Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
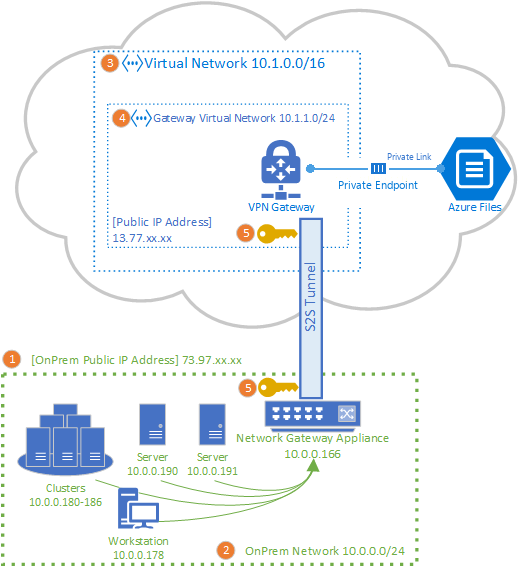
You can use a site-to-site VPN connection to mount your Azure file shares from your on-premises network, without sending data over the open internet. You can set up a site-to-site VPN using Azure VPN Gateway, which is an Azure resource offering VPN services. You deploy VPN Gateway in a resource group alongside storage accounts or other Azure resources.
We strongly recommend that you read Azure Files networking overview before continuing with this article for a complete discussion of the networking options available for Azure Files.
The article details the steps to configure a site-to-site VPN to mount Azure file shares directly on-premises. If you're looking to route sync traffic for Azure File Sync over a site-to-site VPN, see configuring Azure File Sync proxy and firewall settings.
Prerequisites
An Azure file share you would like to mount on-premises. Azure file shares are deployed within storage accounts, which are management constructs that represent a shared pool of storage in which you can deploy multiple file shares, as well as other storage resources, such as blobs or queues. You can learn more about how to deploy Azure file shares and storage accounts in Create an Azure file share.
A private endpoint for the storage account deployed in the virtual network you'll use for VPN Gateway. A private endpoint assigns the storage account a private IP address from within your virtual network address space, enabling on-premises clients to access Azure Files through the VPN tunnel. To learn how to create a private endpoint, see Configuring Azure Files network endpoints.
A network appliance or server in your on-premises data center that's compatible with Azure VPN Gateway. Azure Files is agnostic of the on-premises network appliance chosen, but Azure VPN Gateway maintains a list of tested devices. Different network appliances offer different features, performance characteristics, and management functionalities, so consider these when selecting a network appliance.
If you don't have an existing network appliance, Windows Server contains a built-in Server Role, Routing and Remote Access (RRAS), which can be used as the on-premises network appliance. To learn more about how to configure Routing and Remote Access in Windows Server, see RAS Gateway.
Configure virtual network and network access
To configure a new or existing virtual network and restrict storage account access, follow these steps.
Sign in to the Azure portal and navigate to the storage account containing the Azure file share you would like to mount on-premises.
In the service menu, under Security + networking, select Networking. Unless you added a virtual network to your storage account when you created it, the resulting pane should have the radio button for Enabled from all networks selected under Public network access.
To restrict storage account access to specific virtual networks, select the Enabled from selected virtual networks and IP addresses radio button. Under the Virtual networks subheading, select either + Add existing virtual network or + Add new virtual network. Creating a new virtual network will result in a new Azure resource being created. The new or existing virtual network resource must be in the same region as the storage account, but it doesn't need to be in the same resource group or subscription. However, keep in mind that the resource group, region, and subscription you deploy your virtual network into must match where you deploy your virtual network gateway in the next step.
