Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Applies to: ✔️ Linux VMs ✔️ Flexible scale sets
This article is for Windows users who want to create and use secure shell (SSH) keys to connect to Linux virtual machines (VMs) in Azure. You can also generate and store SSH keys in the Azure portal to use when creating VMs in the portal.
To use SSH keys from a Linux or macOS client, see the quick steps. For a more detailed overview of SSH, see Detailed steps: Create and manage SSH keys for authentication to a Linux VM in Azure.
Overview of SSH and keys
SSH is an encrypted connection protocol that allows secure sign-ins over unsecured connections. SSH is the default connection protocol for Linux VMs hosted in Azure. Although SSH itself provides an encrypted connection, using passwords with SSH still leaves the VM vulnerable to brute-force attacks. We recommend connecting to a VM over SSH using a public-private key pair, also known as SSH keys.
The public-private key pair is like the lock on your front door. The lock is exposed to the public, anyone with the right key can open the door. The key is private, and only given to people you trust because it can be used to unlock the door.
The public key is placed on your Linux VM when you create the VM.
The private key remains on your local system. Protect this private key. Don't share it.
When you connect to your Linux VM, the VM tests the SSH client to make sure it has the correct private key. If the client has the private key, it's granted access to the VM.
Depending on your organization's security policies, you can reuse a single key pair to access multiple Azure VMs and services. You don't need a separate pair of keys for each VM.
Your public key can be shared with anyone, but only you (or your local security infrastructure) should have access to your private key.
Supported SSH key formats
Azure currently supports following key types:
- SSH protocol 2 (SSH-2) RSA (Rivest, Shamir, Adleman) with a minimum length of 2048 bits
- ED25519 Keys with a fixed length of 256 bits
Other key formats such as Elliptic-curve Diffie-Hellman (ECDH) and Elliptic Curve Digital Signature Algorithm (ECDSA) are currently not supported.
SSH clients
Recent versions of Windows 10 include OpenSSH client commands to create and use SSH keys and make SSH connections from PowerShell or a command prompt.
You can also install the Windows Subsystem for Linux to connect to your VM over SSH and use other native Linux tools within a Bash shell.
Create an SSH key pair
The easiest way to create and manage your SSH keys is to use the portal to create and store them for reuse.
You can also create key pairs with the Azure CLI with the az sshkey create command, as described in Generate and store SSH keys.
To create an SSH key pair on your local computer using the ssh-keygen command from PowerShell or a command prompt, use the following command:
ssh-keygen -m PEM -t rsa -b 2048
Enter a filename, or use the default shown in parenthesis (for example C:\Users\username/.ssh/id_rsa). Enter a passphrase for the file, or leave the passphrase blank if you don't want to use a passphrase.
Create a VM using your key
To create a Linux VM that uses SSH keys for authentication, provide your SSH public key when creating the VM.
Using the Azure CLI, you specify the path and filename for the public key using az vm create and the --ssh-key-value parameter.
az vm create \
--resource-group myResourceGroup \
--name myVM \
--image Ubuntu2204\
--admin-username azureuser \
--ssh-key-value ~/.ssh/id_rsa.pub
With PowerShell, use New-AzVM and add the SSH key to the VM configuration using`. For an example, see Quickstart: Create a Linux virtual machine in Azure with PowerShell.
If you do many deployments using the portal, you might want to upload your public key to Azure, where it can be easily selected when creating a VM from the portal. For more information, see Upload an SSH key.
Connect to your VM
With the public key deployed on your Azure VM, and the private key on your local system, SSH to your VM using the IP address or DNS name of your VM. Replace azureuser and 10.111.12.123 in the following command with the administrator user name, the IP address (or fully qualified domain name), and the path to your private key:
ssh -i ~/.ssh/id_rsa azureuser@10.111.12.123
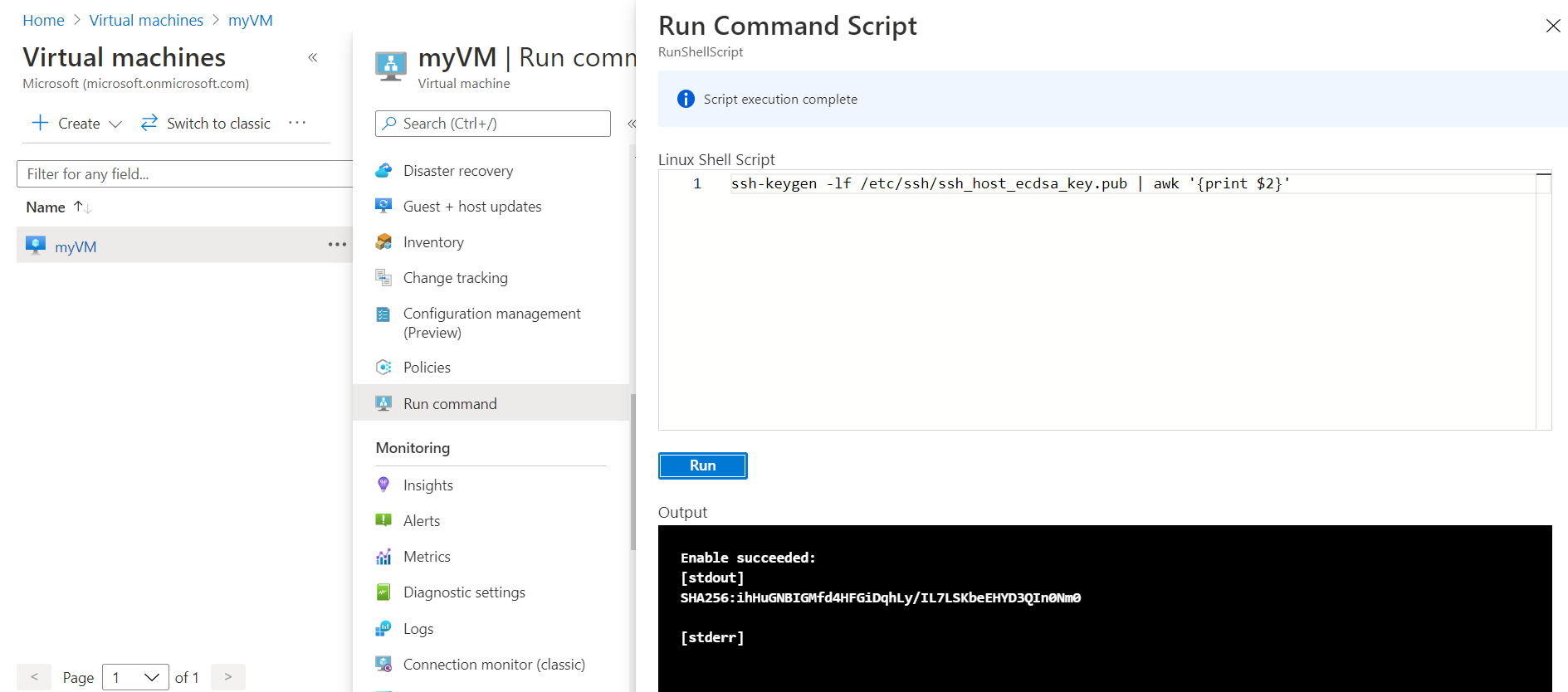
If you've never connected to this VM before you'll be asked to verify the hosts fingerprint. It's tempting to accept the fingerprint presented, however, this exposes you to a possible person in the middle attack. You should always validate the hosts fingerprint. You only need to do this on the first time you connect from a client. To obtain the host fingerprint via the portal, use the Run Command with the following command: ssh-keygen -lf /etc/ssh/ssh_host_ecdsa_key.pub | awk '{print $2}'.
To run the command using CLI, use the az vm run-command invoke command.
If you configured a passphrase when you created your key pair, enter the passphrase when prompted.
If the VM is using the just-in-time access policy, you need to request access before you can connect to the VM. For more information about the just-in-time policy, see Manage virtual machine access using the just in time policy.
Next steps
For information about SSH keys in the Azure portal to use when creating VMs, see Generate and store SSH keys in the Azure portal.
For information about SSH keys in the Azure CLI to use when creating VMs, see Generate and store SSH keys with the Azure CLI.
For detailed steps, options, and advanced examples of working with SSH keys, see Detailed steps to create SSH key pairs.
If you have difficulty using SSH to connect to your Linux VMs, see Troubleshoot SSH connections to an Azure Linux VM.