Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Important
This article covers Microsoft Purview data governance permissions in the new Microsoft Purview portal using Microsoft Purview Unified Catalog.
- For data governance permissions in the classic Microsoft Purview portal, see permissions in the classic Microsoft Purview governance portal.
Microsoft Purview data governance has two solutions in the Microsoft Purview Portal: Data Map and Unified Catalog. These solutions use tenant/organizational-level permissions, existing data access permissions, and domain/collection permissions to provide users access to governance tools and data assets.
The kind of permissions available to use depends on your Microsoft Purview account type.
Check your account type
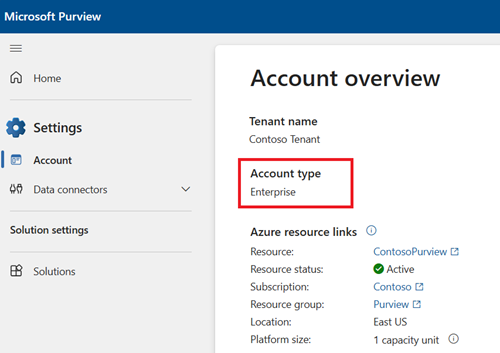
Check whether your organization has the free or enterprise type of account. To check your account type, go to the Microsoft Purview portal, select the Settings card. Under Account, view your Account type.
Important
For users newly created in Microsoft Entra ID, it might take some time for permissions to propagate even after correct permissions are applied.
Tenant level role groups
Assigned at the organizational level, tenant level role groups provide general and administrative permissions for both Microsoft Purview Data Map and Unified Catalog. If you're managing your Microsoft Purview account or your organization's data governance strategy, you probably need to belong to one or more of these role groups:
- Purview Administrators
- Data Source Administrators
- Data Governance
Data Map permissions
Data Map uses a set of predefined roles to control who can access what within the account. Domains and collections are tools used by Data Map to group assets, sources, and other artifacts into a hierarchy for discoverability, and to manage access control within Data Map.
Find a description of each role and learn how to add roles and restrict access through collections.
For more detailed information about the roles available in collections, see who should be assigned what roles or the collections example.
Tip
If you're a data steward or data product owner for Unified Catalog, it's a good idea to have Data Map permissions as well.
Data asset lifecycle example
To understand how permissions work between Data Map and Unified Catalog, review the table below on the full lifecycle of an Azure SQL table in the environment:
| Step | Role | Permission level |
|---|---|---|
| 1. The Azure SQL Database is registered in Data Map | Data Source Administrator | Data Map |
| 2. The Azure SQL Database is scanned in Data Map | Data Curator or Data Source Administrator | Data Map |
| 3. The Azure SQL table is curated and certified | Data Curator | Data Map |
| 4. A governance domain is created in the Microsoft Purview Account | Governance Domain Creator | Catalog |
| 5. A data product is created in the governance domain | Governance Domain Owner and/or Data Product Owner | Governance domain |
| 6. The Azure SQL table is added as an asset to the data product | Data Product Owner and/or Steward | Governance domain |
| 7. An access policy is added to the data product | Data Product Owner and/or Steward | Governance domain |
| 8. A user searches Unified Catalog, looking for data assets that match their needs | Asset permissions or data reader permission | Asset permissions or Data Map permissions |
| 9. A user searches data products, looking for a product that matches their needs | Global Catalog Reader | Catalog |
| 10. A user requests access to the resources in the data product | Global Catalog Reader | Catalog |
| 11. A user views Data Health Insights to track the health of their Data Catalog | Data Health Reader | Catalog |
| 12. A user wants to develop a new report to track data health progress in their catalog | Data Health Owner | Catalog |