Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Important
This article covers private endpoints for the classic Microsoft Purview governance portal (https://web.purview.azure.cn). In this guide, you'll learn how to deploy private endpoints for your Microsoft Purview account to allow you to connect to your Microsoft Purview account only from VNets and private networks. To achieve this goal, you need to deploy account and portal private endpoints for your Microsoft Purview account.
The Microsoft Purview account private endpoint is used to add another layer of security by enabling scenarios where only client calls that originate from within the virtual network are allowed to access the Microsoft Purview account. This private endpoint is also a prerequisite for the portal private endpoint.
The Microsoft Purview portal private endpoint is required to enable connectivity to the classic Microsoft Purview governance portal using a private network.
Note
If you only create account and portal private endpoints, you won't be able to run any scans. To enable scanning on a private network, you will also need to create an ingestion private endpoint.
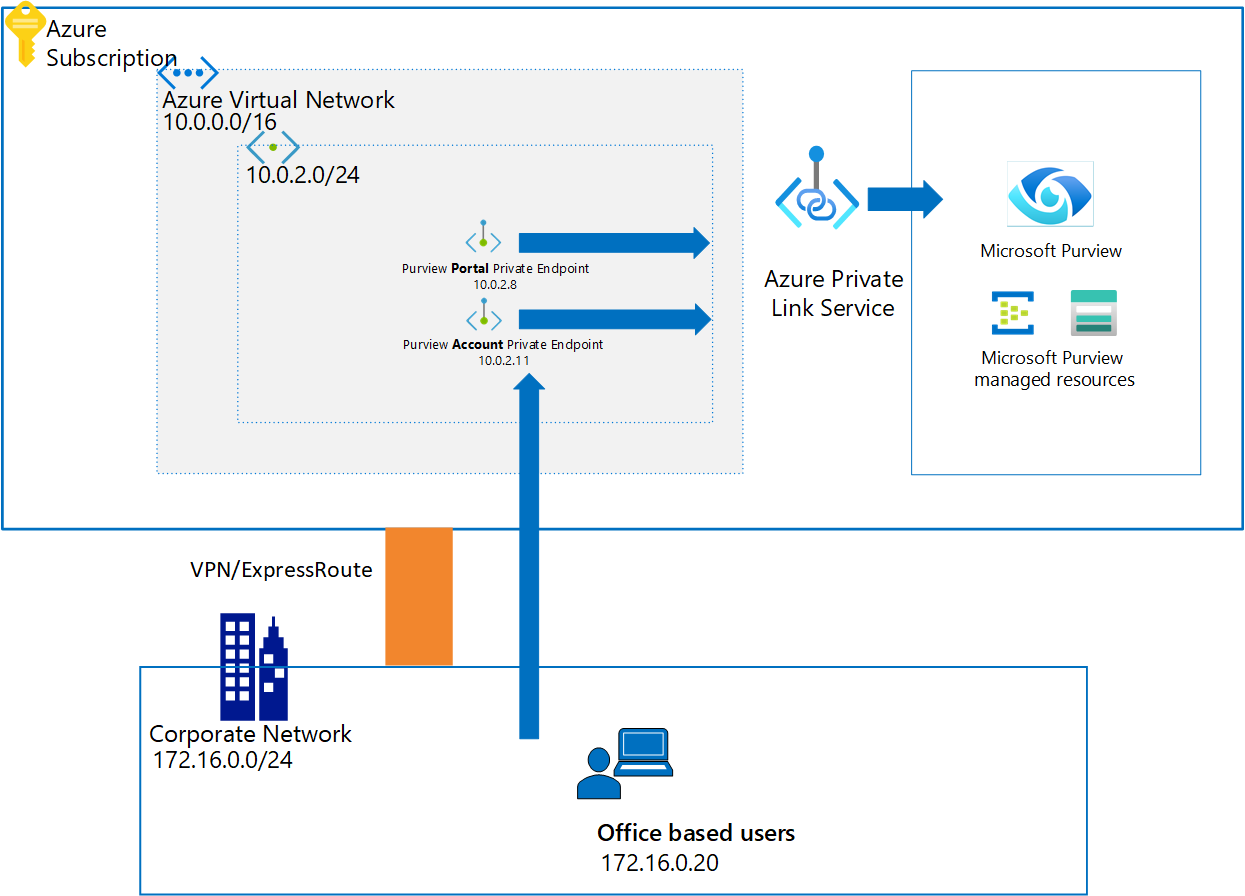
For more information about Azure Private Link service, see private links and private endpoints to learn more.
