Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Important
Attention: All Microsoft Defender for Cloud features will be officially retired in Azure in China region on August 18, 2026 per the announcement posted by 21Vianet.
Important
This article applies to commercial clouds. If you're using Microsoft Azure operated by 21Vianet, see the Enable Defender for SQL servers on Machines government article.
The Defender for SQL Servers on Machines plan is one of the Defender for Databases plans in Microsoft Defender for Cloud. Use Defender for SQL Servers on Machines to protect SQL virtual machines (VM) and Azure Arc SQL Server instances.
Important
The Defender for SQL Servers on Machines plan is undergoing a transition to the new agent architecture. For more information, see Defender for SQL Servers on Machines plan transition.
Prerequisites
Subscription permissions: To deploy the plan on a subscription, including Azure Policy, you need Subscription Owner permissions.
SQL Server instance permissions: SQL Server service accounts must be a member of the sysadmin fixed server role on each SQL Server instance, which is the default setting. Learn more about the SQL Server service account requirement.
Supported Resources:
- SQL virtual machines, and Azure Arc SQL Server instances are supported.
- On-premises machines must be onboarded to Arc and registered as Azure Arc SQL Server instances.
Communication: Allow outbound HTTPS traffic on Transmission Control Protocol (TCP) port 443 using Transport Layer Security (TLS) to *.<region>.arcdataservices.com URL. Learn more about URL requirements.
Extensions: Ensure these extensions aren't blocked in your environment. Learn more about restricting extensions installation on Windows VMs.
- Defender for SQL (IaaS and Arc)
- Publisher: Microsoft.Azure.AzureDefenderForSQL
- Type: AdvancedThreatProtection.Windows
- SQL IaaS Extension (IaaS)
- Publisher: Microsoft.SqlServer.Management
- Type: SqlIaaSAgent
- SQL IaaS Extension (Arc)
- Publisher: Microsoft.AzureData
- Type: WindowsAgent.SqlServer
- Defender for SQL (IaaS and Arc)
Supported SQL Server versions - SQL Server 2012 (11.x) and later versions.
Supported operating systems- Windows Server 2012 R2 and later versions.
Note
Azure Arc SQL Server instances with the Arc proxy feature enabled are not currently supported. Arc proxy is an optional connectivity feature for Azure Arc-enabled servers.
Enable the plan
Enable the plan on an Azure subscription
To enable the Defender for SQL servers on machines plan, you need to enable the Defender for Databases plan on your subscription. The Defender for SQL servers on machines plan is included in the Defender for Databases plan.
Sign in to the Azure portal.
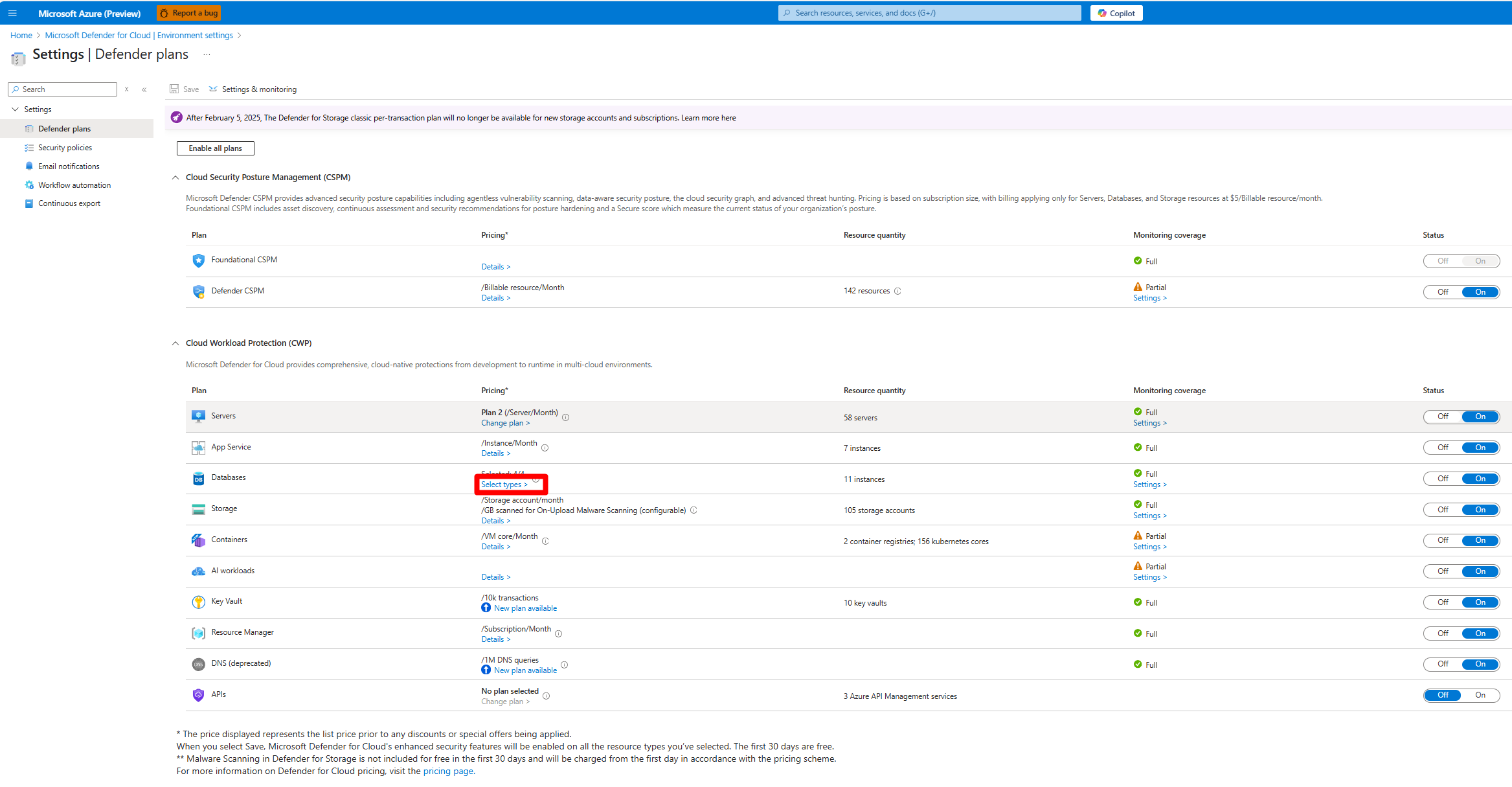
Navigate to Microsoft Defender for Cloud > Environment settings.
Select the relevant subscription.
On the Defender plans page, locate the Databases plan and select Select types.
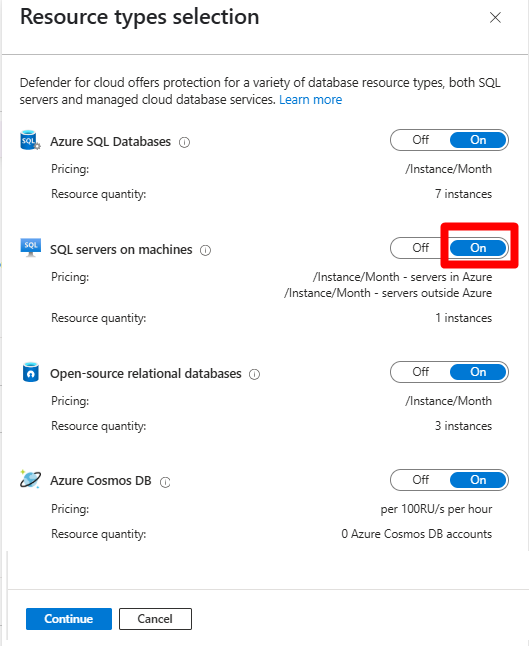
In the Resource types selection window, toggle the SQL Servers on Machines plan to On.
Select Continue > Save.
Enable the plan at the SQL Server resource level
We recommend enabling the plan on your entire Azure subscription. However, you might need to enable Defender for SQL on machines on specific machines.
To enable the plan on specific machines, you need to disable the plan on the subscription and apply the following instructions to the relevant machines at the resource level.
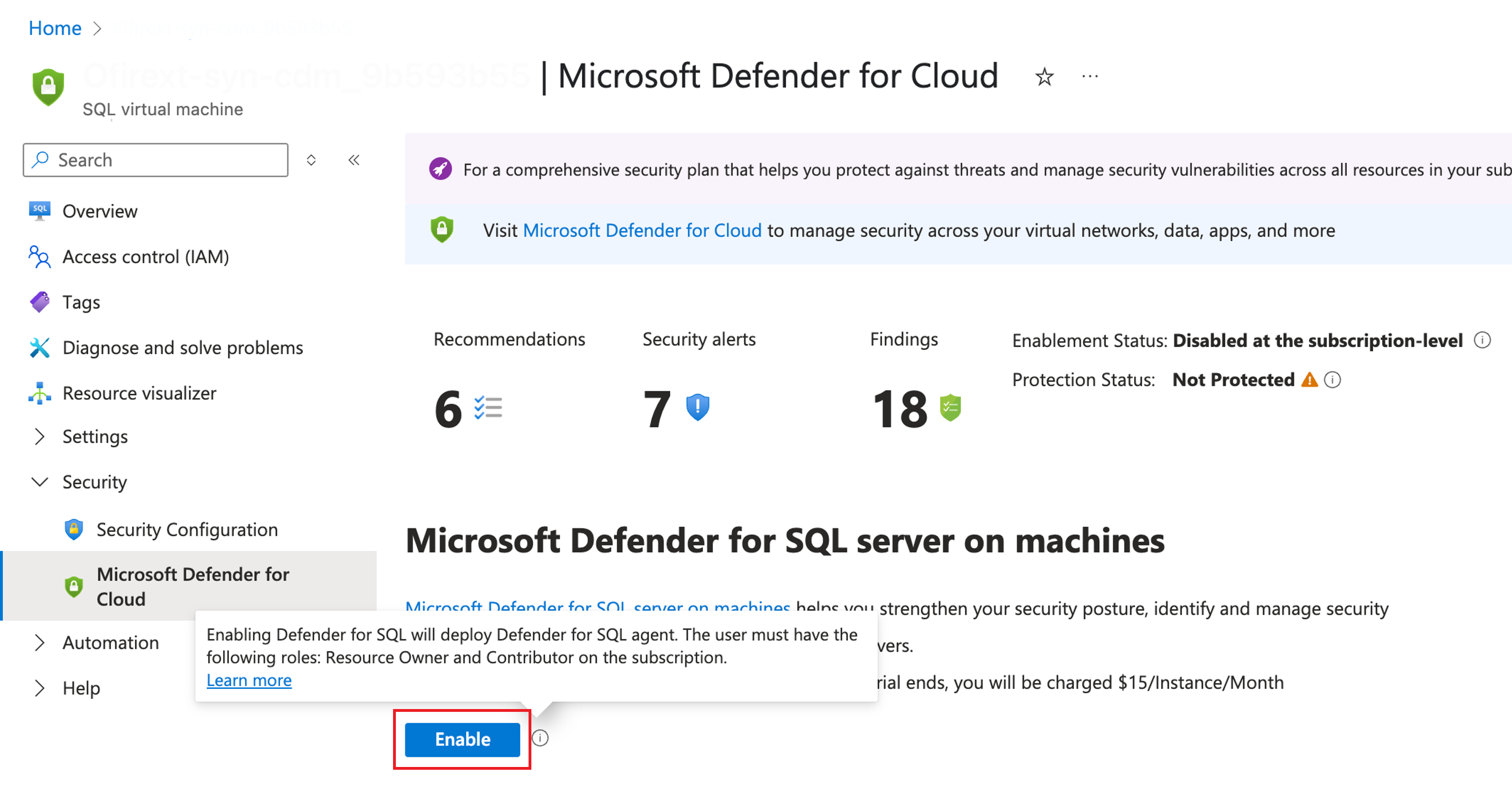
In the Azure portal, search for and select:
- Azure Arc > Data services > SQL Server instances.
or - SQL virtual machines.
- Azure Arc > Data services > SQL Server instances.
Select the relevant SQL Server instance.
Locate the security menu and select Microsoft Defender for Cloud.
Select Enable Microsoft Defender for SQL servers on Machines.
Verify that your machines are protected
Important
Don't skip this step, as it's important to verify your deployment is protected.
Depending on your environment, it can take a few hours to discover and protect SQL instances. As a final step, you should verify that all machines are protected.