Azure Key Vault是一种云服务,用于安全地存储和访问机密。 机密是你想要严格控制对其的访问的任何内容,例如 API 密钥、密码、证书或加密密钥。 Key Vault服务支持两种类型的容器:保管库和托管硬件安全模块(HSM)池。 保管库支持存储软件和 HSM 支持的密钥、机密和证书。 托管 HSM 池仅支持 HSM 支持的密钥。 有关完整详细信息,请参阅 Azure Key Vault REST API 概述。
下面是其他重要的术语:
Tenant:租户是拥有和管理Azure云服务的特定实例的组织。 它通常用于指代组织使用的Azure和Microsoft 365服务集合。
保管库所有者:保管库所有者可以创建密钥保管库并获得它的完全访问权限和控制权。 保管库所有者还可以设置审核来记录谁访问了机密和密钥。 管理员可以控制密钥生命周期。 他们可以滚动到密钥的新版本、对其进行备份,以及执行相关的任务。
保管库使用者:当保管库所有者为保管库使用者授予了访问权限时,使用者可以对密钥保管库内的资产执行操作。 可用操作取决于所授予的权限。
托管 HSM 管理员:分配有管理员角色的用户可以完全控制托管 HSM 池。 他们可以创建更多的角色分配来向其他用户委托受控制的访问权限。
托管 HSM 加密管理人员/用户:通常分配给用户或服务主体的内置角色,这些角色将使用托管 HSM 中的密钥执行加密操作。 加密用户可以创建新的密钥,但不能删除密钥。
托管 HSM 加密服务用户:这是一个内置角色,通常分配给服务帐户的托管服务标识(例如,存储帐户),用于使用客户管理的密钥对静态数据进行加密。
Resource:资源是可通过Azure提供的可管理项。 常见示例包括虚拟机、存储帐户、Web 应用、数据库和虚拟网络。 这只是其中一小部分。
资源组:资源组是一个容器,用于保存Azure解决方案的相关资源。 资源组可以包含解决方案的所有资源,也可以只包含想要作为组来管理的资源。 根据对组织有利的原则,决定如何将资源分配到资源组。
安全主体:Azure安全主体是用户创建的应用、服务和自动化工具用于访问特定Azure资源的安全标识。 可将其视为具有特定角色,并且权限受到严格控制的“用户标识”(用户名和密码,或者证书)。 与普通的用户标识不同,安全主体应该只需执行特定的操作。 如果只向它授予执行管理任务所需的最低权限级别,则可以提高安全性。 与应用程序或服务一起使用的安全主体称为“服务主体”。 有关详细信息,请参阅 应用程序和服务主体对象。
Microsoft Entra ID:Microsoft Entra ID是租户的Active Directory服务。 每个目录有一个或多个域。 每个目录可以有多个订阅与之关联,但只有一个租户。
Azure租户 ID:租户 ID 是标识Azure订阅中Microsoft Entra实例的唯一方法。
Managed identities:Azure Key Vault 提供了安全存储凭据和其他密钥和机密的方法,但代码需要进行身份验证才能到 Key Vault 检索凭据。 通过使用托管标识,为Azure服务在Microsoft Entra ID中提供自动管理的标识,这使解决该问题更加简单。 可以使用此标识对支持Microsoft Entra身份验证的任何服务Key Vault或任何支持Microsoft Entra身份验证的服务进行身份验证,而无需在代码中提供任何凭据。 有关详细信息,请参阅下图和有关 Azure 资源托管标识的概述。
身份验证
若要使用Key Vault执行任何操作,首先需要对其进行身份验证。 可通过三种方法对Key Vault进行身份验证:
- Azure 资源的托管标识:在 Azure 中部署虚拟机上的应用时,可以将标识分配给有权访问Key Vault的虚拟机。 还可以将标识分配给 其他Azure资源。 这种方法的好处在于应用或服务不管理第一个机密的轮换。 Azure自动轮换身份。 我们将此方法作为最佳做法推荐。
- 服务主体和证书:可以使用有权访问Key Vault的服务主体和关联的证书。 我们不建议使用此方法,因为应用程序所有者或开发人员必须轮换证书。 有关详细信息,请参阅 创建服务主体。
- 服务主体和机密:尽管可以使用服务主体和机密对Key Vault进行身份验证,但我们不建议使用它。 很难自动轮换用于对Key Vault进行身份验证的启动机密。
Key Vault角色
使用下表更好地了解Key Vault如何帮助满足开发人员和安全管理员的需求。
| 角色 | 问题陈述 | 已由Azure Key Vault解决 |
|---|---|---|
| Azure 应用程序的开发人员 | “我想为使用密钥进行签名和加密的Azure编写应用程序。 但我希望这些密钥与应用程序分开,使解决方案适用于在地理上分散的应用程序。 希望这些密钥和机密都是经过加密的,而无需自己编写代码。 我还希望这些密钥和机密对于我来说很容易在应用程序中使用,并发挥最佳性能。” |
√ 密钥存储在保管库中,可按需由 URI 调用。 √ 密钥由 Azure 通过使用行业标准算法、密钥长度和硬件安全模块进行保护。 √密钥在驻留在应用程序所在的同一Microsoft数据中心的 HSM 中进行处理。 与驻留在单独位置(如本地)的密钥相比,此方法提供了更好的可靠性和更低的延迟。 |
| 软件即服务 (SaaS) 开发人员 | “对于客户的租户密钥和机密,我不想承担任何实际或潜在法律责任。 我希望客户拥有并管理其密钥,这样我就可以集中精力做我最擅长的事情,即提供核心软件功能。” |
√客户可以将自己的密钥导入Azure并对其进行管理。 当 SaaS 应用程序需要使用客户的密钥执行加密操作时,Key Vault代表应用程序执行这些操作。 应用程序看不到客户的密钥。 |
| 首席安全官 (CSO) | “我想要知道应用程序是否遵循 FIPS 140 Level 3 HSM 的安全密钥管理规范。 我想要确保我的组织掌控密钥生命周期,并可监视密钥的使用。 尽管我们使用多个Azure服务和资源,但我想从Azure中的单个位置管理密钥。 |
√ 选择保管库或托管 HSM以用于经过 FIPS 140 验证的 HSM。 √ 选择“托管 HSM 池”以获取通过 FIPS 140-2 级别 3 验证的 HSM。 √ Key Vault 设计确保 Azure 无法看到或提取您的密钥。 √ 以近实时方式记录密钥的使用。 √保管库提供单个接口,无论在Azure中拥有多少个保管库、它们支持哪些区域以及哪些应用程序都使用这些保管库。 |
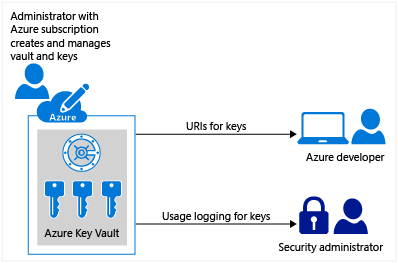
具有Azure订阅的任何人都可以创建和使用密钥保管库。 尽管Key Vault使开发人员和安全管理员受益,但可由管理其他Azure服务的组织的管理员实现和管理。 例如,此管理员可以使用Azure订阅登录,为存储密钥的组织创建保管库,然后负责如下操作任务:
- 创建或导入密钥或机密
- 吊销或删除密钥或机密
- 授权用户或应用程序访问密钥保管库,使它们能够管理或使用其密钥和机密
- 配置密钥用法(例如,签名或加密)
- 监视密钥用法
该管理员然后会为开发人员提供 URI,方便其从应用程序进行调用。 该管理员也会将密钥使用日志记录信息提供给安全管理员。
开发人员还可通过使用 API 直接管理密钥。 有关详细信息,请参阅Azure Key Vault开发人员指南。
后续步骤
- Azure Key Vault开发人员指南入门
- 了解 Azure Key Vault 安全功能
- 了解 Azure Key Vault 中的 Authentication
- 了解如何安全管理您的 HSM 池
Azure Key Vault在大多数区域中可用。 有关详细信息,请参阅 Key Vault 定价页。