Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Applies to: Azure Logic Apps (Consumption + Standard)
To extend your workflows with custom code that performs advanced computations or processes dynamic data, create and call functions in Azure Functions from workflows in Azure Logic Apps. When you create functions in Azure Functions, you can complete tasks like the following:
- Run functions created by using C# or Node.js.
- Perform advanced calculations in your workflow.
- Apply advanced formatting or compute fields in your workflow.
This guide shows how to call and run a function in Azure Functions from your Consumption or Standard workflow in Azure Logic Apps. You also learn about the prerequisites, limitations, and tips for working with Azure Functions to ensure seamless integration and optimal performance.
Tip
To run code without using Azure Functions, see:
For more information, see:
Limitations
For Azure Functions to operate correctly in your workflow, review the following limitations:
Function app resources must use either the .NET or Node.js runtime stack.
Functions must be written in either C# or JavaScript code.
Functions must use the HTTP trigger template.
The HTTP trigger template can accept and handle content with the
application/jsontype as input from your workflow. When you add an Azure function to your workflow, the workflow designer shows any available custom functions created with this template in your Azure subscription.For Azure function call authentication, only Consumption workflows support managed identity authentication with Microsoft Entra ID. For more information, see how to enable authentication for Azure function calls.
Standard workflows don't support managed identity authentication.
Azure Logic Apps doesn't support using Azure Functions with deployment slots enabled.
Although this scenario might sometimes work, this behavior is unpredictable and might result in authorization problems when your workflow tries to call the Azure function.
Prerequisites
An Azure account and subscription. Get a Azure account.
An Azure function app resource, which can contain one or more Azure functions.
Make sure that your function app resource and logic app resource exist in the same Azure subscription.
The Azure function to call from your workflow.
To create this function, use any of the following tools:
Your function code must include the response and payload that you want returned to your workflow after the function completes.
This guide uses the following sample function named FabrikamAzureFunction. The
contextobject in this sample function refers to the message that your workflow sends through the Azure Functions action parameter named Request Body and is later explained in this guide:module.exports = function (context, data) { var input = data; // Function processing logic // Function response for later use context.res = { body: { content:"Thank you for your feedback: " + input } }; context.done(); }To access the
contextobject's properties from inside your function, use the following syntax:context.body.<property-name>For example, to reference the
contentproperty in thecontextobject, use this code:context.body.contentThis code also includes an
inputvariable, which stores the value from thedataparameter so that your function can perform operations on that value. Inside JavaScript functions, thedatavariable is also a shortcut forcontext.body.Note
The
bodyproperty mentioned here applies to thecontextobject and differs from the Body value in an action's output, which you might also pass to your function.
A Consumption or Standard logic app workflow that starts with any trigger.
The examples in this guide use the Office 365 Outlook trigger named When a new email arrives.
To create and call an Azure function that calls another workflow, make sure that secondary workflow starts with a trigger that provides a callable endpoint.
For example, you can start the workflow with the general HTTP or Request trigger, or you can use a service-based trigger, such as Azure Queues or Event Grid. Inside your function, send an HTTP POST request to the trigger's URL and include the payload that you want your secondary workflow to process. For more information, see Call, trigger, or nest logic app workflows.
Tips for working with Azure Functions
Find functions with OpenAPI definitions
To set up your function app so that your workflow can find and use functions that have OpenAPI definitions, follow these steps:
In the Azure portal, open your function app. Make sure that the function app is actively running.
