Applies to: ✔️ Linux VMs ✔️ Windows VMs ✔️
Azure Disk Storage supports double encryption at rest for managed disks. For conceptual information on double encryption at rest, and other managed disk encryption types, see the Double encryption at rest section of our disk encryption article.
Restrictions
Double encryption at rest isn't currently supported with either Ultra Disks or Premium SSD v2 disks.
Prerequisites
If you're going to use Azure CLI, install the latest Azure CLI and sign in to an Azure account with az login.
If you're going to use the Azure PowerShell module, install the latest Azure PowerShell version, and sign in to an Azure account using Connect-AzAccount.
Getting started
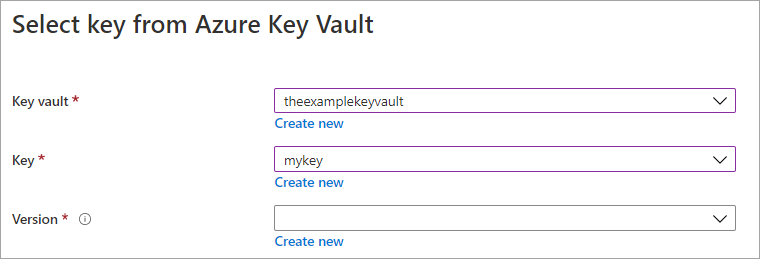
Sign in to the Azure portal.
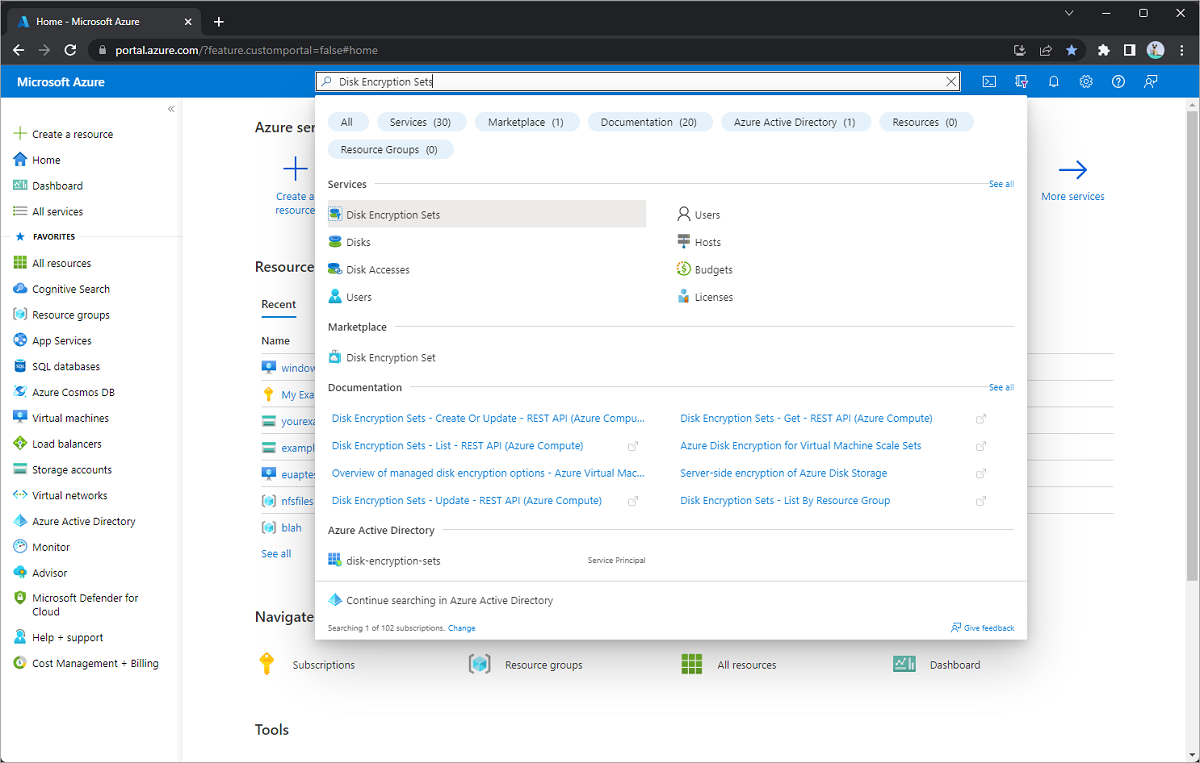
Search for and select Disk Encryption Sets.
