IoT Hub使用 X.509 证书对设备进行身份验证。 使用 X.509 身份验证可以在建立传输层安全性 (TLS) 标准连接的过程中,对 IoT 设备进行身份验证。
本文介绍如何使用第三方托管的 X.509 CA 证书对连接到IoT Hub的设备进行身份验证。
身份验证和授权
身份验证是证明你自己的身份的过程。 身份验证用于验证用户或设备的身份以连接到 IoT Hub。 它有时缩写为 AuthN。
Authorization是确认IoT Hub上经过身份验证的用户或设备的权限的过程。 它指定允许访问的资源和命令,以及可使用这些资源和命令执行的操作。 授权有时缩写为 AuthZ。
X.509 证书仅用于IoT Hub中的身份验证,而不是授权。 与 Microsoft Entra ID 和 共享访问签名不同,无法使用 X.509 证书自定义权限。
Microsoft与第三方 PKI
公钥基础结构(PKI)使用数字证书对设备和服务之间的数据进行身份验证和加密。 PKI 证书用于保障 VPN、Wi-Fi、电子邮件、Web 以及设备标识等场景的安全。 管理 PKI 证书具有挑战性、成本高昂和复杂,尤其是对于具有许多设备和用户的组织而言。
IoT Hub支持两种类型的 PKI 提供程序进行 X.509 证书身份验证:
| PKI 服务提供商 | 需要集成 | 需要 Azure 设备注册表(ADR) | 需要设备预配服务 (DPS) |
|---|---|---|---|
| Azure托管的 PKI | 否。 直接在Azure设备注册表(ADR)中配置证书颁发机构。 | 是的 | 是的 |
| 第三方 PKI (DigiCert、GlobalSign 等) | 是的。 需要手动集成。 | 否 | 否 |
证书身份验证类型
X.509 证书颁发机构 (CA) 证书是一种数字证书,可对其他证书进行签名。 如果数字证书符合 IETF RFC 5280 标准规定的证书格式标准,则它被视为 X.509 证书。
X.509 CA 功能通过证书颁发机构(CA)实现设备对 IoT Hub 的身份验证。 它极大地简化了初始设备登记过程,以及设备制造期间的供应链后勤。
可以通过将证书指纹或证书颁发机构(CA)上传到IoT Hub,使用任何 X.509 证书通过IoT Hub对设备进行身份验证。
X.509 CA 签名 - 对于生产方案,建议使用此选项,它是本文的重点。
如果设备具有 CA 签名的 X.509 证书,则在注册设备之前,将签名链中的根或中间 CA 证书上传到IoT Hub。 设备具有 X.509 证书并且在其证书信任链中具有已验证的 X.509 CA。 设备连接后,会显示其完整的证书链,IoT 中心知道 X.509 CA,因此可以验证该设备。 多个设备可以针对相同的已验证 X.509 CA 进行身份验证。
X.509 自签名
如果设备具有自签名 X.509 证书,则需要向 IoT Hub 提供一个证书版本以进行身份验证。 注册设备时,请上传证书“指纹”,这是设备 X.509 证书的哈希。 设备连接后,它会显示其证书,IoT 中心可以根据它知道的哈希来验证设备。
强制执行 X.509 身份验证
为了进一步提高安全性,可以将 IoT 中心配置为不允许对设备和模块进行 SAS 身份验证,而将 x.509 保留为唯一接受的身份验证选项。 目前,此功能在Azure门户中不可用。 若要配置,请将 disableDeviceSAS 和 disableModuleSAS 设置为 IoT Hub 资源属性上的 true:
az resource update -n <iothubName> -g <resourceGroupName> --resource-type Microsoft.Devices/IotHubs --set properties.disableDeviceSAS=true properties.disableModuleSAS=true
X.509 CA 证书身份验证的优势
IoT Hub需要连接的每个设备的唯一标识。 对于基于证书的身份验证,这些标识采用证书形式。
在每个设备上提供唯一证书的有效但效率低下的方法是预生成证书,并为所有供应链合作伙伴提供相应的私钥。 这种方法必须同时解决一些问题才可确保信任度,如下所示:
除了忽略 PKI 最佳做法(绝不共享私钥)外,还必须与供应链合作伙伴共享设备私钥,这使得供应链中的信任构建成本高昂。 这需要安装系统(例如安全室)来存放设备私钥和建立定期安全审核等流程。 这两者均会增加供应链成本。
安全记录供应链中的设备,然后通过设备停用功能在部署中管理它们,这已成为每个键/设备对的一对一任务。 这样的关系排除了设备的组管理,除非以某种方式将组的概念明确嵌入该过程。 因此,安全会计和设备生命周期管理成为沉重的运营负担。
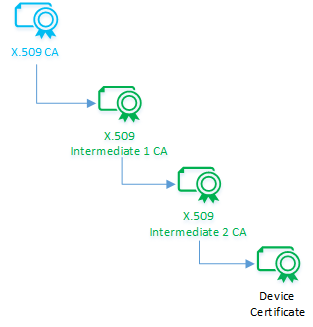
X.509 CA 证书身份验证使用证书链来为这些挑战提供完美的解决方案。 证书链如此生成:一个 CA 对一个中间 CA 进行签名,这个中间 CA 转而对另一个中间 CA 进行签名,依此类推,直到最后一个中间 CA 对设备进行签名。 证书链在 CA 证书与下游设备之间创建了一种一对多的关系。 通过此关系,可以通过注册 X.509 CA 证书一次将任意数量的设备注册到 IoT Hub。
X.509 CA 身份验证还简化了供应链物流。 典型的设备制造流程需要多个步骤及多个保管人。 通过使用证书颁发机构,可以将每个保管人签名到加密信任链,而不是将设备私钥委托给他们。 每个保管人在各自的制造流步骤中对设备进行签名。 整体结果是一个具有内置责任机制的优化供应链,通过使用加密信任链实现。
在设备保护其唯一私钥时,此过程可实现最大安全性。 为此,我们建议使用能够内在生成私钥的硬件安全模块 (HSM)。
X.509 证书流
本部分介绍如何使用 X.509 CA 证书对连接到IoT Hub的设备进行身份验证,其中包括以下步骤:
- 获取 X.509 CA 证书。
- 使用 X.509 CA 证书为设备签名。
- 将 X.509 CA 证书注册到IoT Hub。
- 对使用 X.509 CA 签名的设备进行身份验证。
- 如果设备证书遭到入侵,请吊销它。
获取 X.509 CA 证书
X.509 CA 证书位于每个设备的证书链的顶层。 可以根据目标用途购买或创建它。
对于生产环境,我们建议从专业的证书服务提供商处购买 X.509 CA 证书。
此外,还可以创建自签名的 X.509 CA 证书进行测试。 有关创建用于测试的证书的详细信息,请参阅创建和上传用于测试的证书。 我们不建议为生产环境使用自签名证书。
不管 X.509 CA 证书是如何获取的,都请确保保持其相应私钥的机密性,并始终对此私钥进行保护。
购买证书