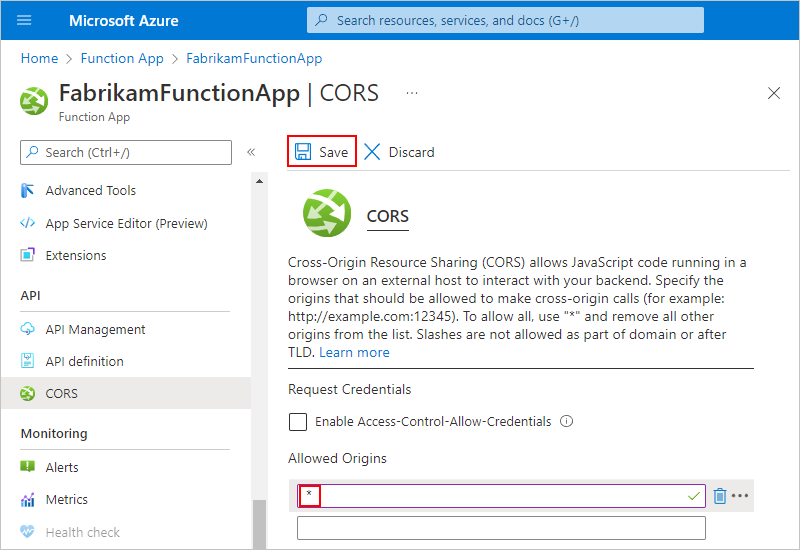
On your function app, set up Cross-Origin Resource Sharing (CORS) so that all origins are permitted by following these steps:
Access the property values in HTTPS requests
Webhook-based functions can accept HTTPS requests as inputs and pass these requests to other functions.
For example, although Azure Logic Apps has functions that convert DateTime values, you can access a property in a request object that passes to the function and perform operations on that property value.
This basic sample JavaScript function uses the dot (.) operator to access properties in objects:
function convertToDateString(request, response){
var data = request.body;
response = {
body: data.date.ToDateString();
}
}
The following steps describe what happens in this function:
The function creates a
datavariable and assigns thebodyobject, which is in therequestobject, to the variable. To reference thebodyobject in therequestobject, the function uses the dot (.) operator:var data = request.body;The function can now access the
dateproperty through thedatavariable.The function converts the property value from DateTime type to DateString type by calling the
ToDateString()function. The function returns the result through thebodyproperty in the function's response:body: data.date.ToDateString();After you create your function in Azure Functions, follow the steps to add an Azure function to your workflow.
Pass URI parameters to a function
To pass a URI parameter to your function, use query parameters in the function's endpoint URL.
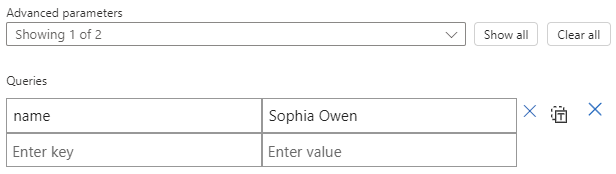
In the workflow designer with the function information pane open, from the Advanced parameters list, select Queries.
A table appears where you can enter parameter input as key-value pairs.
Enter the key-value pair for your parameter, for example:
Add a function to your workflow (Consumption + Standard workflows)
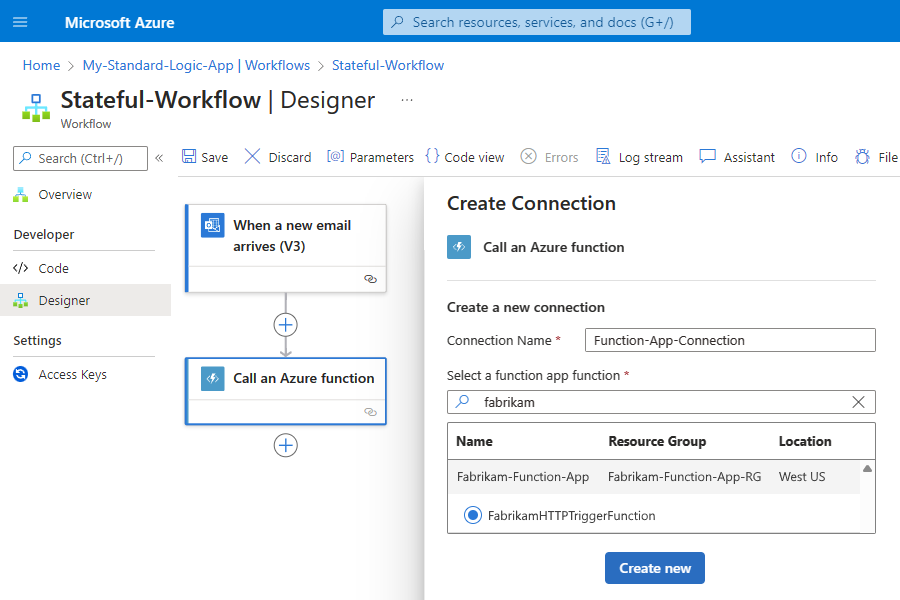
To call an Azure function from your workflow, add that function like any other action in the workflow designer.