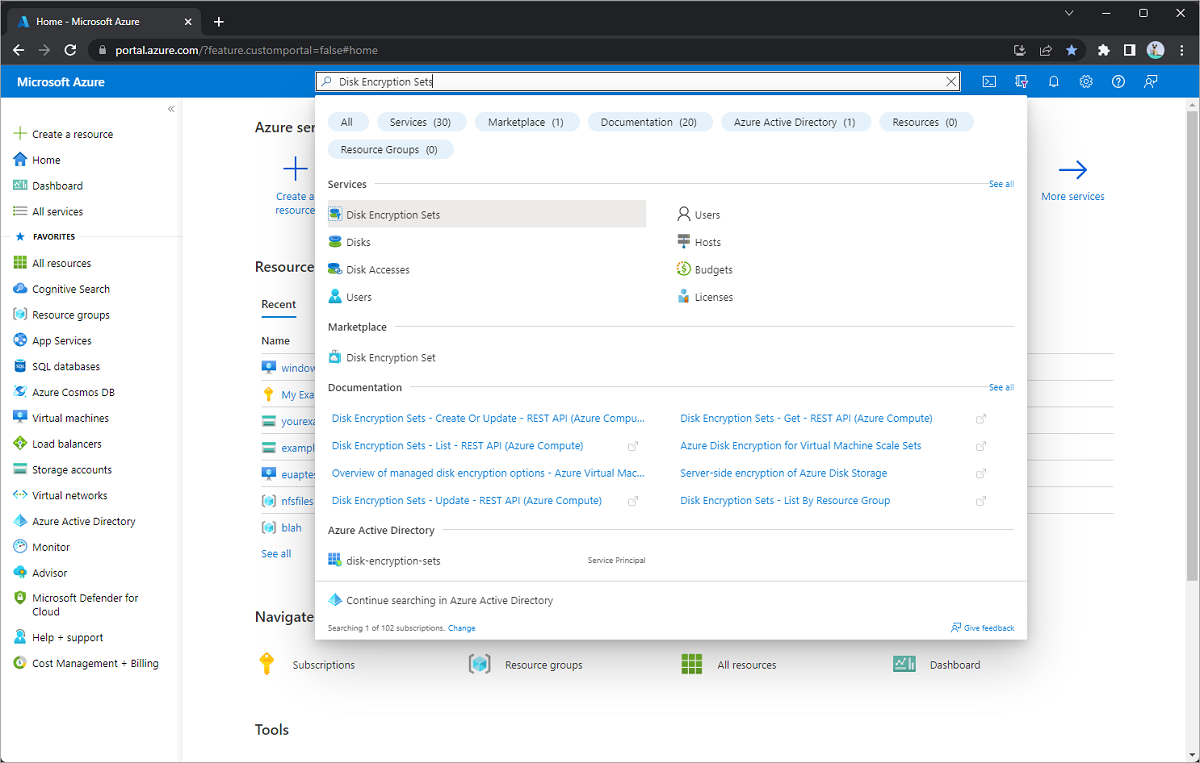
Select + Create.
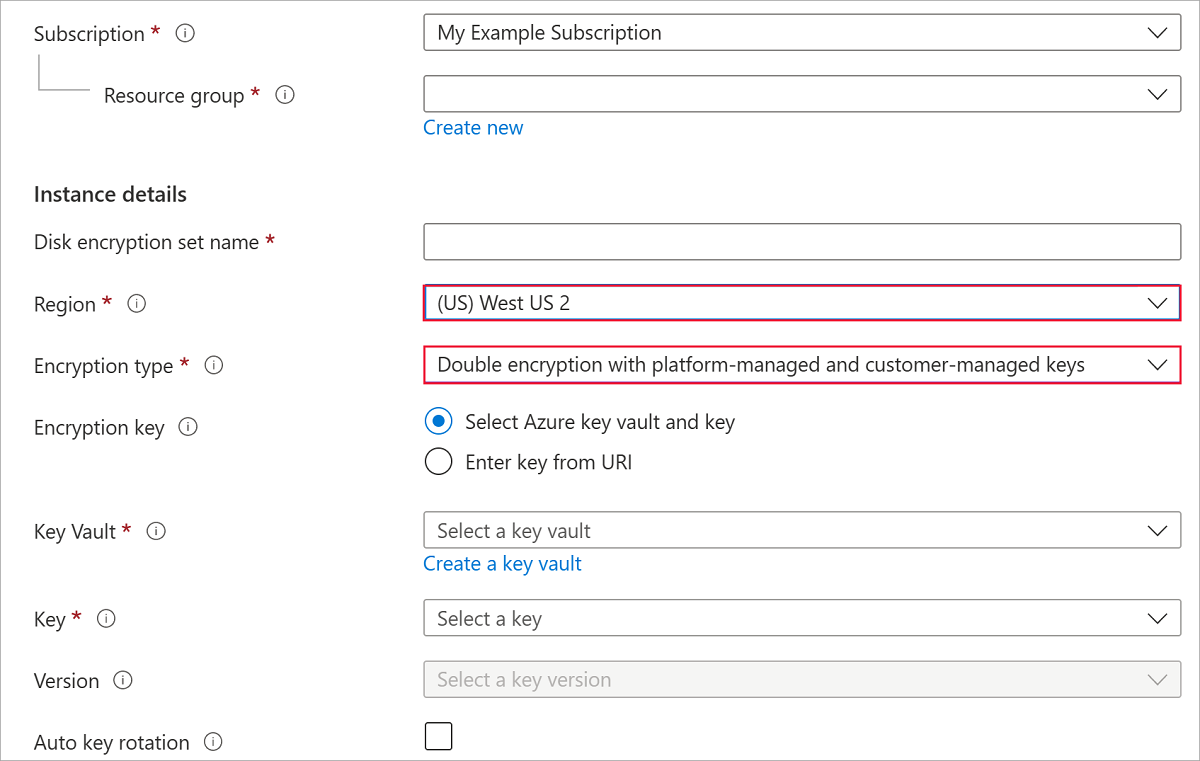
Select one of the supported regions.
For Encryption type, select Double encryption with platform-managed and customer-managed keys.
Note
Once you create a disk encryption set with a particular encryption type, it cannot be changed. If you want to use a different encryption type, you must create a new disk encryption set.
Fill in the remaining info.
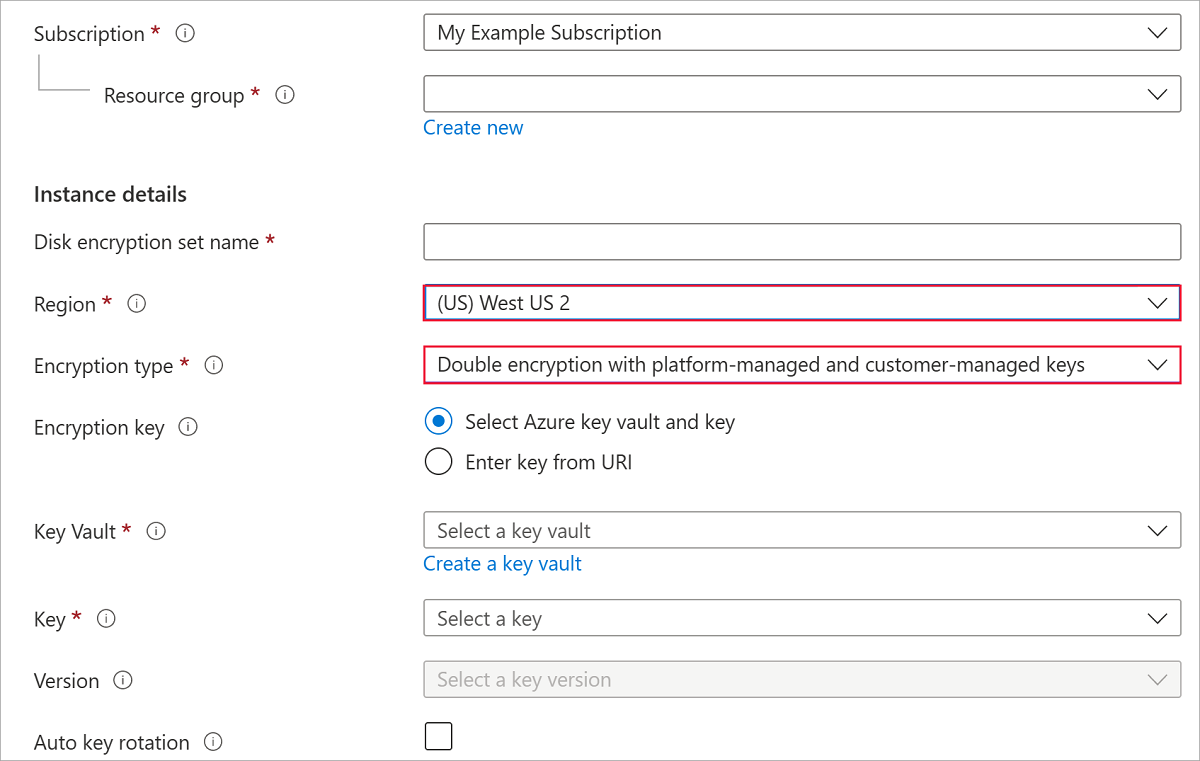
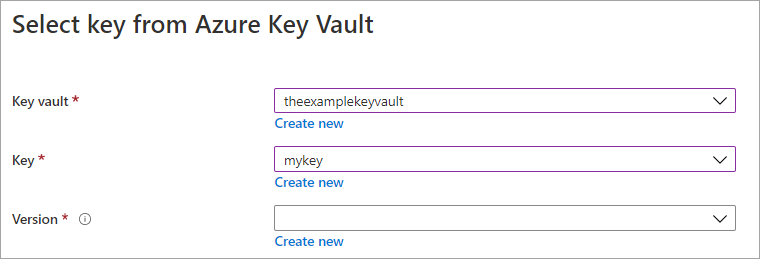
Select an Azure Key Vault and key, or create a new one if necessary.
Note
If you create a Key Vault instance, you must enable soft delete and purge protection. These settings are mandatory when using a Key Vault for encrypting managed disks, and protect you from losing data due to accidental deletion.
Select Create.
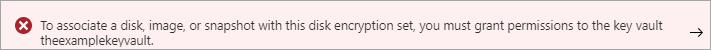
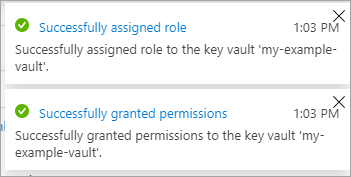
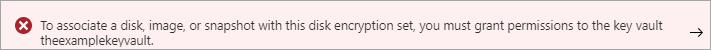
Navigate to the disk encryption set you created, and select the error that is displayed. This will configure your disk encryption set to work.
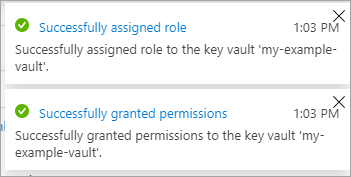
A notification should pop up and succeed. Doing this will allow you to use the disk encryption set with your key vault.
Navigate to your disk.
Select Encryption.
For Encryption type, select Double encryption with platform-managed and customer-managed keys.
Select your disk encryption set.
select Save.
You have now enabled double encryption at rest on your managed disk.
Create an instance of Azure Key Vault and encryption key.