Deployment checklist
Using this guide, you can deploy these private endpoints for an existing Microsoft Purview account:
Choose an appropriate Azure virtual network and a subnet to deploy Microsoft Purview private endpoints. Select one of the following options:
- Deploy a new virtual network in your Azure subscription.
- Locate an existing Azure virtual network and a subnet in your Azure subscription.
Define an appropriate DNS name resolution method, so Microsoft Purview account and web portal can be accessible through private IP addresses. You can use any of the following options:
- Deploy new Azure DNS zones using the steps explained further in this guide.
- Add required DNS records to existing Azure DNS zones using the steps explained further in this guide.
- After completing the steps in this guide, add required DNS A records in your existing DNS servers manually.
Deploy account and portal private endpoints for an existing Microsoft Purview account.
Enable access to Microsoft Entra ID if your private network has network security group rules set to deny for all public internet traffic.
After completing this guide, adjust DNS configurations if needed.
Validate your network and name resolution from management machine to Microsoft Purview.
Enable account and portal private endpoint
There are two ways you can add Microsoft Purview account and portal private endpoints for an existing Microsoft Purview account:
- Use the Azure portal (Microsoft Purview account).
- Use the Private Link Center.
Use the Azure portal (Microsoft Purview account)
Go to the Azure portal, and then select your Microsoft Purview account, and under Settings select Networking, and then select Private endpoint connections.
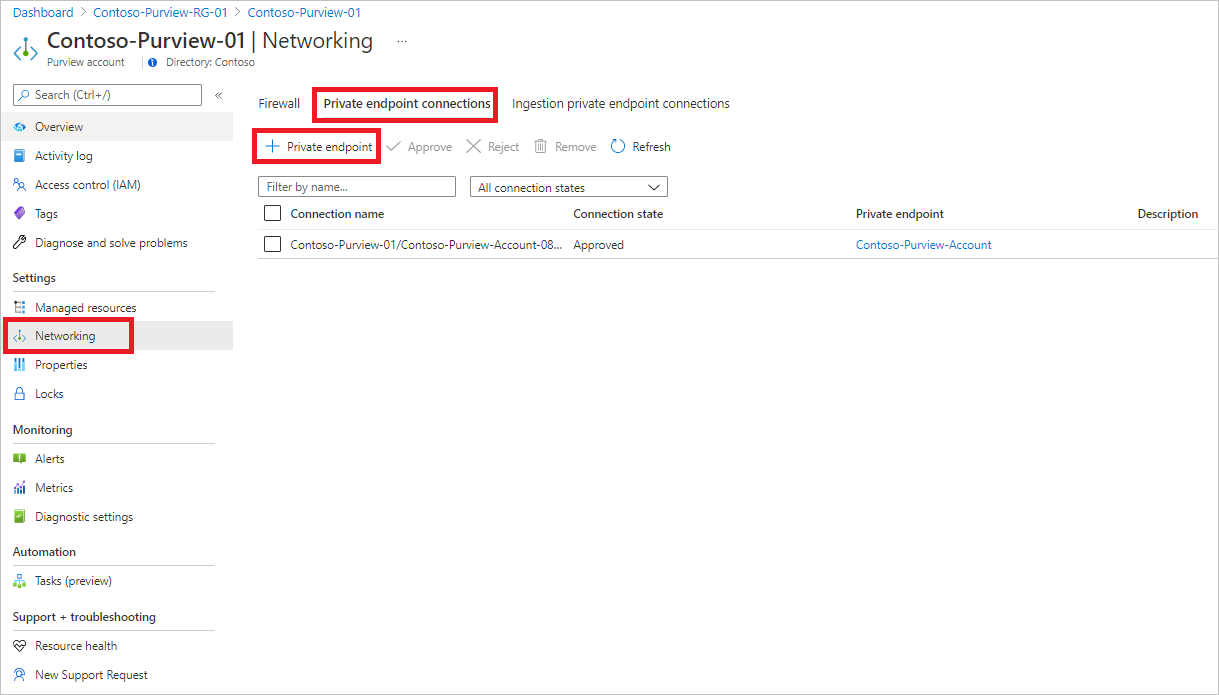
Select + Private endpoint to create a new private endpoint.
