Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Use an allow list or block list to control which organizations can receive B2B collaboration invitations. For example, to block personal email domains, add domains like Gmail.com and Outlook.com to a block list. To allow invitations only to partner organizations, add domains such as Contoso.com, Fabrikam.com, and Litware.com to an allow list.
This article explains how to configure an allow list or block list for B2B collaboration.
- In the portal by configuring collaboration restrictions in your organization's External collaboration settings
Important considerations
- You can create either an allow list or a block list. You can't set up both types of lists. By default, whatever domains aren't in the allow list are on the block list, and vice versa.
- You can create only one policy per organization. You can update the policy to include more domains, or you can delete the policy to create a new one.
- The number of domains you can add to an allow list or block list is limited only by the size of the policy. This limit applies to the number of characters, so you can have a greater number of shorter domains or fewer longer domains. The maximum size of the entire policy is 25 KB (25,000 characters), which includes the allow list or block list and any other parameters configured for other features.
- This list works independently from OneDrive and SharePoint Online allow/block lists. If you want to restrict individual file sharing in SharePoint Online, you need to set up an allow or block list for OneDrive and SharePoint Online. For more information, see Restrict sharing of SharePoint and OneDrive content by domain.
- The list doesn't apply to external users who already redeemed the invitation. The list will be enforced after the list is set up. If a user invitation is in a pending state, and you set a policy that blocks their domain, the user's attempt to redeem the invitation fails.
- Both allow/block list and cross-tenant access settings are checked at the time of invitation.
Set the allow or block list policy in the portal
By default, the Allow invitations to be sent to any domain (most inclusive) setting is enabled. In this case, you can invite B2B users from any organization.
Important
Microsoft recommends that you use roles with the fewest permissions. This practice helps improve security for your organization. Global Administrator is a highly privileged role that should be limited to emergency scenarios or when you can't use an existing role.
Add a block list
This is the most common scenario, where your organization wants to work with almost any organization but wants to prevent users from specific domains from being invited as B2B users.
To add a block list:
Sign in to the Microsoft Entra admin center as a Global Administrator.
Browse to Entra ID > External Identities > External collaboration settings.
Under Collaboration restrictions, select Deny invitations to the specified domains.
Under Target domains, enter the name of one of the domains that you want to block. For multiple domains, enter each domain on a new line. For example:
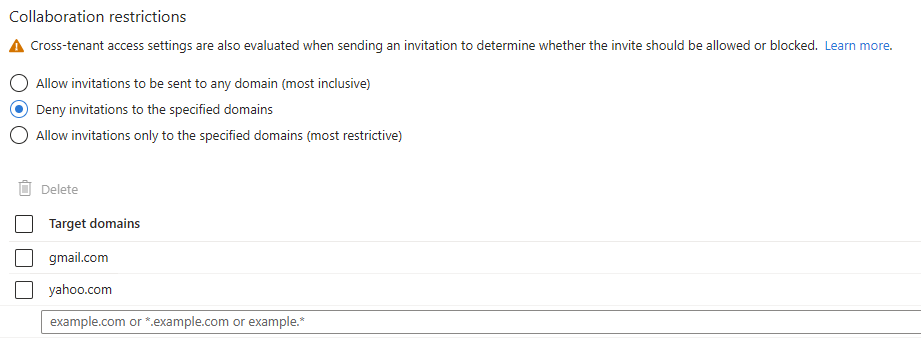
When you're done, select Save.
After you save the policy, invitations to blocked domains fail and the inviter sees a blocked-domain message.
Add an allow list
This is a more restrictive configuration. Only domains in the allow list can receive invitations.
If you want to use an allow list, take time to fully evaluate your business needs. If you make this policy too restrictive, users might send documents over email or use other unsanctioned ways to collaborate.
To add an allow list:
Sign in to the Microsoft Entra admin center as a Global Administrator.
Browse to Entra ID > External Identities > External collaboration settings.
Under Collaboration restrictions, select Allow invitations only to the specified domains (most restrictive).
Under Target domains, enter the name of one of the domains that you want to allow. For multiple domains, enter each domain on a new line. For example:
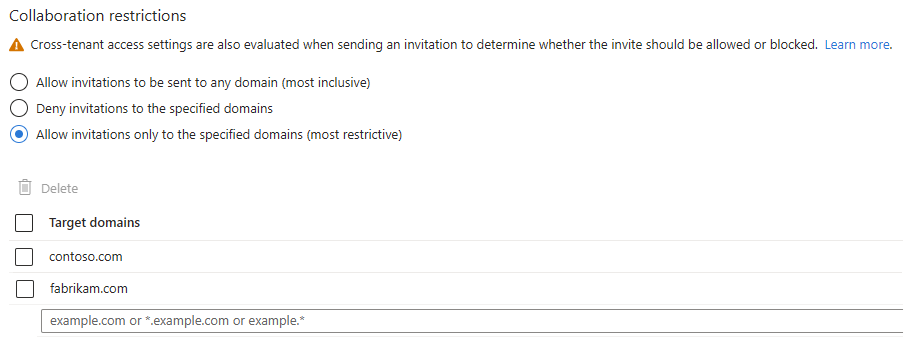
When you're done, select Save.
After you save the policy, invitations to domains not in the allow list fail, and the inviter sees a blocked-domain message.
Switch from allow list to block list and vice versa
Switching from one policy to another discards the existing policy configuration. Make sure to back up details of your configuration before you perform the switch.