本文介绍:
- 可以为此服务收集的监视数据的类型。
- 如何分析这些数据。
如果具有依赖于 Azure 资源的关键应用程序和业务流程,则需要监视并获取系统的警报。 Azure Monitor 服务会从系统的每个组件收集并聚合指标和日志。 Azure Monitor 提供可用性、性能和复原能力视图,并在出现问题时向你发送通知。 可以使用 Azure 门户、PowerShell、Azure CLI、REST API 或客户端库来设置和查看监视数据。
- 有关 Azure Monitor 的详细信息,请参阅 Azure Monitor 概述。
- 有关监视 Azure 资源的常规方法的详细信息,请参阅使用 Azure Monitor 监视 Azure 资源。
本文介绍了 Azure 容器注册表生成的监视数据,以及如何使用 Azure Monitor 的功能在这些数据的基础上进行分析和发出警报。
Monitor 概述
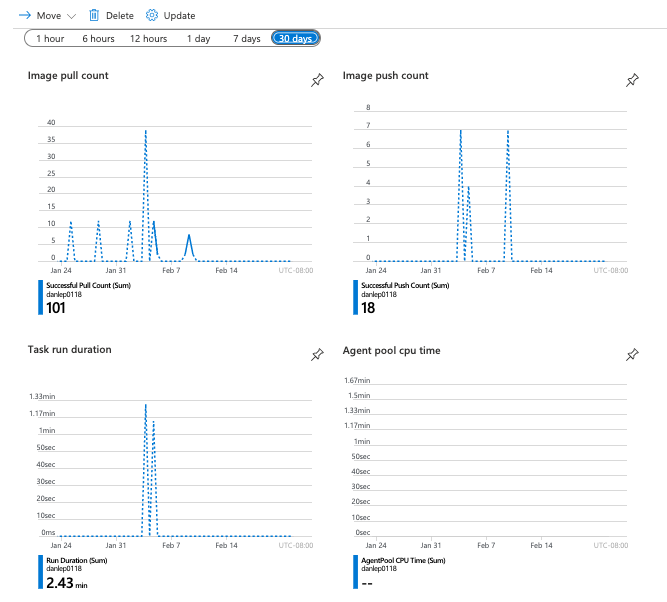
每个注册表的 Azure 门户中的“概述”页面上均有一个显示最近资源使用情况和活动(例如推送和拉取操作)的简要视图。 这些高级别信息非常有用,但只显示少量数据。
资源类型
Azure 使用资源类型和 ID 的概念来标识订阅中的所有内容。 同样的,Azure Monitor 根据资源类型(也称为“命名空间”)将核心监视数据组织为指标和日志。 不同的指标和日志可用于不同的资源类型。 服务可能与多种资源类型关联。
资源类型也是 Azure 中运行的每个资源的资源 ID 的一部分。 例如,虚拟机的一种资源类型是 Microsoft.Compute/virtualMachines。 有关服务及其关联资源类型的列表,请参阅资源提供程序。
有关容器注册表的资源类型的详细信息,请参阅 Azure 容器注册表监视数据参考。
监视数据
Azure 容器注册表收集与 Azure 资源中的监视数据中所述的其他 Azure 资源相同的监视数据。
有关 Azure 容器注册表创建的指标和日志的详细信息,请参阅 Azure 容器注册表监视数据参考。
收集和路由
平台指标和活动日志会自动收集和存储,但你可以使用诊断设置将其路由到其他位置。
在创建诊断设置并将其路由到一个或多个位置之前,不会收集和存储资源日志。
有关使用 Azure 门户、CLI 或 PowerShell 创建诊断设置的详细过程,请参阅创建诊断设置以收集 Azure 中的平台日志和指标。 创建诊断设置时,请指定要收集的日志类别。 Azure 容器注册表监视数据参考列出了 Azure 容器注册表的类别。
提示
也可以通过导航到门户中的注册表来创建注册表诊断设置。 在菜单中,选择“监视”下的“诊断设置”。
以下部分将讨论可以收集的指标和日志。
数据存储
对于 Azure Monitor:
- 指标数据存储在 Azure Monitor 指标数据库中。
- 日志数据存储在 Azure Monitor 日志存储中。 Log Analytics 是 Azure 门户中可以查询此存储的工具。
- Azure 活动日志是一个单独的存储区,在 Azure 门户中有自己的接口。
- 可选择将指标和活动日志数据路由到 Azure Monitor 日志数据库存储,以便可使用 Log Analytics 查询数据并将其与其他日志数据关联。
有关 Azure Monitor 如何存储数据的详细信息,请参阅 Azure Monitor 数据平台。
Azure Monitor 平台指标
Azure Monitor 为大多数服务提供平台指标。 这些指标是:
- 针对每个命名空间单独定义。
- 存储在 Azure Monitor 时序指标数据库中。
- 是轻型数据,并且能够支持准实时警报。