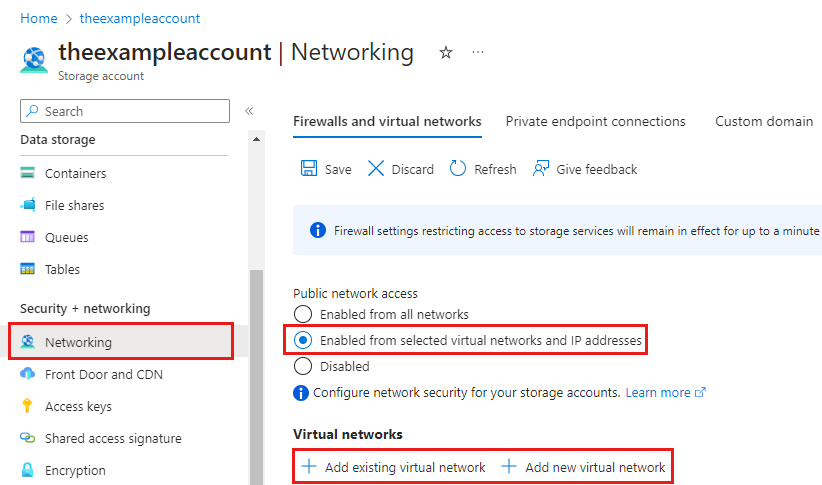
If you add an existing virtual network, you must first create a gateway subnet on the virtual network. You'll be asked to select one or more subnets of that virtual network. If you create a new virtual network, you'll create a subnet as part of the creation process. You can add more subnets later through the resulting Azure resource for the virtual network.
Select Save at the top of the page.
Create a private endpoint for the storage account
A private endpoint assigns your storage account a private IP address from within your virtual network's address space. When on-premises clients connected through the VPN tunnel resolve the storage account's fully qualified domain name (FQDN), the name resolves to the private IP address instead of the public IP, and traffic routes through the tunnel.
Without a private endpoint, storageaccount.file.core.chinacloudapi.cn resolves to the storage account's public IP address, and on-premises routing tables send traffic directly over the internet, bypassing the VPN tunnel entirely.
Navigate to the storage account in the Azure portal. In the service menu, under Security + networking, select Networking, and then select the Private endpoint connections tab.
Select + Private endpoint.
On the Basics tab, select the subscription, resource group, and region. Give the private endpoint a name.
On the Resource tab, select Microsoft.Storage/storageAccounts as the resource type. Select your storage account as the resource, and file as the target sub-resource.
On the Virtual Network tab, select the virtual network and subnet where you want to place the private endpoint. This should be a subnet within the virtual network you configured in the previous section (not the GatewaySubnet).
Select Yes for Integrate with private DNS zone. This creates a
privatelink.file.core.chinacloudapi.cnprivate DNS zone linked to your virtual network, which is required for the storage account's FQDN to resolve to the private IP address.Select Review + create, then Create.
Deploy a virtual network gateway
To deploy a virtual network gateway, follow these steps.
In the search box at the top of the Azure portal, search for and then select Virtual network gateways. The Virtual network gateways page should appear. At the top of the page, select + Create.
On the Basics tab, fill in the values for Project details and Instance details. Your virtual network gateway must be in the same subscription, Azure region, and resource group as the virtual network.
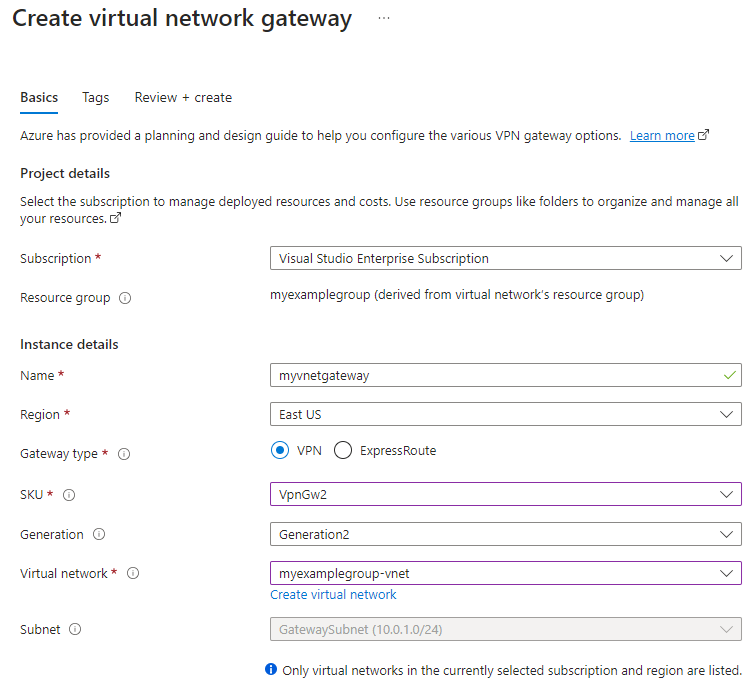
- Subscription: Select the subscription you want to use from the dropdown.
