,由描述受警报影响的资源和常见警报元数据(如严重性或说明)的所有警报类型使用。
如果要基于资源组等条件将警报实例路由到特定团队,可使用“概要”部分中的字段为所有警报类型提供路由逻辑。 然后,接收警报通知的团队可以使用上下文信息字段对其进行调查。
警报上下文:根据警报类型而变化的字段。 警报上下文字段描述警报的原因。 例如,指标警报将在警报上下文中包含指标名称和指标值等字段。 活动日志警报将包含有关生成警报的事件的信息。
自定义属性:如果已为指标警报规则配置了操作组,则可以通过添加自定义属性向警报有效负载中添加更多信息。
注释
自定义属性目前仅受指标警报支持。 对于所有其他警报类型,“自定义属性”字段为 null。
示例警报有效负载
{
"schemaId": "azureMonitorCommonAlertSchema",
"data": {
"essentials": {
"alertId": "/subscriptions/<subscription ID>/providers/Microsoft.AlertsManagement/alerts/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e",
"alertRule": "WCUS-R2-Gen2",
"severity": "Sev3",
"signalType": "Metric",
"monitorCondition": "Resolved",
"monitoringService": "Platform",
"alertTargetIDs": [
"/subscriptions/<subscription ID>/resourcegroups/pipelinealertrg/providers/microsoft.compute/virtualmachines/wcus-r2-gen2"
],
"configurationItems": [
"wcus-r2-gen2"
],
"originAlertId": "3f2d4487-b0fc-4125-8bd5-7ad17384221e_PipeLineAlertRG_microsoft.insights_metricAlerts_WCUS-R2-Gen2_-117781227",
"firedDateTime": "2019-03-22T13:58:24.3713213Z",
"resolvedDateTime": "2019-03-22T14:03:16.2246313Z",
"description": "",
"essentialsVersion": "1.0",
"alertContextVersion": "1.0"
},
"alertContext": {
"properties": null,
"conditionType": "SingleResourceMultipleMetricCriteria",
"condition": {
"windowSize": "PT5M",
"allOf": [
{
"metricName": "Percentage CPU",
"metricNamespace": "Microsoft.Compute/virtualMachines",
"operator": "GreaterThan",
"threshold": "25",
"timeAggregation": "Average",
"dimensions": [
{
"name": "ResourceId",
"value": "b1b1b1b1-cccc-dddd-eeee-f2f2f2f2f2f2"
}
],
"metricValue": 7.727
}
]
}
}
}
}
指标警报示例
以下是指标警报有效负载示例。
具有静态阈值且 monitoringService = Platform 的指标警报
{
"alertContext": {
"properties": null,
"conditionType": "SingleResourceMultipleMetricCriteria",
"condition": {
"windowSize": "PT5M",
"allOf": [
{
"metricName": "Percentage CPU",
"metricNamespace": "Microsoft.Compute/virtualMachines",
"operator": "GreaterThan",
"threshold": "25",
"timeAggregation": "Average",
"dimensions": [
{
"name": "ResourceId",
"value": "b1b1b1b1-cccc-dddd-eeee-f2f2f2f2f2f2"
}
],
"metricValue": 31.1105
}
],
"windowStartTime": "2019-03-22T13:40:03.064Z",
"windowEndTime": "2019-03-22T13:45:03.064Z"
}
}
}
具有动态阈值且 monitoringService = Platform 的指标警报
{
"alertContext": {
"properties": null,
"conditionType": "DynamicThresholdCriteria",
"condition": {
"windowSize": "PT5M",
"allOf": [
{
"alertSensitivity": "High",
"failingPeriods": {
"numberOfEvaluationPeriods": 1,
"minFailingPeriodsToAlert": 1
},
"ignoreDataBefore": null,
"metricName": "Egress",
"metricNamespace": "microsoft.storage/storageaccounts",
"operator": "GreaterThan",
"threshold": "47658",
"timeAggregation": "Total",
"dimensions": [],
"metricValue": 50101
}
],
"windowStartTime": "2021-07-20T05:07:26.363Z",
"windowEndTime": "2021-07-20T05:12:26.363Z"
}
}
}
可用性测试的指标警报,并且 monitoringService = Platform
{
"alertContext": {
"properties": null,
"conditionType": "WebtestLocationAvailabilityCriteria",
"condition": {
"windowSize": "PT5M",
"allOf": [
{
"metricName": "Failed Location",
"metricNamespace": null,
"operator": "GreaterThan",
"threshold": "2",
"timeAggregation": "Sum",
"dimensions": [],
"metricValue": 5,
"webTestName": "myAvailabilityTest-myApplication"
}
],
"windowStartTime": "2019-03-22T13:40:03.064Z",
"windowEndTime": "2019-03-22T13:45:03.064Z"
}
}
}
示例日志搜索警报
注释
启用通用架构时,有效负载中的字段将重置为通用架构字段。 因此,日志搜索警报在通用架构方面具有以下限制:
- 使用 WebHook 进行日志搜索警报时,如果自定义了电子邮件主题和/或 JSON 有效负载,则不支持通用架构,因为通用架构会覆盖这些自定义配置。
- 对于使用通用架构的警报,每个警报的大小上限为 256KB。 如果日志搜索警报有效负载包含导致警报超过大小上限的搜索结果,则搜索结果不会嵌入到日志搜索警报有效负载中。 可检查有效负载是否包含带
IncludedSearchResults标志的搜索结果。 如果搜索结果不被包含,请使用LinkToFilteredSearchResultsAPI或LinkToSearchResultsAPI通过 Log Analytics API 来访问查询结果。
monitoringService = Platform 的日志搜索警报
{
"alertContext": {
"SearchQuery": "Perf | where ObjectName == \"Processor\" and CounterName == \"% Processor Time\" | summarize AggregatedValue = avg(CounterValue) by bin(TimeGenerated, 5m), Computer",
"SearchIntervalStartTimeUtc": "3/22/2019 1:36:31 PM",
"SearchIntervalEndtimeUtc": "3/22/2019 1:51:31 PM",
"ResultCount": 2,
"LinkToSearchResults": "https://portal.azure.cn/#Analyticsblade/search/index?_timeInterval.intervalEnd=2018-03-26T09%3a10%3a40.0000000Z&_timeInterval.intervalDuration=3600&q=Usage",
"LinkToFilteredSearchResultsUI": "https://portal.azure.cn/#Analyticsblade/search/index?_timeInterval.intervalEnd=2018-03-26T09%3a10%3a40.0000000Z&_timeInterval.intervalDuration=3600&q=Usage",
"LinkToSearchResultsAPI": "https://api.loganalytics.io/v1/workspaces/workspaceID/query?query=Heartbeat×pan=2020-05-07T18%3a11%3a51.0000000Z%2f2020-05-07T18%3a16%3a51.0000000Z",
"LinkToFilteredSearchResultsAPI": "https://api.loganalytics.io/v1/workspaces/workspaceID/query?query=Heartbeat×pan=2020-05-07T18%3a11%3a51.0000000Z%2f2020-05-07T18%3a16%3a51.0000000Z",
"SeverityDescription": "Warning",
"WorkspaceId": "a0a0a0a0-bbbb-cccc-dddd-e1e1e1e1e1e1",
"SearchIntervalDurationMin": "15",
"AffectedConfigurationItems": [
"INC-Gen2Alert"
],
"SearchIntervalInMinutes": "15",
"Threshold": 10000,
"Operator": "Less Than",
"Dimensions": [
{
"name": "Computer",
"value": "INC-Gen2Alert"
}
],
"SearchResults": {
"tables": [
{
"name": "PrimaryResult",
"columns": [
{
"name": "$table",
"type": "string"
},
{
"name": "Computer",
"type": "string"
},
{
"name": "TimeGenerated",
"type": "datetime"
}
],
"rows": [
[
"Fabrikam",
"33446677a",
"2018-02-02T15:03:12.18Z"
],
[
"Contoso",
"33445566b",
"2018-02-02T15:16:53.932Z"
]
]
}
],
"dataSources": [
{
"resourceId": "/subscriptions/bbbb1b1b-cc2c-dd3d-ee4e-ffffff5f5f5f/resourcegroups/test/providers/microsoft.operationalinsights/workspaces/test",
"tables": [
"Heartbeat"
]
}
]
},
"IncludedSearchResults": "True",
"AlertType": "Metric measurement"
}
}
monitoringService = Application Insights 的日志搜索警报
{
"alertContext": {
"SearchQuery": "requests | where resultCode == \"500\" | summarize AggregatedValue = Count by bin(Timestamp, 5m), IP",
"SearchIntervalStartTimeUtc": "3/22/2019 1:36:33 PM",
