Azure Monitor使用Azure管理的密钥加密数据。 可以使用自己的加密密钥来保护工作区中的数据。 通过在Azure Monitor中使用客户管理的密钥,可以控制加密密钥生命周期并访问日志。 设置客户管理的密钥后,摄入到链接工作区的新数据将使用 Azure 密钥保管库 或 Azure 密钥保管库 托管 HSM(硬件安全模块)中的密钥进行加密。
客户管理的密钥概述
静态数据加密是组织中常见的隐私和安全要求。 可以让Azure完全管理静态加密,或使用各种选项来密切管理加密和加密密钥。
Azure Monitor 确保使用 Azure 托管密钥(MMK)对所有数据和保存的查询进行静态加密。 Azure Monitor加密的使用与Azure 存储加密运行的方式相同。
若要控制密钥生命周期并撤销对数据的访问,请在 Azure 密钥保管库 或 Azure 密钥保管库 托管 HSM 中使用自己的密钥加密数据。 客户管理的密钥功能在 专用群集 上可用,并提供更高级别的保护和控制。
引入到专用群集的数据加密两次 - 使用Azure托管密钥或客户管理的密钥,在基础结构级别使用两种不同的加密算法和两个不同的密钥。 双重加密可以在其中一种加密算法或密钥被泄露的情况下提供保护。
过去 14 天内引入的数据或最近在查询中使用的数据保存在热缓存(受 SSD 支持)中,以提高查询效率。 无论是否配置客户管理的密钥,Azure Monitor都使用Azure管理的基础结构密钥加密热缓存数据。 对热缓存数据的访问仍受客户管理的密钥状态的约束。 如果 撤销对密钥的访问权限,系统会删除热缓存数据,并且无法访问它。
重要
专用群集使用承诺层级定价模型,该模型至少为 100 GB/天。
Azure Monitor中客户管理密钥的工作原理
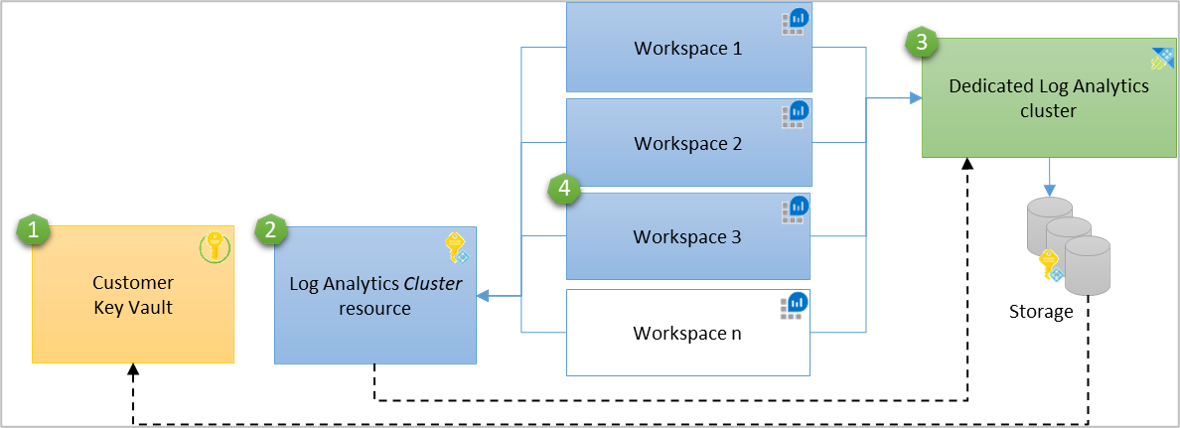
Azure Monitor 使用托管标识向 Azure 密钥保管库 中的密钥授予访问权限。 群集级别支持 Log Analytics 群集的身份功能。 若要在多个工作区上提供客户管理的密钥,Log Analytics专用群集资源充当密钥保管库与Log Analytics工作区之间的中间标识连接。 群集的存储使用与群集关联的托管标识通过Microsoft Entra ID向Azure 密钥保管库进行身份验证。
群集支持两种 托管标识类型:系统分配和用户分配。
- 当设置为
identitytypeSystemAssigned时,系统分配的托管标识更简单,并在群集中自动生成。 使用此标识授予对 密钥保管库 的群集存储访问权限,以便进行数据加密和解密。 - 用户分配的托管标识允许在群集创建时配置客户管理的密钥,将
identitytype设置为UserAssigned,并在创建群集之前在密钥保管库授予它权限。
在新群集上或具有链接的数据引入工作区的现有专用群集上配置客户管理的密钥。 您可以随时将工作区从集群中解除链接。 引入到链接工作区的新数据使用密钥进行加密,旧数据仍使用Azure管理的密钥进行加密。 配置不会中断引入或查询,查询可以无缝地跨新旧数据执行。 从群集取消链接工作区时,引入的新数据会使用Azure管理的密钥进行加密。
重要
客户管理的密钥功能是区域性的。 Azure 密钥保管库、专用群集和链接工作区必须位于同一区域,但它们可以位于不同的订阅中。