Fill in the basic information.
On the Resource tab, for Resource type, select Microsoft.Purview/accounts.
For Resource, select the Microsoft Purview account, and for Target sub-resource, select account.
On the Configuration tab, select the virtual network and optionally, select Azure Private DNS zone to create a new Azure DNS Zone.
Note
For DNS configuration, you can also use your existing Azure Private DNS Zones from the dropdown list or add the required DNS records to your DNS Servers manually later. For more information, see Configure DNS Name Resolution for private endpoints
Go to the summary page, and select Create to create the portal private endpoint.
Follow the same steps when you select portal for Target sub-resource.
Use the Private Link Center
Go to the Azure portal.
In the search bar at the top of the page, search for private link and go to the Private Link pane by selecting the first option.
Select + Add, and fill in the basic details.
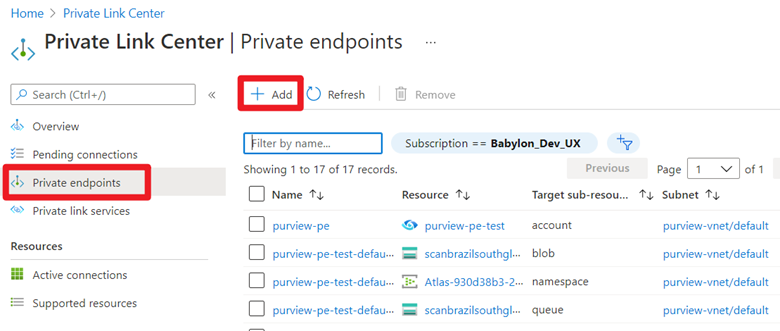
For Resource, select the already created Microsoft Purview account. For Target sub-resource, select account.
On the Configuration tab, select the virtual network and private DNS zone. Go to the summary page, and select Create to create the account private endpoint.
Note
Follow the same steps when you select portal for Target sub-resource.
Enable access to Microsoft Entra ID
Note
If your VM, VPN gateway, or VNet Peering gateway has public internet access, it can access the Microsoft Purview portal and the Microsoft Purview account enabled with private endpoints. For this reason, you don't have to follow the rest of the instructions. If your private network has network security group rules set to deny all public internet traffic, you'll need to add some rules to enable Microsoft Entra ID access. Follow the instructions to do so.
These instructions are provided for accessing Microsoft Purview securely from an Azure VM. Similar steps must be followed if you're using VPN or other virtual network Peering gateways.
Go to your VM in the Azure portal, and under Settings, select Networking. Then select Outbound port rules, Add outbound port rule.