"SearchIntervalEndtimeUtc": "3/22/2019 1:51:33 PM",
"ResultCount": 2,
"LinkToSearchResults": "https://portal.azure.cn/AnalyticsBlade/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/?query=search+*+&timeInterval.intervalEnd=2018-03-26T09%3a10%3a40.0000000Z&_timeInterval.intervalDuration=3600&q=Usage",
"LinkToFilteredSearchResultsUI": "https://portal.azure.cn/AnalyticsBlade/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/?query=search+*+&timeInterval.intervalEnd=2018-03-26T09%3a10%3a40.0000000Z&_timeInterval.intervalDuration=3600&q=Usage",
"LinkToSearchResultsAPI": "https://api.applicationinsights.io/v1/apps/0MyAppId0/metrics/requests/count",
"LinkToFilteredSearchResultsAPI": "https://api.applicationinsights.io/v1/apps/0MyAppId0/metrics/requests/count",
"SearchIntervalDurationMin": "15",
"SearchIntervalInMinutes": "15",
"Threshold": 10000.0,
"Operator": "Less Than",
"ApplicationId": "00001111-aaaa-2222-bbbb-3333cccc4444",
"Dimensions": [
{
"name": "IP",
"value": "1.1.1.1"
}
],
"SearchResults": {
"tables": [
{
"name": "PrimaryResult",
"columns": [
{
"name": "$table",
"type": "string"
},
{
"name": "Id",
"type": "string"
},
{
"name": "Timestamp",
"type": "datetime"
}
],
"rows": [
[
"Fabrikam",
"33446677a",
"2018-02-02T15:03:12.18Z"
],
[
"Contoso",
"33445566b",
"2018-02-02T15:16:53.932Z"
]
]
}
],
"dataSources": [
{
"resourceId": "/subscriptions/cccc2c2c-dd3d-ee4e-ff5f-aaaaaa6a6a6a/resourcegroups/test/providers/microsoft.operationalinsights/workspaces/test",
"tables": [
"Heartbeat"
]
}
]
},
"IncludedSearchResults": "True",
"AlertType": "Metric measurement"
}
}
monitoringService = Log Alerts V2 的日志搜索警报
注释
API 版本 2020-05-01 中的日志搜索警报规则使用此有效负载类型,该类型仅支持通用架构。 使用此版本时,搜索结果不会嵌入到日志搜索警报有效负载中。 使用维度来提供已触发警报的上下文。 还可以使用 LinkToFilteredSearchResultsAPI 或 LinkToSearchResultsAPI 通过 Log Analytics API 访问查询结果。 如果必须嵌入结果,请使用包含所提供链接的逻辑应用,以生成自定义有效负载。
{
"alertContext": {
"properties": {
"name1": "value1",
"name2": "value2"
},
"conditionType": "LogQueryCriteria",
"condition": {
"windowSize": "PT10M",
"allOf": [
{
"searchQuery": "Heartbeat",
"metricMeasureColumn": "CounterValue",
"targetResourceTypes": "['Microsoft.Compute/virtualMachines']",
"operator": "LowerThan",
"threshold": "1",
"timeAggregation": "Count",
"dimensions": [
{
"name": "Computer",
"value": "TestComputer"
}
],
"metricValue": 0.0,
"failingPeriods": {
"numberOfEvaluationPeriods": 1,
"minFailingPeriodsToAlert": 1
},
"linkToSearchResultsUI": "https://portal.azure.cn#@aaaabbbb-0000-cccc-1111-dddd2222eeee/blade/Microsoft_Azure_Monitoring_Logs/LogsBlade/source/Alerts.EmailLinks/scope/%7B%22resources%22%3A%5B%7B%22resourceId%22%3A%22%2Fsubscriptions%2aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e%2FresourceGroups%2FContoso%2Fproviders%2FMicrosoft.Compute%2FvirtualMachines%2FContoso%22%7D%5D%7D/q/eJzzSE0sKklKTSypUSjPSC1KVQjJzE11T81LLUosSU1RSEotKU9NzdNIAfJKgDIaRgZGBroG5roGliGGxlYmJlbGJnoGEKCpp4dDmSmKMk0A/prettify/1/timespan/2020-07-07T13%3a54%3a34.0000000Z%2f2020-07-09T13%3a54%3a34.0000000Z",
"linkToFilteredSearchResultsUI": "https://portal.azure.cn#@aaaabbbb-0000-cccc-1111-dddd2222eeee/blade/Microsoft_Azure_Monitoring_Logs/LogsBlade/source/Alerts.EmailLinks/scope/%7B%22resources%22%3A%5B%7B%22resourceId%22%3A%22%2Fsubscriptions%2aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e%2FresourceGroups%2FContoso%2Fproviders%2FMicrosoft.Compute%2FvirtualMachines%2FContoso%22%7D%5D%7D/q/eJzzSE0sKklKTSypUSjPSC1KVQjJzE11T81LLUosSU1RSEotKU9NzdNIAfJKgDIaRgZGBroG5roGliGGxlYmJlbGJnoGEKCpp4dDmSmKMk0A/prettify/1/timespan/2020-07-07T13%3a54%3a34.0000000Z%2f2020-07-09T13%3a54%3a34.0000000Z",
"linkToSearchResultsAPI": "https://api.loganalytics.io/v1/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/resourceGroups/Contoso/providers/Microsoft.Compute/virtualMachines/Contoso/query?query=Heartbeat%7C%20where%20TimeGenerated%20between%28datetime%282020-07-09T13%3A44%3A34.0000000%29..datetime%282020-07-09T13%3A54%3A34.0000000%29%29×pan=2020-07-07T13%3a54%3a34.0000000Z%2f2020-07-09T13%3a54%3a34.0000000Z",
"linkToFilteredSearchResultsAPI": "https://api.loganalytics.io/v1/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/resourceGroups/Contoso/providers/Microsoft.Compute/virtualMachines/Contoso/query?query=Heartbeat%7C%20where%20TimeGenerated%20between%28datetime%282020-07-09T13%3A44%3A34.0000000%29..datetime%282020-07-09T13%3A54%3A34.0000000%29%29×pan=2020-07-07T13%3a54%3a34.0000000Z%2f2020-07-09T13%3a54%3a34.0000000Z"
}
],
"windowStartTime": "2020-07-07T13:54:34Z",
"windowEndTime": "2020-07-09T13:54:34Z"
}
}
}
示例活动日志警报
具有 monitoringService = Activity Log - Administrative 的活动日志警报
{
"alertContext": {
"authorization": {
"action": "Microsoft.Compute/virtualMachines/restart/action",
"scope": "/subscriptions/<subscription ID>/resourceGroups/PipeLineAlertRG/providers/Microsoft.Compute/virtualMachines/WCUS-R2-ActLog"
},
"channels": "Operation",
"claims": "{\"aud\":\"https://management.core.chinacloudapi.cn/\",\"iss\":\"https://sts.chinacloudapi.cn/aaaabbbb-0000-cccc-1111-dddd2222eeee/\",\"iat\":\"1553260826\",\"nbf\":\"1553260826\",\"exp\":\"1553264726\",\"aio\":\"42JgYNjdt+rr+3j/dx68v018XhuFAwA=\",\"appid\":\"11112222-bbbb-3333-cccc-4444dddd5555\",\"appidacr\":\"2\",\"http://schemas.microsoft.com/identity/claims/identityprovider\":\"https://sts.chinacloudapi.cn/aaaabbbb-0000-cccc-1111-dddd2222eeee/\",\"http://schemas.microsoft.com/identity/claims/objectidentifier\":\"22223333-cccc-4444-dddd-5555eeee6666\",\"http://schemas.xmlsoap.org/ws/2005/05/identity/claims/nameidentifier\":\"22223333-cccc-4444-dddd-5555eeee6666\",\"http://schemas.microsoft.com/identity/claims/tenantid\":\"aaaabbbb-0000-cccc-1111-dddd2222eeee\",\"uti\":\"v5wYC9t9ekuA2rkZSVZbAA\",\"ver\":\"1.0\"}",
"caller": "22223333-cccc-4444-dddd-5555eeee6666",
"correlationId": "aaaa0000-bb11-2222-33cc-444444dddddd",
"eventSource": "Administrative",
"eventTimestamp": "2019-03-22T13:56:31.2917159+00:00",
"eventDataId": "bbbbcccc-1111-dddd-2222-eeee3333ffff",
"level": "Informational",
"operationName": "Microsoft.Compute/virtualMachines/restart/action",
"operationId": "aaaaaaaa-0000-1111-2222-bbbbbbbbbbbb",
"status": "Succeeded",
"subStatus": "",
"submissionTimestamp": "2019-03-22T13:56:54.067593+00:00"
}
}
具有 monitoringService = Activity Log - Policy 的活动日志警报
{
"alertContext": {
"authorization": {
"action": "Microsoft.Resources/checkPolicyCompliance/read",
"scope": "/subscriptions/<GUID>"
},
"channels": "Operation",
"claims": "{\"aud\":\"https://management.chinacloudapi.cn/\",\"iss\":\"https://sts.chinacloudapi.cn/<GUID>/\",\"iat\":\"1566711059\",\"nbf\":\"1566711059\",\"exp\":\"1566740159\",\"aio\":\"42FgYOhynHNw0scy3T/bL71+xLyqEwA=\",\"appid\":\"<GUID>\",\"appidacr\":\"2\",\"http://schemas.microsoft.com/identity/claims/identityprovider\":\"https://sts.chinacloudapi.cn/<GUID>/\",\"http://schemas.microsoft.com/identity/claims/objectidentifier\":\"<GUID>\",\"http://schemas.xmlsoap.org/ws/2005/05/identity/claims/nameidentifier\":\"<GUID>\",\"http://schemas.microsoft.com/identity/claims/tenantid\":\"<GUID>\",\"uti\":\"Miy1GzoAG0Scu_l3m1aIAA\",\"ver\":\"1.0\"}",
"caller": "<GUID>",
"correlationId": "<GUID>",
"eventSource": "Policy",
"eventTimestamp": "2019-08-25T11:11:34.2269098+00:00",
"eventDataId": "<GUID>",
"level": "Warning",
"operationName": "Microsoft.Authorization/policies/audit/action",
"operationId": "<GUID>",
"properties": {
"isComplianceCheck": "True",
"resourceLocation": "chinanorth2",
"ancestors": "<GUID>",
"policies": "[{\"policyDefinitionId\":\"/providers/Microsoft.Authorization/policyDefinitions/<GUID>/\",\"policySetDefinitionId\":\"/providers/Microsoft.Authorization/policySetDefinitions/<GUID>/\",\"policyDefinitionReferenceId\":\"vulnerabilityAssessmentMonitoring\",\"policySetDefinitionName\":\"<GUID>\",\"policyDefinitionName\":\"<GUID>\",\"policyDefinitionEffect\":\"AuditIfNotExists\",\"policyAssignmentId\":\"/subscriptions/<GUID>/providers/Microsoft.Authorization/policyAssignments/SecurityCenterBuiltIn/\",\"policyAssignmentName\":\"SecurityCenterBuiltIn\",\"policyAssignmentScope\":\"/subscriptions/<GUID>\",\"policyAssignmentSku\":{\"name\":\"A1\",\"tier\":\"Standard\"},\"policyAssignmentParameters\":{}}]"
},
"status": "Succeeded",
"subStatus": "",
"submissionTimestamp": "2019-08-25T11:12:46.1557298+00:00"
}
}
具有 monitoringService = Activity Log - Autoscale 的活动日志警报
{
"alertContext": {
"channels": "Admin, Operation",
"claims": "{\"http://schemas.xmlsoap.org/ws/2005/05/identity/claims/spn\":\"Microsoft.Insights/autoscaleSettings\"}",
"caller": "Microsoft.Insights/autoscaleSettings",
"correlationId": "<GUID>",
"eventSource": "Autoscale",
"eventTimestamp": "2019-08-21T16:17:47.1551167+00:00",
"eventDataId": "<GUID>",
"level": "Informational",
"operationName": "Microsoft.Insights/AutoscaleSettings/Scaleup/Action",
"operationId": "<GUID>",
"properties": {
"description": "The autoscale engine attempting to scale resource '/subscriptions/d<GUID>/resourceGroups/testRG/providers/Microsoft.Compute/virtualMachineScaleSets/testVMSS' from 9 instances count to 10 instances count.",
"resourceName": "/subscriptions/<GUID>/resourceGroups/voiceassistancedemo/providers/Microsoft.Compute/virtualMachineScaleSets/alexademo",
"oldInstancesCount": "9",
"newInstancesCount": "10",
"activeAutoscaleProfile": "{\r\n \"Name\": \"Auto created scale condition\",\r\n \"Capacity\": {\r\n \"Minimum\": \"1\",\r\n \"Maximum\": \"10\",\r\n \"Default\": \"1\"\r\n },\r\n \"Rules\": [\r\n {\r\n \"MetricTrigger\": {\r\n \"Name\": \"Percentage CPU\",\r\n \"Namespace\": \"microsoft.compute/virtualmachinescalesets\",\r\n \"Resource\": \"/subscriptions/<GUID>/resourceGroups/testRG/providers/Microsoft.Compute/virtualMachineScaleSets/testVMSS\",\r\n \"ResourceLocation\": \"chinanorth\",\r\n \"TimeGrain\": \"PT1M\",\r\n \"Statistic\": \"Average\",\r\n \"TimeWindow\": \"PT5M\",\r\n \"TimeAggregation\": \"Average\",\r\n \"Operator\": \"GreaterThan\",\r\n \"Threshold\": 0.0,\r\n \"Source\": \"/subscriptions/<GUID>/resourceGroups/testRG/providers/Microsoft.Compute/virtualMachineScaleSets/testVMSS\",\r\n \"MetricType\": \"MDM\",\r\n \"Dimensions\": [],\r\n \"DividePerInstance\": false\r\n },\r\n \"ScaleAction\": {\r\n \"Direction\": \"Increase\",\r\n \"Type\": \"ChangeCount\",\r\n \"Value\": \"1\",\r\n \"Cooldown\": \"PT1M\"\r\n }\r\n }\r\n ]\r\n}",
"lastScaleActionTime": "Wed, 21 Aug 2019 16:17:47 GMT"
},
"status": "Succeeded",
"submissionTimestamp": "2019-08-21T16:17:47.2410185+00:00"
}
}
具有 monitoringService = Activity Log - Security 的活动日志警报
{
"alertContext": {
"channels": "Operation",
"correlationId": "<GUID>",
"eventSource": "Security",
"eventTimestamp": "2019-08-26T08:34:14+00:00",
"eventDataId": "<GUID>",
"level": "Informational",
"operationName": "Microsoft.Security/locations/alerts/activate/action",
"operationId": "<GUID>",
"properties": {
"threatStatus": "Quarantined",
"category": "Virus",
"threatID": "2147519003",
"filePath": "C:\\AlertGeneration\\test.eicar",
"protectionType": "Windows Defender",
"actionTaken": "Blocked",
"resourceType": "Virtual Machine",
"severity": "Low",
"compromisedEntity": "testVM",
"remediationSteps": "[\"No user action is necessary\"]",
"attackedResourceType": "Virtual Machine"
},
"status": "Active",
"submissionTimestamp": "2019-08-26T09:28:58.3019107+00:00"
}
}
具有 monitoringService = ServiceHealth 的活动日志警报
{
"alertContext": {
"authorization": null,
"channels": 1,
"claims": null,
"caller": null,
"correlationId": "bbbb1111-cc22-3333-44dd-555555eeeeee",
"eventSource": 2,
"eventTimestamp": "2019-06-24T11:31:19.0312699+00:00",
"httpRequest": null,
"eventDataId": "<GUID>",
"level": 3,
"operationName": "Microsoft.ServiceHealth/maintenance/action",
"operationId": "<GUID>",
"properties": {
"title": "Azure Synapse Analytics Scheduled Maintenance Pending",
"service": "Azure Synapse Analytics",
"region": "China North",
"communication": "<MESSAGE>",
"incidentType": "Maintenance",
"trackingId": "<GUID>",
"impactStartTime": "2019-06-26T04:00:00Z",
"impactMitigationTime": "2019-06-26T12:00:00Z",