购买 CA 证书的好处是可让知名根 CA 充当可信第三方,确保设备连接时 IoT 设备的合法性。 如果设备是在其中与第三方产品或服务进行交互的开放 IoT 网络的一部分,请选择此选项。
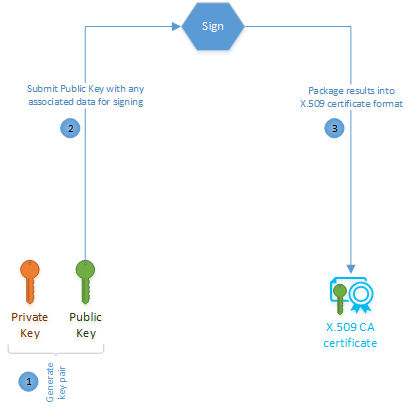
若要购买 X.509 CA 证书,请选择一家根证书服务提供商。 根证书颁发机构会指导你如何创建公钥/私钥对以及如何为他们的服务生成证书签名请求 (CSR)。 CSR 是从证书颁发机构申请证书的正式过程。 此次购买的结果是一个用于作为授权证书的证书。 由于 X.509 证书普遍存在,所以该证书格式可能已按照 IETF RFC 5280 标准正确设置。
创建自签名证书
创建自签名 X.509 CA 证书的过程与购买证书的过程类似,只不过它不需要像根证书颁发机构这样的第三方签名人。
在准备好购买证书颁发机构证书之前,可以选择此选项进行测试。 如果设备未连接到IoT Hub之外的任何第三方服务,还可以在生产环境中使用自签名 X.509 CA 证书。
在证书信任链中为设备签名
X.509 CA 证书的所有者能以加密方式为某个中间 CA 签名,而该 CA 又能为另一个中间 CA 签名,依此类推,直到最后一个中间 CA 为设备证书签名。 结果是一个由级联证书组成的链,其被称为证书信任链。 这种信任委派十分重要,因为它能够建立一种监护链,并避免共享签名密钥。
链中的这种证书级联体现了授权的逻辑转移。 许多供应链遵循此逻辑交接,这样每个中间 CA 就会在接收所有上游 CA 证书时登录到该链。 最后一个中间 CA 最终对每个设备进行签名,并将链中的所有颁发机构证书注入设备。
设备证书(也称为叶证书)必须将其公用名 (CN) 设置为在 Azure IoT Hub 中注册 IoT 设备时使用的 device ID(CN=deviceId)。 身份验证需要此设置。
对于使用 X.509 身份验证的模块,模块的证书公用名称 (CN) 格式必须如 CN=deviceId/moduleId 所示。
了解如何在签署设备时创建证书链。
将 X.509 CA 证书注册到 IoT Hub
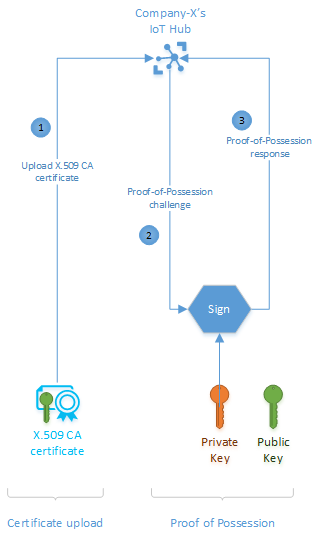
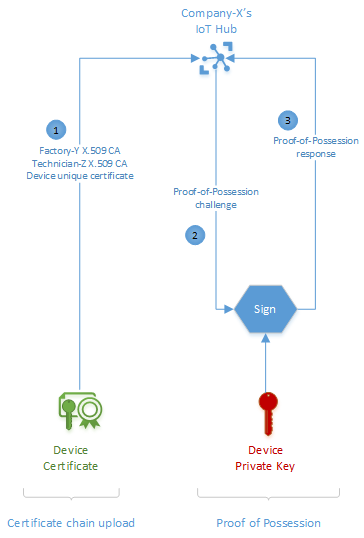
将 X.509 CA 证书注册到IoT Hub,该证书使用它对设备进行身份验证。 X.509 CA 证书可以验证其证书信任链中具有 CA 的任何设备。 注册 X.509 CA 证书是一个两步过程,包括上传证书文件,然后建立所有权证明。
上传过程需要上传包含证书的文件。 此文件不得包含任何私钥。
所有权证明步骤涉及你和IoT Hub之间的加密质询和响应过程,以验证你是否确实拥有 CA 证书。 可以选择自动或手动验证所有权。 对于手动验证,IoT Hub 生成一个随机质询挑战,您需要使用 CA 证书的私钥进行签名。 如果按照建议保持私钥的机密性并对其进行保护,则只有你才能拥有所需的信息来完成此步骤。 私钥的机密性是此方法的信任源。 在签署挑战后,上传包含结果的文件以完成验证。
了解如何注册 CA 证书
对使用 X.509 CA 证书签名的设备进行身份验证
注册 X.509 CA 证书并在证书信任链中为设备签名后,最后一步就是进行设备身份验证。 当 X.509 CA 签名的设备建立连接时,会上传其证书链用于验证。 使用此信息,IoT Hub在两个步骤中对设备进行身份验证。