- 密钥保管库
- 具有 密钥保管库 权限的托管标识的日志分析集群资源——该标识将传播到基础专用集群存储中。
- 专用群集
- 连接到专用群集的工作区
加密密钥类型
存储数据加密使用三种类型的密钥:
- KEK - 密钥加密密钥(客户管理的密钥)
- AEK - 帐户加密密钥
- DEK - 数据加密密钥
下列规则适用:
- 群集存储为每个存储帐户都有唯一的加密密钥,称为 AEK。
- AEK 生成 DEKs,这是加密写入磁盘的每个数据块的密钥。
- 在群集中配置客户管理的 KEK 时,群集存储会向 密钥保管库 发送
wrap和unwrap请求进行 AEK 加密和解密。 - KEK永远不会离开密钥保管库。 如果将密钥存储在Azure 密钥保管库托管 HSM 中,则永远不会离开该硬件。
- Azure 存储使用与群集关联的托管标识进行身份验证。 它通过 Microsoft Entra ID 访问 Azure 密钥保管库。
操作密钥保护
Log Analytics专用群集使用的加密模型遵循 envelope 加密原则。 存储在 Azure 密钥保管库 或托管 HSM 中的客户管理的密钥保护群集使用的服务级别加密密钥(AEK)。 这些服务级别密钥不会保留在群集本身的存储中。
在正常操作期间,专用集群存储会在服务运行时内存中缓存 AEK,用于活动密码操作,并定期联系 密钥保管库 以更新密钥。 以下措施保护缓存的操作密钥:
- Managed identity authentication - 群集的 managed identity 控制对密钥保管库的访问,确保只有授权群集才能访问密钥。
- Azure平台计算隔离 - 专用群集在Azure计算基础结构上运行,该基础结构提供虚拟机监控程序强制的租户隔离、主机级内存保护、操作系统级进程隔离和虚拟机边界执行。 有关Azure平台隔离的详细信息,请参阅 Azure 公有云中的 Isolation。
- 加密的基础结构存储 - 在基础结构级别使用平台管理的密钥进行双重加密可保护群集上的数据。
暂时性操作缓存是一种可用性机制。 它允许群集在临时密钥保管库连接中断(例如暂时性网络错误或 DNS 故障)期间继续引入和查询操作。 操作密钥缓存不会替换或削弱客户管理的密钥在密钥保管库中提供的保护。 对加密数据(包括 热缓存)的访问仍受 CMK 状态控制。 如果 撤销对密钥的访问权限,加密的数据将无法访问该服务。
所需的权限
若要执行为专用群集预配和管理客户管理的密钥所需的群集相关作,需要以下权限:
| 行动 | 所需的权限或角色 |
|---|---|
| 创建专用群集 |
Microsoft.Resources/deployments/* 和 Microsoft.OperationalInsights/clusters/write 权限例如,由Log Analytics 参与者内置角色提供的功能 |
| 更改群集属性 |
Microsoft.OperationalInsights/clusters/write 权限,例如由“Log Analytics Contributor”内置角色提供 |
| 将工作区链接到群集 |