"impactedServices": "[{\"ImpactedRegions\":[{\"RegionName\":\"China North\"}],\"ServiceName\":\"Azure Synapse Analytics\"}]",
"impactedServicesTableRows": "<tr>\r\n<td align='center' style='padding: 5px 10px; border-right:1px solid black; border-bottom:1px solid black'>Azure Synapse Analytics</td>\r\n<td align='center' style='padding: 5px 10px; border-bottom:1px solid black'>China North<br></td>\r\n</tr>\r\n",
"defaultLanguageTitle": "Azure Synapse Analytics Scheduled Maintenance Pending",
"defaultLanguageContent": "<MESSAGE>",
"stage": "Planned",
"communicationId": "<GUID>",
"maintenanceId": "<GUID>",
"isHIR": "false",
"version": "0.1.1"
},
"status": "Active",
"subStatus": null,
"submissionTimestamp": "2019-06-24T11:31:31.7147357+00:00",
"ResourceType": null
}
}
具有 monitoringService = ResourceHealth 的活动日志警报
{
"alertContext": {
"channels": "Admin, Operation",
"correlationId": "<GUID>",
"eventSource": "ResourceHealth",
"eventTimestamp": "2019-06-24T15:42:54.074+00:00",
"eventDataId": "<GUID>",
"level": "Informational",
"operationName": "Microsoft.Resourcehealth/healthevent/Activated/action",
"operationId": "<GUID>",
"properties": {
"title": "This virtual machine is stopping and deallocating as requested by an authorized user or process",
"details": null,
"currentHealthStatus": "Unavailable",
"previousHealthStatus": "Available",
"type": "Downtime",
"cause": "UserInitiated"
},
"status": "Active",
"submissionTimestamp": "2019-06-24T15:45:20.4488186+00:00"
}
}
示例 Prometheus 警报
{
"alertContext": {
"interval": "PT1M",
"expression": "sql_up > 0",
"expressionValue": "0",
"for": "PT2M",
"labels": {
"Environment": "Prod",
"cluster": "myCluster1"
},
"annotations": {
"summary": "alert on SQL availability"
},
"ruleGroup": "/subscriptions/<subscription ID>/resourceGroups/myResourceGroup/providers/Microsoft.AlertsManagement/prometheusRuleGroups/myRuleGroup"
}
}
测试操作的示例有效负载
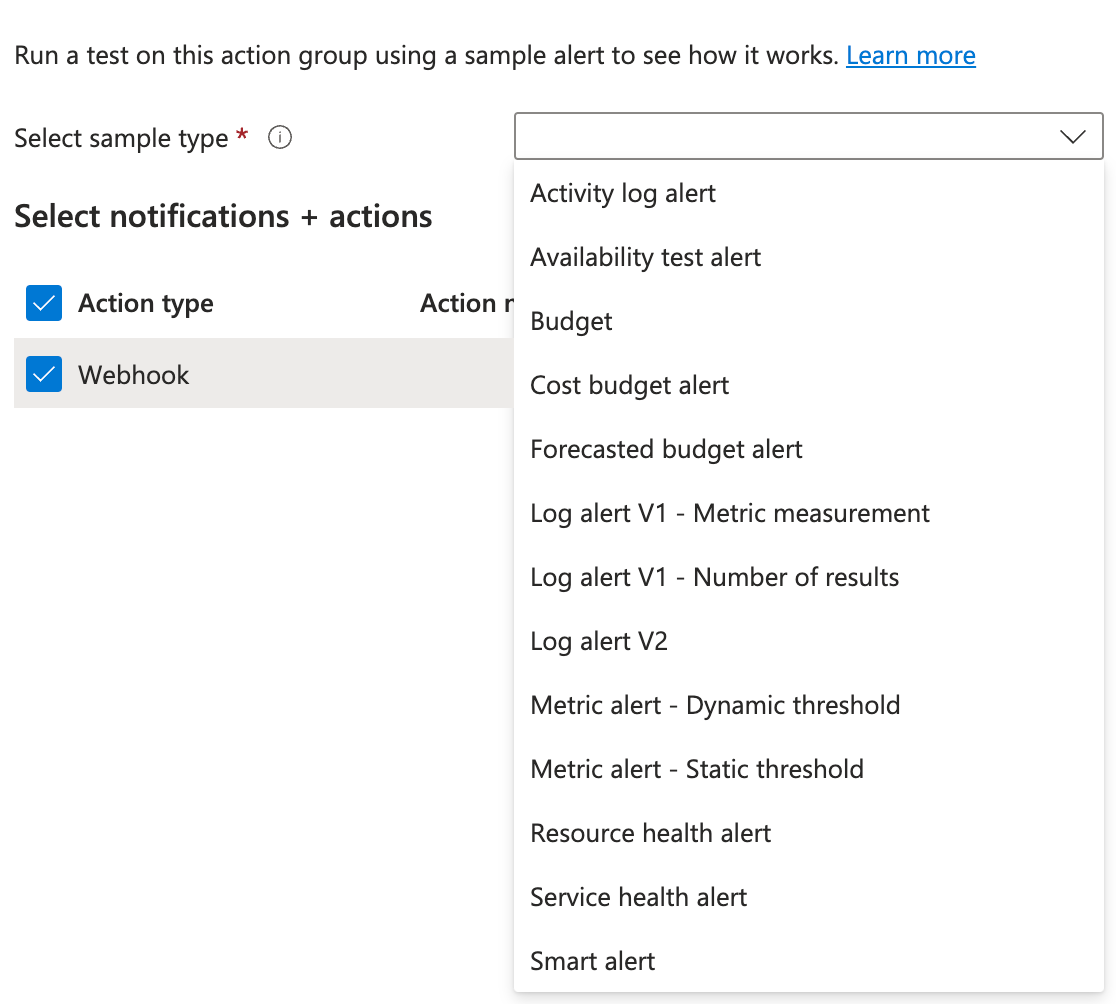
配置 Azure作组 以路由警报通知(例如,通过 Webhook、逻辑应用、Azure 函数或事件中心),请务必验证接收终结点是否可以处理 通用警报架构 有效负载结构。
Azure 提供 “测试作” 功能来模拟警报并将示例有效负载发送到配置的终结点。 这有助于验证集成,而无需触发实际资源条件。
本部分介绍在使用启用了通用警报架构的“测试作组”功能时发送的测试有效负载的结构和内容。
注释
测试有效负载模拟实际警报,但包含 模拟元数据 ,并不表示任何特定的资源或条件。
示例测试作 Activity log alert
{
"schemaId": "azureMonitorCommonAlertSchema",
"data": {
"essentials": {
"alertId": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/resourceGroups/test-RG/providers/microsoft.insights/activityLogAlerts/Test_Alert",
"alertRule": "test-activityLogAlertRule",
"severity": "Sev4",
"signalType": "Activity Log",
"monitorCondition": "Fired",
"monitoringService": "Activity Log - Administrative",
"alertTargetIDs": [
"/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/resourcegroups/test-RG/providers/microsoft.compute/virtualmachines/test-VM"
],
"configurationItems": [
"test-VM"
],
"originAlertId": "dddd3333-ee44-5555-66ff-777777aaaaaa_123456789012345678901234567890ab",
"firedDateTime": "2025-04-15T11:26:21.386Z",
"description": "Alert rule description",
"essentialsVersion": "1.0",
"alertContextVersion": "1.0"
},
"alertContext": {
"authorization": {
"action": "Microsoft.Compute/virtualMachines/restart/action",
"scope": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/resourceGroups/test-RG/providers/Microsoft.Compute/virtualMachines/test-VM"
},
"channels": "Operation",
"claims": "{}",
"caller": "user@contoso.com",
"correlationId": "cccc2222-dd33-4444-55ee-666666ffffff",
"eventSource": "Administrative",
"eventTimestamp": "2025-04-15T11:26:21.386Z",
"eventDataId": "dddd3333-ee44-5555-66ff-777777aaaaaa",
"level": "Informational",
"operationName": "Microsoft.Compute/virtualMachines/restart/action",
"operationId": "bbbbbbbb-1111-2222-3333-cccccccccccc",
"properties": {
"eventCategory": "Administrative",
"entity": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/resourceGroups/test-RG/providers/Microsoft.Compute/virtualMachines/test-VM",
"message": "Microsoft.Compute/virtualMachines/restart/action",
"hierarchy": "22222222-2222-2222-2222-222222222222/CnAIOrchestrationServicePublicCorpprod/33333333-3333-3333-3333-3333333333333/cccccccc-2222-3333-4444-dddddddddddd/dddddddd-3333-4444-5555-eeeeeeeeeeee/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e"
},
"status": "Succeeded",
"subStatus": "",
"submissionTimestamp": "2025-04-15T11:26:21.386Z",
"Activity Log Event Description": ""
}
}
}
示例测试作 Availability test alert
{
"schemaId": "azureMonitorCommonAlertSchema",
"data": {
"essentials": {
"alertId": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/providers/Microsoft.AlertsManagement/alerts/eeeeeeee-4444-5555-6666-ffffffffffff",
"alertRule": "test-availabilityTest-test-applicationInsights",
"severity": "Sev4",
"signalType": "Metric",
"monitorCondition": "Fired",
"monitoringService": "Platform",
"alertTargetIDs": [
"/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/resourcegroups/test-RG/providers/microsoft.insights/components/test-applicationInsights"
],
"configurationItems": [
"test-applicationInsights"
],
"originAlertId": "aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e_test-RG_microsoft.insights_metricalerts_test-availabilityTest-test-applicationInsights_1234567890",
"firedDateTime": "2025-04-15T17:42:34.824Z",
"description": "Alertruledescription",
"essentialsVersion": "1.0",
"alertContextVersion": "1.0"
},
"alertContext": {
"properties": null,
"conditionType": "WebtestLocationAvailabilityCriteria",
"condition": {
"windowSize": "PT5M",
"allOf": [
{
"metricName": "FailedLocation",
"metricNamespace": null,
"operator": "GreaterThan",
"threshold": "2",
"timeAggregation": "Sum",
"dimensions": [],
"metricValue": 5.0,
"webTestName": "test-availabilityTest-test-applicationInsights"
}
],
"windowStartTime": "2025-04-15T17:42:34.824Z",
"windowEndTime": "2025-04-15T17:42:34.824Z"
}
},
"customProperties": {
"customKey1": "value1",
"customKey2": "value2"
}
}
}
示例测试作 Budget alert
{
"schemaId": "azureMonitorCommonAlertSchema",
"data": {
"essentials": {
"monitoringService": "CostAlerts",
