Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Azure provides integrated access control management for resources and applications based on Microsoft Entra ID. A key advantage of using Microsoft Entra ID with Azure Event Hubs is that you don't need to store credentials in code. Instead, request an OAuth 2.0 access token from the Microsoft identity platform. The resource name to request a token is https://eventhubs.chinacloudapi.cn/, and it's the same for all clouds/tenants (For Kafka clients, the resource to request a token is https://<namespace>.servicebus.chinacloudapi.cn). Microsoft Entra authenticates the security principal, such as a user, group, service principal, or managed identity, running the application. If authentication succeeds, Microsoft Entra ID returns an access token to the application, which can then use the token to authorize requests to Azure Event Hubs resources.
When a role is assigned to a Microsoft Entra security principal, Azure grants access to those resources for that security principal. Access can be scoped to the subscription, resource group, Event Hubs namespace, or any resource under it. A Microsoft Entra security principal can assign roles to a user, group, application service principal, or a managed identity for Azure resources.
Note
A role definition is a collection of permissions. Azure role-based access control (Azure RBAC) enforces these permissions through role assignment. A role assignment includes three elements: security principal, role definition, and scope. For more information, see Understanding the different roles.
Built-in roles for Azure Event Hubs
Azure provides these built-in roles to authorize access to Event Hubs data using Microsoft Entra ID and OAuth:
- Azure Event Hubs Data Owner: Use this role to give complete access to Event Hubs resources.
- Azure Event Hubs Data Sender: A security principal assigned to this role can send events to a specific event hub or all event hubs in a namespace.
- Azure Event Hubs Data Receiver: A security principal assigned to this role can receive events from a specific event hub or all event hubs in a namespace.
For Schema Registry built-in roles, see Schema Registry roles.
Important
The preview release supported adding Event Hubs data access privileges to the Owner or Contributor role. However, these privileges are no longer honored. If you're using the Owner or Contributor role, switch to the Azure Event Hubs Data Owner role.
Authenticate from an application
A key advantage of using Microsoft Entra ID with Event Hubs is that you don't need to store your credentials in your code. Instead, request an OAuth 2.0 access token from Microsoft identity platform. Microsoft Entra authenticates the security principal (a user, a group, or service principal) running the application. If authentication succeeds, Microsoft Entra ID returns the access token to the application, and the application can then use the access token to authorize requests to Azure Event Hubs.
The following sections explain how to configure a native application or web application for authentication with Microsoft identity platform 2.0. For more information about Microsoft identity platform 2.0, see Microsoft identity platform (v2.0) overview.
For an overview of the OAuth 2.0 code grant flow, see Authorize access to Microsoft Entra web applications using the OAuth 2.0 code grant flow.
Register your application with Microsoft Entra ID
The first step to use Microsoft Entra ID to authorize Event Hubs resources is to register a client application with a Microsoft Entra tenant in the Azure portal. Follow steps in the Quickstart: Register an application with the Microsoft identity platform to register an application in Microsoft Entra ID that represents your application trying to access Event Hubs resources.
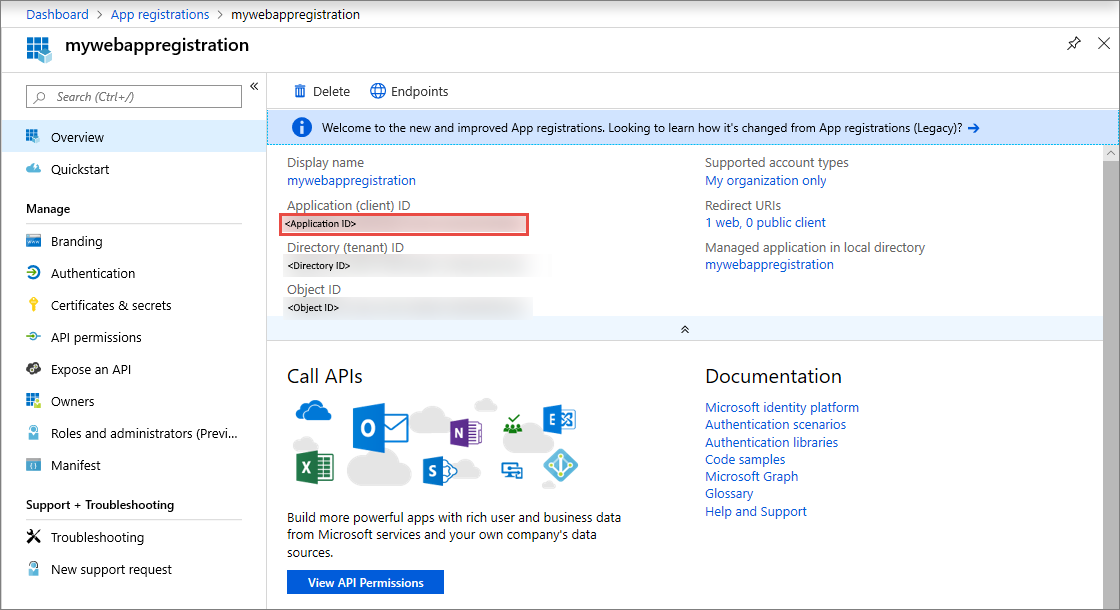
When you register your client application, you supply information about the application. Microsoft Entra ID provides a client ID, also called an application ID, to associate the application with Microsoft Entra runtime. To learn more about the client ID, see Application and service principal objects in Microsoft Entra ID.
Note
If you register the application as a native application, specify any valid URI for the Redirect URI. For native applications, this value doesn't need to be a real URL. For web applications, the redirect URI must be a valid URI because it specifies the URL where tokens are provided.
After you register your application, you see the Application (client) ID under Settings:
Create a client secret for authentication
The application requires a client secret to prove its identity when requesting a token. Follow steps from Add a client secret to create a client secret for your app in Microsoft Entra ID.
Assign Azure roles using the Azure portal
Assign one of the Event Hubs roles to the application's service principal at the desired scope, such as the Event Hubs namespace, resource group, or subscription. For detailed steps, see Assign Azure roles using the Azure portal.
After defining the role and its scope, test this behavior with samples available in this GitHub location. To learn more about managing access to Azure resources using Azure role-based access control (RBAC) and the Azure portal, see this article.
Use client libraries to acquire tokens
After registering your application and granting it permissions to send or receive data in Azure Event Hubs, add code to your application to authenticate a security principal and acquire an OAuth 2.0 token. To authenticate and acquire the token, use one of the Microsoft identity platform authentication libraries or another open-source library that supports OpenID Connect 1.0. Your application can then use the access token to authorize a request against Azure Event Hubs.
For scenarios where acquiring tokens is supported, see the Scenarios section of the Microsoft Authentication Library (MSAL) for .NET GitHub repository.
Samples
- RBAC samples using the legacy .NET Microsoft.Azure.EventHubs package. We're working on creating a new version of this sample using the latest Azure.Messaging.EventHubs package. See the already converted Managed Identity.
- RBAC sample using the legacy Java com.microsoft.azure.eventhubs package. Use the migration guide to migrate this sample to use the new package (
com.azure.messaging.eventhubs). To learn more about using the new package, see samples here.
Related content
To learn more about Azure RBAC, see What is Azure role-based access control (Azure RBAC).
To learn how to assign and manage Azure role assignments with Azure PowerShell, Azure CLI, or the REST API, see these articles.
See the following related articles: