Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
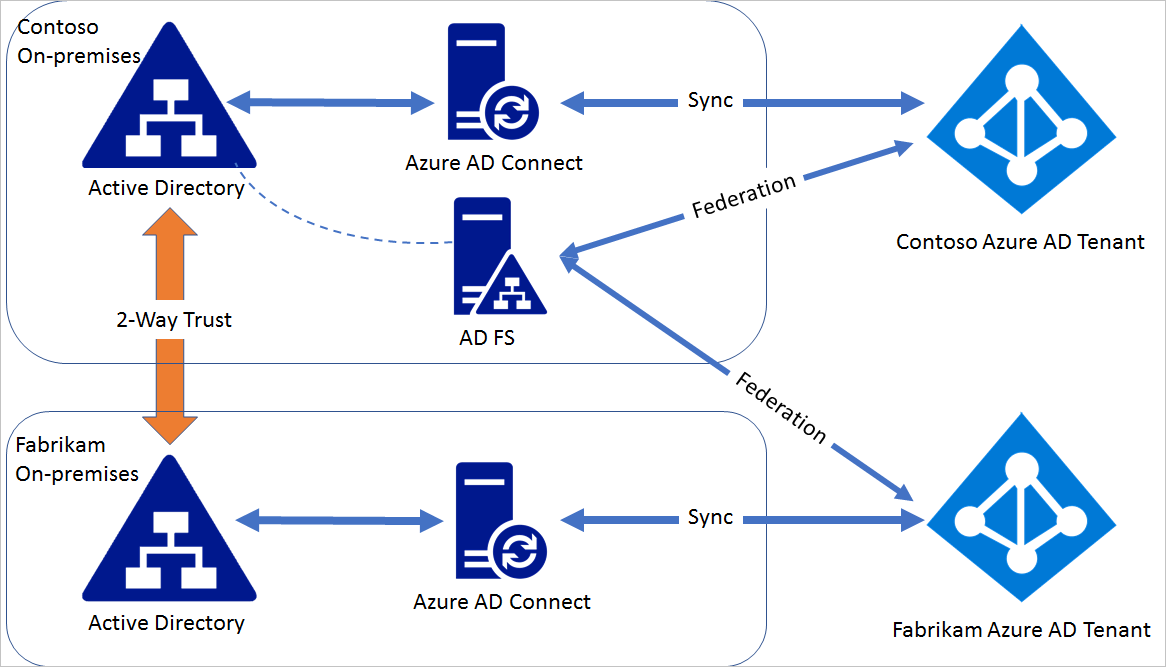
A single high available AD FS farm can federate multiple forests if they have two-way trust between them. These multiple forests may or may not correspond to the same Microsoft Entra ID. This article provides instructions on how to configure federation between a single AD FS deployment and multiple instances of Microsoft Entra ID.
Note
Device writeback and automatic device join are not supported in this scenario.
Note
Microsoft Entra Connect cannot be used to configure federation in this scenario as Microsoft Entra Connect can configure federation for domains in a single Microsoft Entra ID.
Steps for federating AD FS with multiple Microsoft Entra IDs
Consider a domain contoso.com in Microsoft Entra contoso.partner.onmschina.cn is already federated with the AD FS on-premises installed in contoso.com on-premises Active Directory environment. Fabrikam.com is a domain in fabrikam.partner.onmschina.cn Microsoft Entra ID.
Step 1: Establish a two-way trust
For AD FS in contoso.com to be able to authenticate users in fabrikam.com, a two-way trust is needed between contoso.com and fabrikam.com. Follow the guideline in this article to create the two-way trust.
Step 2: Modify contoso.com federation settings
The default issuer set for a single domain federated to AD FS is "http://ADFSServiceFQDN/adfs/services/trust", for example, http://fs.contoso.com/adfs/services/trust. Microsoft Entra ID requires unique issuer for each federated domain. Because AD FS is going to federate two domains, the issuer value needs to be modified so that it's unique.
On the AD FS server, open Microsoft Graph PowerShell and do the following steps:
Connect to the Microsoft Entra ID that contains the domain contoso.com.
Connect-MgGraph -Environment China -ClientId 'YOUR_CLIENT_ID' -TenantId 'YOUR_TENANT_ID' -Scope 'Domain.ReadWrite.All'
Update the federation settings for contoso.com:
$domainId = "contoso.com"
$newIssuer = "http://contoso.com/adfs/services/trust"
$fed = Get-MgDomainFederationConfiguration -DomainId $domainId
Update-MgDomainFederationConfiguration `
-DomainId $domainId `
-InternalDomainFederationId $fed.Id `
-IssuerUri $newIssuer
Issuer in the domain federation setting is changed to http://contoso.com/adfs/services/trust and an issuance claim rule is added for the Microsoft Entra ID Relying Party Trust to issue the correct issuerId value based on the UPN suffix.
Step 3: Federate fabrikam.com with AD FS
In Microsoft Graph PowerShell session perform the following steps: Connect to Microsoft Entra ID that contains the domain fabrikam.com
Connect-MgGraph -Environment China -ClientId 'YOUR_CLIENT_ID' -TenantId 'YOUR_TENANT_ID' -Scope 'Domain.ReadWrite.All'
Convert the fabrikam.com managed domain to federated:
# Create the federation configuration
$params = @{
"@odata.type" = "#microsoft.graph.internalDomainFederation"
displayName = "fabrikam.com"
issuerUri = $issuerUri
signingCertificate = $signingCertificate
passiveSignInUri = $passiveSignInUri
preferredAuthenticationProtocol = $preferredAuthenticationProtocol
activeSignInUri = $activeSignInUri
signOutUri = $signOutUri
}
New-MgDomainFederationConfiguration -DomainId $domainId -BodyParameter $params
# Switch the domain authentication type to Federated
Update-MgDomain -DomainId $domainId -AuthenticationType "Federated"
The prior operation federates the domain fabrikam.com with the same AD FS. You can verify the domain settings by using Get-MsolDomainFederationSettings for both domains.