Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
You can use private endpoints for your Azure Storage accounts to allow clients on an Azure Virtual Network to securely access data over a Private Link. The private endpoint uses a separate IP address from the virtual network address space for each storage account service. Network traffic between the clients on the virtual network and the storage account traverses over the virtual network and a private link on the Microsoft backbone network, eliminating exposure from the public internet.
Note
Private endpoints are not available for general-purpose v1 storage accounts.
Using private endpoints for your storage account enables you to:
- Secure your storage account by using a private link. You can manually configure the storage firewall to block connections on the public endpoint of the storage service. Creating a private link does not automatically block connections on the public endpoint.
- Increase security for the virtual network by enabling you to block exfiltration of data from the virtual network.
- Securely connect to storage accounts from on-premises networks that connect to the virtual network using VPN or ExpressRoutes with private-peering.
Conceptual overview
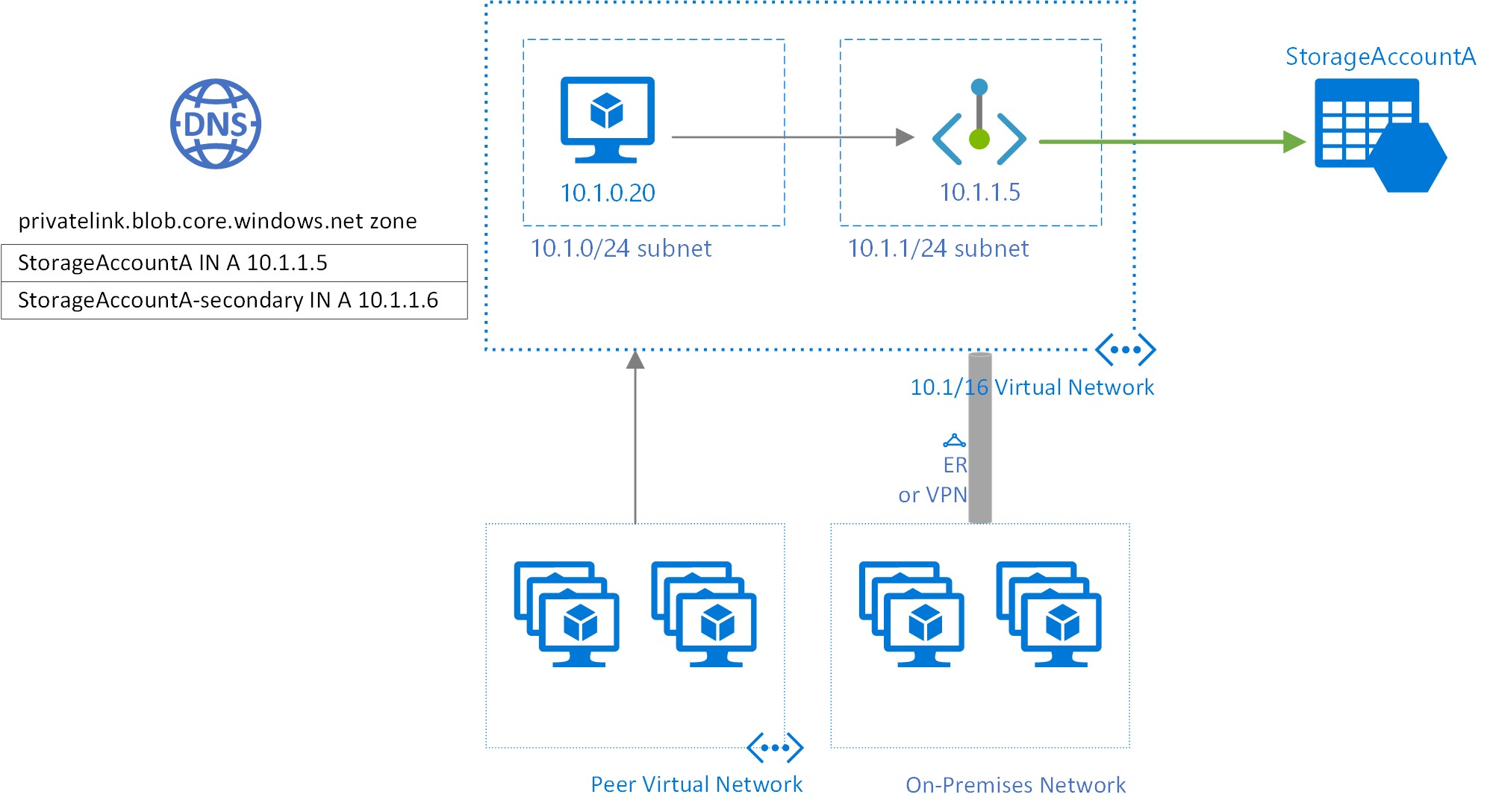
A private endpoint is a special network interface for an Azure service in your Virtual Network. When you create a private endpoint for your storage account, it provides secure connectivity between clients on your virtual network and your storage. The private endpoint is assigned an IP address from the IP address range of your virtual network. The connection between the private endpoint and the storage service uses a secure private link.