- 用于跟踪资源随时间推移的性能变化。
集合:Azure Monitor 会自动收集平台指标。 不需要任何配置。
路由:通常还可将平台指标路由到 Azure Monitor 日志/Log Analytics,从而可以使用其他日志数据对其进行查询。 有关详细信息,请参阅指标诊断设置。 有关如何为服务配置诊断设置,请参阅在 Azure Monitor 中创建诊断设置。
有关可以为 Azure Monitor 中的所有资源收集的所有指标的列表,请参阅 Azure Monitor 中支持的指标。
有关容器注册表的可用指标列表,请参阅 Azure 容器注册表监视数据参考。
分析指标
可以从 “Azure Monitor” 菜单中打开“指标”,使用指标资源管理器根据来自其他 Azure 服务的指标为 Azure 容器注册表分析指标。 有关使用此工具的详细信息,请参阅使用 Azure Monitor 指标资源管理器分析指标。
提示
还可以导航到门户中的注册表,进入指标资源管理器。 在菜单中,选择“监视”下的“指标”。
有关为 Azure 容器注册表收集的平台指标的列表,请参阅 Azure 容器注册表监视数据参考指标。
Azure 命令行接口 (CLI)
以下 Azure CLI 命令可用于获取有关指标 Azure 容器注册表的信息。
- az monitor metrics list-definitions - 列出指标定义和维度
- az monitor metrics list - 检索指标值
REST API
可以使用此 Azure Monitor REST API 以编程方式获得有关 Azure 容器注册表指标的信息。
Azure Monitor 资源日志
借助资源日志,可以深入了解 Azure 资源已执行的操作。 日志是自动生成的,但必须将日志路由到 Azure Monitor 日志以保存或查询它们。 日志按类别组织。 给定的命名空间可能具有多个资源日志类别。
收集:在创建诊断设置并将日志路由到一个或多个位置之前,不会收集和存储资源日志。 创建诊断设置时,请指定要收集的日志类别。 可以通过多种方式创建和维护诊断设置,包括 Azure 门户、编程方式以及通过 Azure Policy。
路由:建议的默认设置是将资源日志路由到 Azure Monitor 日志,以便可以使用其他日志数据查询它们。 其他位置(例如 Azure 存储、Azure 事件中心和某些 Azure 监视合作伙伴)也可用。 有关详细信息,请参阅 Azure 资源日志和资源日志目标。
有关收集、存储和路由资源日志的详细信息,请参阅 Azure Monitor 中的诊断设置。
有关 Azure Monitor 中所有可用资源日志类别的列表,请参阅 Azure Monitor 中支持的资源日志。
Azure Monitor 中的所有资源日志都具有相同的标头字段,后跟特定于服务的字段。 Azure Monitor 资源日志架构概述了常见架构。
分析日志
Azure Monitor 日志中的数据以表形式存储,每个表具有自己独有的属性集。
Azure Monitor 中的所有资源日志都具有后跟服务特定字段的相同字段。 Azure Monitor 资源日志架构概述了常见架构。 有关 Azure 容器注册表资源日志的架构,可参阅 Azure 容器注册表数据参考。
活动日志是 Azure 中的一种平台日志,可用于深入了解订阅级别事件。 你可以单独查看它或将它路由到 Azure Monitor 日志,然后便可以在其中使用 Log Analytics 执行复杂得多的查询。
有关为 Azure 容器注册表收集的资源日志类型列表,请参阅 Azure 容器注册表监视数据参考。
如需查看 Azure Monitor 日志使用并可通过 Log Analytics 查询的表列表,请参阅 Azure 容器监视数据参考。
有关可用的资源日志类别、其关联的 Log Analytics 表以及容器注册表的日志架构,请参阅 Azure 容器注册表监视数据参考。
Azure 活动日志
活动日志包含订阅级事件,这些事件跟踪从资源外部看到的每个 Azure 资源的操作;例如,创建新资源或启动虚拟机。
收集:活动日志事件会自动生成并收集在单独的存储中,以便在 Azure 门户中查看。
路由:可将活动日志数据发送到 Azure Monitor 日志,以便可以将它们与其他日志数据一起进行分析。 其他位置(例如 Azure 存储、Azure 事件中心和某些 Azure 监视合作伙伴)也可用。 有关如何路由活动日志的详细信息,请参阅 Azure 活动日志概述。
分析监视数据
有许多工具可用于分析监视数据。
Azure Monitor 工具
Azure Monitor 支持以下基本工具:
指标资源管理器,它是 Azure 门户中的工具,可用于查看和分析 Azure 资源的指标。 有关详细信息,请参阅使用 Azure Monitor 指标资源管理器分析指标。
Log Analytics,它是 Azure 门户中的一种工具,支持使用 Kusto 查询语言 (KQL) 来查询和分析日志数据。 有关详细信息,请参阅 Azure Monitor 日志查询入门。
活动日志,它在 Azure 门户中具有用于执行查看和基本搜索的用户界面。 要进行更深入的分析,必须将数据路由到 Azure Monitor 日志,并在 Log Analytics 中运行更复杂的查询。
支持更复杂可视化效果的工具包括:
- 仪表板,它支持将不同类型的数据合并到 Azure 门户的单个窗格中。
- 工作簿,它们是可在 Azure 门户中创建的可自定义报表。 工作簿可以包括文本、指标和日志查询。
- Power BI,它是一项业务分析服务,可提供跨各种数据源的交互式可视化效果。 可将 Power BI 配置为自动从 Azure Monitor 导入日志数据,以利用这些可视化效果。
Azure Monitor 导出工具
可以使用以下方法将数据从 Azure Monitor 中提取到其他工具中:
指标:使用适用于指标的 REST API 从 Azure Monitor 指标数据库提取指标数据。 API 支持使用筛选表达式优化检索到的数据。 有关详细信息,请参阅 Azure Monitor REST API 参考。
日志:使用 REST API 或关联的客户端库。
要开始使用适用于 Azure Monitor 的 REST API,请参阅 Azure 监视 REST API 演练。
Kusto 查询
可使用 Kusto 查询语言 (KQL) 来分析 Azure Monitor 日志/Log Analytics 存储中的监视数据。
重要
在门户的服务菜单中选择“日志”时,会打开 Log Analytics,并且其查询范围设置为当前服务。 此范围意味着日志查询将仅包含来自该资源类型的数据。 如果希望运行的查询包含来自其他 Azure 服务的数据,请从“Azure Monitor”菜单中选择“日志”。 有关详细信息,请参阅 Azure Monitor Log Analytics 中的日志查询范围和时间范围。
有关任何服务的常见查询的列表,请参阅 Log Analytics 查询界面。
例如,以下查询从 ContainerRegistryRepositoryEvents 表中检索最近 24 小时的数据:
ContainerRegistryRepositoryEvents
| where TimeGenerated > ago(1d)
下图显示了示例输出:
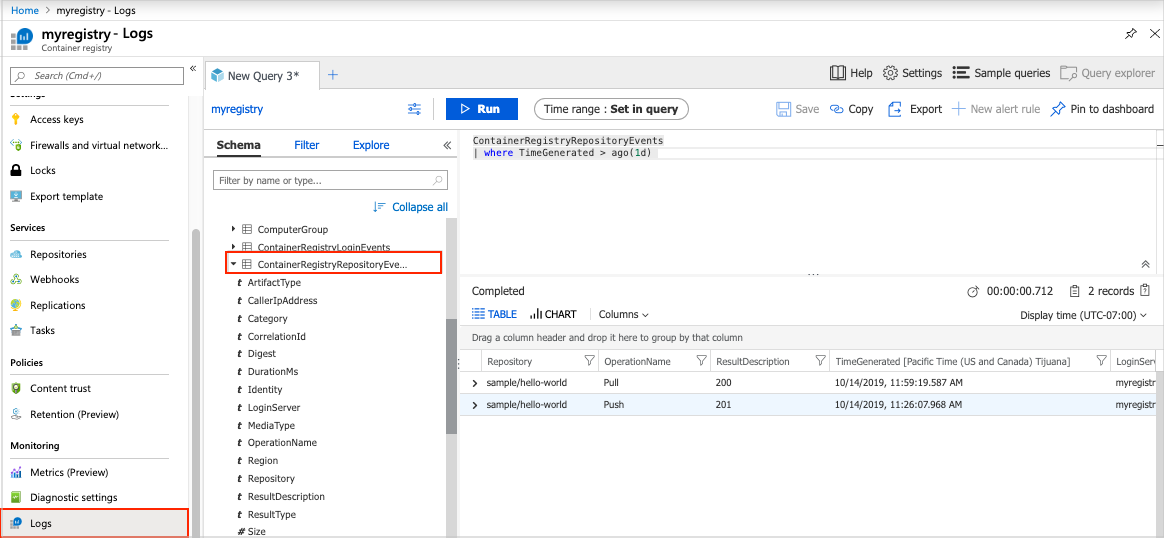
下面是可用来帮助你监视注册表资源的查询。
最近一小时内的错误事件:
union Event, Syslog // Event table stores Windows event records, Syslog stores Linux records
| where TimeGenerated > ago(1h)
| where EventLevelName == "Error" // EventLevelName is used in the Event (Windows) records
or SeverityLevel== "err" // SeverityLevel is used in Syslog (Linux) records
100 个最近的注册表事件:
ContainerRegistryRepositoryEvents
| union ContainerRegistryLoginEvents
| top 100 by TimeGenerated
| project TimeGenerated, LoginServer, OperationName, Identity, Repository, DurationMs, Region , ResultType
删除了存储库的用户或对象的标识:
ContainerRegistryRepositoryEvents
| where OperationName contains "Delete"
| project LoginServer, OperationName, Repository, Identity, CallerIpAddress
删除了标记的用户或对象的标识:
ContainerRegistryRepositoryEvents
| where OperationName contains "Untag"
| project LoginServer, OperationName, Repository, Tag, Identity, CallerIpAddress
存储库级操作失败:
ContainerRegistryRepositoryEvents
| where ResultDescription contains "40"
| project TimeGenerated, OperationName, Repository, Tag, ResultDescription
注册表身份验证失败:
ContainerRegistryLoginEvents
| where ResultDescription != "200"
| project TimeGenerated, Identity, CallerIpAddress, ResultDescription
警报
在监视数据中发现特定情况时,Azure Monitor 警报会主动向你发出通知。 有了警报,你就可以在客户注意到你的系统中的问题之前找出和解决问题。 有关详细信息,请参阅 Azure Monitor 警报。
Azure 资源的常见警报具有许多来源。 有关 Azure 资源常见警报的示例,请参阅示例日志警报查询。 Azure Monitor 基线警报 (AMBA) 站点提供了 Azure 登陆区域 (ALZ) 方案的关键警报指标、仪表板和指南。
通用警报模式对 Azure Monitor 警报通知的使用体验进行了标准化。 有关详细信息,请参阅常见警报架构。
警报类型
可以针对 Azure Monitor 数据平台中的任何指标或日志数据源发出警报。 警报具有许多不同类型,具体取决于要监视的服务以及要收集的监视数据。 不同类型的警报各有优缺点。 有关详细信息,请参阅选择正确的监视警报类型。