- Resource Group: This setting is autofilled when you select your virtual network on this page.
- Name: Name your virtual network gateway. Naming your gateway isn't the same as naming a gateway subnet. It's the name of the virtual network gateway object you're creating.
- Region: Select the region in which you want to create this resource. The region for the virtual network gateway must be the same as the virtual network.
- Gateway type: Select VPN. VPN gateways use the virtual network gateway type VPN.
- SKU: Select the gateway SKU that supports the features you want to use from the dropdown. The SKU controls the number of allowed Site-to-Site tunnels and desired performance of the VPN. See Gateway SKUs. Don't use the Basic SKU if you want to use IKEv2 authentication (route-based VPN).
- Generation: Select the generation you want to use. We recommend using a Generation2 SKU. For more information, see Gateway SKUs.
- Virtual network: From the dropdown, select the virtual network you configured in the previous step.
- Subnet: This field should be grayed out and list the name of the gateway subnet you created, along with its IP address range. If you instead see a Gateway subnet address range field with a text box, then you haven't yet configured a gateway subnet on the virtual network.
Specify the values for the Public IP address that gets associated to the virtual network gateway. The public IP address is assigned to this object when the virtual network gateway is created. The only time the primary public IP address changes is when the gateway is deleted and re-created. It doesn't change across resizing, resetting, or other internal maintenance/upgrades.
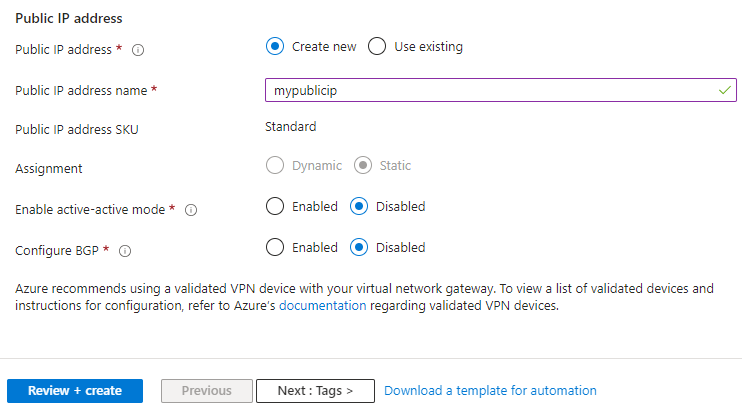
- Public IP address: The IP address of the virtual network gateway that will be exposed to the internet. Likely, you'll need to create a new IP address, however you may also use an existing unused IP address. If you select Create new, a new IP address Azure resource will be created in the same resource group as the virtual network gateway, and the Public IP address name will be the name of the newly created IP address. If you select Use existing, you must select the existing unused IP address.
- Public IP address name: In the text box, type a name for your public IP address instance.
- Public IP address SKU: Setting is autoselected.
- Assignment: The assignment is typically autoselected and can be either Dynamic or Static.
- Enable active-active mode: Select Disabled. Only enable this setting if you're creating an active-active gateway configuration. To learn more about active-active mode, see Highly available cross-premises and VNet-to-VNet connectivity.
- Configure BGP: Select Disabled, unless your configuration specifically requires Border Gateway Protocol. If you do require this setting, the default ASN is 65515, although this value can be changed. To learn more about this setting, see About BGP with Azure VPN Gateway.
Select Review + create to run validation. Once validation passes, select Create to deploy the virtual network gateway. Deployment can take up to 45 minutes to complete.
Create a local network gateway for your on-premises gateway
A local network gateway is an Azure resource that represents your on-premises network appliance. It's deployed alongside your storage account, virtual network, and virtual network gateway, but doesn't need to be in the same resource group or subscription as the storage account. To create a local network gateway, follow these steps.
In the search box at the top of the Azure portal, search for and select local network gateways. The Local network gateways page should appear. At the top of the page, select + Create.
On the Basics tab, fill in the values for Project details and Instance details.