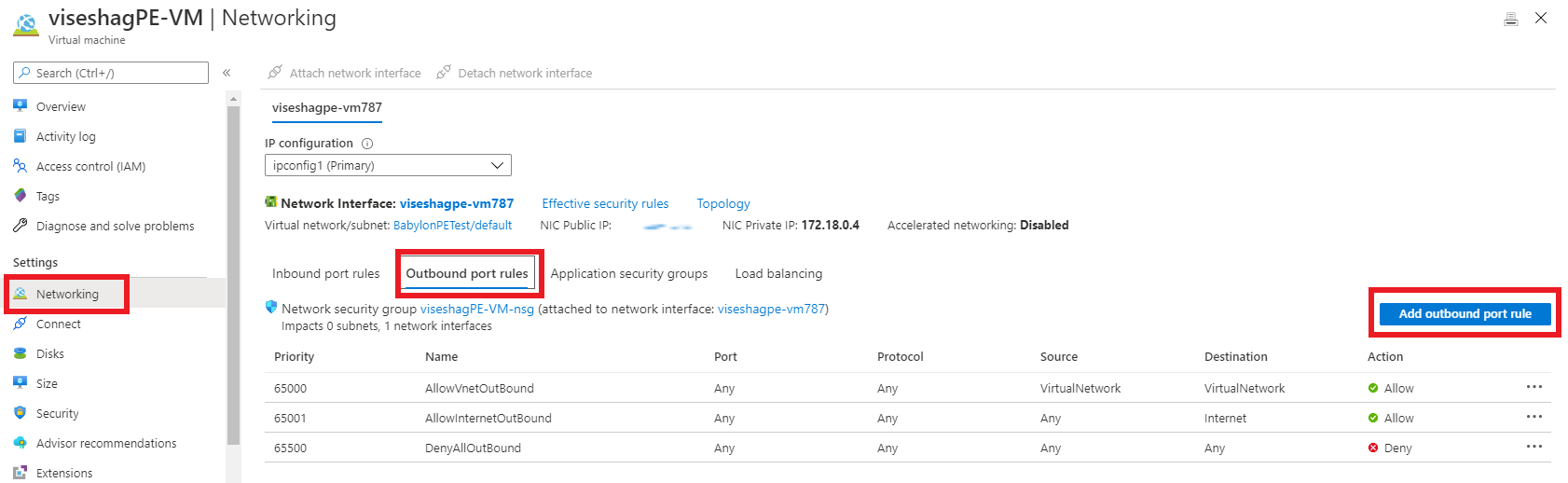
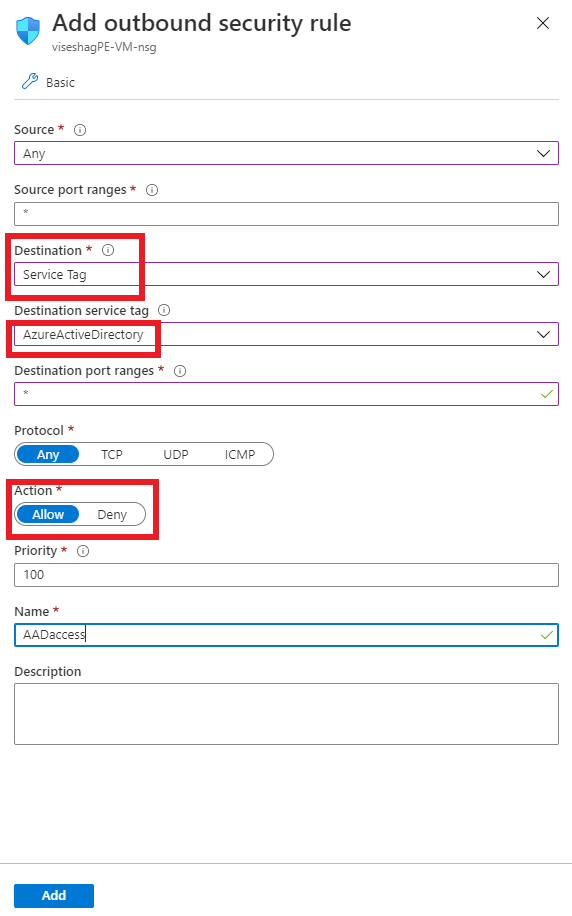
On the Add outbound security rule pane:
- Under Destination, select Service Tag.
- Under Destination service tag, select AzureActiveDirectory.
- Under Destination port ranges, select *.
- Under Action, select Allow.
- Under Priority, the value should be higher than the rule that denied all internet traffic.
Create the rule.
Follow the same steps to create another rule to allow the AzureResourceManager service tag. If you need to access the Azure portal, you can also add a rule for the AzurePortal service tag.
Connect to the VM and open the browser. Go to the browser console by selecting Ctrl+Shift+J, and switch to the network tab to monitor network requests. Enter web.purview.azure.cn in the URL box, and try to sign in by using your Microsoft Entra credentials. Sign-in will probably fail, and on the Network tab on the console, you can see Microsoft Entra ID trying to access aadcdn.msauth.net but getting blocked.
