Azure Firewall是云原生智能网络防火墙安全服务,为Azure云工作负载提供顶层威胁防护。 它是一种完全有状态的防火墙即服务,具有内置的高可用性和无限的云可伸缩性。 Azure Firewall检查东西向和南北向流量。 若要了解这些流量类型,请参阅东-西和南-北流量。
Azure Firewall在三个 SKU 中提供:基本、标准和高级。
注释
Azure Firewall是构成Azure网络安全类别的服务之一。 此类别中的其他服务包括 Azure DDoS 防护 和 Azure Web Application Firewall。 每个服务都有自己的独特功能和用例。 有关此服务类别的详细信息,请参阅 网络安全。
基本Azure Firewall
Azure Firewall Basic 专为中小企业(SMB)设计,以保护其Azure云环境。 它以负担得起的价格提供基本保护。
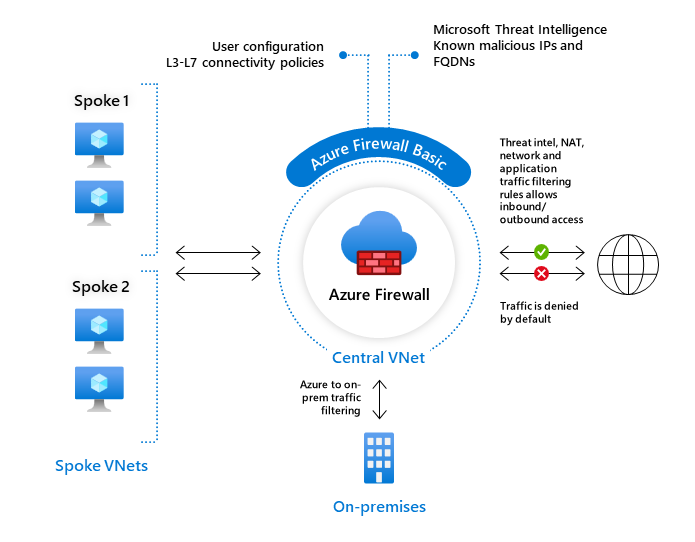
Azure Firewall基本版的主要限制包括:
- 仅支持威胁 Intel 警报模式。
- 具有两个虚拟机后端实例的固定缩放单元
- 建议用于预估吞吐量为 250 Mbps 的环境
有关详细信息,请参阅 按 SKU 的 Azure Firewall 功能。
Azure Firewall 标准
Azure Firewall Standard 具备从微软网络安全部门直接推送的 L3-L7 筛选功能和威胁情报。 它可以提醒你并阻止与已知恶意 IP 地址和域之间的流量。 它实时更新,以防止新的和新兴的威胁。
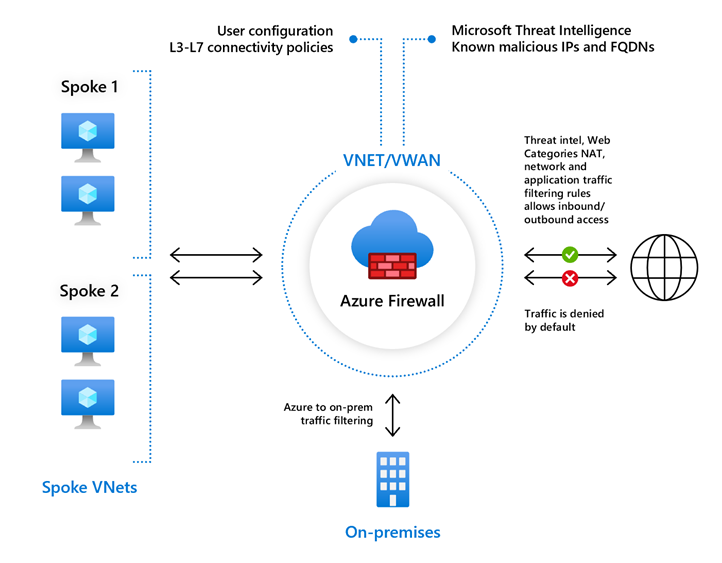
有关详细信息,请参阅 按 SKU 的 Azure Firewall 功能。
Azure 防火墙高级版
Azure Firewall Premium 提供高级功能,包括基于签名的 IDPS,用于通过识别特定模式进行快速攻击检测。 这些模式可能包括网络流量中的字节序列或恶意软件使用的已知恶意指令序列。 超过 50 个类别的 67,000 个签名实时更新,可防范恶意软件、网络钓鱼、硬币挖掘和特洛伊木马攻击等新兴攻击。
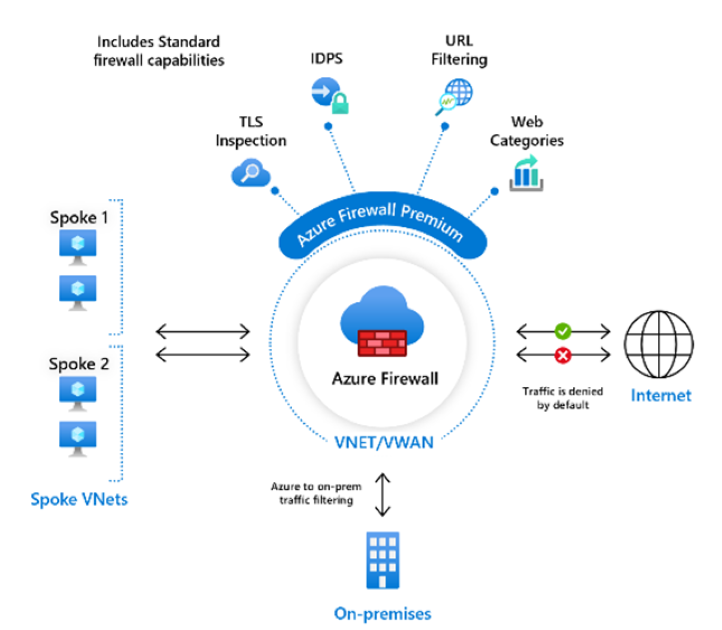
有关详细信息,请参阅 按 SKU 的 Azure Firewall 功能。
功能比较
若要比较所有Azure Firewall SKU 功能,请参阅 选择正确的 Azure Firewall SKU 以满足需求。
Azure 防火墙管理器
Azure Firewall Manager提供了一个中心位置,用于跨多个订阅管理Azure防火墙。 它使用防火墙策略,将一套通用的网络和应用程序规则和配置应用到租户中的防火墙。
防火墙管理器支持虚拟网络和Virtual WAN(安全虚拟中心)环境中的防火墙。 安全虚拟中心使用Virtual WAN路由自动化解决方案,只需几个步骤即可简化将流量路由到防火墙。
若要了解详细信息,请参阅 Azure Firewall Manager。
定价和 SLA
有关定价详细信息,请参阅 Azure Firewall 定价。
有关 SLA 信息,请参阅 Azure Firewall SLA。
支持的区域
有关受支持区域的列表,请参阅Azure按区域提供的产品。
最新动态
若要了解最新更新,请参阅 Azure 更新。
已知问题
有关已知问题,请参阅 Azure Firewall 已知问题。