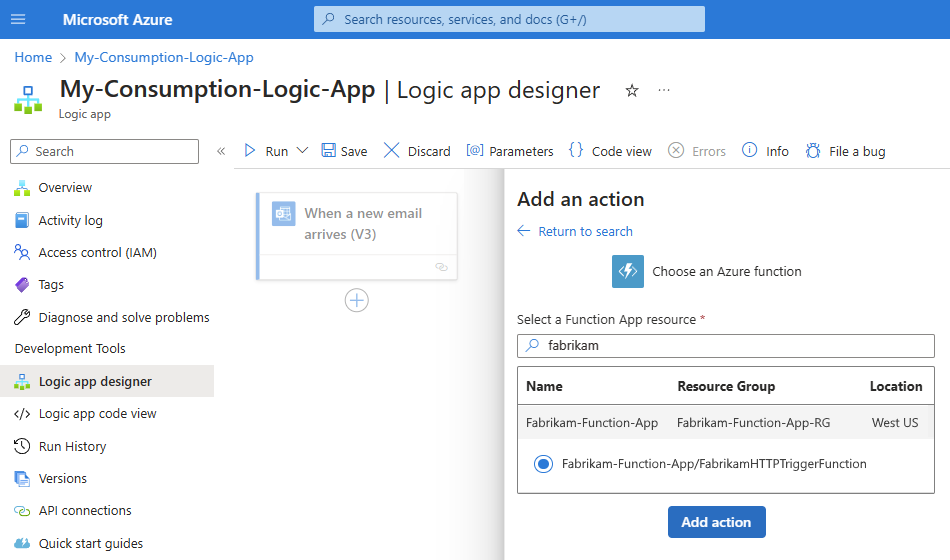
In the Azure portal, open your Consumption logic app resource. Open the workflow in the designer.
In the designer, follow the general steps to add the Azure Functions action named Choose an Azure function.
In the Add an action pane, follow these steps:
From the function apps list, select your function app.
Select the function, and then select Add action, for example:
After the function's information box appears, follow these steps:
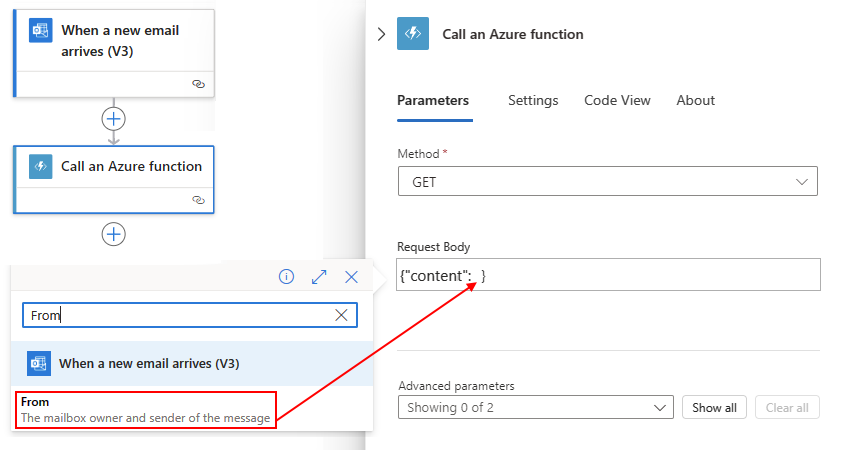
For Request Body, enter your function's input, which must use the format for a JavaScript Object Notation (JSON) object, for example:
{"context": <selected-input> }This input is the context object payload or message that your workflow sends to your function.