首先,IoT Hub加密方式验证证书链以保持内部一致性。 然后,IoT Hub向设备发出所有权证明质询。 IoT Hub在设备的成功所有权证明响应中声明设备真实性。 此声明假设设备的私钥受到保护,并且只有该设备才能成功响应此质询。 我们建议使用设备中的安全芯片(例如硬件安全模块 (HSM))来保护私钥。
与IoT Hub的成功设备连接完成身份验证过程,也表明设置正确。 每次设备连接时,IoT Hub重新协商 TLS 会话并验证设备的 X.509 证书。
吊销设备证书
IoT Hub使用基于证书的身份验证对设备进行身份验证时,不会检查证书颁发机构的证书吊销列表。 如果由于证书泄露,需要阻止设备连接到IoT Hub,请在标识注册表中禁用该设备。 有关详细信息,请参阅禁用或删除设备。
示例方案
X 公司生产 Smart-X-Widget 并提供专业安装服务。 X 公司将制造和安装外包。 Y 工厂负责生产 Smart-X-Widget,技术人员 Z 负责安装。 Company-X 希望 Smart-X 小组件从 Factory-Y 直接寄送至 Technician-Z 进行安装,然后再直接连接到 Company-X 的 IoT Hub 实例。 为实现这一目的,X 公司需完成几个一次性安装操作,对 Smart-X-Widget 进行准备以实现自动连接。 此端到端方案包括以下步骤:
获取 X.509 CA 证书
将 X.509 CA 证书注册到 IoT Hub
将设备通过签名添加到证书信任链中
连接设备
教程:创建和上传用于测试的证书中演示了这些步骤。
获取证书
X 公司可以从公共根证书颁发机构购买 X.509 CA 证书,或者通过自签名过程创建一个证书。 上述任一选项都需要完成两个基本步骤:生成公钥/私钥对,并在证书中为公钥签名。
不同服务提供商完成这些步骤的方式详情有所不同。
将证书注册到IoT Hub
Company-X 需要将 X.509 CA 注册到IoT Hub,以便在它们连接时对 Smart-X-Widget 进行身份验证。 此过程是一次性的,完成后即可对任何数量的 Smart-X-Widget 设备进行身份验证和管理。 CA 证书和设备证书之间的一对多关系是使用 X.509 CA 身份验证方法的主要优点之一。 另一种方法是为每个 Smart-X-Widget 设备上传单个证书指纹,但这会增加运营成本。
注册 X.509 CA 证书的过程包括两个步骤:上传证书,然后提供证书所有权证明。
上传证书
X.509 CA 证书上传过程就是:将 CA 证书上传到IoT Hub。 IoT Hub需要文件中的证书。
在任何情况下,证书文件都不能包含任何私钥。 公钥基础结构 (PKI) 标准的最佳做法规定,X 公司的私钥只能驻留在 X 公司内部。
证明所有权
与所有数字证书相同,X.509 CA 证书也是易遭窃听的公共信息。 因此,窃听者可能会截获某份证书并尝试将其作为自己的证书上传。 在我们的示例中,IoT Hub必须确保上传的 CA 证书 Company-X 确实属于公司 X。 实现这一目的的方法是:要求 X 公司通过所有权证明 (PoP) 流程证明他们拥有该证书。
对于所有权证明流,IoT Hub生成一个随机数,以便 Company-X 使用其私钥进行签名。 如果 X 公司遵循了 PKI 最佳做法并保护了私钥,那么只有他们才能够正确响应所有权证明质询。 IoT Hub成功响应所有权证明质询后,继续注册 X.509 CA 证书。