Microsoft.OperationalInsights/clusters/write、Microsoft.OperationalInsights/workspaces/write 和 Microsoft.OperationalInsights/workspaces/linkedservices/write 权限,例如由Log Analytics 参与者内置角色提供的权限为例 |
| 检查工作区链接状态 |
Microsoft.OperationalInsights/workspaces/read访问工作区的权限,例如,内置角色中的Log Analytics读取者 |
| 获取群集或检查群集的预配状态 |
Microsoft.OperationalInsights/clusters/read 权限,例如由 日志分析读取者内置角色 提供的权限 |
| 更新群集中的承诺层级或计费类型 |
Microsoft.OperationalInsights/clusters/write 权限,例如由“Log Analytics Contributor”内置角色提供 |
| 授予所需权限 | 具有*/write权限的所有者或贡献者角色,或者具有权限的Microsoft.OperationalInsights/* |
| 解除群集与工作区的关联 |
Microsoft.OperationalInsights/workspaces/linkedServices/delete 权限,例如由“Log Analytics Contributor”内置角色提供 |
| 删除专用群集 |
Microsoft.OperationalInsights/clusters/delete 权限,例如由“Log Analytics Contributor”内置角色提供 |
客户管理的密钥预配步骤
按照以下步骤在专用群集上配置客户管理的密钥:
- 创建或分配 Azure 密钥保管库 KEK (存储密钥)
- 将专用群集的托管标识类型与 密钥保管库 访问进行匹配
- 授予托管标识密钥保管库的权限
- 使用密钥标识符详细信息更新专用群集
- 验证专用群集预配
- 将工作区链接到专用群集
创建或分配 Azure 密钥保管库 KEK (存储密钥)
Azure密钥管理产品的 portfolio列出了可以使用的保管库和托管 HSM。
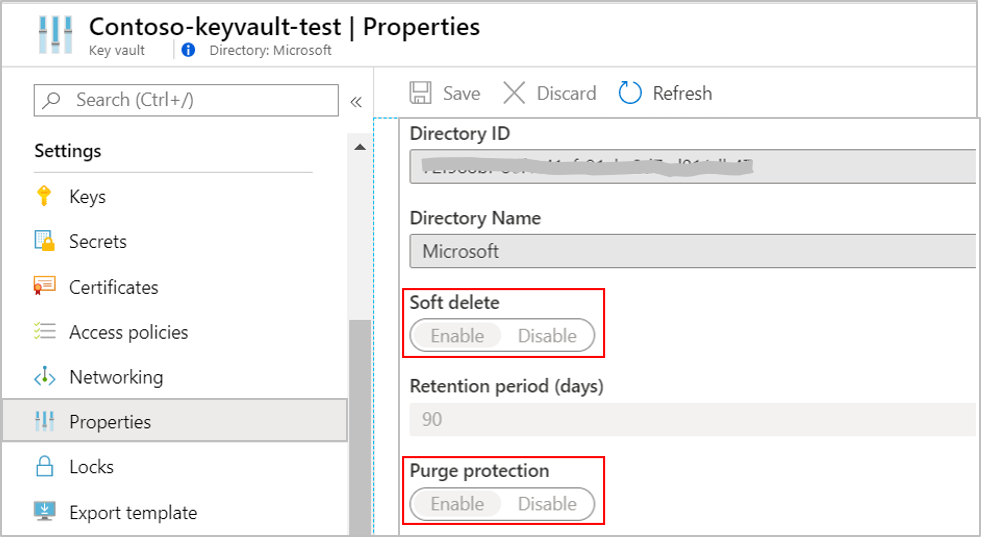
在专用群集所在的区域中创建或使用现有Azure 密钥保管库,或者计划其驻留位置。 将密钥生成或导入Azure 密钥保管库以用于日志加密。 必须将Azure 密钥保管库配置为可恢复,以保护密钥和对Azure Monitor中的数据的访问。 可以在密钥保管库中的属性下验证此配置。 启用 软删除 和 清除保护。
重要
若要有效响应即将到期的密钥等Azure 密钥保管库事件,请通过 Azure 事件网格 设置通知。 密钥过期时,引入和查询不会受到影响,但无法更新群集中的密钥。 请按照以下步骤解决:
- 在 Azure 门户中的群集概述页中,在 JSON View 下标识群集的概述页中使用的密钥。
- 在Azure 密钥保管库中延长密钥过期日期。
- 使用活动密钥更新群集,最好使用版本值
'',以始终自动使用最新版本。
可以使用 CLI 和 PowerShell 在 密钥保管库中更新这些设置:
将专用群集的托管身份类型与 密钥保管库 的访问权限相匹配。
