Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
By default, the internet can access Service Bus namespaces as long as the request contains valid authentication and authorization. By using the IP firewall, you can restrict inbound traffic to a set of IPv4 addresses or IPv4 address ranges in CIDR (Classless Inter-Domain Routing) notation.
This feature is helpful in scenarios where Azure Service Bus should be accessible only from certain well-known sites. Firewall rules enable you to configure rules to accept traffic originating from specific IPv4 addresses. For example, if you use Service Bus with Azure Express Route, you can create a firewall rule to allow traffic from only your on-premises infrastructure IP addresses or addresses of a corporate NAT gateway.
This article shows you how to configure IP firewall rules for a Service Bus namespace using the Azure portal, Azure CLI, PowerShell, or ARM templates.
IP firewall rules
IP firewall rules restrict inbound traffic to a set of IPv4 addresses or IPv4 address ranges in CIDR (Classless Inter-Domain Routing) notation.
IP firewall rules apply at the Service Bus namespace level. The rules apply to all connections from clients using any supported protocol (AMQP (5671) and HTTPS (443)). Service Bus rejects any connection attempt from an IP address that doesn't match an allowed IP rule on the Service Bus namespace as unauthorized. The response doesn't mention the IP rule. IP filter rules are applied in order, and the first rule that matches the IP address determines the accept or reject action.
Note
Networking options differ between Service Bus SKUs. The Standard SKU supports IP filtering but doesn't include the "Trusted Services" option. For Premium SKU networking features, see the dedicated Premium SKU networking documentation.
Important points
Private Endpoints and Service Endpoints are supported only in the premium tier of Service Bus. If upgrading to the premium tier isn't an option, you can use IP firewall rules by using the Azure portal, Azure Resource Manager templates, Azure CLI, PowerShell, or REST API.
Specify at least one IP firewall rule or virtual network rule for the namespace to allow traffic only from the specified IP addresses or subnet of a virtual network. If there are no IP and virtual network rules, the namespace is accessible over the public internet (using the access key).
Implementing firewall rules can prevent other Azure services from interacting with Service Bus. As an exception, you can allow access to Service Bus resources from certain trusted services even when IP filtering is enabled. For a list of trusted services, see Trusted services.
The following services don't support Trusted services and instead utilize a feature called VNet Integration to make outbound calls through a VNet:
- Azure App Service
- Azure Functions
For more details, see Integrate your app with an Azure virtual network.
Use Azure portal
When creating a namespace, you can either allow public only (from all networks) or private only (only via private endpoints) access to the namespace. Once the namespace is created, you can allow access from specific IP addresses or from specific virtual networks (using network service endpoints).
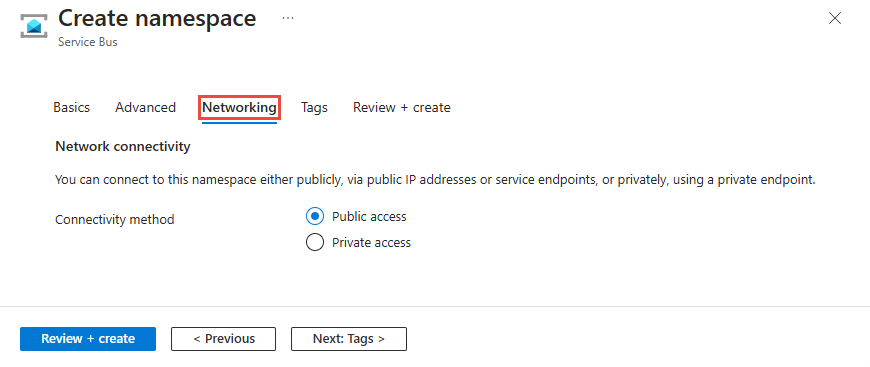
Configure public access when creating a namespace
To enable public access, select Public access on the Networking page of the namespace creation wizard.
