Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Microsoft Entra External ID combines powerful solutions for working with people outside your organization. With External ID capabilities, you can allow external identities to securely access your apps and resources.
Whether you're working with external partners, consumers, or business customers, users can bring their own identities. These identities can include corporate or government-issued accounts and social identity providers.
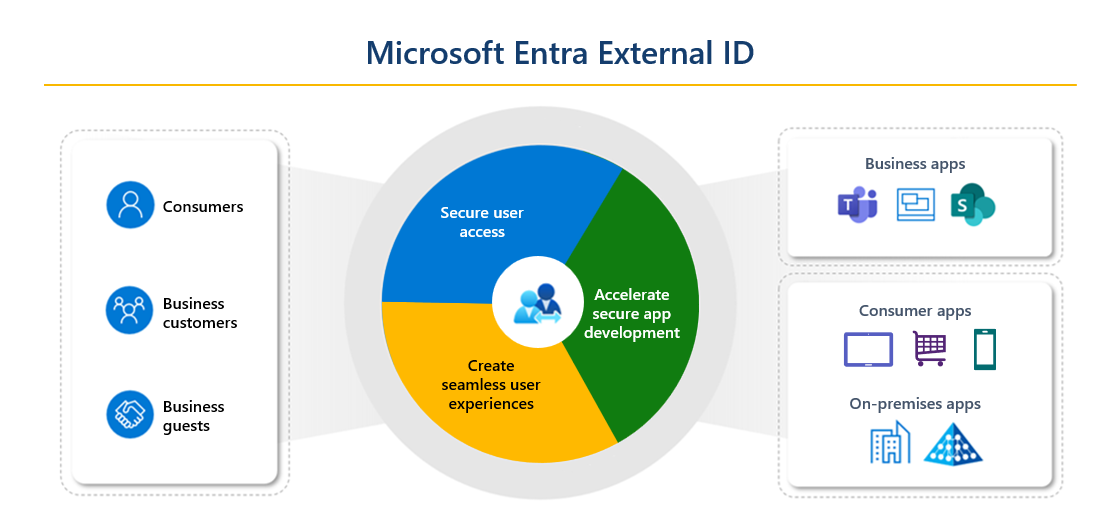
These scenarios fall within the scope of External ID:
If you're an organization or a developer who creates consumer apps, use External ID to quickly add authentication and customer identity and access management (CIAM) to your application. Register your app, create customized sign-in experiences, and manage your app users in a Microsoft Entra tenant in an external configuration. This tenant is separate from your employees and organizational resources.
If you want to enable your employees to collaborate with business partners and guests, use B2B collaboration in External ID. Allow secure access to your enterprise apps through invitation. Determine the level of access that guests have to the Microsoft Entra tenant that contains your employees and organizational resources, which is a tenant in a workforce configuration.
External ID is a flexible solution for both:
- Consumer-oriented app developers who need authentication and CIAM
- Businesses that seek secure B2B collaboration
Collaborate with business guests
External ID B2B collaboration allows your workforce to collaborate with external business partners. You can invite anyone to sign in to your Microsoft Entra organization by using their own credentials so they can access the apps and resources that you want to share with them.
Use B2B collaboration when you need to let business guests access your Office 365 apps, software-as-a-service (SaaS) apps, and line-of-business apps. There are no credentials associated with business guests. Instead, they authenticate with their home organization or identity provider, and then your organization checks their eligibility for guest collaboration.
There are various ways to add business guests to your organization for collaboration:
Invite users to collaborate by using their Microsoft Entra accounts, Microsoft accounts, or social identities that you enable. An admin can use the Microsoft Entra admin center or PowerShell to invite users to collaborate. Users sign in to the shared resources by using a simple redemption process with their work, school, or other email account.
Use Microsoft Entra entitlement management, a feature for managing identity and access for external users at scale. You can use this feature to automate access request workflows, access assignments, reviews, and expiration.
A user object is created for business guests in the same directory that you use for your employees. You can manage this user object like other user objects in your directory. For example, you can add it to groups. You can assign permissions to the user object for authorization while letting users use their existing credentials for authentication.
You can use cross-tenant access settings to manage collaboration with other Microsoft Entra organizations and across Azure clouds. For collaboration with non-Microsoft Entra external users and organizations, use external collaboration settings.
Related technologies
Several Microsoft Entra technologies are related to collaboration with external users and organizations. As you design your External ID collaboration model, consider these other features.
Azure Active Directory B2C (Azure AD B2C)
Important
Effective May 1, 2025, Azure Active Directory B2C (Azure AD B2C) is no longer available for new customers to purchase. To learn more, see Is Azure AD B2C still available to purchase? in our FAQ.
Azure AD B2C is a legacy solution for customer identity and access management. Azure AD B2C includes a separate consumer-based directory that you manage in the Azure portal through the Azure AD B2C service. Each Azure AD B2C tenant is separate and distinct from other Microsoft Entra ID and Azure AD B2C tenants.
The Azure AD B2C portal experience is similar to Microsoft Entra ID, but there are key differences. For example, you can customize your user journeys by using the Identity Experience Framework.
For more information about how an Azure AD B2C tenant differs from a Microsoft Entra tenant, see Supported Microsoft Entra features in Azure AD B2C. For details about configuring and managing Azure AD B2C, see the Azure AD B2C documentation.
Microsoft Entra entitlement management for business guest sign-up
You might not know ahead of time which individual external collaborators need access to your resources. You need a way for users from partner companies to sign themselves up with policies that you control.
To enable users from other organizations to request access, you can use Microsoft Entra entitlement management to configure policies that manage access for external users. Upon approval, these users are provisioned with guest accounts and assigned to groups, apps, and SharePoint Online sites.
Multitenant applications
If you offer a SaaS application to many organizations, you can configure your application to accept sign-ins from any Microsoft Entra tenant. This configuration is called making your application multitenant. Users in any Microsoft Entra tenant can sign in to your application after they consent to use their account with your application. Learn how to enable multitenant sign-ins.
Microsoft Graph APIs
All External ID features are also supported for automation through Microsoft Graph APIs, except the feature listed in the next section. For more information, see Manage Microsoft Entra identity and network access by using Microsoft Graph.
Capabilities not supported in Microsoft Graph
| External ID feature | Supported in | Automation workarounds |
|---|---|---|
| Identify organizations that you belong to | Workforce tenants | See the Tenants - List Azure Resource Manager API. For Teams shared channels, use the Get tenantReferences Microsoft Graph API. |
Microsoft Graph API for B2B collaboration
-
By using these APIs, you can set up policies for inbound and outbound collaboration. For example, you can allow or block features for everyone by default and limit access to specific organizations, groups, users, and applications.
You can also use these APIs to accept MFA and device claims (compliant claims and Microsoft Entra hybrid-joined claims) from other Microsoft Entra organizations.
Resource type for invitation management. Build your own onboarding experiences for business guests. For example, you can use the Create Invitation API to automatically send a customized invitation email directly to the B2B user. Or you can use the
inviteRedeemUrlvalue returned in the creation response to craft your own invitation (through your communication mechanism of choice) to the invited user.