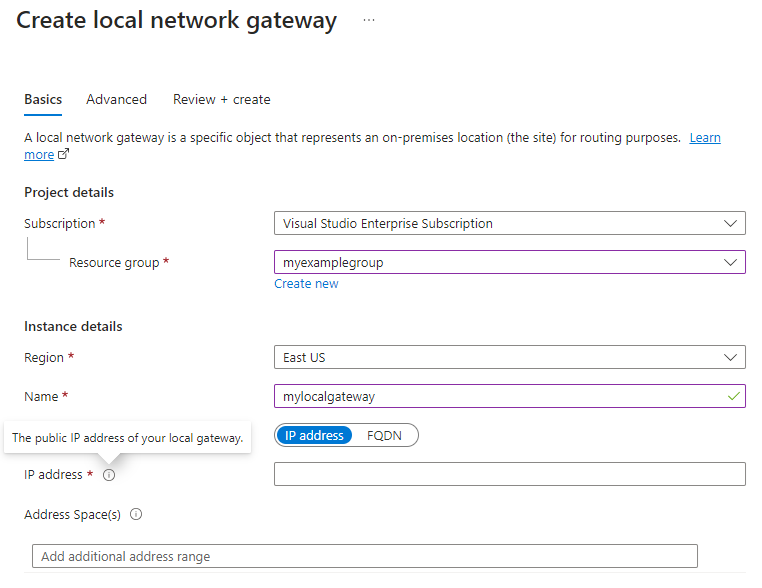
- Subscription: The desired Azure subscription. This doesn't need to match the subscription used for the virtual network gateway or the storage account.
- Resource group: The desired resource group. This doesn't need to match the resource group used for the virtual network gateway or the storage account.
- Region: The Azure region the local network gateway resource should be created in. This should match the region you selected for the virtual network gateway and the storage account.
- Name: The name of the Azure resource for the local network gateway. This name may be any name you find useful for your management.
- Endpoint: Leave IP address selected.
- IP address: The public IP address of your local gateway on-premises.
- Address space: The address range or ranges for the network this local network gateway represents. For example: 192.168.0.0/16. If you add multiple address space ranges, make sure that the ranges you specify don't overlap with ranges of other networks that you want to connect to. If you plan to use this local network gateway in a BGP-enabled connection, then the minimum prefix you need to declare is the host address of your BGP Peer IP address on your VPN device.
If your organization requires BGP, select the Advanced tab to configure BGP settings. To learn more, see About BGP with Azure VPN Gateway.
Select Review + create to run validation. Once validation passes, select Create to create the local network gateway.
Configure on-premises network appliance
The specific steps to configure your on-premises network appliance depend on the network appliance your organization has selected.
When configuring your network appliance, you'll need the following items:
A shared key. This is the same shared key that you specify when creating your site-to-site VPN connection. In our examples, we use a basic shared key such as 'abc123'. We recommend that you generate a more complex key to use that complies with your organization's security requirements.
The public IP address of your virtual network gateway. To find the public IP address of your virtual network gateway using PowerShell, run the following command. In this example,
mypublicipis the name of the public IP address resource that you created in an earlier step.Get-AzPublicIpAddress -Name mypublicip -ResourceGroupName <resource-group>
Depending on the VPN device that you have, you might be able to download a VPN device configuration script. For more information, see Download VPN device configuration scripts.
The following links provide more configuration information:
For information about compatible VPN devices, see About VPN devices.
For links to device configuration settings, see Validated VPN devices. We provide the device configuration links on a best-effort basis, but it's always best to check with your device manufacturer for the latest configuration information.
The list shows the versions that we tested. If the OS version for your VPN device isn't on the list, it still might be compatible. Check with your device manufacturer.
For basic information about VPN device configuration, see Overview of partner VPN device configurations.
For information about editing device configuration samples, see Editing samples.
For cryptographic requirements, see About cryptographic requirements and Azure VPN gateways.
For information about parameters that you need to complete your configuration, see Default IPsec/IKE parameters. The information includes IKE version, Diffie-Hellman (DH) group, authentication method, encryption and hashing algorithms, security association (SA) lifetime, perfect forward secrecy (PFS), and Dead Peer Detection (DPD).
For IPsec/IKE policy configuration steps, see Configure custom IPsec/IKE connection policies for S2S VPN and VNet-to-VNet.
To connect multiple policy-based VPN devices, see Connect a VPN gateway to multiple on-premises policy-based VPN devices.
Create the site-to-site connection
To complete the deployment of a site-to-site VPN, you must create a connection between your on-premises network appliance (represented by the local network gateway resource) and the Azure virtual network gateway. To do this, follow these steps.