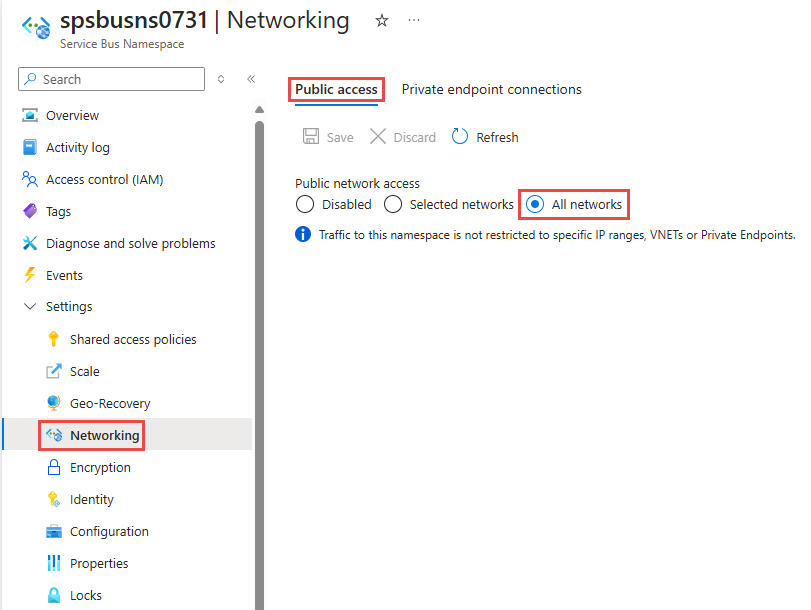
After you create the namespace, select Networking on the left menu of the Service Bus Namespace page. You see that All Networks option is selected. You can select Selected Networks option and allow access from specific IP addresses or specific virtual networks. The next section provides you details on configuring IP firewall to specify the IP addresses from which the access is allowed.
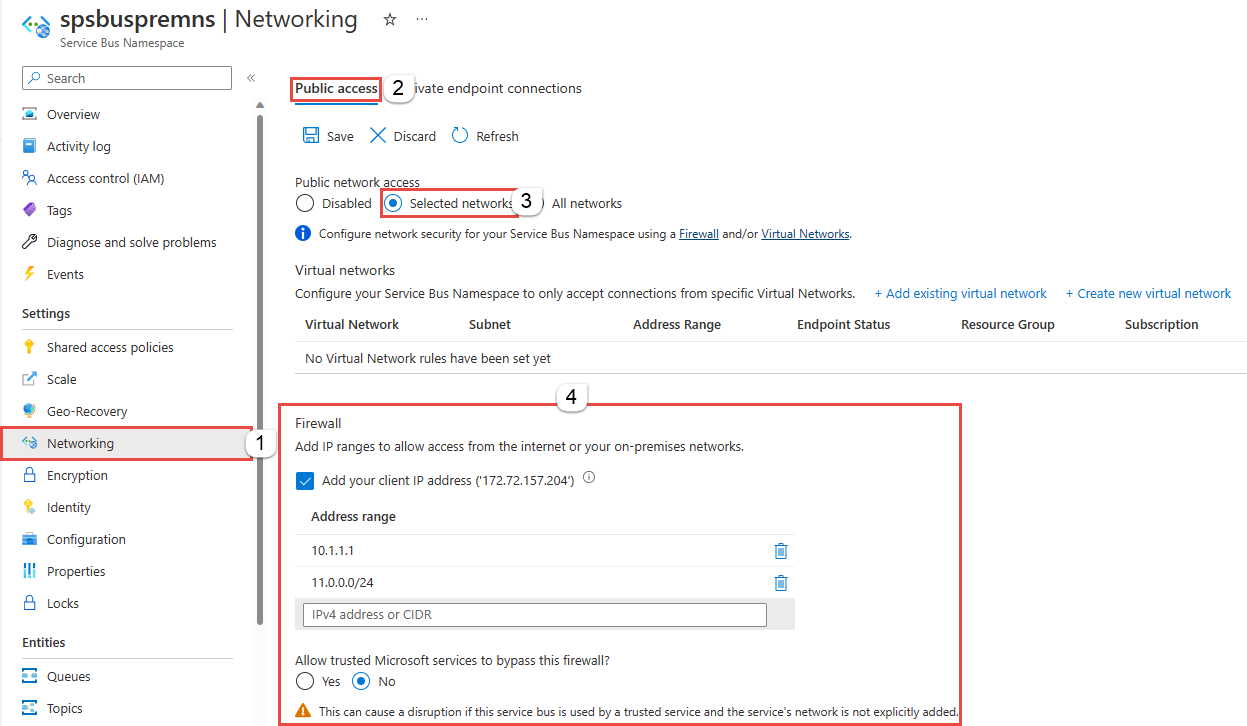
Configure IP firewall for an existing namespace
This section shows you how to use the Azure portal to create IP firewall rules for a Service Bus namespace.