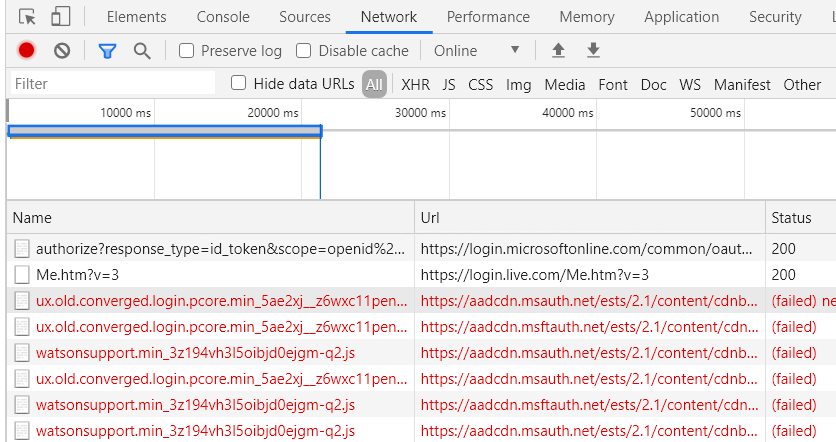
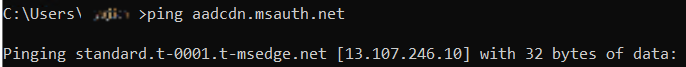
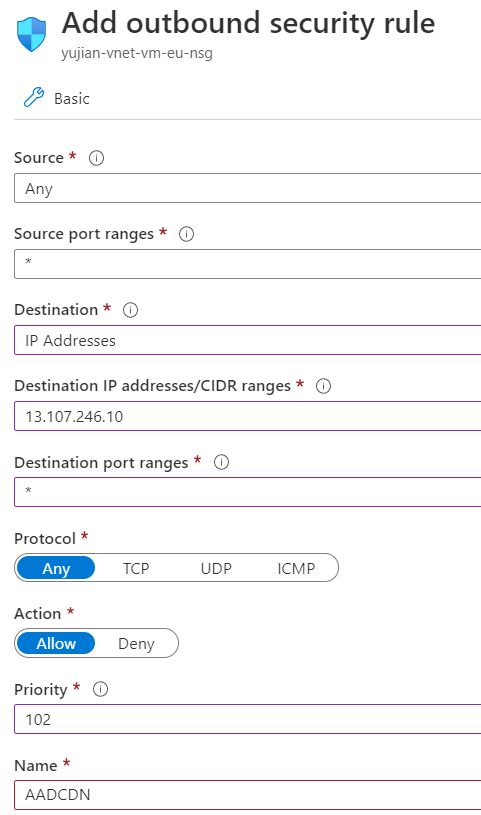
In this case, open a command prompt on the VM, ping aadcdn.msauth.net, get its IP, and then add an outbound port rule for the IP in the VM's network security rules. Set the Destination to IP Addresses and set Destination IP addresses to the aadcdn IP. Because of Azure Load Balancer and Azure Traffic Manager, the Microsoft Entra Content Delivery Network IP might be dynamic. After you get its IP, it's better to add it into the VM's host file to force the browser to visit that IP to get the Microsoft Entra Content Delivery Network.
After the new rule is created, go back to the VM and try to sign in by using your Microsoft Entra credentials again. If sign-in succeeds, then the Microsoft Purview portal is ready to use. But in some cases, Microsoft Entra ID redirects to other domains to sign in based on a customer's account type. For example, for a live.com account, Microsoft Entra ID redirects to live.com to sign in, and then those requests are blocked again. For Microsoft employee accounts, Microsoft Entra ID accesses msft.sts.microsoft.com for sign-in information.
Check the networking requests on the browser Networking tab to see which domain's requests are getting blocked, redo the previous step to get its IP, and add outbound port rules in the network security group to allow requests for that IP. If possible, add the URL and IP to the VM's host file to fix the DNS resolution. If you know the exact sign-in domain's IP ranges, you can also directly add them into networking rules.
Now your Microsoft Entra sign-in should be successful. The Microsoft Purview portal will load successfully, but listing all the Microsoft Purview accounts won't work because it can only access a specific Microsoft Purview account. Enter
web.purview.azure.cn/resource/{PurviewAccountName}to directly visit the Microsoft Purview account that you successfully set up a private endpoint for.