专用群集使用其托管标识访问 密钥保管库 KEK 来加密数据。 专用群集的托管标识类型必须与 密钥保管库 角色分配标识匹配,以允许数据加密和解密作。
identity时,将 typeSystemAssigned 属性设置为 UserAssigned 或 。
例如,在请求正文中添加以下值,以创建具有系统分配的托管标识的群集:
{
"identity": {
"type": "SystemAssigned"
}
}
注意
可以在创建群集后更改标识类型,而无需中断引入或查询,但有以下注意事项:
有关创建专用群集的详细信息,请参阅 创建和管理专用群集。
向托管标识授予 密钥保管库 权限
密钥保管库有两种权限模型,用于授予对专用群集和基础存储的访问权限:Azure基于角色的访问控制(Azure RBAC - 推荐)和保管库访问策略(旧版)。
分配Azure RBAC (建议)
若要添加角色分配,你必须具有一个拥有
Microsoft.Authorization/roleAssignments/write和Microsoft.Authorization/roleAssignments/delete权限的角色,例如用户访问管理员或所有者。- 在 Azure 门户中打开 密钥保管库,然后选择 “设置>访问配置>Azure 基于角色的访问控制 并 应用”。
- 选择 转到访问控制(IAM),然后添加角色分配 密钥保管库 Crypto Service Encryption User。
- 在“成员”选项卡中选择“托管标识”,然后选择标识的订阅和标识作为成员。
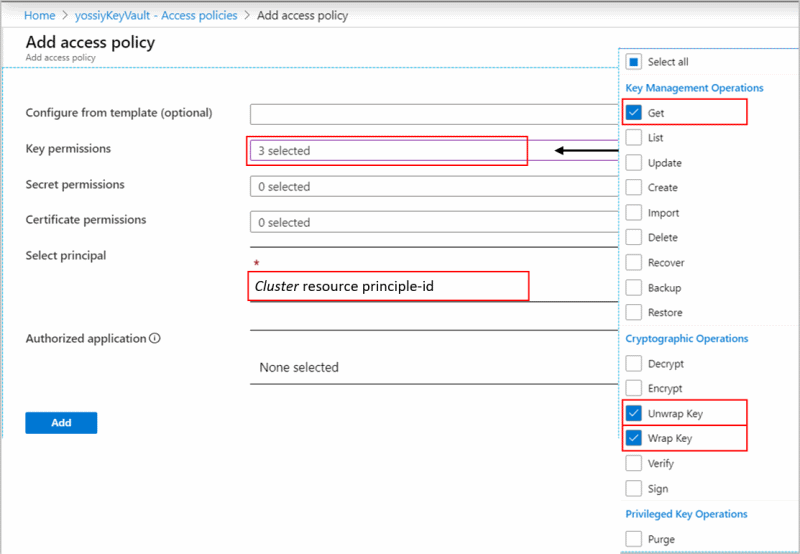
分配保管库访问策略(旧版)
在 Azure 门户中打开 密钥保管库,并选择 “访问策略>保管库访问策略>+ 添加访问策略 ”以使用以下设置创建策略:
- 密钥权限 - 选择“ 获取>包装密钥 ”和 “解包密钥”。
- 根据群集中使用的标识类型(系统或用户分配的托管标识)选择主体
- 系统分配的托管标识:输入群集名称或群集主体 ID
- 用户分配的托管标识 - 输入标识名称
需要 Get 权限来验证是否已将密钥保管库配置为可恢复,以保护密钥以及访问Azure Monitor数据。
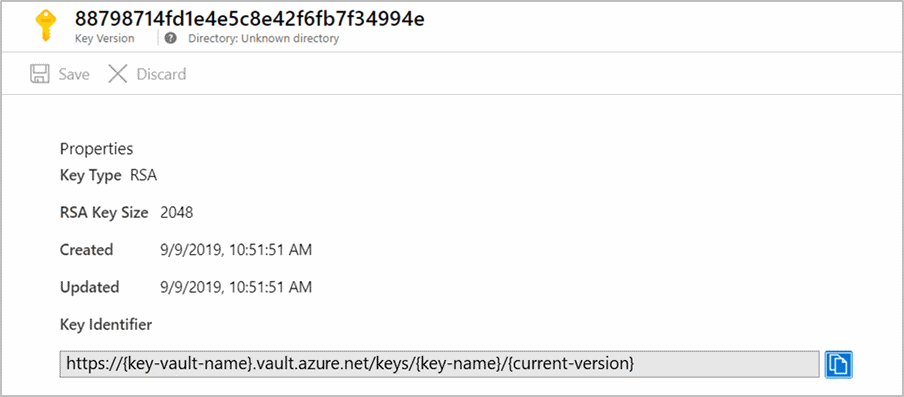
使用密钥标识符详细信息更新专用群集
群集的所有操作都需要 Microsoft.OperationalInsights/clusters/write 操作权限。 所有者或参与者角色(包括 */write 操作)可以授予此权限。 Log Analytics 贡献者角色(其中包括 Microsoft.OperationalInsights/* 操作)也授予此权限。
此步骤更新专用群集存储的密钥和版本,以便用于 AEKwrap 和 unwrap。
重要
- 密钥轮换可以是自动的,也可以针对每个明确的密钥版本进行。 请参阅 密钥轮换 ,在更新专用群集中的密钥标识符详细信息之前确定合适的方法。
- 专用群集更新不得在同一操作中包含标识和键标识符详细信息。 如果需要更新这两个方面,更新必须在两个连续操作中进行。
使用密钥标识符详细信息在群集中更新 KeyVaultProperties。
该操作是异步操作,可能需要一段时间才能完成。
验证专用群集预配
验证群集预配状态是否为Succeeded,然后再将工作区链接到群集。 如果在预配之前链接工作区和引入数据,该过程会删除引入的数据,并且无法恢复它。
使用 CLI、PowerShell 或 REST API 验证预配状态,如“ 使用密钥标识符详细信息更新专用群集 ”部分中所述。
将工作区链接到专用群集
重要
仅在群集预配后执行此步骤。 如果在预配之前链接工作区和引入数据,该过程会删除引入的数据,并且无法恢复它。
若要链接工作区,请参阅 “创建和管理专用群集”。
管理与客户管理的密钥相关的操作
密钥吊销
重要
- 若要撤销对数据的访问权限,请在密钥保管库中禁用密钥或删除访问策略。
- 将群集
identitytype设置为None还会撤销对数据的访问权限,但不要使用此方法,因为你无法在不联系支持人员的情况下还原它。
必须区分有意吊销密钥和临时密钥保管库连接中断:
-
有意吊销密钥 - 故意禁用密钥或删除访问策略时,群集的存储将在一小时内或更早地不可用。 引入到链接工作区的新数据将被删除且不可恢复。 系统删除热缓存(SSD)数据,并且无法访问。 这些工作区上的查询失败。 只要群集和工作区不会被删除,以前引入的数据就保持不变。 数据保留策略控制无法访问的数据,并在达到保留期时将其清除。 群集存储尝试定期访问 密钥保管库 以执行
wrap和unwrap操作。 重新启用密钥并unwrap成功后,系统会从专用群集存储重新加载 SSD 数据。 数据引入和查询功能在 30 分钟内恢复。 - 临时密钥保管库中断 - 在暂时性连接错误(网络超时、DNS失败)期间,群集使用缓存的操作密钥来维护数据引入和查询的可用性,从而不造成中断。 群集会定期尝试联系密钥保管库,恢复连接后恢复正常操作。 暂时性操作缓存不会绕过或削弱密钥吊销控制。 在暂时性连接中断期间,尚未公布有关群集在无法访问“密钥保管库”情况下可运行的具体时长。
密钥轮换
密钥轮换具有两种模式:
- 自动调整 - 在群集中更新
"keyVaultProperties"并省略"keyVersion"属性,或将其设置为''。 存储会自动使用最新的密钥版本。 - 显式密钥版本更新 - 更新
"keyVaultProperties"属性,并在"keyVersion"属性中更新密钥版本。 密钥轮换需要显式更新群集中的"keyVersion"属性。 有关详细信息,请参阅更新群集的密钥标识符详细信息。 如果在密钥保管库中生成新的密钥版本,但不更新群集中的密钥,则群集存储会继续使用以前的密钥。 如果在更新群集中的新密钥之前禁用或删除旧密钥,请输入 密钥吊销 状态。
在密钥轮换操作期间和之后,你的所有数据仍然可以访问。 群集始终使用帐户加密密钥(AEK)加密数据,该密钥使用 密钥保管库 中的新密钥加密密钥(KEK)版本进行加密。
用于保存的查询和日志搜索警报的客户管理密钥
Log Analytics中使用的查询语言具有表达性,并且可以在查询语法或注释中包含敏感信息。 具有严格法规和合规性要求的组织必须使用客户管理的密钥来加密此类信息。 将存储帐户链接到工作区时,Azure Monitor使你能够存储使用密钥加密的已保存查询、函数和日志搜索警报。
注意
无论客户管理的密钥配置如何,在以下情况下,查询都会使用 Microsoft 密钥 (MMK) 进行加密:Azure 仪表板、Azure 逻辑应用、Azure 笔记本和自动化运行手册。
