Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
This article outlines how to register and Azure SQL Managed Instance, as well as how to authenticate and interact with the Azure SQL Managed Instance in Microsoft Purview. For more information about Microsoft Purview, read the introductory article.
Supported capabilities
Scanning capabilities
| Metadata Extraction | Full Scan | Incremental Scan | Scoped Scan |
|---|---|---|---|
| Yes | Yes | Yes | Yes |
Other capabilities
For classifications, policies, and live view, see the list of supported capabilities.
Prerequisites
An Azure account with an active subscription. Create an account.
An active Microsoft Purview account.
You'll need to be a Data Source Administrator and Data Reader to register a source and manage it in the Microsoft Purview governance portal. See our Microsoft Purview Permissions page for details.
Configure public endpoint in Azure SQL Managed Instance
Note
We now support scanning Azure SQL Managed Instances over the private connection using Microsoft Purview ingestion private endpoints and a self-hosted integration runtime VM. For more information related to prerequisites, see Connect to your Microsoft Purview and scan data sources privately and securely
Register
This section describes how to register an Azure SQL Managed Instance in Microsoft Purview using the Microsoft Purview governance portal.
Authentication for registration
If you need to create new authentication, you need to authorize database access to SQL Database SQL Managed Instance. There are three authentication methods that Microsoft Purview supports today:
System or user assigned managed identity to register
Note
If you're using Private Endpoints to connect to Microsoft Purview, managed identity isn't supported.
You can use either your Microsoft Purview system-assigned managed identity (SAMI), or a user-assigned managed identity (UAMI) to authenticate. Both options allow you to assign authentication directly to Microsoft Purview, like you would for any other user, group, or service principal. The Microsoft Purview system-assigned managed identity is created automatically when the account is created and has the same name as your Microsoft Purview account. A user-assigned managed identity is a resource that can be created independently. To create one, you can follow our user-assigned managed identity guide.
You can find your managed identity Object ID in the Azure portal by following these steps:
For Microsoft Purview account’s system-assigned managed identity:
- Open the Azure portal, and navigate to your Microsoft Purview account.
- Select the Properties tab on the left side menu.
- Select the Managed identity object ID value and copy it.
For user-assigned managed identity (preview):
- Open the Azure portal, and navigate to your Microsoft Purview account.
- Select the Managed identities tab on the left side menu
- Select the user assigned managed identities, select the intended identity to view the details.
- The object (principal) ID is displayed in the overview essential section.
Either managed identity will need permission to get metadata for the database, schemas and tables, and to query the tables for classification.
- Create a Microsoft Entra user in Azure SQL Managed Instance by following the prerequisites and tutorial on Create contained users mapped to Microsoft Entra identities
- Assign
db_datareaderpermission to the identity.
Service Principal to register
There are several steps to allow Microsoft Purview to use service principal to scan your Azure SQL Managed Instance.
Create or use an existing service principal
To use a service principal, you can use an existing one or create a new one. If you're going to use an existing service principal, skip to the next step. If you have to create a new Service Principal, follow these steps:
- Navigate to the Azure portal.
- Select Microsoft Entra ID from the left-hand side menu.
- Select App registrations.
- Select + New application registration.
- Enter a name for the application (the service principal name).
- Select Accounts in this organizational directory only.
- For Redirect URI, select Web and enter any URL you want; it doesn't have to be real or work.
- Then select Register.
Configure Microsoft Entra authentication in the database account
The service principal must have permission to get metadata for the database, schemas, and tables. It must also be able to query the tables to sample for classification.
- Configure and manage Microsoft Entra authentication with Azure SQL
- Create a Microsoft Entra user in Azure SQL Managed Instance by following the prerequisites and tutorial on Create contained users mapped to Microsoft Entra identities
- Assign
db_datareaderpermission to the identity.
Add service principal to key vault and Microsoft Purview's credential
It's required to get the service principal's application ID and secret:
- Navigate to your Service Principal in the Azure portal
- Copy the values the Application (client) ID from Overview and Client secret from Certificates & secrets.