Applications in the virtual network can connect to the storage service over the private endpoint seamlessly, using the same connection strings and authorization mechanisms that they would use otherwise. Private endpoints can be used with all protocols supported by the storage account, including REST and SMB.
Private endpoints can be created in subnets that use Service Endpoints. Clients in a subnet can thus connect to one storage account using private endpoint, while using service endpoints to access others.
When you create a private endpoint for a storage service in your virtual network, a consent request is sent for approval to the storage account owner. If the user requesting the creation of the private endpoint is also an owner of the storage account, this consent request is automatically approved.
Storage account owners can manage consent requests and the private endpoints through the 'Private endpoints' tab for the storage account in the Azure portal.
Tip
If you want to restrict access to your storage account through the private endpoint only, configure the storage firewall to deny or control access through the public endpoint.
You can secure your storage account to only accept connections from your virtual network by configuring the storage firewall to deny access through its public endpoint by default. You don't need a firewall rule to allow traffic from a virtual network that has a private endpoint, since the storage firewall only controls access through the public endpoint. Private endpoints instead rely on the consent flow for granting subnets access to the storage service.
Additionally, when a private endpoint is configured, traffic from the associated virtual network is always allowed, even if public network access is disabled on the storage account.
Note
When copying blobs between storage accounts, your client must have network access to both accounts. So if you choose to use a private link for only one account (either the source or the destination), make sure that your client has network access to the other account. To learn about other ways to configure network access, see Configure Azure Storage firewalls and virtual networks.
Creating a private endpoint
To create a private endpoint by using the Azure portal, see Connect privately to a storage account from the Storage Account experience in the Azure portal.
To create a private endpoint by using PowerShell or the Azure CLI, see either of these articles. Both of them feature an Azure web app as the target service, but the steps to create a private link are the same for an Azure Storage account.
When you create a private endpoint, you must specify the storage account and the storage service to which it connects.
You need a separate private endpoint for each storage resource that you need to access, namely Blobs, Data Lake Storage, Files, Queues, Tables, or Static Websites. On the private endpoint, these storage services are defined as the target sub-resource of the associated storage account.
If you create a private endpoint for the Data Lake Storage storage resource, then you should also create one for the Blob Storage resource. That's because operations that target the Data Lake Storage endpoint might be redirected to the Blob endpoint. Similarly, if you add a private endpoint for Blob Storage only, and not for Data Lake Storage, some operations (such as Manage ACL, Create Directory, Delete Directory, etc.) will fail since the APIs require a DFS private endpoint. By creating a private endpoint for both resources, you ensure that all operations can complete successfully.
Tip
Create a separate private endpoint for the secondary instance of the storage service for better read performance on RA-GRS accounts. Make sure to create a general-purpose v2(Standard or Premium) storage account.
For read access to the secondary region with a storage account configured for geo-redundant storage, you need separate private endpoints for both the primary and secondary instances of the service. You don't need to create a private endpoint for the secondary instance for failover. The private endpoint will automatically connect to the new primary instance after failover. For more information about storage redundancy options, see Azure Storage redundancy.
Connecting to a private endpoint
Clients on a virtual network using the private endpoint should use the same connection string for the storage account as clients connecting to the public endpoint. We rely upon DNS resolution to automatically route the connections from the virtual network to the storage account over a private link.
Important
Use the same connection string to connect to the storage account using private endpoints as you'd use otherwise. Don't connect to the storage account using its privatelink subdomain URL.
By default, We create a private DNS zone attached to the virtual network with the necessary updates for the private endpoints. However, if you're using your own DNS server, you may need to make additional changes to your DNS configuration. The section on DNS changes below describes the updates required for private endpoints.
DNS changes for private endpoints
Note
For details on how to configure your DNS settings for private endpoints, see Azure Private Endpoint DNS configuration.
When you create a private endpoint, the DNS CNAME resource record for the storage account is updated to an alias in a subdomain with the prefix privatelink. By default, we also create a private DNS zone, corresponding to the privatelink subdomain, with the DNS A resource records for the private endpoints.
When you resolve the storage endpoint URL from outside the virtual network with the private endpoint, it resolves to the public endpoint of the storage service. When resolved from the virtual network hosting the private endpoint, the storage endpoint URL resolves to the private endpoint's IP address.
For the illustrated example above, the DNS resource records for the storage account 'StorageAccountA', when resolved from outside the virtual network hosting the private endpoint, will be:
| Name | Type | Value |
|---|---|---|
StorageAccountA.blob.core.chinacloudapi.cn |
CNAME | StorageAccountA.privatelink.blob.core.chinacloudapi.cn |
StorageAccountA.privatelink.blob.core.chinacloudapi.cn |
CNAME | <storage service public endpoint> |
| <storage service public endpoint> | A | <storage service public IP address> |
As previously mentioned, you can deny or control access for clients outside the virtual network through the public endpoint using the storage firewall.
The DNS resource records for StorageAccountA, when resolved by a client in the virtual network hosting the private endpoint, will be:
| Name | Type | Value |
|---|---|---|
StorageAccountA.blob.core.chinacloudapi.cn |
CNAME | StorageAccountA.privatelink.blob.core.chinacloudapi.cn |
StorageAccountA.privatelink.blob.core.chinacloudapi.cn |
A | 10.1.1.5 |
This approach enables access to the storage account using the same connection string for clients on the virtual network hosting the private endpoints, as well as clients outside the virtual network.
If you are using a custom DNS server on your network, clients must be able to resolve the FQDN for the storage account endpoint to the private endpoint IP address. You should configure your DNS server to delegate your private link subdomain to the private DNS zone for the virtual network, or configure the A records for StorageAccountA.privatelink.blob.core.chinacloudapi.cn with the private endpoint IP address.
Tip
When using a custom or on-premises DNS server, you should configure your DNS server to resolve the storage account name in the privatelink subdomain to the private endpoint IP address. You can do this by delegating the privatelink subdomain to the private DNS zone of the virtual network or by configuring the DNS zone on your DNS server and adding the DNS A records.
The recommended DNS zone names for private endpoints for storage services, and the associated endpoint target sub-resources, are:
| Storage service | Target sub-resource | Zone name |
|---|---|---|
| Blob service | blob | privatelink.blob.core.chinacloudapi.cn |
| Data Lake Storage | dfs | privatelink.dfs.core.chinacloudapi.cn |
| File service | file | privatelink.file.core.chinacloudapi.cn |
| Queue service | queue | privatelink.queue.core.chinacloudapi.cn |
| Table service | table | privatelink.table.core.chinacloudapi.cn |
| Static Websites | web | privatelink.web.core.chinacloudapi.cn |
For more information on configuring your own DNS server to support private endpoints, refer to the following articles:
Pricing
For pricing details, see Azure Private Link pricing.
Known Issues
Keep in mind the following known issues about private endpoints for Azure Storage.
Storage access constraints for clients in virtual networks with private endpoints
Clients in virtual networks with existing private endpoints face constraints when accessing other storage accounts that have private endpoints. For example, suppose a virtual network N1 has a private endpoint for a storage account A1 for Blob storage. If storage account A2 has a private endpoint in a virtual network N2 for Blob storage, then clients in virtual network N1 must also access Blob storage in account A2 using a private endpoint. If storage account A2 does not have any private endpoints for Blob storage, then clients in virtual network N1 can access Blob storage in that account without a private endpoint.
This constraint is a result of the DNS changes made when account A2 creates a private endpoint.
Copying blobs between storage accounts
You can copy blobs between storage accounts by using private endpoints only if you use the Azure REST API, or tools that use the REST API. These tools include AzCopy, Storage Explorer, Azure PowerShell, Azure CLI, and the Azure Blob Storage SDKs.
Only private endpoints that target the blob or file storage resource endpoint are supported. This includes REST API calls against Data Lake Storage accounts in which the blob resource endpoint is referenced explicitly or implicitly. Private endpoints that target the Data Lake Storage dfs resource endpoint are not yet supported. Copying between storage accounts by using the Network File System (NFS) protocol is not yet supported.