Navigate to the virtual network gateway you created. In the table of contents for the virtual network gateway, select Settings > Connections, and then select + Add.
On the Basics tab, fill in the values for Project details and Instance details.
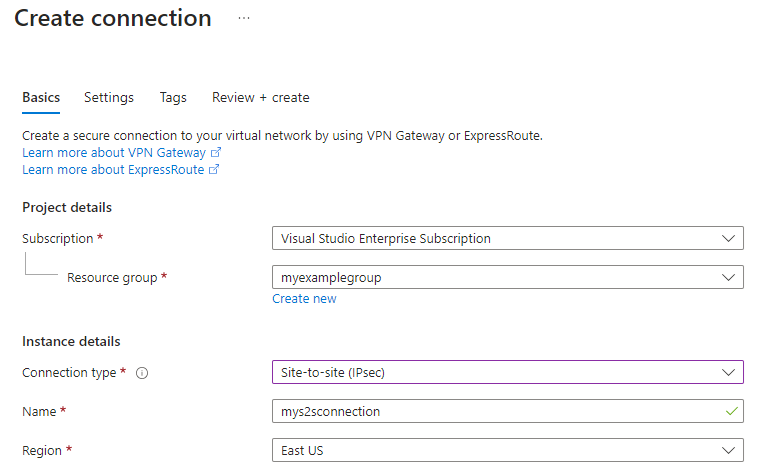
- Subscription: The desired Azure subscription.
- Resource group: The desired resource group.
- Connection type: Because this a site-to-site connection, select Site-to-site (IPsec) from the drop-down list.
- Name: The name of the connection. A virtual network gateway can host multiple connections, so choose a name that's helpful for your management and that will distinguish this particular connection.
- Region: The region you selected for the virtual network gateway and the storage account.
On the Settings tab, supply the following information.
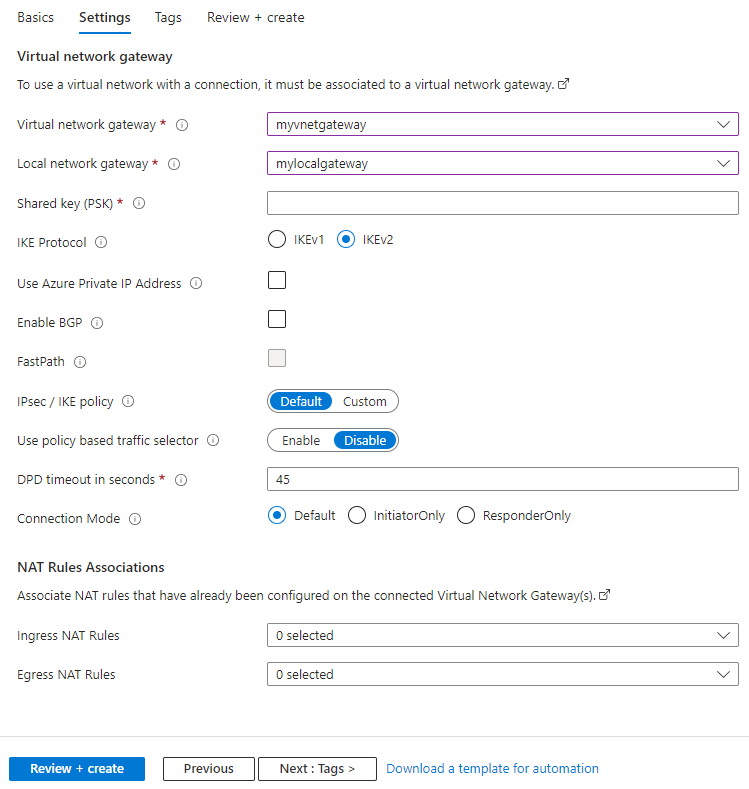
- Virtual network gateway: Select the virtual network gateway you created.
- Local network gateway: Select the local network gateway you created.
- Shared key (PSK): A mixture of letters and numbers used to establish encryption for the connection. The same shared key must be used in both the virtual network and local network gateways. If your gateway device doesn't provide one, you can make one up here and provide it to your device.
- IKE protocol: Depending on your VPN device, select IKEv1 for policy-based VPN or IKEv2 for route-based VPN. To learn more about the two types of VPN gateways, see About policy-based and route-based VPN gateways.