将存储帐户链接到保存的查询时,该服务会将保存的查询和日志搜索警报查询存储在存储帐户中。 通过控制存储帐户 静态加密策略,可以使用客户管理的密钥来保护保存的查询和日志搜索警报。 你负责与该存储帐户相关的所有成本。
为保存的查询设置客户管理的密钥之前注意事项
- 你需要对工作区和存储帐户具有写入权限。
- 存储帐户必须是 StorageV2,并且与Log Analytics工作区位于同一区域中。
- 保存在 查询包中的查询 不会存储在链接的存储帐户上,并且无法使用客户管理的密钥进行加密。 建议使用客户管理的密钥将查询另存为经典查询以保护查询。
- 链接存储帐户中保存的查询和函数是服务项目,其格式可能会更改。
- 为保存的查询链接存储帐户时,不支持查询历史记录和固定到仪表板功能。
- 可以将保存的查询和日志搜索警报查询连接到单个或多个存储帐户。
- 若要使用密钥保持查询和功能加密,请使用客户管理的密钥配置链接的存储帐户。 在创建存储帐户时或之后执行此操作。
为保存的查询配置链接存储帐户
链接存储帐户以在存储帐户中保留保存的查询和函数。
注意
操作将保存的查询和函数从工作区转移到存储帐户中的一个表。 可以取消链接已保存查询的存储帐户,以将保存的查询和函数移回工作区。 如果在作后Azure门户中未显示已保存的查询或函数,请刷新浏览器。
工作簿的客户管理密钥
借助 Azure Monitor,还可以将使用密钥加密的工作簿查询存储在自己的存储帐户中。 请记住保存的查询和日志搜索警报的客户管理密钥中描述的相同注意事项。
在工作簿保存作中选择“将内容保存到 Azure 存储帐户”。
为保存的日志警报查询设置客户管理的密钥之前注意事项
- 群集将警报查询作为 Blob 保存在存储帐户中。
- 触发的日志搜索警报不包含搜索结果或警报查询。 使用 警报维度 获取触发警报的上下文。
- 若要使用密钥保持查询和函数加密,请使用客户管理的密钥配置链接的存储帐户。 在创建存储帐户时或之后执行此操作。
为日志搜索警报查询配置链接存储帐户
链接用于“警报”的存储帐户,以在存储帐户中保留日志搜索警报查询。
注意事项和限制
每个区域和订阅最多可以创建五个活动群集。
每个区域和订阅最多可以有七个预留集群(活动的或最近删除的)。
最多可以将 1,000 个Log Analytics工作区链接到群集。
您可以在 30 天内对特定工作区执行最多两个工作区链接操作。
当前不支持将群集移到另一个资源组或订阅。
群集更新不应在同一操作中包含标识和密钥标识符的详细信息。 若要更新这两个操作,请使用两个连续的操作。
目前,Lockbox 在中国不可用。
从 2020 年 10 月起,在受支持区域中创建的群集会自动配置双重加密。 可以通过在群集上发送
GET请求来验证群集是否已配置为双重加密,并在启用了双重加密的群集上观察isDoubleEncryptionEnabled值为true。如果创建群集并收到错误“
region-name不支持群集双重加密”,则仍可以通过在 REST 请求正文中添加"properties": {"isDoubleEncryptionEnabled": false}来创建群集,而无需双重加密。创建群集后,无法更改双重加密设置。