To select output values from previous steps in the workflow, select inside the Request Body box, and then select the option that opens the dynamic content list (lightning icon).
To create an expression, select inside the Request Body box, and then select the option that opens the expression editor (function icon).
The following example specifies a JSON object with the
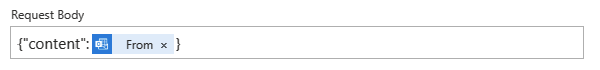
contentattribute and the From output value from the email trigger as the Request Body value: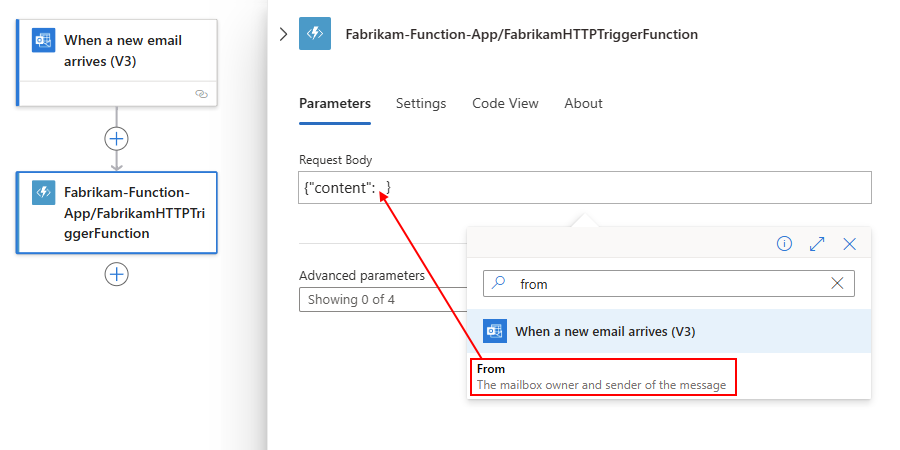
In this case, the context object isn't cast as a string. The object's content is directly added to the JSON payload. The following image shows the finished example:
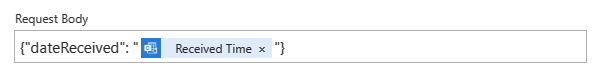
If you enter a context object other than a JSON token that passes a string, a JSON object, or a JSON array, you receive an error. However, you can cast the context object as a string by enclosing the token in quotation marks (" "). For example, if you wanted to use the Received Time output value:
To enter other information such as the method to use, request headers, query parameters, or authentication, open the Advanced parameters list, and select the parameters you want.
For authentication, your options differ based on your selected function. For more information, see Enable authentication for functions.
Enable authentication for Azure function calls (Consumption workflows only)
Your Consumption workflow can use a manually created, user-assigned managed identity to authenticate the call to the Azure function and access resources protected by Microsoft Entra ID. A managed identity authenticates access without requiring you to sign in and provide credentials or secrets. Azure manages this identity for you and helps keep your credentials secure because you don't have to manage credentials or rotate secrets.
For this scenario, you need to set up a user-assigned managed identity at the logic app resource level. The call that your workflow makes to the Azure function uses this managed identity for authentication.
For more information, see:
To set up your function app and function so they use the managed identity for your Consumption logic app resource, follow these high-level steps:
Enable and set up the managed identity for your logic app resource.
Find the required values to set up Microsoft Entra authentication.
Set up your function for anonymous authentication (Consumption workflows only)
For your function to use the managed identity for your Consumption logic app resource, set your function's authentication level to anonymous. Otherwise, your workflow throws a BadRequest error.
In the Azure portal, open your function app.
The following steps use an example function app named FabrikamFunctionApp.
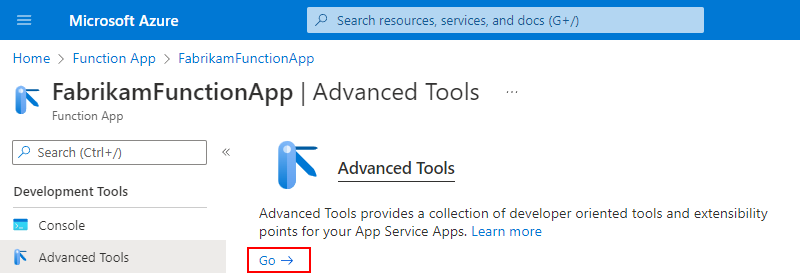
On the function app sidebar, under Development Tools, select Advanced Tools > Go.
To confirm that you want to leave the Azure portal and go to the website URL for your function app, select Continue.
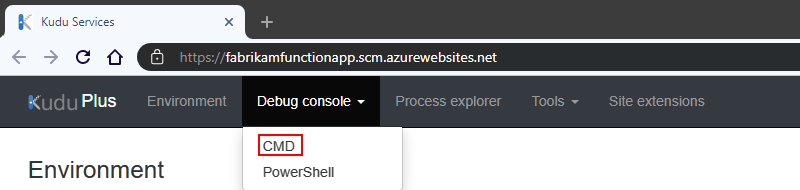
After the Kudu Services page opens, on the Kudu website's title bar, from the Debug console menu, select CMD.
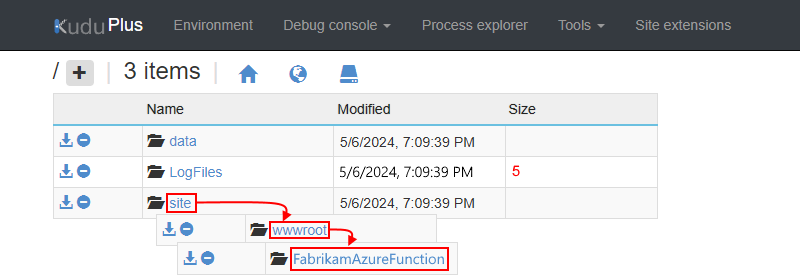
On the next page, from the folder list, select site > wwwroot > your-function.
The following steps use an example function named FabrikamAzureFunction.
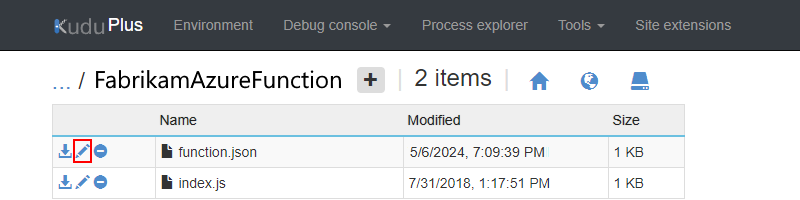
Open the function.json file for editing.
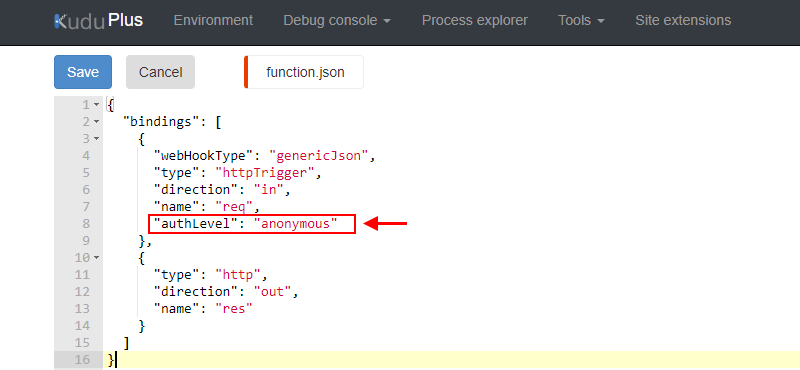
In the
bindingsobject, confirm whether theauthLevelproperty exists.If the property exists, set the property value to
anonymous. Otherwise, add the property, and set the value.When you finish, on the editor toolbar, select Save. Continue to the next section.
Find the required values to set up Microsoft Entra authentication (Consumption workflows only)
Before you can set up your function app to use the managed identity and Microsoft Entra authentication, you need to find and save specific IDs by following these high-level steps:
Find the tenant ID for your Microsoft Entra tenant
Either run the PowerShell command named Get-AzContext, or in the Azure portal, follow these steps:
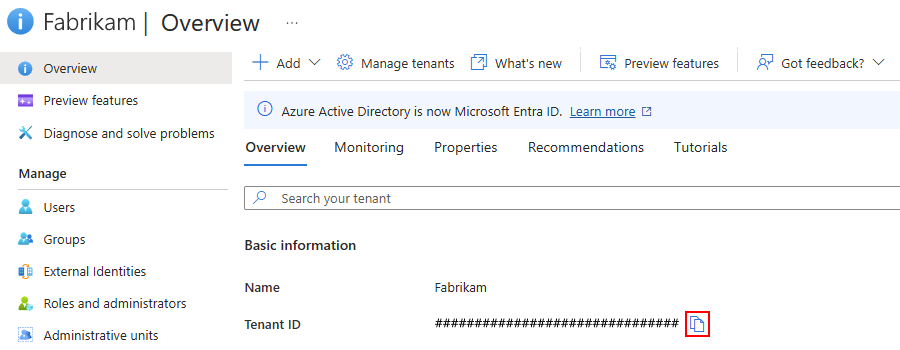
In the Azure portal, open your Microsoft Entra tenant.
This guide uses Fabrikam as the example tenant.
On the tenant sidebar, select Overview.
Copy and save your tenant ID for later use, for example:
Find the object ID for your managed identity
After you set up the user-assigned managed identity for your Consumption logic app resource, find the object ID for the managed identity. You use this ID to find the associated Enterprise application in your Microsoft Entra tenant.
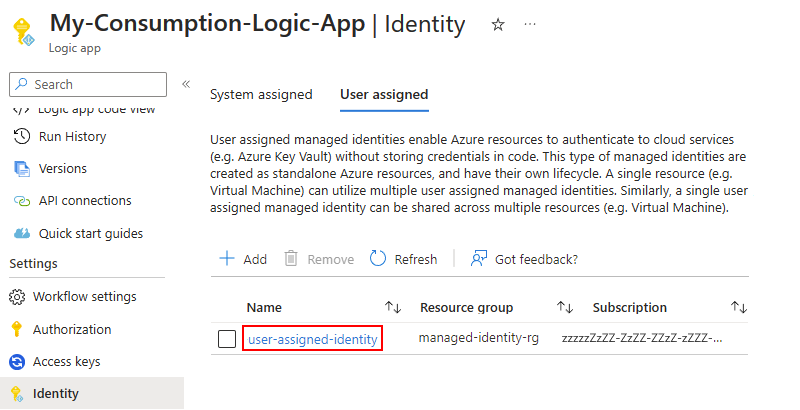
On the logic app sidebar, expand Settings, select Identity, and then select the User assigned tab.
On the User assigned tab, select the managed identity:
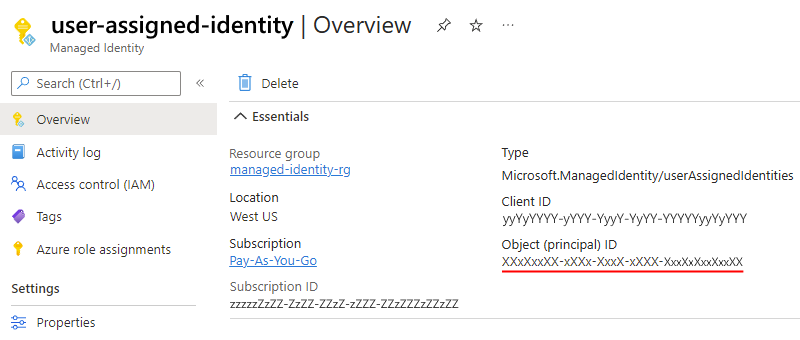
On the Managed Identity page, copy the identity's Object (principal) ID value:
Find the application ID for the Azure Enterprise application associated with your managed identity
After you enable the managed identity for your Consumption logic app resource, Azure automatically creates an associated Azure Enterprise application that has the same name.
You need to find the associated Enterprise application and copy its Application ID. You use this application ID to add an identity provider for your function app by creating an app registration. Follow these steps:
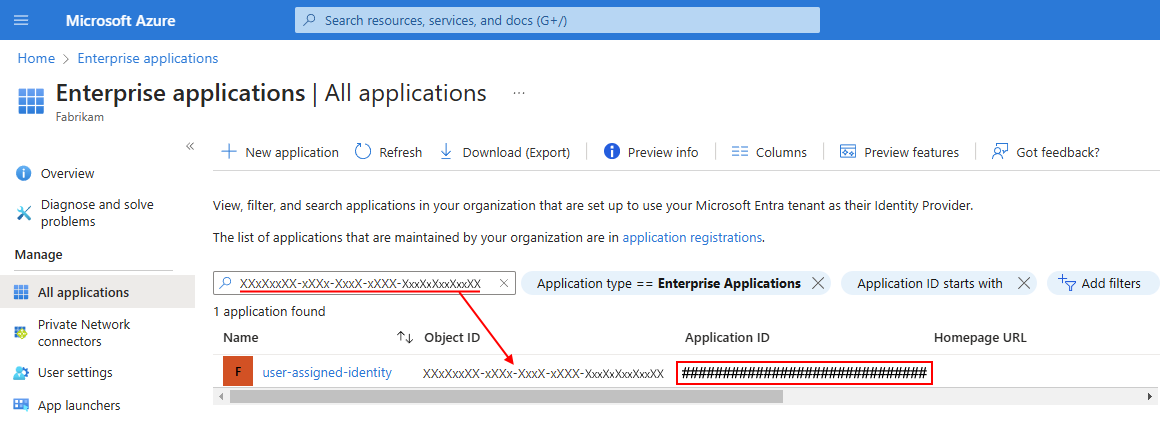
In the Azure portal, open your Microsoft Entra tenant.
On the tenant sidebar, expand Manage, and then select Enterprise applications.
On the All applications page, in the search box, enter the object ID for your managed identity. From the results, find the matching enterprise application, and copy the Application ID value:
Continue to the next section to add an identity provider to your function app by using the copied application ID value.
Add an identity provider for your function app (Consumption workflows only)
After you get the tenant ID and the application ID, set up your function app to use Microsoft Entra authentication by adding an identity provider and creating an app registration:
In the Azure portal, open your function app.
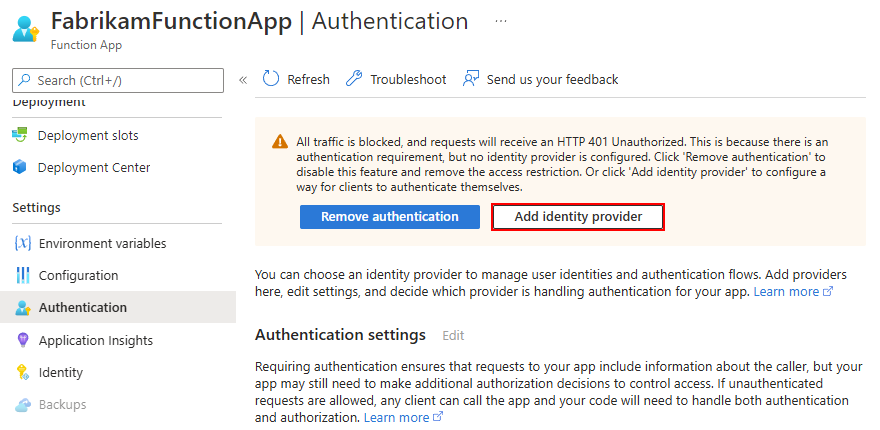
On the function app sidebar, expand Settings, select Authentication, and then select Add identity provider, for example:
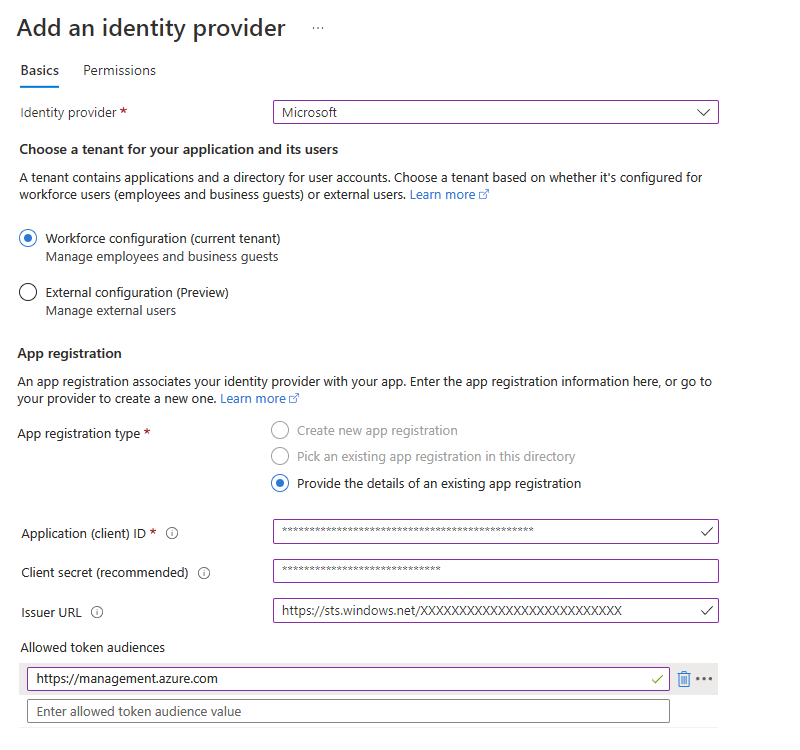
On the Add an identity provider page, on the Basics tab, from the Identity provider list, select Microsoft.
Under App registration, for App registration type, select Provide the details of an existing app registration, and enter the values that you previously saved where described in the following table:
Parameter Required Value Description Application (client) ID Yes <application-ID> The unique identifier to use for this app registration. For this example, use the application ID that you copied for the Enterprise application associated with your managed identity. Issuer URL No <authentication-endpoint-URL>/<Microsoft-Entra-tenant-ID>/v2.0 This URL redirects users to the correct Microsoft Entra tenant and downloads the appropriate metadata to determine the appropriate token signing keys and token issuer claim value. For apps that use Azure AD v1, omit /v2.0 from the URL.
For this scenario, use the following URL:https://sts.chinacloudapi.cn/<Microsoft-Entra-tenant-ID>Allowed token audiences No <application-ID-URI> The application ID URI (resource ID) for the function app. For a cloud or server app where you want to allow authentication tokens from a web app, add the application ID URI for the web app. The configured client ID is always implicitly considered as an allowed audience.
For this scenario, the value is the following URI:https://management.chinacloudapi.cn
Later, use the same URI in the Audience property when you set up your function action in your workflow to use the managed identity.
Important: The application ID URI (resource ID) must exactly match the value that Microsoft Entra ID expects, including any required trailing slashes.Your version now looks like the following example:
If you're setting up your function app with an identity provider for the first time, the App Service authentication settings section also appears. These options determine how your function app responds to unauthenticated requests. The default selection redirects all requests to sign in with the new identity provider. You can customize this behavior now or adjust these settings later from the main Authentication page by selecting Edit next to Authentication settings. To learn more about these options, see Authentication flow - Authentication and authorization in Azure App Service and Azure Functions.
Otherwise, continue with the next step.
To finish creating the app registration, select Add.
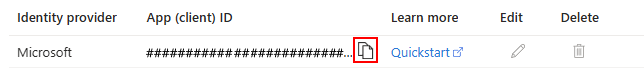
The Authentication page lists the identity provider and the app registration's application (client) ID. Your function app can now use this app registration for authentication.
Copy and save the app registration's App (client) ID value.
You use this ID in the Azure Functions action that you add to your workflow.
Return to the workflow designer, and follow the steps to authenticate access with the managed identity by using the Azure Functions action.
Remember to enter the application (client) ID in the function action's Audience property.