Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Important
Attention: All Microsoft Sentinel features will be officially retired in Azure in China regions on August 18, 2026 per the announcement posted by 21Vianet.
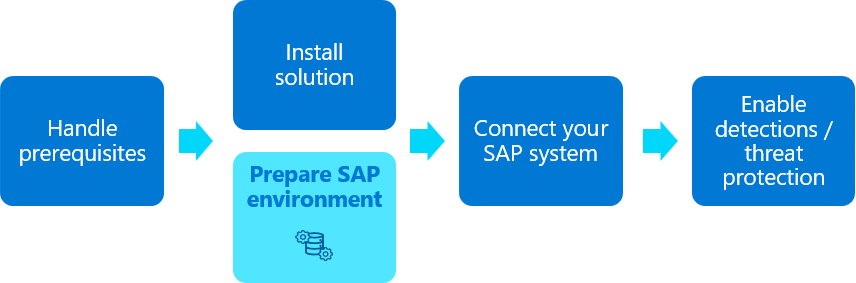
This article describes how to prepare your SAP environment for connecting to the SAP data connector. Preparation includes configuring required SAP authorizations and, optionally, deploying extra SAP change requests (CRs).
This article is part of the second step in deploying the Microsoft Sentinel solution for SAP applications.
The procedures in this article are typically performed by your SAP BASIS team.
Prerequisites
- Before you start, make sure to review the prerequisites for deploying the Microsoft Sentinel solution for SAP applications.
Configure the Microsoft Sentinel role
To allow the SAP data connector to connect to your SAP system, you must create an SAP system role specifically for this purpose.
We recommend creating this role by deploying the NPLK900271 SAP change request (CR): K900271.NPL | R900271.NPL
Deploy the CRs on your SAP system as needed just as you'd deploy other CRs. We strongly recommend that deploying SAP CRs is done by an experienced SAP system administrator. For more information, see the SAP documentation.
Alternately, load the role authorizations from the MSFTSEN_SENTINEL_CONNECTOR file, which includes all the basic permissions for the data connector to operate.
Experienced SAP administrators might choose to create the role manually and assign it the appropriate permissions. In such cases, create a role manually with the relevant authorizations required for the logs you want to ingest. For more information, see Required ABAP authorizations. Examples in our documentation use the /MSFTSEN/SENTINEL_RESPONDER name.
When configuring the role, we recommend that you:
- Generate an active role profile for Microsoft Sentinel by running the PFCG transaction.
- Use
/MSFTSEN/SENTINEL_RESPONDERas the role name.
For more information, see the SAP documentation on creating roles.
Create a user
The Microsoft Sentinel solution for SAP applications requires a user account to connect to your SAP system. When creating your user:
- Make sure to create a system user.
- Assign the /MSFTSEN/SENTINEL_RESPONDER role to the user, which you'd created in the previous step.
For more information, see the SAP documentation.
Configure SAP auditing
Some installations of SAP systems might not have audit logging enabled by default. For best results in evaluating the performance and efficacy of the Microsoft Sentinel solution for SAP applications, enable auditing of your SAP system and configure the audit parameters.
We recommend that you configure auditing for all messages from the audit log, instead of only specific logs. Ingestion cost differences are generally minimal and the data is useful for Microsoft Sentinel detections and in post-compromise investigations and hunting.
Tip
If you want to ingest SAP HANA DB logs, make sure to also enable auditing for SAP HANA DB. For more information, see Collect SAP HANA audit logs in Microsoft Sentinel
Tip
For SAP systems managed by SAP RISE/ECS, Security Audit Log enablement is part of the shared responsibility agreement. Verify with your SAP contact if auditing is already active by default or if any additional steps need to be taken.
For more information, see SAP's article.
Configure your system to use SNC for secure connections
By default, the SAP data connector agent connects to an SAP server using a remote function call (RFC) connection and a username and password for authentication.
However, you might need to make the connection on an encrypted channel or use client certificates for authentication. In these cases, use Smart Network Communications (SNC) from SAP to secure your data connections, as described in this section.
In a production environment, we strongly recommend that your consult with SAP administrators to create a deployment plan for configuring SNC. For more information, see the SAP documentation.
When configuring SNC:
- If the client certificate was issued by an enterprise certification authority, transfer the issuing CA and root CA certificates to the system where you plan to create the data connector agent.
- Make sure to also enter the relevant values and use the relevant procedures when configuring the SAP data connector agent container.
Configure support for extra data retrieval (recommended)
While this step is optional, we recommend that you enable the SAP data connector to retrieve the following content information from your SAP system:
- DB Table and Spool Output logs
- Client IP address information from the security audit logs
Deploy the relevant CRs from the Microsoft Sentinel GitHub repository, according to your SAP version:
SAP BASIS versions Recommended CR 750 and higher NPLK900202: K900202.NPL, R900202.NPL
When deploying this CR any of the following SAP versions, also deploy 2641084 - Standardized read access to data of Security Audit Log:
- 750 SP04 to SP12
- 751 SP00 to SP06
- 752 SP00 to SP02740 NPLK900201: K900201.NPL, R900201.NPL Deploy the CRs on your SAP system as needed just as you'd deploy other CRs. We strongly recommend that deploying SAP CRs is done by an experienced SAP system administrator. For more information, see the SAP documentation.
For more information, see the SAP Community and the SAP documentation.
To support SAP BASIS versions 7.31-7.5 SP12 in sending client IP address information to Microsoft Sentinel, activate logging for SAP table USR41. For more information, see the SAP documentation.
Verify that the PAHI table is updated at regular intervals
The SAP PAHI table includes data on the history of the SAP system, the database, and SAP parameters. In some cases, the Microsoft Sentinel solution for SAP applications can't monitor the SAP PAHI table at regular intervals, due to missing or faulty configuration. It's important to update the PAHI table and to monitor it frequently, so that the Microsoft Sentinel solution for SAP applications can alert on suspicious actions that might happen at any time throughout the day. For more information, see:
If the PAHI table is updated regularly, the SAP_COLLECTOR_FOR_PERFMONITOR job is scheduled and runs hourly. If the SAP_COLLECTOR_FOR_PERFMONITOR job doesn't exist, make sure to configure it as needed.
For more information, see Database Collector in Background Processing and Configuring the Data Collector.