- Navigate to your key vault
- Select Settings > Secrets
- Select + Generate/Import and enter the Name of your choice and Value as the Client secret from your Service Principal
- Select Create to complete
- If your key vault isn't connected to Microsoft Purview yet, you'll need to create a new key vault connection
- Finally, create a new credential using the Service Principal to set up your scan.
SQL authentication to register
Note
Only the server-level principal login (created by the provisioning process) or members of the loginmanager database role in the master database can create new logins. It takes about 15 minutes after granting permission, the Microsoft Purview account should have the appropriate permissions to be able to scan the resource(s).
You can follow the instructions in CREATE LOGIN to create a login for Azure SQL Managed Instance if you don't have this login available. You'll need username and password for the next steps.
- Navigate to your key vault in the Azure portal
- Select Settings > Secrets
- Select + Generate/Import and enter the Name and Value as the password from your Azure SQL Managed Instance
- Select Create to complete
- If your key vault isn't connected to Microsoft Purview yet, you'll need to create a new key vault connection
- Finally, create a new credential using the username and password to set up your scan.
Steps to register
Open the Microsoft Purview governance portal by:
- Browsing directly to https://web.purview.azure.cn and selecting your Microsoft Purview account.
- Opening the Azure portal, searching for and selecting the Microsoft Purview account. Select the the Microsoft Purview governance portal button.
Navigate to the Data Map.
Select Register
Select Azure SQL Managed Instance and then Continue.
Select From Azure subscription, select the appropriate subscription from the Azure subscription drop-down box and the appropriate server from the Server name drop-down box.
Provide the public endpoint fully qualified domain name and port number. Then select Register to register the data source.
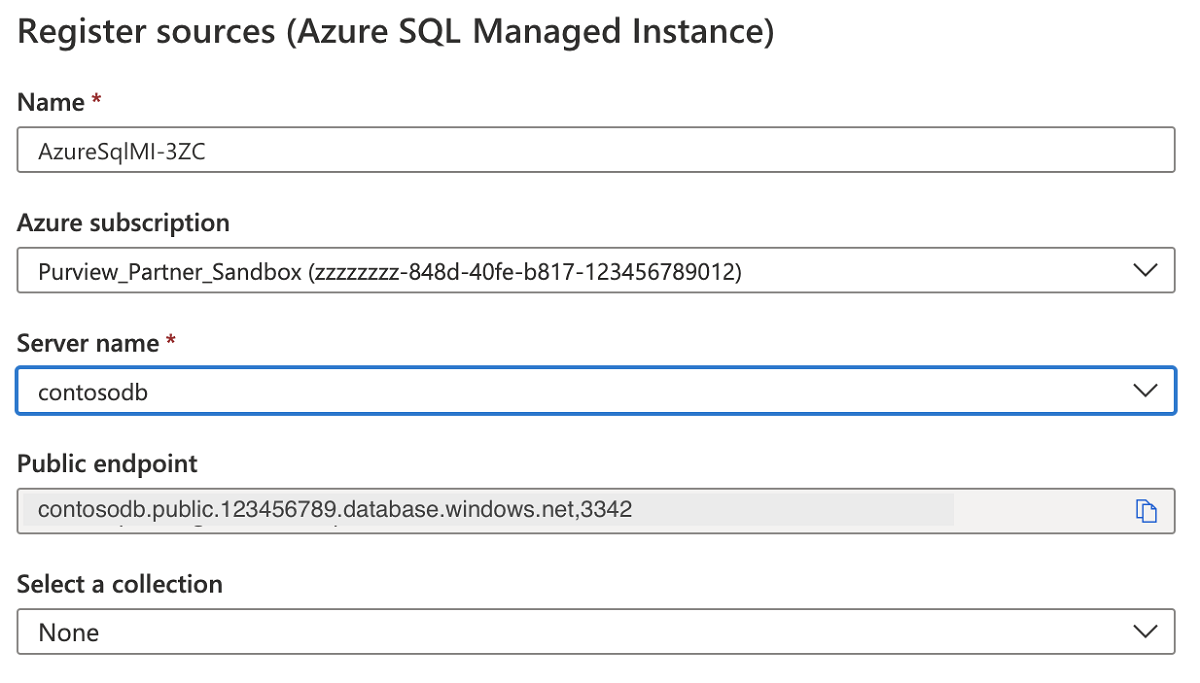
For Example:
foobar.public.123.database.chinacloudapi.cn,3342
Scan
Follow the steps below to scan an Azure SQL Managed Instance to automatically identify assets and classify your data. For more information about scanning in general, see our introduction to scans and ingestion.
Create and run scan
To create and run a new scan, complete the following steps:
Select the Data Map tab on the left pane in the Microsoft Purview governance portal.
Select the Azure SQL Managed Instance source that you registered.
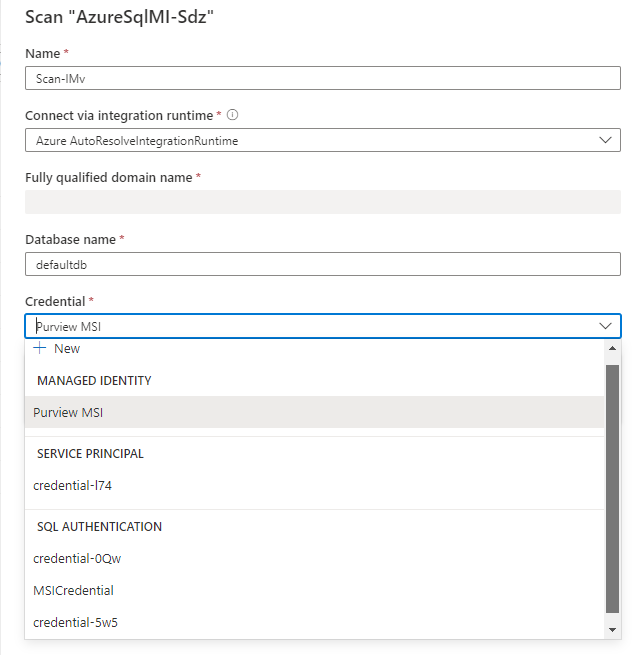
Select New scan
Choose either the Azure integration runtime if your source is publicly accessible, a self-hosted integration runtime if your source is in a private virtual network. For more information about which integration runtime to use, see the choose the right integration runtime configuration article.
Select the credential to connect to your data source.
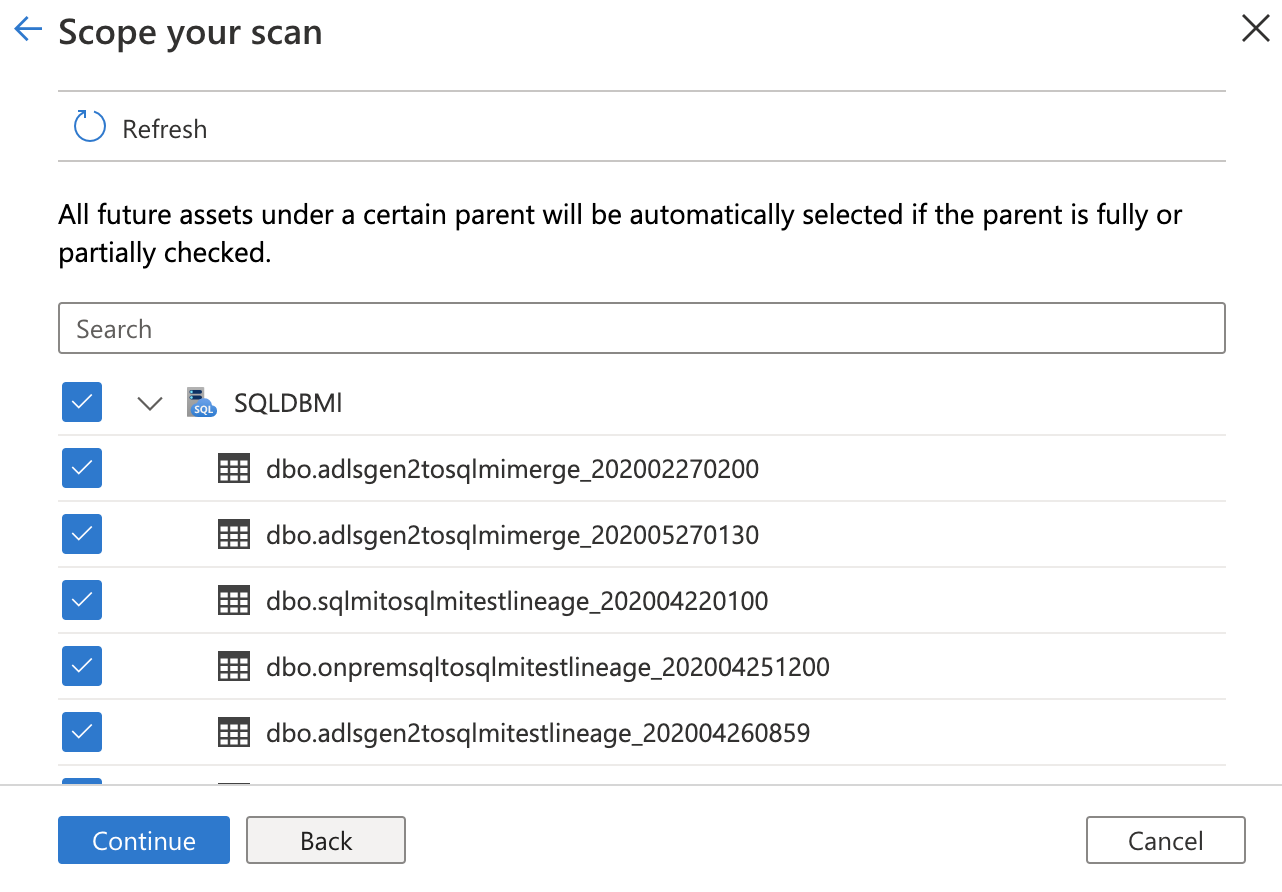
You can scope your scan to specific tables by choosing the appropriate items in the list.
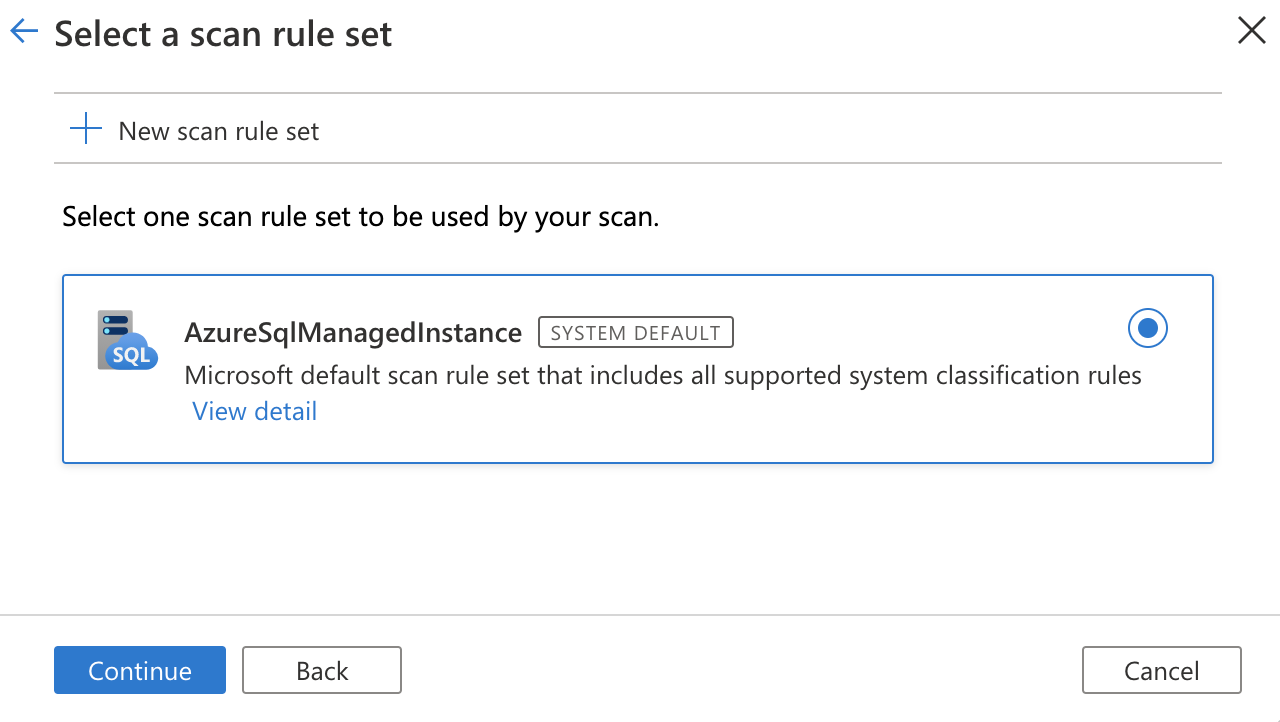