仍链接到群集的已删除工作区允许执行恢复操作。 只能在 软删除 期间使用。 恢复会将工作区返回到其以前的状态,并保持链接到群集。
客户管理的密钥的加密应用于在配置后新引入的数据。 在配置前引入的数据仍将使用 Microsoft 密钥进行加密。 你可以无缝查询在配置客户管理的密钥前后引入的数据。
必须将Azure 密钥保管库配置为可恢复。 默认情况下未启用这些属性,应使用 CLI 或 PowerShell 对其进行配置:
Azure 密钥保管库、群集和工作区必须位于同一区域和同一 Microsoft Entra 租户中,但它们可以位于不同的订阅中。
如果将群集的
identitytype设置为None,还可撤销数据访问权,但不建议使用此方法,因为如果不联系支持人员就无法将其还原。 建议通过密钥吊销来撤销对你的数据的访问权限。如果 密钥保管库 位于 Private-Link(虚拟网络),则不能将客户管理的密钥用于用户分配的托管标识。 在此情景中使用系统分配的托管标识。
故障排除
密钥保管库可用性对行为的影响 - 有关群集如何在处理临时密钥保管库中断与密钥有意吊销上的详细信息,请参阅 密钥吊销。 群集在短时间内缓存 AEK,并以每 6 到 60 秒的频率定期联系 密钥保管库 以
unwrap。如果在群集处于预配状态或更新状态时更新群集,更新将失败。
如果在创建群集时遇到冲突错误,则可能在过去 14 天内删除了同名的群集并保留其名称。 删除后的群集名称在删除后 14 天内可用。
如果工作区已链接到另一个群集,则将工作区链接到群集将失败。
如果创建群集并立即指定
KeyVaultProperties,则在为群集分配标识并向密钥保管库授予权限之前,该操作可能会失败。如果您尝试更新现有的
KeyVaultProperties群集,而 密钥保管库 中缺少Get密钥访问策略,则操作会失败。如果无法部署群集,请验证 Azure 密钥保管库、群集和链接工作区是否位于同一区域。 它们可以位于不同的订阅中。
如果在密钥保管库轮换密钥,并且不会更新群集中的新密钥标识符详细信息,群集会继续使用以前的密钥,并且数据将不可访问。 更新群集中的新密钥标识符详细信息以恢复数据引入和查询功能。 使用
''表示法更新密钥版本,以确保专用群集存储始终自动使用最新的密钥版本。某些作运行时间较长,可能需要一段时间才能完成,包括群集创建、群集密钥更新和群集删除。 可以通过向群集或工作区发送
GET请求并观察响应来检查作状态。 例如,未链接的工作区在clusterResourceId下没有features。错误消息
群集更新
- 400 - 群集处于正在删除状态。 当前异步操作正在进行中。 群集必须完成其操作,才能执行任意更新操作。
- 400 - KeyVaultProperties 不为空,但格式错误。 请参阅密钥标识符更新。
- 400 - 无法验证密钥保管库中的密钥。 可能是由于权限不足或密钥不存在。 验证是否在密钥保管库中设置密钥和访问策略。
- 400 - 密钥不可恢复。 密钥保管库 必须设置为软删除和清除保护。 请参阅 密钥保管库 文档。
- 400 - 现在无法执行操作。 等待异步操作完成,然后重试。
- 400 - 群集处于正在删除状态。 等待异步操作完成,然后重试。
群集获取
- 404 - 找不到群集。 群集可能已被删除。 如果尝试使用该名称创建群集但发生冲突,则该群集正处于删除过程中。