Go to your Service Bus namespace in the Azure portal.
On the left menu, select the Networking option under Settings.
Note
You see the Networking tab only for premium namespaces.
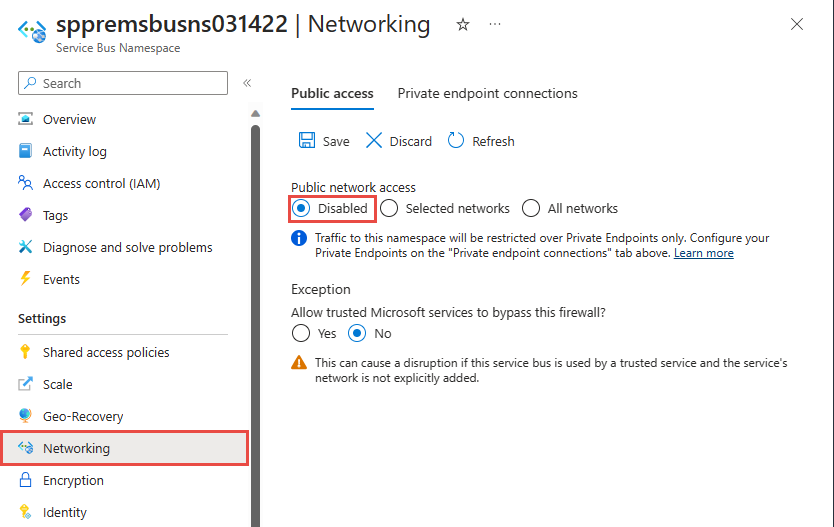
On the Networking page, for Public network access, you can set one of the three following options. Choose the Selected networks option to allow access from only specified IP addresses.
Disabled. This option disables any public access to the namespace. The namespace is accessible only through private endpoints.
Choose whether you want to allow trusted Azure services to bypass the firewall. For the list of trusted Azure services for Azure Service Bus, see the Trusted Azure services section.
Selected networks. This option enables public access to the namespace from selected networks by using an access key.
Important
If you choose Selected networks, add at least one IP firewall rule or a virtual network that has access to the namespace. Choose Disabled if you want to restrict all traffic to this namespace over private endpoints only.
All networks (default). This option enables public access from all networks by using an access key. If you select the All networks option, Service Bus accepts connections from any IP address (by using the access key). This setting is equivalent to a rule that accepts the 0.0.0.0/0 IP address range.
To allow access from only specified IP address, select the Selected networks option if it isn't already selected. In the Firewall section, follow these steps:
Select Add your client IP address option to give your current client IP the access to the namespace.
For address range, enter a specific IPv4 address or a range of IPv4 address in CIDR notation.
Specify whether you want to allow trusted Microsoft services to bypass this firewall. For the list of trusted Azure services for Azure Service Bus, see the Trusted Azure services section.
Warning
If you select the Selected networks option and don't add at least one IP firewall rule or a virtual network on this page, the namespace can't be accessed over public internet (using the access key).
Select Save on the toolbar to save the settings. Wait for a few minutes for the confirmation to show up on the portal notifications.
Note
To restrict access to specific virtual networks, see Allow access from specific networks.
Trusted Microsoft services
When you enable the Allow trusted Microsoft services to bypass this firewall setting, the following services are granted access to your Service Bus resources.
Important
When enabling trusted Microsoft services, always assign a Managed Identity. This identity facilitates secure communication between your Service Bus namespace and the trusted Azure service.
| Trusted service | Supported usage scenarios |
|---|---|
| Azure Event Grid | Allows Azure Event Grid to send events to queues or topics in your Service Bus namespace. You also need to do the following steps:
For more information, see Event delivery with a managed identity |
| Azure Stream Analytics | Allows an Azure Stream Analytics job to output data to Service Bus queues to topics. Important: The Stream Analytics job should be configured to use a managed identity to access the Service Bus namespace. Add the identity to the Azure Service Bus Data Sender role on the Service Bus namespace. |
| Azure IoT Hub | Allows an IoT hub to send messages to queues or topics in your Service Bus namespace. You also need to do the following steps: |
| Azure API Management | The API Management service allows you to send messages to a Service Bus queue/topic in your Service Bus Namespace.
|
| Azure Monitor (Diagnostic Settings and Action Groups) | Allows Azure Monitor to send diagnostic information and alert notifications to Service Bus in your Service Bus namespace. Azure Monitor can read from and write data to the Service Bus namespace. |
| Azure Synapse | Allows Azure Synapse to connect to the service bus using the Synapse Workspace Managed Identity. Add the Azure Service Bus Data Sender, Receiver or Owner role to the identity on the Service Bus namespace. |
The other trusted services for Azure Service Bus can be found below:
- Azure Data Explorer
- Azure Health Data Services
- Azure Arc
- Azure Kubernetes
- Azure Machine Learning
- Microsoft Purview
- Microsoft Defender for Cloud
- Azure Provider Hub
Use a template
This section shows sample templates that add a virtual network and a firewall rule to an existing Service Bus namespace.
ipMask is a single IPv4 address or a block of IP addresses in CIDR notation. For example, in CIDR notation 70.37.104.0/24 represents the 256 IPv4 addresses from 70.37.104.0 to 70.37.104.255, with 24 indicating the number of significant prefix bits for the range.
Note
The default value of the defaultAction is Allow. When you add virtual network or firewall rules, make sure you set the defaultAction to Deny.
@description('Name of the Service Bus namespace')
param namespaceName string
@description('Location for all resources.')
param location string = resourceGroup().location
resource serviceBusNamespace 'Microsoft.ServiceBus/namespaces@2024-01-01' = {
name: namespaceName
location: location
sku: {
name: 'Premium'
tier: 'Premium'
capacity: 1
}
properties: {
premiumMessagingPartitions: 1
minimumTlsVersion: '1.2'
publicNetworkAccess: 'Enabled'
disableLocalAuth: false
zoneRedundant: true
}
resource networkRuleSet 'networkRuleSets' = {
name: 'default'
properties: {
publicNetworkAccess: 'Enabled'
defaultAction: 'Deny'
virtualNetworkRules: []
ipRules: [
{
ipMask: '10.1.1.1'
action: 'Allow'
}
{
ipMask: '11.0.0.0/24'
action: 'Allow'
}
]
}
}
}
To deploy the template, follow the instructions for Azure Resource Manager.
Important
If you don't specify any IP or virtual network rules, all traffic flows into the namespace even if you set the defaultAction to deny. Users can access the namespace over the public internet (by using the access key). To allow traffic only from the specified IP addresses or subnet of a virtual network, specify at least one IP rule or virtual network rule for the namespace.
Use Azure CLI
Use az servicebus namespace network-rule-set add, list, update, and remove commands to manage IP firewall rules for a Service Bus namespace.
Use Azure PowerShell
Use the following Azure PowerShell commands to add, list, remove, update, and delete IP firewall rules.
- Use
New-AzServiceBusIPRuleConfigandSet-AzServiceBusNetworkRuleSettogether to add an IP firewall rule.
Default action and public network access
REST API
For API versions 2021-01-01-preview and earlier, the default value of the defaultAction property is Deny. However, the deny rule isn't enforced unless you set IP filters or virtual network rules. If you don't set any IP filters or virtual network rules, Service Bus treats the default action as Allow.
From API version 2021-06-01-preview onwards, the default value of the defaultAction property is Allow, to accurately reflect the service-side enforcement. If you set the default action to Deny, the service enforces IP filters and virtual network rules. If you set the default action to Allow, the service doesn't enforce IP filters and virtual network rules. The service remembers the rules when you turn them off and then back on again.
API versions 2021-06-01-preview onwards also introduce a new property named publicNetworkAccess. If you set it to Disabled, operations are restricted to private links only. If you set it to Enabled, operations are allowed over the public internet.
For more information about these properties, see Create or Update Private Endpoint Connections.
Note
None of the above settings bypass validation of claims via SAS or Microsoft Entra authentication. The authentication check always runs after the service validates the network checks that are configured by defaultAction, publicNetworkAccess, and privateEndpointConnections settings.
Azure portal
Azure portal always uses the latest API version to get and set properties. If you previously configured your namespace by using 2021-01-01-preview and earlier with defaultAction set to Deny, and specified zero IP filters and virtual network rules, the portal previously checked Selected Networks on the Networking page of your namespace. Now, it checks the All networks option.
Related content
To constrain access to Service Bus to Azure virtual networks, see the following article: