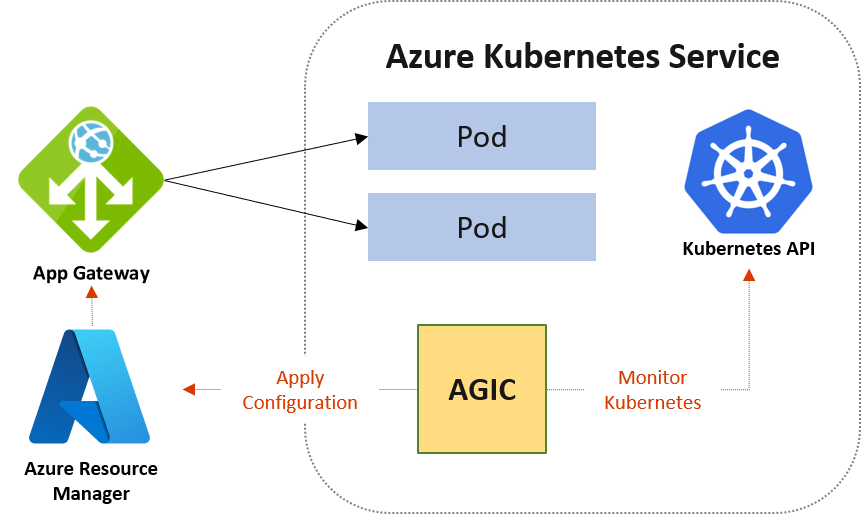
应用程序网关入口控制器(AGIC)是一个 Kubernetes 应用程序,它使 Azure Kubernetes Service (AKS) 群集能够使用本机 Azure Application Gateway L7 负载均衡器向 Internet 公开工作负荷。 AGIC 监视托管的 Kubernetes 群集,并持续更新应用程序网关,以便所选服务向 Internet 公开。
入口控制器在 AKS 群集上的一个独立的 Pod 中运行。 AGIC 监视 Kubernetes 资源子集的更改。 AKS 群集的状态将转换为特定于应用程序网关的配置,并应用于 Azure Resource Manager (ARM)。
在本文中,你将了解 AGIC 的优势、部署选项(Helm 和 AKS 加载项)和支持的容器网络配置。
应用程序网关入口控制器的好处
AGIC 消除对 AKS 群集前的另一个负载均衡器或公共 IP 地址的需求。 在请求到达 AKS 群集之前,它会避免数据路径中的多个跃点。 应用程序网关直接使用其专用 IP 地址与 Pod 通信,不需要 NodePort 或 KubeProxy 服务。 此功能也会改进部署性能。
入口控制器仅由Standard_v2和WAF_v2 SKU支持,这些SKU还启用自动缩放优势。 应用程序网关可以响应流量负载的增减并相应地进行缩放,不消耗 AKS 群集中的任何资源。
在 AGIC 基础上使用应用程序网关还可以提供 TLS 策略和 Web 应用程序防火墙 (WAF) 功能,这有助于保护 AKS 群集。
AGIC 通过 Kubernetes 入口资源以及服务和部署/Pod 进行配置。 通过使用本机Azure Application Gateway L7 负载均衡器,AGIC 提供以下功能:
- URL 路由
- 基于 Cookie 的相关性
- TLS 终止
- 端到端 TLS
- 支持公共、专用和混合网站
- 集成式 Web 应用程序防火墙
警告
默认情况下,AGIC 假定其链接到的应用程序网关的完全所有权。 AGIC 将覆盖所有未在 Kubernetes Ingress 资源中定义的现有应用程序网关配置。 启用 AGIC 时,将删除或替换之前在应用程序网关上配置的任何侦听器、后端池、规则或其他设置。 在现有应用程序网关上启用 AGIC 之前,请通过从 Azure 门户导出模板来备份应用程序网关配置。 有关详细信息,请参阅 备份应用程序网关部署。
如果需要 AGIC 与现有应用程序网关配置共存,请参阅 设置共享应用程序网关部署 (仅 Helm)。
Helm 部署与 AKS 加载项之间的差异
可以使用 Helm 或 AKS 作为加载项为 AKS 群集部署 AGIC。 将 AGIC 部署为 AKS 加载项的主要好处是,它比通过 Helm 部署要简单得多。 若要进行新的设置,在 Azure CLI 中通过一行内容即可部署新应用程序网关和将 AGIC 作为加载项启用的新 AKS 群集。 该加载项也是一项完全托管的服务,这提供了一些额外的优势,例如自动更新和更多的支持。 Microsoft 完全支持部署 AGIC(Helm 和 AKS 加载项)的两种方式。 此外,该附加产品作为出色的附加产品,可改善与 AKS 的集成。
尽管在 AKS 群集中将 AGIC 加载项部署为 Pod,但 Helm 部署版本与 AGIC 加载项版本之间存在一些差异。 以下列表突出显示了差异:
- 无法修改 AKS 加载项中的 Helm 部署值:
-
verbosityLevel默认设置为 5 -
usePrivateIp默认情况下设置为 false;使用 use-private-ip 批注覆盖此设置 - 加载项不支持
shared - 该加载项不支持
reconcilePeriodSeconds -
armAuth.type在加载项上不受支持
-
- 通过 Helm 部署的 AGIC 支持 ProhibitedTargets,这意味着 AGIC 可以为 AKS 群集专门配置应用程序网关,而不会影响其他现有后端。 AGIC 加载项当前不具备该功能。
- 由于 AGIC 加载项是托管服务,因此会自动接收最新版本的 AGIC 加载项的更新。 相比之下,通过 Helm 部署 AGIC 时,必须手动更新 AGIC。
注意
每个 AKS 群集只能部署一个 AGIC 加载项,每个 AGIC 加载项当前只能面向一个应用程序网关。 对于每个群集需要多个 AGIC 的部署或需要多个面向某个应用程序网关的 AGIC 的部署,请使用通过 Helm 部署的 AGIC。
Helm 和 AGIC 加载项都不支持 ExternalName 服务。
容器网络和 AGIC
应用程序网关入口控制器支持以下 AKS 网络产品/服务:
- Kubenet
- CNI
- CNI 覆盖网络
Azure CNI 和 Azure CNI 覆盖是应用程序网关入口控制器的两个推荐选项。 选择网络模型时,请考虑每个 CNI 插件的用例及其使用的网络模型类型:
| CNI 插件 | 网络模型 | 用例要点 |
|---|---|---|
| Azure CNI 虚拟网络 | 覆盖 | - 最适合虚拟网络 IP 保护 - API 服务器支持的最大节点数 + 每个节点 250 个 Pod - 更简单的配置 - 无法直接从外部访问 Pod IP |
| Azure CNI Pod 子网 | 平坦 | - 可以从外部直接访问 Pod - 用于提升虚拟网络 IP 地址使用效率 或 支持大型群集规模的模式 |
| Azure CNI 节点子网 | 平坦 | - 可直接从外部访问 Pod - 更简单的配置 - 扩展性受限 - 虚拟网络 IP 的使用效率低下 |
将用于容器的应用程序网关预配到启用了 CNI 覆盖或 CNI 的群集中时,适用于容器的应用程序网关会自动检测预期的网络配置。 无需更改网关或 Ingress API 配置来指定 CNI Overlay 或 CNI。
使用 Azure CNI 覆盖时,请考虑以下限制:
- AGIC 控制器:必须运行版本 v1.9.1 或更高版本才能利用 CNI 覆盖。
- 子网大小:应用程序网关子网的前缀最大为 /24;每个子网仅支持一个部署。
- 子网委派:应用程序网关子网必须具有Microsoft.Network/applicationGateways 的子网委派。
- 区域虚拟网络对等互连:不能在同一区域的某个虚拟网络中部署应用程序网关,也不能在同一区域的某个虚拟网络中部署 AKS 群集节点。
- 全局虚拟网络对等互连:您无法在一个地区的虚拟网络中部署应用网关,并且不能在不同地区的虚拟网络中部署AKS集群节点。
- 由世纪互联运营的中国版 Azure 不支持 Azure CNI Overlay 与应用程序网关入口控制器的组合使用。
注意
应用网关入口控制器会自动检测 AKS 群集从 Kubenet 或 CNI 升级到 CNI Overlay。 在维护时段内计划升级,因为可能发生流量中断。 群集升级后,控制器可能需要几分钟才能检测和配置对 CNI 覆盖的支持。
警告
在升级之前,请确保应用程序网关子网是 /24 或更小的子网。 若从 CNI 升级到具有较大子网(例如 /23)的 CNI 覆盖,会导致服务中断,并且需要使用受支持的子网大小重新创建应用程序网关子网。
后续步骤
- AKS 加载项绿地部署:有关如何在白板基础结构上安装 AGIC 加载项、AKS 和应用程序网关的说明。
- AKS 加载项棕地部署:使用现有的应用程序网关在 AKS 群集上安装 AGIC 加载项。
- Helm“绿色地带”部署:在白板基础结构上通过 Helm、新 AKS 群集和新应用程序网关安装 AGIC。
- Helm“棕色地带”部署:在现有的 AKS 群集和应用程序网关上通过 Helm 部署 AGIC。