- Use Azure Private IP Address: Checking this option allows you to use Azure private IPs to establish an IPsec VPN connection. Support for private IPs must be set on the VPN gateway for this option to work. It's only supported on AZ Gateway SKUs.
- Enable BGP: Leave unchecked unless your organization specifically requires this setting.
- Enable Custom BGP Addresses: Leave unchecked unless your organization specifically requires this setting.
- FastPath: FastPath is designed to improve the datapath performance between your on-premises network and your virtual network. Learn more.
- IPsec / IKE policy: The IPsec / IKE policy that will be negotiated for the connection. Leave Default selected unless your organization requires a custom policy. Learn more.
- Use policy based traffic selector: Leave disabled unless you need to configure the Azure VPN gateway to connect to a policy-based VPN firewall on premises. If you enable this field, you must ensure your VPN device has the matching traffic selectors defined with all combinations of your on-premises network (local network gateway) prefixes to/from the Azure virtual network prefixes, instead of any-to-any. For example, if your on-premises network prefixes are 10.1.0.0/16 and 10.2.0.0/16, and your virtual network prefixes are 192.168.0.0/16 and 172.16.0.0/16, you would need to specify the following traffic selectors:
- 10.1.0.0/16 <====> 192.168.0.0/16
- 10.1.0.0/16 <====> 172.16.0.0/16
- 10.2.0.0/16 <====> 192.168.0.0/16
- 10.2.0.0/16 <====> 172.16.0.0/16
- DPD timeout in seconds: Dead Peer Detection Timeout of the connection in seconds. The recommended and default value for this property is 45 seconds.
- Connection mode: Connection mode is used to decide which gateway can initiate the connection. When this value is set to:
- Default: Both Azure and the on-premises VPN gateway can initiate the connection.
- ResponderOnly: Azure VPN gateway will never initiate the connection. The on-premises VPN gateway must initiate the connection.
- InitiatorOnly: Azure VPN gateway will initiate the connection and reject any connection attempts from the on-premises VPN gateway.
Select Review + create to run validation. Once validation passes, select Create to create the connection. You can verify the connection has been made successfully through the virtual network gateway's Connections page.
Configure DNS forwarding for on-premises access
For on-premises clients to access Azure file shares through the VPN tunnel, DNS must resolve the storage account's FQDN (for example, storageaccount.file.core.chinacloudapi.cn) to the private endpoint's private IP address. Without DNS forwarding, on-premises DNS resolves the FQDN to the storage account's public IP address, and traffic routes over the internet instead of the VPN tunnel.
Option 1: Azure DNS Private Resolver (recommended)
Deploy an Azure DNS Private Resolver in your virtual network. Configure your on-premises DNS servers to conditionally forward queries for file.core.chinacloudapi.cn to the Private Resolver's inbound endpoint IP address. The Private Resolver can resolve names against the privatelink.file.core.chinacloudapi.cn private DNS zone that was linked to your virtual network when you created the private endpoint.
Option 2: DNS forwarder virtual machines
Deploy one or more DNS forwarder VMs in your virtual network that forward queries to the Azure recursive resolver at 168.63.129.16. Configure your on-premises DNS servers to conditionally forward queries for file.core.chinacloudapi.cn to the IP addresses of these forwarder VMs.
For detailed instructions on both approaches, see Configuring DNS forwarding for Azure Files.
Verify DNS resolution from on-premises
Before mounting your file share, verify that DNS resolution is working correctly from an on-premises machine connected to the VPN. The FQDN should resolve to a private IP address from your virtual network's address space.
Windows (PowerShell):
Resolve-DnsName -Name storageaccount.file.core.chinacloudapi.cn
Linux/macOS:
nslookup storageaccount.file.core.chinacloudapi.cn
If the result returns a public IP address instead of a private IP (for example, 10.0.x.x), your DNS forwarding isn't configured correctly and the mount traffic won't traverse the VPN tunnel.
Mount Azure file share
Before mounting, confirm that DNS resolution returns the private endpoint's private IP address (see previous section). If DNS resolution returns a public IP, the mount traffic will bypass the VPN tunnel.
Once DNS resolution is confirmed, mount your Azure file share on-premises. See the instructions to mount by OS: