Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
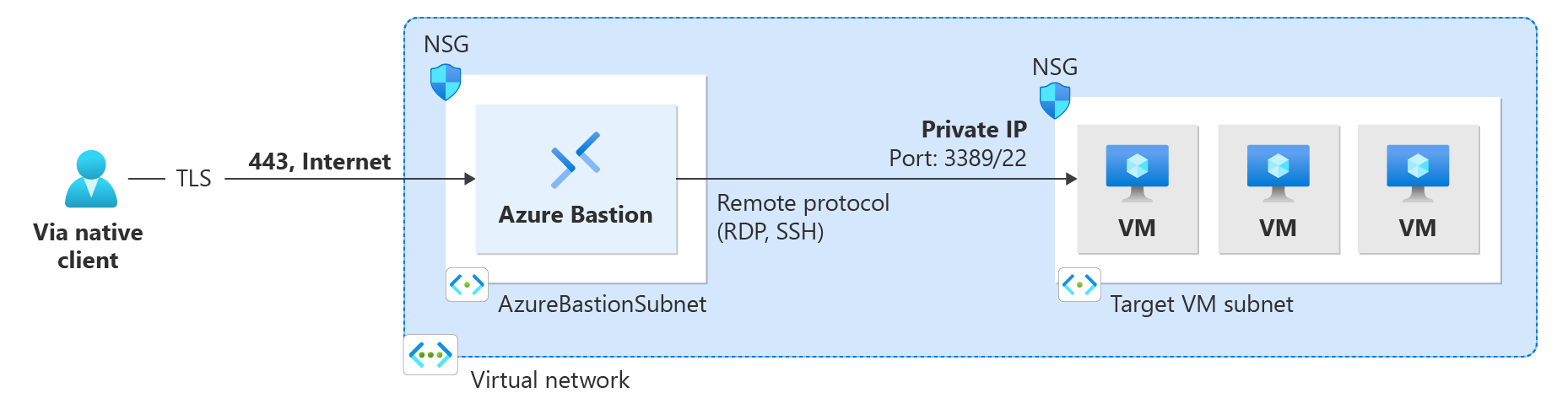
This article helps you connect to a VM in the virtual network using the native client (SSH or RDP) on your local Windows computer. The native client feature lets you connect to your target VMs via Bastion using Azure CLI, and expands your sign-in options to include local SSH key pair and Microsoft Entra ID. For more information and steps to configure Bastion for native client connections, see Configure Bastion for native client connections. Connections via native client require the Bastion Standard SKU or higher.
After you've configured Bastion for native client support, you can connect to a VM using a native Windows client. The method you use to connect depends on both the client you're connecting from, and the VM you're connecting to. The following list shows some of the available ways you can connect from a Windows native client. See Connect to VMs for the full list showing available client connection/feature combinations.
- Connect to a Windows VM using az network bastion rdp.
- Connect to a Linux VM using az network bastion ssh.
- Connect to a VM using az network bastion tunnel.
- Transfer files over RDP.
- Transfer files over SSH using az network bastion tunnel.
Prerequisites
Before you begin, verify that you have the following prerequisites:
- The latest version of the CLI commands (version 2.32 or later) is installed. You can update your CLI for Bastion using
az extension update --name bastion. For information about installing the CLI commands, see Install the Azure CLI and Get Started with Azure CLI. - Azure Bastion is already deployed and configured for your virtual network. For steps, see Configure Bastion for native client connections.
- A virtual machine in the virtual network.
- The VM's Resource ID. The Resource ID can be easily located in the Azure portal. Go to the Overview page for your VM and select the JSON View link to open the Resource JSON. Copy the Resource ID at the top of the page to your clipboard to use later when connecting to your VM.
- If you plan to sign in to your virtual machine using your Microsoft Entra credentials, make sure your virtual machine is set up using one of the following methods:
- Enable Microsoft Entra sign-in for a Windows VM or Linux VM.
- Configure your Windows VM to be Microsoft Entra joined.
- Configure your Windows VM to be Microsoft Entra hybrid joined.
Verify roles and ports
Verify that the following roles and ports are configured in order to connect to the VM.
Required roles
Reader role on the virtual machine.
Reader role on the NIC with private IP of the virtual machine.
Reader role on the Azure Bastion resource.
Virtual Machine Administrator Login or Virtual Machine User Login role, if you're using the Microsoft Entra sign-in method. You only need to do this if you're enabling Microsoft Entra login using the processes outlined in one of these articles:
Ports
To connect to a Linux VM using native client support, you must have the following ports open on your Linux VM:
- Inbound port: SSH (22) or
- Inbound port: Custom value (you'll then need to specify this custom port when you connect to the VM via Azure Bastion)
To connect to a Windows VM using native client support, you must have the following ports open on your Windows VM:
- Inbound port: RDP (3389) or
- Inbound port: Custom value (you'll then need to specify this custom port when you connect to the VM via Azure Bastion)
To learn about how to best configure NSGs with Azure Bastion, see Working with NSG access and Azure Bastion.
Connect to a VM
The steps in the following sections help you connect to a VM from a Windows native client using the az network bastion command.
RDP to a Windows VM
When a user connects to a Windows VM via RDP, they must have rights on the target VM. If the user isn't a local administrator, add the user to the Remote Desktop Users group on the target VM.
Sign in to your Azure account using
az login. If you have more than one subscription, you can view them usingaz account listand select the subscription containing your Bastion resource usingaz account set --subscription "<subscription ID>".Note
Before you can use Azure CLI in Microsoft Azure operated by 21Vianet, please run
az cloud set -n AzureChinaCloudfirst to change the cloud environment. If you want to switch back to Azure Public Cloud, runaz cloud set -n AzureCloudagain.To connect via RDP, use the following example.
az network bastion rdp --name "<BastionName>" --resource-group "<ResourceGroupName>" --target-resource-id "<VMResourceId>"After running the command, you're prompted to input your credentials. You can use either a local username and password, or your Microsoft Entra credentials. Once you sign in to your target VM, the native client on your computer opens up with your VM session via MSTSC.
Important
Remote connection to VMs that are joined to Microsoft Entra ID is allowed only from Windows 10 or later PCs that are Microsoft Entra registered (starting with Windows 10 20H1), Microsoft Entra joined, or Microsoft Entra hybrid joined to the same directory as the VM.
Specify authentication method
Optionally, you can also specify the authentication method as part of the command.
- Microsoft Entra authentication: For Windows 10 version 20H2+, Windows 11 21H2+, and Windows Server 2022, use
--enable-mfa. For more information, see az network bastion rdp - optional parameters.
Specify a custom port
You can specify a custom port when you connect to a Windows VM via RDP.
One scenario where this could be especially useful would be connecting to a Windows VM via port 22. This is a potential workaround for the limitation with the az network bastion ssh command, which can't be used by a Windows native client to connect to a Windows VM.
To specify a custom port, include the field --resource-port in the sign-in command, as shown in the following example.
az network bastion rdp --name "<BastionName>" --resource-group "<ResourceGroupName>" --target-resource-id "<VMResourceId>" --resource-port "22"
RDP to a Windows VM IP address
You can also connect to a VM private IP address, instead of the resource ID. Microsoft Entra authentication, and custom ports and protocols aren't supported when using this type of connection. For more information about IP-based connections, see Connect to a VM - IP address.
Using the az network bastion command, replace --target-resource-id with --target-ip-address and the specified IP address to connect to your VM.
az network bastion rdp --name "<BastionName>" --resource-group "<ResourceGroupName>" --target-ip-address "<VMIPAddress>"
SSH to a Linux VM
Sign in to your Azure account using
az login. If you have more than one subscription, you can view them usingaz account listand select the subscription containing your Bastion resource usingaz account set --subscription "<subscription ID>".Sign in to your target Linux VM using one of the following example options. If you want to specify a custom port value, include the field --resource-port in the sign-in command.
Microsoft Entra ID:
If you're signing in to a Microsoft Entra login-enabled VM, use the following command. For more information, see Azure Linux VMs and Microsoft Entra ID.
az network bastion ssh --name "<BastionName>" --resource-group "<ResourceGroupName>" --target-resource-id "<VMResourceId or VMSSInstanceResourceId>" --auth-type "AAD"SSH key pair:
The extension can be installed by running,
az extension add --name ssh. To sign in using an SSH key pair, use the following example.az network bastion ssh --name "<BastionName>" --resource-group "<ResourceGroupName>" --target-resource-id "<VMResourceId or VMSSInstanceResourceId>" --auth-type "ssh-key" --username "<Username>" --ssh-key "<Filepath>"Username/password:
If you're signing in using a local username and password, use the following command. You'll then be prompted for the password for the target VM.
az network bastion ssh --name "<BastionName>" --resource-group "<ResourceGroupName>" --target-resource-id "<VMResourceId or VMSSInstanceResourceId>" --auth-type "password" --username "<Username>"Once you sign in to your target VM, the native client on your computer opens up with your VM session using SSH CLI extension (az ssh).
SSH to a Linux VM IP address
You can also connect to a VM private IP address, instead of the resource ID. Microsoft Entra authentication, and custom ports and protocols aren't supported when using this type of connection. For more information about IP-based connections, see Connect to a VM - IP address.
Using the az network bastion command, replace --target-resource-id with --target-ip-address and the specified IP address to connect to your VM.
az network bastion ssh --name "<BastionName>" --resource-group "<ResourceGroupName>" --target-ip-address "<VMIPAddress>" --auth-type "ssh-key" --username "<Username>" --ssh-key "<Filepath>"
Connect to a VM - tunnel command
The az network bastion tunnel command is another way that you can connect to your VMs. When you use this command, you can do the following:
- Connect from native clients on non-Windows local computers. (For example, a Linux computer.)
- Connect to a VM using SSH or RDP. (The bastion tunnel doesn't relay web servers or hosts.)
- Use the native client of your choice.
- Transfer files to your target VM from your local computer.
Limitations:
- Signing in using an SSH private key stored in Azure Key Vault isn't supported with this feature. Before signing in to your Linux VM using an SSH key pair, download your private key to a file on your local machine.
Steps:
Sign in to your Azure account using
az login. If you have more than one subscription, you can view them usingaz account listand select the subscription containing your Bastion resource usingaz account set --subscription "<subscription ID>".Open the tunnel to your target VM. Without root privileges use local port 1024 or above as ports below that are privileged ports only accessible by root.
az network bastion tunnel --name "<BastionName>" --resource-group "<ResourceGroupName>" --target-resource-id "<VMResourceId or VMSSInstanceResourceId>" --resource-port "<TargetVMPort>" --port "<LocalMachinePort>"Connect to your target VM using SSH or RDP, the native client of your choice, and the local machine port you specified in the previous step.
For example, you can use the following command if you have the OpenSSH client installed on your local computer:
ssh <username>@127.0.0.1 -p <LocalMachinePort>
Tunnel to a VM IP address
You can also connect to a VM private IP address, instead of the resource ID. Microsoft Entra ID authentication, and custom ports and protocols, aren't supported when using this type of connection. For more information about IP-based connections, see Connect to a VM - IP address.
Using the az network bastion tunnel command, replace --target-resource-id with --target-ip-address and the specified IP address to connect to your VM.
az network bastion tunnel --name "<BastionName>" --resource-group "<ResourceGroupName>" --target-ip-address "<VMIPAddress>" --resource-port "<TargetVMPort>" --port "<LocalMachinePort>"
Multi-connection tunnel
Add the following to your $HOME.ssh\config.
Host tunneltunnel HostName 127.0.0.1 Port 2222 User mylogin StrictHostKeyChecking=No UserKnownHostsFile=\\.\NULAdd the tunnel connection to your established tunnel connection.
az network bastion tunnel --name mybastion --resource-group myrg --target-resource-id /subscriptions/<mysubscription>/resourceGroups/myrg/providers/Microsoft.Compute/virtualMachines/myvm --resource-port 22 --port 22Create an ssh tunnel in the bastion tunnel.
ssh -L 2222:127.0.0.1:22 mylogin@127.0.0.1Use VS Code to connect to your tunnel connection.