使用 Microsoft.Resources/deploymentScripts 版本 2023-08-01,可以使用一些附加配置在专用网络中运行部署脚本:
创建用户分配的托管标识,并在
identity属性中指定它。 若要分配标识,请参阅 “标识”。在专用网络中创建存储帐户,并指定使用现有存储帐户的部署脚本。 有关详细信息,请参阅使用现有存储帐户。 存储帐户需要一些其他配置:
- 在 Azure 门户中打开存储帐户。
- 在左侧菜单中,选择 “访问控制”(IAM),然后选择“ 角色分配 ”选项卡。
- 将 存储文件数据特权参与者 角色添加到用户分配的托管标识。
- 在左侧菜单中的 “安全性 + 网络”下,选择“ 网络”,然后选择“ 防火墙和虚拟网络”。
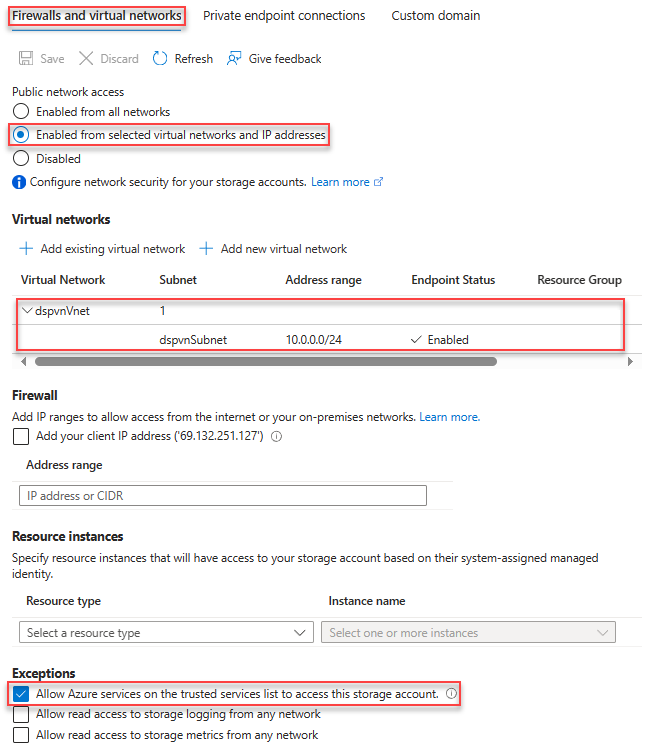
- 选择“已从所选虚拟网络和 IP 地址启用”。
- 在 “虚拟网络”下,添加子网。 在以下屏幕截图中,子网称为 dspvnVnet。
- 在“异常”下面,选择“允许受信任的服务列表中的 Azure 服务访问此存储帐户”。
以下 Bicep 文件演示如何配置用于运行部署脚本的环境:
@maxLength(10) // Required maximum length, because the storage account has a maximum of 26 characters
param prefix string
param location string = resourceGroup().location
param userAssignedIdentityName string = '${prefix}Identity'
param storageAccountName string = '${prefix}stg${uniqueString(resourceGroup().id)}'
param vnetName string = '${prefix}Vnet'
param subnetName string = '${prefix}Subnet'
resource vnet 'Microsoft.Network/virtualNetworks@2025-01-01' = {
name: vnetName
location: location
properties: {
addressSpace: {
addressPrefixes: [
'10.0.0.0/16'
]
}
enableDdosProtection: false
subnets: [
{
name: subnetName
properties: {
addressPrefix: '10.0.0.0/24'
serviceEndpoints: [
{
service: 'Microsoft.Storage'
}
]
delegations: [
{
name: 'Microsoft.ContainerInstance.containerGroups'
properties: {
serviceName: 'Microsoft.ContainerInstance/containerGroups'
}
}
]
}
}
]
}
}
resource subnet 'Microsoft.Network/virtualNetworks/subnets@2024-05-01' existing = {
parent: vnet
name: subnetName
}
resource storageAccount 'Microsoft.Storage/storageAccounts@2025-06-01' = {
name: storageAccountName
location: location
sku: {
name: 'Standard_LRS'
}
kind: 'StorageV2'
properties: {
networkAcls: {
bypass: 'AzureServices'
virtualNetworkRules: [
{
id: subnet.id
action: 'Allow'
state: 'Succeeded'
}
]
defaultAction: 'Deny'
}
}
}
resource userAssignedIdentity 'Microsoft.ManagedIdentity/userAssignedIdentities@2025-01-31-preview' = {
name: userAssignedIdentityName
location: location
}
resource storageFileDataPrivilegedContributor 'Microsoft.Authorization/roleDefinitions@2022-04-01' existing = {
name: '69566ab7-960f-475b-8e7c-b3118f30c6bd' // Storage File Data Privileged Contributor
scope: tenant()
}
resource roleAssignment 'Microsoft.Authorization/roleAssignments@2022-04-01' = {
scope: storageAccount
name: guid(storageFileDataPrivilegedContributor.id, userAssignedIdentity.id, storageAccount.id)
properties: {
principalId: userAssignedIdentity.properties.principalId
roleDefinitionId: storageFileDataPrivilegedContributor.id
principalType: 'ServicePrincipal'
}
}
您可以使用以下 Bicep 文件来测试部署。
param prefix string
param location string = resourceGroup().location
param utcValue string = utcNow()
param storageAccountName string
param vnetName string
param subnetName string
param userAssignedIdentityName string
resource vnet 'Microsoft.Network/virtualNetworks@2025-01-01' existing = {
name: vnetName
resource subnet 'subnets' existing = {
name: subnetName
}
}
resource userAssignedIdentity 'Microsoft.ManagedIdentity/userAssignedIdentities@2025-01-31-preview' existing = {
name: userAssignedIdentityName
}
resource dsTest 'Microsoft.Resources/deploymentScripts@2023-08-01' = {
name: '${prefix}DS'
location: location
identity: {
type: 'userAssigned'
userAssignedIdentities: {
'${userAssignedIdentity.id}': {}
}
}
kind: 'AzureCLI'
properties: {
forceUpdateTag: utcValue
azCliVersion: '2.52.0'
storageAccountSettings: {
storageAccountName: storageAccountName
}
containerSettings: {
subnetIds: [
{
id: vnet::subnet.id
}
]
}
scriptContent: 'echo "Hello world!"'
retentionInterval: 'P1D'
cleanupPreference: 'OnExpiration'
}
}
后续步骤
本文介绍了如何访问专用虚拟网络。 若要了解详细信息,请访问以下链接: