Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Important
Attention: All Microsoft Defender for Cloud features will be officially retired in Azure in China region on August 18, 2026 per the announcement posted by 21Vianet.
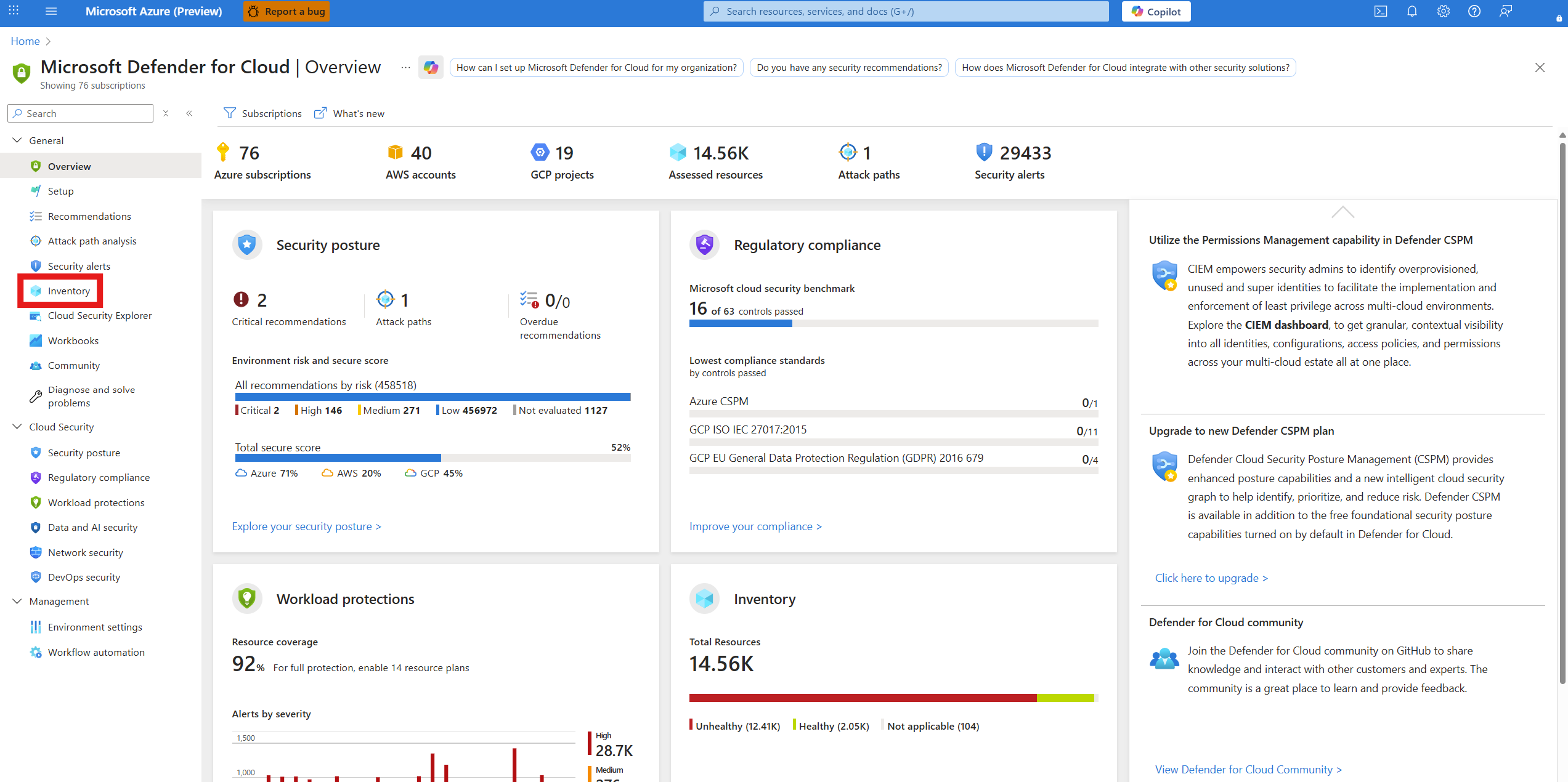
Microsoft Defender for Cloud continuously analyzes the security state of your Azure resources for network security best practices. When Defender for Cloud identifies potential security vulnerabilities, it creates recommendations that guide you through the process of configuring the needed controls to harden and protect your resources.
Review Defender for Cloud networking recommendations.
This article addresses recommendations that apply to your Azure resources from a network security perspective. Networking recommendations center around next generation firewalls, Network Security Groups, Just In Time (JIT) Virtual Machine (VM) access, overly permissive inbound traffic rules, and more. For a list of networking recommendations and remediation actions, see Managing security recommendations in Microsoft Defender for Cloud.
Review networking resources and their recommendations
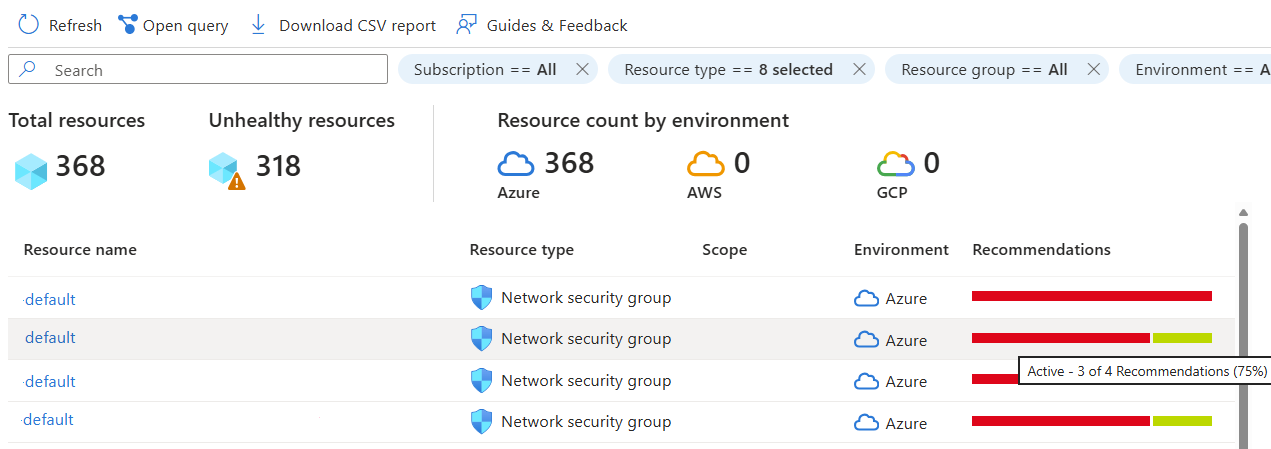
The inventory page shows your resources by type. Use the resource type filter to see only the networking resources in your environment.
Sign in to the Azure portal.
Go to Microsoft Defender for Cloud > Inventory.
Select the Resource type filter.
Enter Network.
Select the relevant resource types.
Select Apply.
Hover over the recommendation indicator to see the number of active recommendations for each resource.
Select a resource to view the affiliated recommendations.
Select a recommendation.