以下列表介绍了可以创建的 Azure Monitor 警报类型:
- 指标警报会定期评估资源指标。 指标可以是平台指标、自定义指标、Azure Monitor 中的日志转换为的指标或 Application Insights 指标。 指标警报还可以应用多个条件和动态阈值。
- 日志警报支持用户使用 Log Analytics 查询按照预定义的频率评估资源日志。
- 当发生匹配所定义条件的新活动日志事件时,会触发活动日志警报。 资源运行状况警报和服务运行状况警报是报告服务和资源运行状况的活动日志警报。
还可以为某些 Azure 服务创建以下类型的警报:
- Application Insights 资源上的智能检测警报会就 Web 应用程序中的潜在性能问题和故障异常自动向你发出警报。 可以在 Application Insights 资源上迁移智能检测,以便为不同的智能检测模块创建警报规则。
- Prometheus 警报:针对 Prometheus 指标的警报,这些指标存储在适用于 Prometheus 的 Azure Monitor 托管服务中。 该警报规则基于 PromQL,它是一种开源查询语言。 你的服务可能不支持此类型警报。 目前,Prometheus 用于具有来宾操作系统的有限服务集,例如 Azure 虚拟机和 Azure 容器实例。
- 对于某些 Azure 资源(包括虚拟机、Azure Kubernetes 服务 [AKS] 资源和 Log Analytics 工作区),提供了现成可用的建议警报规则。
监视多个资源
通过将相同的指标警报规则应用于同一 Azure 区域中的多个相同类型资源,可以进行大规模的监视。 将为每个受监视的资源发送单独通知。 有关受支持的 Azure 服务和云,请参阅使用一项警报规则监视多个资源。
Azure 容器注册表警报规则
下表列出了容器注册表的一些建议警报规则。 这些警报只是示例。 可以为 Azure 容器注册表监视数据参考中列出的任何指标、日志条目或活动日志条目设置警报。
| 警报类型 | 条件 | 说明 |
|---|---|---|
| 指标 | 信号:已使用存储 运算符:大于 聚合类型:Average 阈值:5 GB |
如果使用的注册表存储超过指定值,则会发出警报。 |
示例:当使用的注册表存储超过特定值时,会发送电子邮件警报
在 Azure 门户中导航到注册表。
在“监视”下选择“指标”。
在指标资源管理器的“指标”中,选择“使用的存储”。
选择“新建预警规则”。
在“范围”中,确认要创建警报规则的注册表资源。
在“条件”中,选择“添加条件”。
- 在“信号名”中,选择“使用的存储”。
- 在“图表周期”中,选择“过去 24 小时”。
- 在“警报逻辑”的“阈值”中,选择一个值,如“5”。 在“单位”中,选择一个值,如“GB”。
- 接受其余设置的默认值,然后选择“完成”。
在“操作”中,选择“添加操作组”“+ 创建操作组”。
输入操作组的详细信息。
在“通知”选项卡上,选择“电子邮件/短信”并输入接收者(例如 )。 选择“查看 + 创建”。
输入警报规则的名称和说明,然后选择严重级别。
选择“创建警报规则”。
顾问建议
如果在资源操作期间出现严重情况或即将发生变化,则门户中的“概述”页面上会显示一个警报。
可以在“监视”下的“顾问建议”中找到警报的详细信息和建议补丁。 在正常操作期间,不会显示任何顾问建议。
有关 Azure 顾问的详细信息,请参阅 Azure 顾问概述。
相关内容
- 有关为容器注册表创建的指标、日志和其他重要值的参考,请参阅 Azure 容器注册表监视数据参考。
- 有关监视 Azure 资源的一般详细信息,请参阅使用 Azure Monitor 监视 Azure 资源。