IoT Hub成功响应持有证明挑战后,完成X.509 CA注册。
将设备通过签名添加到证书信任链中
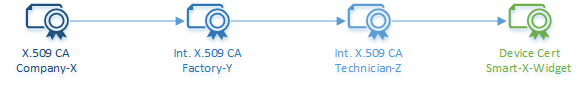
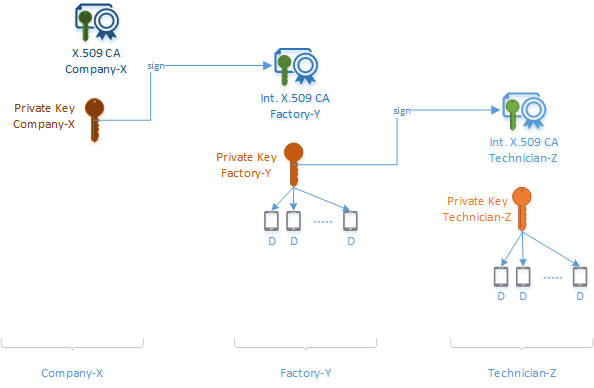
在本示例中,基于证书的身份验证意味着每个 Smart-X-Widget 必须拥有唯一设备证书。 X 公司决定使用 CA 证书并为每个设备创建证书信任链,而不是为每个设备创建单个证书/密钥对。
在本例中,X 公司对 Y 工厂进行签名,Y 工厂转而对 Z 技术人员进行签名,而 Z 技术人员最后要对 Smart-X-Widget 进行签名。
下图显示了信任证书链如何在 Smart-X-Widget 示例中组合到一起。
- X 公司永远不会与任何 Smart-X-Widget 进行物理交互。 它通过为 Y 工厂的中间 CA 证书签名来启动信任证书链。
- Y 工厂现在拥有自己的中间 CA 证书和来自 X 公司的签名。 它将这些项的副本传递到每个设备。 它还使用其中间 CA 证书来为技术人员 Z 的中间 CA 证书和 Smart-X-Widget 设备证书签名。
- 技术人员 Z 现在拥有自己的中间 CA 证书和来自 Y 工厂的签名。 它将这些项的副本传递到每个设备。 它还使用其中间 CA 证书来为 Smart-X-Widget 设备证书签名。
- 现在,每个 Smart-X-Widget 设备都有自己唯一的、用于在整个供应链中交互的设备证书以及来自每个中间 CA 证书的公钥和签名副本。 这些证书和签名可以追溯到原始的 X 公司根。
CA 身份验证方法将安全责任引入了设备制造供应链。 由于证书链过程,链中每位成员的操作均已加密记录且可验证。
此过程依赖于这种假设:唯一的设备公钥/私钥对是单独创建的,并且私钥始终在设备中受到保护。 幸运的是,硬件安全模块 (HSM) 形式的安全硅芯片能够在内部生成密钥并保护私钥。 X 公司只需将此类安全芯片之一添加到 Smart-X-Widget 的组件材料清单即可。
对设备进行身份验证
针对 X.509 CA 身份验证所制造的设备配有唯一设备证书和其各自制造供应链的证书链。 即使是首次连接,也只需 2 步即可实现设备连接:证书链上传、所有权证明。
在我们的示例中,每个 Smart-X-Widget 将其唯一的设备证书与 Factory-Y 和 Technician-Z X.509 CA 证书一起上传,然后响应来自IoT Hub的所有权证明质询。
使用来自公司 X 的预注册 X.509 CA 证书,IoT Hub 验证上传的证书链的内部一致性,并确认证书链是由 X.509 CA 证书的有效所有者创建的。 与 X.509 CA 注册过程一样,IoT Hub使用所有权证明质询响应过程来确定链(因此设备证书)属于上传它的设备。 成功的响应会触发IoT Hub接受设备作为验证并向其授予连接。
信任的基础在于保护私钥(包括设备私钥)。 因此,我们一再强调使用硬件安全模块 (HSM) 形式的安全硅芯片保护设备私钥的重要性,也一再强调绝不共享链中任何证书的私钥这一整体最佳做法。
后续步骤
若要详细了解构成 X.509 证书的字段,请参阅 X.509 证书。
如果你有根 CA 证书或从属 CA 证书,并想要将其上传到 IoT 中心,则必须验证自己对该证书的所有权。 有关详细信息,请参阅教程:创建和上传用于测试的证书。