When creating the Key Vault instance, you must enable soft delete and purge protection. Soft delete ensures that the Key Vault holds a deleted key for a given retention period (90 day default). Purge protection ensures that a deleted key can't be permanently deleted until the retention period lapses. These settings protect you from losing data due to accidental deletion. These settings are mandatory when using a Key Vault for encrypting managed disks.
subscriptionId=yourSubscriptionID
rgName=yourResourceGroupName
location=chinanorth2
keyVaultName=yourKeyVaultName
keyName=yourKeyName
diskEncryptionSetName=yourDiskEncryptionSetName
diskName=yourDiskName
az account set --subscription $subscriptionId
az keyvault create -n $keyVaultName -g $rgName -l $location --enable-purge-protection true --enable-soft-delete true
az keyvault key create --vault-name $keyVaultName -n $keyName --protection software
Get the key URL of the key you created with az keyvault key show.
az keyvault key show --name $keyName --vault-name $keyVaultName
Create a DiskEncryptionSet with encryptionType set as EncryptionAtRestWithPlatformAndCustomerKeys. Replace yourKeyURL with the URL you received from az keyvault key show.
az disk-encryption-set create --resource-group $rgName --name $diskEncryptionSetName --key-url yourKeyURL --source-vault $keyVaultName --encryption-type EncryptionAtRestWithPlatformAndCustomerKeys
Grant the DiskEncryptionSet resource access to the key vault.
Note
It may take few minutes for Azure to create the identity of your DiskEncryptionSet in your Microsoft Entra ID. If you get an error like "Cannot find the Active Directory object" when running the following command, wait a few minutes and try again.
desIdentity=$(az disk-encryption-set show -n $diskEncryptionSetName -g $rgName --query [identity.principalId] -o tsv)
az keyvault set-policy -n $keyVaultName -g $rgName --object-id $desIdentity --key-permissions wrapkey unwrapkey get
Create an instance of Azure Key Vault and encryption key.
When creating the Key Vault instance, you must enable soft delete and purge protection. Soft delete ensures that the Key Vault holds a deleted key for a given retention period (90 day default). Purge protection ensures that a deleted key can't be permanently deleted until the retention period lapses. These settings protect you from losing data due to accidental deletion. These settings are mandatory when using a Key Vault for encrypting managed disks.
$ResourceGroupName="yourResourceGroupName"
$LocationName="chinanorth2"
$keyVaultName="yourKeyVaultName"
$keyName="yourKeyName"
$keyDestination="Software"
$diskEncryptionSetName="yourDiskEncryptionSetName"
$keyVault = New-AzKeyVault -Name $keyVaultName -ResourceGroupName $ResourceGroupName -Location $LocationName -EnableSoftDelete -EnablePurgeProtection
$key = Add-AzKeyVaultKey -VaultName $keyVaultName -Name $keyName -Destination $keyDestination
Retrieve the URL for the key you created, you'll need it for subsequent commands. The ID output from Get-AzKeyVaultKey is the key URL.
Get-AzKeyVaultKey -VaultName $keyVaultName -KeyName $keyName
Get the resource ID for the Key Vault instance you created, you'll need it for subsequent commands.
Get-AzKeyVault -VaultName $keyVaultName
Create a DiskEncryptionSet with encryptionType set as EncryptionAtRestWithPlatformAndCustomerKeys. Replace yourKeyURL and yourKeyVaultURL with the URLs you retrieved earlier.
$config = New-AzDiskEncryptionSetConfig -Location $locationName -KeyUrl "yourKeyURL" -SourceVaultId 'yourKeyVaultURL' -IdentityType 'SystemAssigned'
$config | New-AzDiskEncryptionSet -ResourceGroupName $ResourceGroupName -Name $diskEncryptionSetName -EncryptionType EncryptionAtRestWithPlatformAndCustomerKeys
Grant the DiskEncryptionSet resource access to the key vault.
Note
It may take few minutes for Azure to create the identity of your DiskEncryptionSet in your Microsoft Entra ID. If you get an error like "Cannot find the Active Directory object" when running the following command, wait a few minutes and try again.
$des=Get-AzDiskEncryptionSet -name $diskEncryptionSetName -ResourceGroupName $ResourceGroupName
Set-AzKeyVaultAccessPolicy -VaultName $keyVaultName -ObjectId $des.Identity.PrincipalId -PermissionsToKeys wrapkey,unwrapkey,get
Next steps