Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Azure AD B2C offers several sign-up and sign-in methods for users of your applications. When users sign up for your application, you determine whether they'll use a username or email address to create local accounts in your Azure AD B2C tenant. You can also federate with social identity providers and standard identity protocols (like OAuth 2.0, OpenID Connect, and more).
This article gives an overview of Azure AD B2C sign-in options.
Email sign-in
Email sign-up is enabled by default in your local account identity provider settings. With the email option, users can sign in and sign up with their email address and password.
- Sign-in: Users are prompted to provide their email and password.
- Sign-up: users are prompted for an email address, which is verified at sign-up (optional) and becomes their login ID. The user then enters any other information requested on the sign-up page, for example, display name, given name, and surname. Then they select Continue to create an account.
- Password reset: Users enter and verify their email, after which the user can reset the password
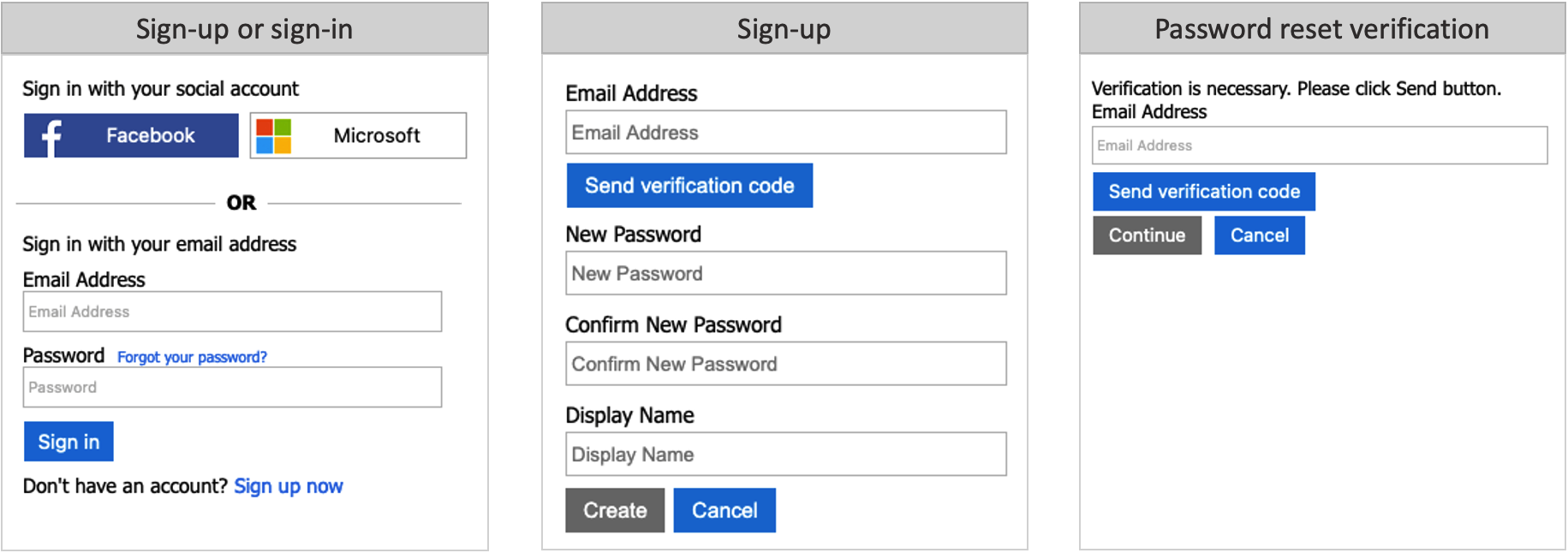
Learn how to configure email sign-in in your local account identity provider.
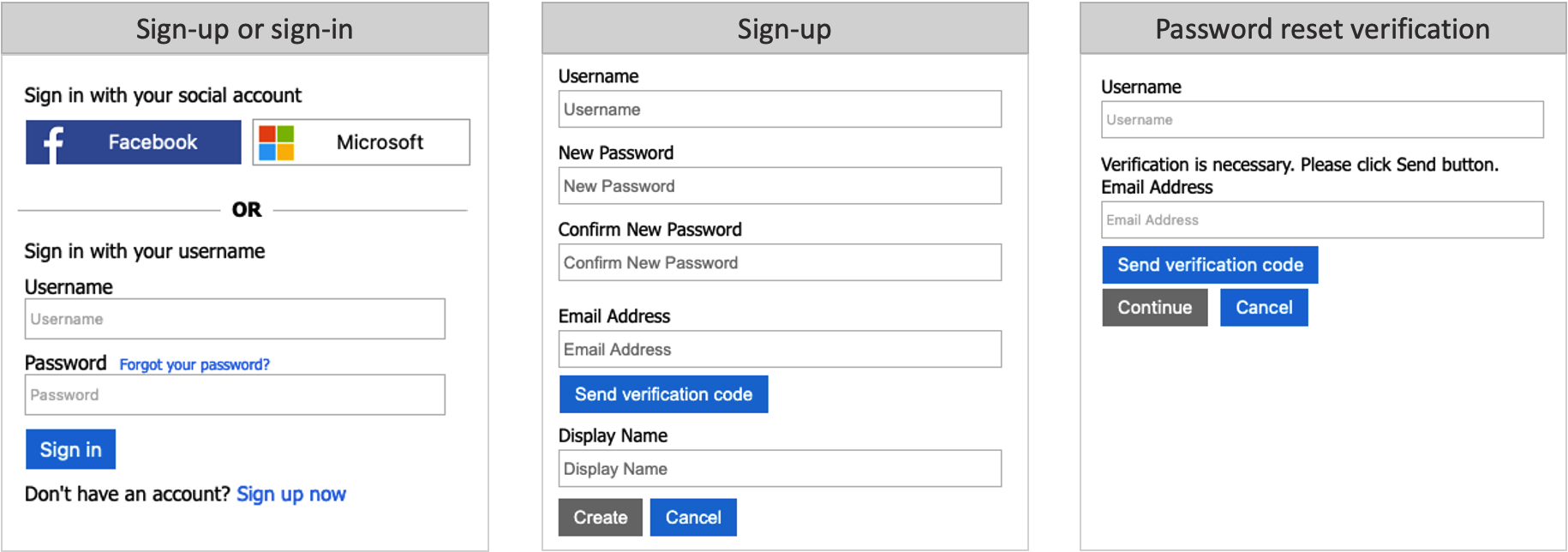
Username sign-in
Your local account identity provider includes a Username option that lets users sign up and sign in to your application with a username and password.
- Sign-in: Users are prompted to provide their username and password.
- Sign-up: Users will be prompted for a username, which will become their login ID. Users will also be prompted for an email address, which will be verified at sign-up. The email address will be used during a password reset flow. The user enters any other information requested on the sign-up page, for example, Display Name, Given Name, and Surname. The user then selects Continue to create the account.
- Password reset: Users must enter their username and the associated email address. The email address must be verified, after which, the user can reset the password.
Federated sign-in
You can configure Azure AD B2C to allow users to sign in to your application with credentials from external social or enterprise identity providers (IdPs). Azure AD B2C supports many external identity providers and any identity provider that supports OAuth 1.0, OAuth 2.0, OpenID Connect, and SAML protocols.
With external identity provider federation, you can offer your consumers the ability to sign in with their existing social or enterprise accounts, without having to create a new account just for your application.
On the sign-up or sign-in page, Azure AD B2C presents a list of external identity providers the user can choose for sign-in. Once they select one of the external identity providers, they're redirected to the selected provider's website to complete the sign-in process. After the user successfully signs in, they're returned to Azure AD B2C for authentication of the account in your application.
You can add identity providers that are supported by Azure Active Directory B2C (Azure AD B2C) to your user flows using the Azure portal. You can also add identity providers to your custom policies.
Next steps
- Find out more about the built-in policies provided by User flows in Azure Active Directory B2C.
- Configure your local account identity provider.