"firedDateTime": "2025-04-15T17:49:34.022Z",
"description": "Delivery Confirmation: This is a sample budget alert from Azure Monitor Action Groups.",
"essentialsVersion": "1.0",
"alertContextVersion": "1.0",
"alertId": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/providers/Microsoft.CostManagement/alerts/Test_Alert",
"alertRule": null,
"severity": null,
"signalType": null,
"monitorCondition": "Fired",
"alertTargetIDs": null,
"configurationItems": [
"budgets"
],
"originAlertId": null
},
"alertContext": {
"AlertCategory": "budgets",
"AlertData": {
"Scope": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/",
"ThresholdType": "Forecasted",
"BudgetType": "Cost",
"BudgetThreshold": "$50.00",
"NotificationThresholdAmount": "$50.00",
"BudgetName": "Test_forcasted_budget",
"BudgetId": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/providers/Microsoft.Consumption/budgets/Test_forcasted_budget",
"BudgetStartDate": "2022-11-01",
"BudgetCreator": "test@sample.test",
"Unit": "USD",
"SpentAmount": "$999.99",
"ForecastedTotalForPeriod": "$1111.11"
}
}
}
}
示例测试作 Cost budget alert
{
"schemaId": "azureMonitorCommonAlertSchema",
"data": {
"essentials": {
"monitoringService": "CostAlerts",
"firedDateTime": "2025-04-15T17:53:32.996Z",
"description": "YourspendforbudgetTest_actual_cost_budgetisnow$11,111.00exceedingyourspecifiedthreshold$25.00.",
"essentialsVersion": "1.0",
"alertContextVersion": "1.0",
"alertId": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/providers/Microsoft.CostManagement/alerts/Test_Alert",
"alertRule": null,
"severity": null,
"signalType": null,
"monitorCondition": "Fired",
"alertTargetIDs": null,
"configurationItems": [
"budgets"
],
"originAlertId": null
},
"alertContext": {
"AlertCategory": "budgets",
"AlertData": {
"Scope": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/",
"ThresholdType": "Actual",
"BudgetType": "Cost",
"BudgetThreshold": "$50.00",
"NotificationThresholdAmount": "$25.00",
"BudgetName": "Test_actual_cost_budget",
"BudgetId": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/providers/Microsoft.Consumption/budgets/Test_actual_cost_budget",
"BudgetStartDate": "2022-11-01",
"BudgetCreator": "test@sample.test",
"Unit": "USD",
"SpentAmount": "$11,111.00"
}
}
}
}
示例测试作 Forecasted budget alert
{
"schemaId": "azureMonitorCommonAlertSchema",
"data": {
"essentials": {
"monitoringService": "CostAlerts",
"firedDateTime": "2025-04-15T17:55:39.04Z",
"description": "Thetotalspendforyourbudget,Test_forcasted_budget,isforecastedtoreach$1111.11beforetheendoftheperiod.Thisamountexceedsyourspecifiedbudgetthresholdof$50.00.",
"essentialsVersion": "1.0",
"alertContextVersion": "1.0",
"alertId": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/providers/Microsoft.CostManagement/alerts/Test_Alert",
"alertRule": null,
"severity": null,
"signalType": null,
"monitorCondition": "Fired",
"alertTargetIDs": null,
"configurationItems": [
"budgets"
],
"originAlertId": null
},
"alertContext": {
"AlertCategory": "budgets",
"AlertData": {
"Scope": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/",
"ThresholdType": "Forecasted",
"BudgetType": "Cost",
"BudgetThreshold": "$50.00",
"NotificationThresholdAmount": "$50.00",
"BudgetName": "Test_forcasted_budget",
"BudgetId": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/providers/Microsoft.Consumption/budgets/Test_forcasted_budget",
"BudgetStartDate": "2022-11-01",
"BudgetCreator": "test@sample.test",
"Unit": "USD",
"SpentAmount": "$999.99",
"ForecastedTotalForPeriod": "$1111.11"
}
}
}
}
作组测试中的旧日志警报 V1
在某些情况下,Azure 仍支持 日志警报 V1 ,包括使用 “测试作组” 功能时。 日志警报 V1 表示对 Azure Monitor 中日志数据的早期生成警报,此前是统一 的计划查询规则 API(v2) 和 通用警报架构的更广泛采用。
在测试期间选择 日志警报 V1 作为警报类型时,有效负载结构和架构与现代通用警报架构格式明显不同。 此测试主要与最初使用日志警报 V1 通知集成的旧系统相关。
注释
Microsoft建议迁移到 日志警报 V2 ,以利用改进的架构一致性。
仅当接收终结点或自动化针对较旧的架构显式生成时,才应测试 日志警报 V1 有效负载。
示例测试作 Log alert V1 - Metric measurement
{
"schemaId": "azureMonitorCommonAlertSchema",
"data": {
"essentials": {
"alertId": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/providers/Microsoft.AlertsManagement/alerts/eeeeeeee-4444-5555-6666-ffffffffffff",
"alertRule": "test-logAlertRule-v1-metricMeasurement",
"severity": "Sev4",
"signalType": "Log",
"monitorCondition": "Fired",
"monitoringService": "Log Analytics",
"alertTargetIDs": [
"/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/resourcegroups/test-RG/providers/microsoft.operationalinsights/workspaces/test-logAnalyticsWorkspace"
],
"configurationItems": [],
"originAlertId": "ffffffff-5555-6666-7777-aaaaaaaaaaaa",
"firedDateTime": "2025-04-15T17:57:27.967Z",
"description": "Alert rule description",
"essentialsVersion": "1.0",
"alertContextVersion": "1.1"
},
"alertContext": {
"SearchQuery": "Heartbeat | summarize AggregatedValue=count() by bin(TimeGenerated, 5m)",
"SearchIntervalStartTimeUtc": "2025-04-15T17:57:27.967Z",
"SearchIntervalEndtimeUtc": "2025-04-15T17:57:27.967Z",
"ResultCount": 2,
"LinkToSearchResults": "https://portal.azure.cn#@cccc2222-dd33-4444-55ee-666666ffffff/blade/Microsoft_Azure_Monitoring_Logs/LogsBlade/source/Alerts.EmailLinks/scope/%7B%22resources%22%3A%5B%7B%22resourceId%22%3A%22%2Fsubscriptions%2Faaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e%2FresourceGroups%2Ftest-RG%2Fproviders%2FMicrosoft.OperationalInsights%2Fworkspaces%2Ftest-logAnalyticsWorkspace%22%7D%5D%7D/q/aBcDeFgHi%2BWqUSguzc1NLMqsSlVwTE8vSk1PLElNCUvMKU21Tc4vzSvRaBcDeFgHiaBcDeFgHiaBcDeFgHiaBcDeFgHi/prettify/1/timespan/2021-11-15T15%3a16%3a49.0000000Z%2f2021-11-16T15%3a16%3a49.0000000Z",
"LinkToFilteredSearchResultsUI": "https://portal.azure.cn#@cccc2222-dd33-4444-55ee-666666ffffff/blade/Microsoft_Azure_Monitoring_Logs/LogsBlade/source/Alerts.EmailLinks/scope/%7B%22resources%22%3A%5B%7B%22resourceId%22%3A%22%2Fsubscriptions%2Faaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e%2FresourceGroups%2Ftest-RG%2Fproviders%2FMicrosoft.OperationalInsights%2Fworkspaces%2Ftest-logAnalyticsWorkspace%22%7D%5D%7D/q/aBcDeFgHiaBcDeFgHiaBcDeFgHiaBcDeFgHiaBcDeFgHidp%2BOPOhDKsHR%2FFeJXsTgzGJRmVui3KF3RpLyEJCX9A2iMl6jgxMn6jRevng3JmIHLdYtKP4DRI9mhc%3D/prettify/1/timespan/2021-11-15T15%3a16%3a49.0000000Z%2f2021-11-16T15%3a16%3a49.0000000Z",
"LinkToSearchResultsAPI": "https://api.loganalytics.io/v1/workspaces/dddd3333-ee44-5555-66ff-777777aaaaaa/query?query=Heartbeat%20%0A%7C%20summarize%20AggregatedValue%3Dcount%28%29%20by%20bin%28TimeGenerated%2C%205m%29×pan=2021-11-15T15%3a16%3a49.0000000Z%2f2021-11-16T15%3a16%3a49.0000000Z",
"LinkToFilteredSearchResultsAPI": "https://api.loganalytics.io/v1/workspaces/dddd3333-ee44-5555-66ff-777777aaaaaa/query?query=Heartbeat%20%0A%7C%20summarize%20AggregatedValue%3Dcount%28%29%20by%20bin%28TimeGenerated%2C%205m%29%7C%20where%20todouble%28AggregatedValue%29%20%3E%200×pan=2021-11-15T15%3a16%3a49.0000000Z%2f2021-11-16T15%3a16%3a49.0000000Z",
"SeverityDescription": "Informational",
"WorkspaceId": "dddd3333-ee44-5555-66ff-777777aaaaaa",
"SearchIntervalDurationMin": "1440",
"AffectedConfigurationItems": [],
"AlertType": "Metric measurement",
"IncludeSearchResults": true,
"Dimensions": [],
"SearchIntervalInMinutes": "1440",
"SearchResults": {
"tables": [
{
"name": "PrimaryResult",
"columns": [
{
"name": "TimeGenerated",
"type": "datetime"
},
{
"name": "AggregatedValue",
"type": "long"
}
],
"rows": [
[
"2025-04-15T17:57:27.967Z",
11
],
[
"2025-04-15T17:57:27.967Z",
11
]
]
}
],
"dataSources": [
{
"resourceId": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/resourcegroups/test-RG/providers/microsoft.operationalinsights/workspaces/test-logAnalyticsWorkspace",
"region": "chinanorth",
"tables": [
"Heartbeat"
]
}
]
},
"Threshold": 0,
"Operator": "Greater Than",
"IncludedSearchResults": "True"
}
}
}
示例测试作 Log alert V1 - Number of results
{
"schemaId": "azureMonitorCommonAlertSchema",
"data": {
"essentials": {
"alertId": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/providers/Microsoft.AlertsManagement/alerts/eeeeeeee-4444-5555-6666-ffffffffffff",
"alertRule": "test-logAlertRule-v1-numResults",
"severity": "Sev4",
"signalType": "Log",
"monitorCondition": "Fired",
"monitoringService": "Log Analytics",
"alertTargetIDs": [
"/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/resourcegroups/test-RG/providers/microsoft.operationalinsights/workspaces/test-logAnalyticsWorkspace"
],
"configurationItems": [
"test-computer"
],
"originAlertId": "22222222-2222-2222-2222-222222222222",
"firedDateTime": "2025-04-15T18:04:40.852Z",
"description": "Alert rule description",
"essentialsVersion": "1.0",
"alertContextVersion": "1.1"
},
"alertContext": {
"SearchQuery": "Heartbeat",
"SearchIntervalStartTimeUtc": "2025-04-15T18:04:40.852Z",
"SearchIntervalEndtimeUtc": "2025-04-15T18:04:40.852Z",
"ResultCount": 1,
"LinkToSearchResults": "https://portal.azure.cn#@cccc2222-dd33-4444-55ee-666666ffffff/blade/Microsoft_Azure_Monitoring_Logs/LogsBlade/source/Alerts.EmailLinks/scope/%7B%22resources%22%3A%5B%7B%22resourceId%22%3A%22%2Fsubscriptions%2Faaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e%2FresourceGroups%2Ftest-RG%2Fproviders%2FMicrosoft.OperationalInsights%2Fworkspaces%2Ftest-logAnalyticsWorkspace%22%7D%5D%7D/q/aBcDeFgHi%2ABCDE%3D%3D/prettify/1/timespan/2021-11-15T15%3a15%3a24.0000000Z%2f2021-11-16T15%3a15%3a24.0000000Z",
"LinkToFilteredSearchResultsUI": "https://portal.azure.cn#@cccc2222-dd33-4444-55ee-666666ffffff/blade/Microsoft_Azure_Monitoring_Logs/LogsBlade/source/Alerts.EmailLinks/scope/%7B%22resources%22%3A%5B%7B%22resourceId%22%3A%22%2Fsubscriptions%2Faaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e%2FresourceGroups%2Ftest-RG%2Fproviders%2FMicrosoft.OperationalInsights%2Fworkspaces%2Ftest-logAnalyticsWorkspace%22%7D%5D%7D/q/aBcDeFgHi%2ABCDE%3D%3D/prettify/1/timespan/2021-11-15T15%3a15%3a24.0000000Z%2f2021-11-16T15%3a15%3a24.0000000Z",
"LinkToSearchResultsAPI": "https://api.loganalytics.io/v1/workspaces/dddd3333-ee44-5555-66ff-777777aaaaaa/query?query=Heartbeat%0A×pan=2021-11-15T15%3a15%3a24.0000000Z%2f2021-11-16T15%3a15%3a24.0000000Z",
"LinkToFilteredSearchResultsAPI": "https://api.loganalytics.io/v1/workspaces/dddd3333-ee44-5555-66ff-777777aaaaaa/query?query=Heartbeat%0A×pan=2021-11-15T15%3a15%3a24.0000000Z%2f2021-11-16T15%3a15%3a24.0000000Z",
"SeverityDescription": "Informational",
"WorkspaceId": "dddd3333-ee44-5555-66ff-777777aaaaaa",
"SearchIntervalDurationMin": "1440",
"AffectedConfigurationItems": [
"test-computer"
],
"AlertType": "Number of results",
"IncludeSearchResults": true,
"SearchIntervalInMinutes": "1440",
"SearchResults": {
"tables": [
{
"name": "PrimaryResult",
"columns": [
{
"name": "TenantId",
"type": "string"
},
{
"name": "Computer",
"type": "string"
},
{
"name": "TimeGenerated",
"type": "datetime"
}
],
"rows": [
[
"dddd3333-ee44-5555-66ff-777777aaaaaa",
"test-computer",
"2025-04-15T18:04:40.852Z"
]
]
}
],
"dataSources": [
{
"resourceId": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/resourcegroups/test-RG/providers/microsoft.operationalinsights/workspaces/test-logAnalyticsWorkspace",
"region": "chinanorth",
"tables": [
"Heartbeat"
]
}
]
},
"Threshold": 0,
"Operator": "Greater Than",
"IncludedSearchResults": "True"
}
}
}
示例测试作 Log alert V2
注释
API 版本 2020-05-01 中的日志搜索警报规则使用此有效负载类型,该类型仅支持通用架构。 使用此版本时,搜索结果不会嵌入到日志搜索警报有效负载中。 使用维度来提供已触发警报的上下文。
还可以使用 LinkToFilteredSearchResultsAPI 或 LinkToSearchResultsAPI 通过 Log Analytics API 访问查询结果。 如果必须嵌入结果,请使用包含所提供链接的逻辑应用,以生成自定义有效负载。
{
"schemaId": "azureMonitorCommonAlertSchema",
"data": {
"essentials": {
"alertId": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/providers/Microsoft.AlertsManagement/alerts/eeeeeeee-4444-5555-6666-ffffffffffff",
"alertRule": "test-logAlertRule-v2",
"severity": "Sev4",
"signalType": "Log",
"monitorCondition": "Fired",
"monitoringService": "Log Alerts V2",
"alertTargetIDs": [
"/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/resourcegroups/test-RG/providers/microsoft.operationalinsights/workspaces/test-logAnalyticsWorkspace"
],
"configurationItems": [
"test-computer"
],
"originAlertId": "22222222-2222-2222-2222-222222222222",
"firedDateTime": "2025-04-15T18:08:03.626Z",
"description": "Alert rule description",
"essentialsVersion": "1.0",
"alertContextVersion": "1.0"
},
"alertContext": {
"properties": {
"customKey1": "value1",
"customKey2": "value2"
},
"conditionType": "LogQueryCriteria",
"condition": {
"windowSize": "PT1H",
"allOf": [
{
"searchQuery": "Heartbeat",
"metricMeasureColumn": null,
"targetResourceTypes": "['Microsoft.OperationalInsights/workspaces']",
"operator": "GreaterThan",
"threshold": "0",
"timeAggregation": "Count",
"dimensions": [
{
"name": "Computer",
"value": "test-computer"
}
],
"metricValue": 3.0,
"failingPeriods": {
"numberOfEvaluationPeriods": 1,
"minFailingPeriodsToAlert": 1
},
"linkToSearchResultsUI": "https://portal.azure.cn#@cccc2222-dd33-4444-55ee-666666ffffff/blade/Microsoft_Azure_Monitoring_Logs/LogsBlade/source/Alerts.EmailLinks/scope/%7B%22resources%22%3A%5B%7B%22resourceId%22%3A%22%2Fsubscriptions%2Faaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e%2FresourceGroups%2Ftest-RG%2Fproviders%2FMicrosoft.OperationalInsights%2Fworkspaces%2Ftest-logAnalyticsWorkspace%22%7D%5D%7D/q/aBcDeFgHiJkLmNaBcDeFgHiJkLmNaBcDeFgHiJkLmNaBcDeFgHiJkLmN1234567890ZAZBZiaGBlaG5lbKlnAAFRmnp6WNUZoqvTBAA%3D/prettify/1/timespan/2021-11-16T10%3a17%3a39.0000000Z%2f2021-11-16T11%3a17%3a39.0000000Z",
"linkToFilteredSearchResultsUI": "https://portal.azure.cn#@cccc2222-dd33-4444-55ee-666666ffffff/blade/Microsoft_Azure_Monitoring_Logs/LogsBlade/source/Alerts.EmailLinks/scope/%7B%22resources%22%3A%5B%7B%22resourceId%22%3A%22%2Fsubscriptions%2Faaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e%2FresourceGroups%2Ftest-RG%2Fproviders%2FMicrosoft.OperationalInsights%2Fworkspaces%2Ftest-logAnalyticsWorkspace%22%7D%5D%7D/q/aBcDeFgHiJkLmN%2Fl35oOTZoKioEOouaBcDeFgHiJkLmN%2BaBcDeFgHiJkLmN%2BaBcDeFgHiJkLmN7HHgOCZTR0Ak%2FaBcDeFgHiJkLmN1234567890Ltcw%2FOqZS%2FuX0L5d%2Bx3iMHNzQiu3Y%2BzsjpFSWlOzgA87vAxeHW2MoAtQxe6OUvVrZR3XYZPXrd%2FIE/prettify/1/timespan/2021-11-16T10%3a17%3a39.0000000Z%2f2021-11-16T11%3a17%3a39.0000000Z",
"linkToSearchResultsAPI": "https://api.loganalytics.io/v1/workspaces/dddd3333-ee44-5555-66ff-777777aaaaaa/query?query=Heartbeat%7C%20where%20TimeGenerated%20between%28datetime%282021-11-16T10%3A17%3A39.0000000Z%29..datetime%282021-11-16T11%3A17%3A39.0000000Z%29%29×pan=2021-11-16T10%3a17%3a39.0000000Z%2f2021-11-16T11%3a17%3a39.0000000Z",
"linkToFilteredSearchResultsAPI": "https://api.loganalytics.io/v1/workspaces/dddd3333-ee44-5555-66ff-777777aaaaaa/query?query=Heartbeat%7C%20where%20TimeGenerated%20between%28datetime%282021-11-16T10%3A17%3A39.0000000Z%29..datetime%282021-11-16T11%3A17%3A39.0000000Z%29%29%7C%20where%20tostring%28Computer%29%20%3D%3D%20%27test-computer%27×pan=2021-11-16T10%3a17%3a39.0000000Z%2f2021-11-16T11%3a17%3a39.0000000Z"
}
],
"windowStartTime": "2025-04-15T18:08:03.626Z",
"windowEndTime": "2025-04-15T18:08:03.626Z"
}
}
}
}
示例测试作 Metric alert - Dynamic threshold
{
"schemaId": "azureMonitorCommonAlertSchema",
"data": {
"essentials": {
"alertId": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/providers/Microsoft.AlertsManagement/alerts/eeeeeeee-4444-5555-6666-ffffffffffff",
"alertRule": "test-dynamicMetricAlertRule",
"severity": "Sev4",
"signalType": "Metric",
"monitorCondition": "Fired",
"monitoringService": "Platform",
"alertTargetIDs": [
"/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/resourcegroups/test-RG/providers/Microsoft.Storage/storageAccounts/test-storageAccount"
],
"configurationItems": [
"test-storageAccount"
],
"originAlertId": "aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e_test-RG_microsoft.insights_metricAlerts_test-metricAlertRule_1234567890",
"firedDateTime": "2025-04-15T18:15:16.104Z",
"description": "Alertruledescription",
"essentialsVersion": "1.0",
"alertContextVersion": "1.0"
},
"alertContext": {
"properties": {
"customKey1": "value1",
"customKey2": "value2"
},
"conditionType": "DynamicThresholdCriteria",
"condition": {
"windowSize": "PT15M",
"allOf": [
{
"alertSensitivity": "Low",
"failingPeriods": {
"numberOfEvaluationPeriods": 3,
"minFailingPeriodsToAlert": 3
},
"ignoreDataBefore": null,
"metricName": "Transactions",
"metricNamespace": "Microsoft.Storage/storageAccounts",
"operator": "GreaterThan",
"threshold": "0.3",
"timeAggregation": "Average",
"dimensions": [],
"metricValue": 78.09,
"webTestName": null
}
],
"windowStartTime": "2025-04-15T18:15:16.104Z",
"windowEndTime": "2025-04-15T18:15:16.104Z"
}
},
"customProperties": {
"customKey1": "value1",
"customKey2": "value2"
}
}
}
示例测试作 Metric alert - Static threshold
{
"schemaId": "azureMonitorCommonAlertSchema",
"data": {
"essentials": {
"alertId": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/providers/Microsoft.AlertsManagement/alerts/eeeeeeee-4444-5555-6666-ffffffffffff",
"alertRule": "test-metricAlertRule",
"severity": "Sev4",
"signalType": "Metric",
"monitorCondition": "Fired",
"monitoringService": "Platform",
"alertTargetIDs": [
"/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/resourcegroups/test-RG/providers/microsoft.storage/storageaccounts/test-storageAccount"
],
"configurationItems": [
"test-storageAccount"
],
"originAlertId": "aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e_test-RG_microsoft.insights_metricAlerts_test-metricAlertRule_1234567890",
"firedDateTime": "2025-04-15T18:17:12.851Z",
"description": "Alertruledescription",
"essentialsVersion": "1.0",
"alertContextVersion": "1.0"
},
"alertContext": {
"properties": {
"customKey1": "value1",
"customKey2": "value2"
},
"conditionType": "SingleResourceMultipleMetricCriteria",
"condition": {
"windowSize": "PT5M",
"allOf": [
{
"metricName": "Transactions",
"metricNamespace": "Microsoft.Storage/storageAccounts",
"operator": "GreaterThan",
"threshold": "0",
"timeAggregation": "Total",
"dimensions": [
{
"name": "ApiName",
"value": "GetBlob"
}
],
"metricValue": 100,
"webTestName": null
}
],
"windowStartTime": "2025-04-15T18:17:12.851Z",
"windowEndTime": "2025-04-15T18:17:12.851Z"
}
},
"customProperties": {
"customKey1": "value1",
"customKey2": "value2"
}
}
}
示例测试作 Resource health alert
{
"schemaId": "azureMonitorCommonAlertSchema",
"data": {
"essentials": {
"alertId": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/providers/Microsoft.AlertsManagement/alerts/eeeeeeee-4444-5555-6666-ffffffffffff",
"alertRule": "test-ResourceHealthAlertRule",
"severity": "Sev4",
"signalType": "Activity Log",
"monitorCondition": "Fired",
"monitoringService": "Resource Health",
"alertTargetIDs": [
"/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/resourcegroups/test-RG/providers/microsoft.compute/virtualmachines/test-VM"
],
"configurationItems": [
"test-VM"
],
"originAlertId": "dddd3333-ee44-5555-66ff-777777aaaaaa_123456789012345678901234567890ab",
"firedDateTime": "2025-04-15T18:19:45.304Z",
"description": "Alert rule description",
"essentialsVersion": "1.0",
"alertContextVersion": "1.0"
},
"alertContext": {
"channels": "Admin, Operation",
"correlationId": "cccc2222-dd33-4444-55ee-666666ffffff",
"eventSource": "ResourceHealth",
"eventTimestamp": "2025-04-15T18:19:45.304Z",
"eventDataId": "dddd3333-ee44-5555-66ff-777777aaaaaa",
"level": "Informational",
"operationName": "Microsoft.Resourcehealth/healthevent/Activated/action",
"operationId": "dddd3333-ee44-5555-66ff-777777aaaaaa",
"properties": {
"title": "Rebooted by user",
"details": null,
"currentHealthStatus": "Unavailable",
"previousHealthStatus": "Available",
"type": "Downtime",
"cause": "UserInitiated"
},
"status": "Active",
"submissionTimestamp": "2025-04-15T18:19:45.304Z",
"Activity Log Event Description": null
}
}
}
示例测试作 Service health alert
{
"schemaId": "azureMonitorCommonAlertSchema",
"data": {
"essentials": {
"alertId": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/providers/Microsoft.AlertsManagement/alerts/1234abcd5678efgh1234abcd5678efgh1234abcd5678efgh1234abcd5678efgh",
"alertRule": "test-ServiceHealthAlertRule",
"severity": "Sev4",
"signalType": "ActivityLog",
"monitorCondition": "Fired",
"monitoringService": "ServiceHealth",
"alertTargetIDs": [
"/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e"
],
"originAlertId": "eeeeeeee-4444-5555-6666-ffffffffffff",
"firedDateTime": "2025-04-15T18:20:36.256Z",
"description": "Alertruledescription",
"essentialsVersion": "1.0",
"alertContextVersion": "1.0"
},
"alertContext": {
"authorization": null,
"channels": 1,
"claims": null,
"caller": null,
"correlationId": "12345678-abcd-efgh-ijkl-abcd12345678",
"eventSource": 2,
"eventTimestamp": "2025-04-15T18:20:36.256Z",
"httpRequest": null,
"eventDataId": "eeeeeeee-4444-5555-6666-ffffffffffff",
"level": 3,
"operationName": "Microsoft.ServiceHealth/incident/action",
"operationId": "12345678-abcd-efgh-ijkl-abcd12345678",
"properties": {
"title": "TestActionGroup-TestServiceHealthAlert",
"service": "AzureServiceName",
"region": "Global",
"communication": "<p>ThisisatestfromServiceHealthAlert</p>",
"incidentType": "Incident",
"trackingId": "TEST-TTT",
"impactStartTime": "2025-04-15T18:20:36.256Z",
"impactMitigationTime": "2025-04-15T18:20:36.256Z",
"impactedServices": [
{
"ImpactedRegions": [
{
"RegionName": "Global"
}
],
"ServiceName": "AzureServiceName"
}
],
"impactedServicesTableRows": "<tr><td>Thisisatestfromservicehealthalert</<td>/<tr>",
"defaultLanguageTitle": "TestActionGroup-TestServiceHealthAlert",
"defaultLanguageContent": "<p>ThisisatestfromServiceHealthAlert</p>",
"stage": "Resolved",
"communicationId": "11223344556677",
"isHIR": "false",
"IsSynthetic": "True",
"impactType": "SubscriptionList",
"version": "0.1.1"
},
"status": "Resolved",
"subStatus": null,
"submissionTimestamp": "2025-04-15T18:20:36.256Z",
"ResourceType": null
}
}
}
示例测试作 Smart alert
{
"schemaId": "azureMonitorCommonAlertSchema",
"data": {
"essentials": {
"alertId": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/providers/Microsoft.AlertsManagement/alerts/eeeeeeee-4444-5555-6666-ffffffffffff",
"alertRule": "test-SmartAlertRule",
"severity": "Sev4",
"signalType": "Log",
"monitorCondition": "Fired",
"monitoringService": "SmartDetector",
"alertTargetIDs": [
"/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/resourcegroups/test-RG/providers/microsoft.insights/components/test-applicationInsights"
],
"configurationItems": [
"test-applicationInsights"
],
"originAlertId": "1234abcd5678efgh1234abcd5678efgh1234abcd5678efgh1234abcd5678efgh",
"firedDateTime": "2021-10-28T19:09:09.1115084Z",
"description": "Dependency Latency Degradation notifies you of an unusual increase in response by a dependency your app is calling (e.g. REST API or database)",
"essentialsVersion": "1.0",
"alertContextVersion": "1.0"
},
"alertContext": {
"DetectionSummary": "A degradation in the dependency duration over the last 24 hours",
"FormattedOccurrenceTime": "2025-04-15T18:23:16.577Z",
"DetectedValue": "0.45 sec",
"NormalValue": "0.27 sec (over the last 7 days)",
"PresentationInsightEventRequest": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/resourceGroups/test-RG/providers/microsoft.insights/components/test-applicationInsights/query?query=systemEvents%0d%0a++++++++++++++++%7c+where+timestamp+%3e%3d+datetime(%272021-10-27T23%3a29%3a59.0000000Z%27)+%0d%0a++++++++++++++++%7c+where+itemType+%3d%3d+%27systemEvent%27+and+name+%3d%3d+%27ProactiveDetectionInsight%27+%0d%0a++++++++++++++++%7c+where+dimensions.InsightType+%3d%3d+3+%0d%0a++++++++++++++++%7c+where+dimensions.InsightVersion+%3d%3d+%27SmartAlert%27%0d%0a++++++++++++++++%7c+where+dimensions.InsightDocumentId+%3d%3d+%2712345678-abcd-1234-5678-abcd12345678%27+%0d%0a++++++++++++++++%7c+project+dimensions.InsightPropertiesTable%2cdimensions.InsightDegradationChart%2cdimensions.InsightCountChart%2cdimensions.InsightLinksTable%0d%0a++++++++++++++++&api-version=2018-04-20",
"SmartDetectorId": "DependencyPerformanceDegradationDetector",
"SmartDetectorName": "Dependency Performance Degradation Detector",
"AnalysisTimestamp": "2025-04-15T18:23:16.577Z"
}
}
}