Then select a scan rule set. You can choose between the system default, existing custom rule sets, or create a new rule set inline.
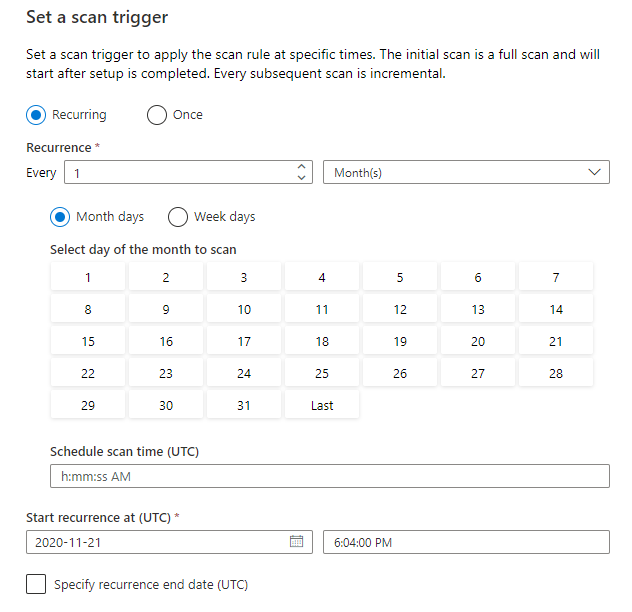
Choose your scan trigger. You can set up a schedule or run the scan once.
Review your scan and select Save and run.
If you're having trouble connecting to your data source, or running your scan, you scan see our troubleshooting guide for scans and connections.
View your scans and scan runs
To view existing scans:
- Go to the Microsoft Purview portal. On the left pane, select Data map.
- Select the data source. You can view a list of existing scans on that data source under Recent scans, or you can view all scans on the Scans tab.
- Select the scan that has results you want to view. The pane shows you all the previous scan runs, along with the status and metrics for each scan run.
- Select the run ID to check the scan run details.
Manage your scans
To edit, cancel, or delete a scan:
Go to the Microsoft Purview portal. On the left pane, select Data Map.
Select the data source. You can view a list of existing scans on that data source under Recent scans, or you can view all scans on the Scans tab.
Select the scan that you want to manage. You can then:
- Edit the scan by selecting Edit scan.
- Cancel an in-progress scan by selecting Cancel scan run.
- Delete your scan by selecting Delete scan.
Note
- Deleting your scan does not delete catalog assets created from previous scans.
Next steps
Now that you've registered your source, follow the below guides to learn more about Microsoft Purview and your data.